結果
セキュリティ評価が完了しました。
リスクスコア:
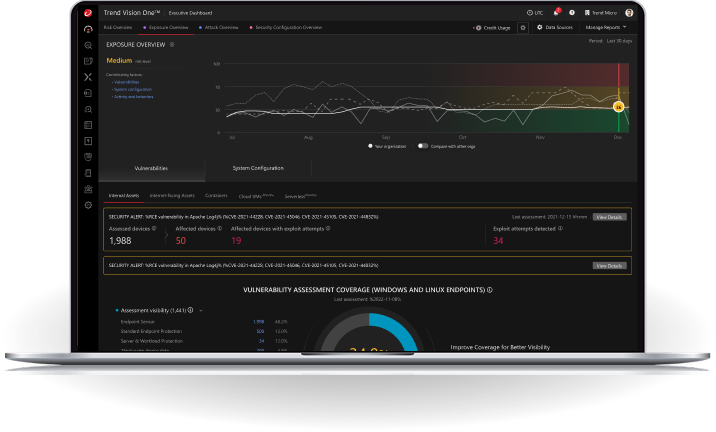
おめでとうございます!あなたのドメインはサイバー攻撃のリスクが低く、良好な状態です。Cyber Risk Exposure Management(CREM)を活用することで、現在の優れたセキュリティ態勢をより簡単に維持することができます。
あなたのドメインには、軽微なセキュリティ改善の余地があります。Cyber Risk Exposure Management(CREM)を活用することで、資産全体を可視化し、リスクの早期発見・対応が可能になります。
あなたのドメインは、サイバー攻撃の侵入口となる危険性があります。Cyber Risk Exposure Management(CREM)を活用し、対応策の優先順位を付けることで、セキュリティを効果的に維持しましょう。