Ransom.Win32.EYECRYLOCKER.A
VirTool:Win32/Vbinder (Microsoft), Backdoor.Win32.Poison.ggrf (Kaspersky)
Windows

Threat Type:
Ransomware
Destructiveness:
No
Encrypted:

In the wild::
Yes
OVERVIEW
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Detalles de entrada
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Instalación
Infiltra y ejecuta los archivos siguientes:
- %User Temp%\EyeCry.exe -> detected as Ransom_Petya.R002C0CIR20
(Nota: %User Temp% es la carpeta Temp del usuario activo, que en el caso de Windows 2000(32-bit), XP y Server 2003(32-bit) suele estar en C:\Documents and Settings\{nombre de usuario}\Local Settings\Temp y en el case de Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) y 10(64-bit) en C:\Users\{nombre de usuario}\AppData\Local\Temp).
)Agrega los procesos siguientes:
- %System%\shutdown.exe -r -f -t 0
(Nota: %System% es la carpeta del sistema de Windows, que en el caso de Windows 98 y ME suele estar en C:\Windows\System, en el caso de Windows NT y 2000 en C:\WINNT\System32 y en el caso de Windows 2000(32-bit), XP, Server 2003(32-bit), Vista, 7, 8, 8.1, 2008(64-bit), 2012(64bit) y 10(64-bit) en C:\Windows\System32).
)Otros detalles
Hace lo siguiente:
- Overwrites the MBR to display the following after forcing the machine to restart:
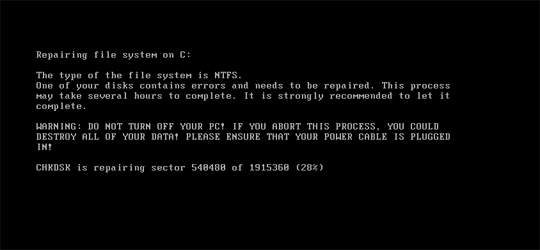
and the following after waiting the for the process in the first image to finish:
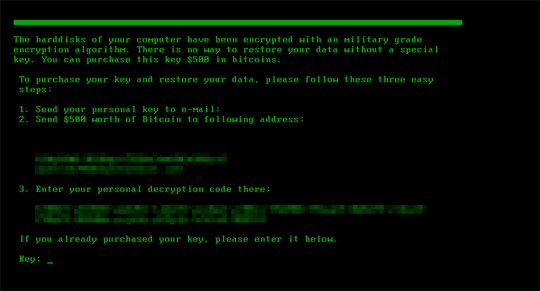
- Prevents access to the machine by displaying the following picture as a ransom note after waiting for the previous steps to finish:
SOLUTION
Step 2
Los usuarios de Windows ME y XP, antes de llevar a cabo cualquier exploración, deben comprobar que tienen desactivada la opción Restaurar sistema para permitir la exploración completa del equipo.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restore your system's Master Boot Record (MBR)
To restore your system's Master Boot Record (MBR):
• On Windows 7 and Server 2008 (R2):
- Insert your Windows Installation DVD into the DVD drive, then press the restart button on your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to choose the installation language. On the Install Windows window, choose your language, locale, and keyboard layout or input method. Click Repair your computer.
- Select Use recovery tools that can help fix problems starting Windows. Select your installation of Windows. Click Next.
- If the Startup Repair window appears, click Cancel, Yes, then Finish.
- In the System Recovery Options menu, click Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Restart to restart your computer normally.
• On Windows 8, 8.1, 10, and Server 2012:
- Insert your Windows Installation DVD in the DVD drive, then restart your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to select the keyboard layout. Then on the Windows Setup window, choose your language, locale, and input method. Click Next, then click Repair your computer.
- Click Troubleshoot>Advanced Options>Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Continue to restart the system normally.
Step 5
Buscar y eliminar este archivo
- %User Temp%\EyeCry.exe
Step 6
Explorar el equipo con su producto de Trend Micro para eliminar los archivos detectados como Ransom.Win32.EYECRYLOCKER.A En caso de que el producto de Trend Micro ya haya limpiado, eliminado o puesto en cuarentena los archivos detectados, no serán necesarios más pasos. Puede optar simplemente por eliminar los archivos en cuarentena. Consulte esta página de Base de conocimientos para obtener más información.
Did this description help? Tell us how we did.

