早期の検知・迅速な対応・リスクの軽減
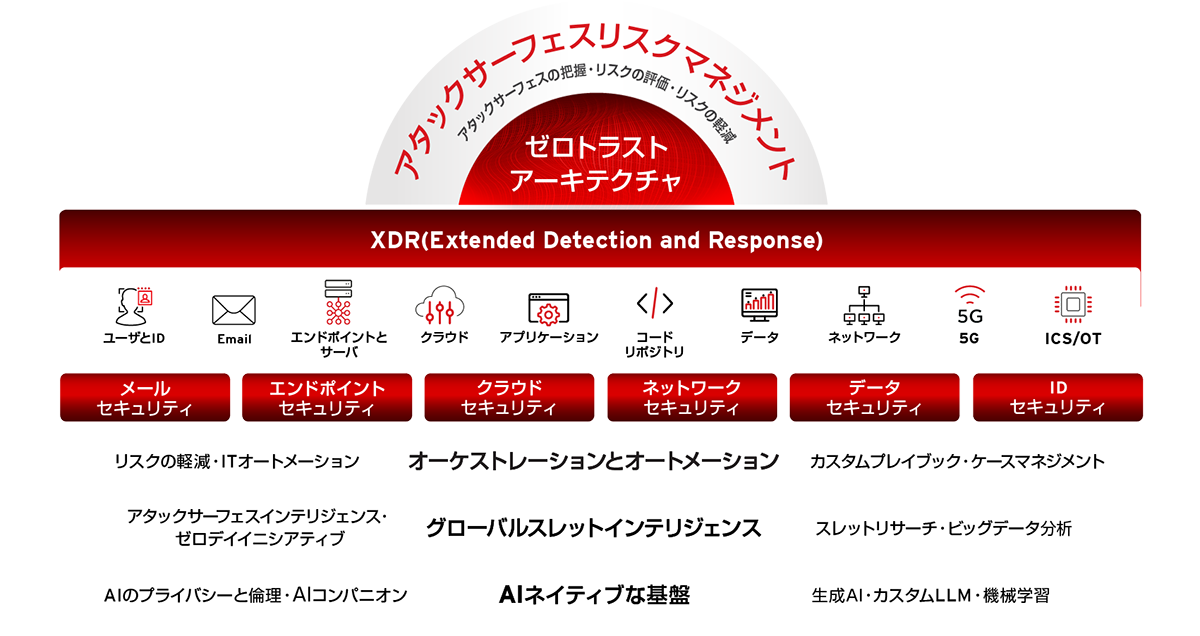
統合サイバーセキュリティプラットフォーム「Trend Vision One™」で脅威を迅速に阻止
サイバーセキュリティコストを70%削減 • アラートを1日あたり1000から4に軽減 • 滞留時間を65%削減
課題別のソリューション
現在および将来の脅威に対抗するサイバーセキュリティソリューション






トレンドマイクロは
24時間365日のサポート体制でセキュリティチームを強化します。
プレミアムサポート、マネージドXDR、およびインシデント対応サービスにより、法人組織のセキュリティチームを支援します。
役割別のソリューション
セキュリティに先手を打つ
導入事例
世界中の50万社を超える企業をトレンドマイクロが支援










サイバーセキュリティのインサイト
最新のリサーチと専門家の視点
ウェビナー・イベント情報
当社の影響
数字で見るトレンドマイクロ
6.5 兆以上
2023年の脅威数
1600 億以上
2023年にブロックした脅威
No. 1
クラウドセキュリティのリーダー
50 万以上
グローバル企業のお客さま