Know the Symptoms: Protect Your Devices While Working From Home

The coronavirus pandemic has forced most businesses to accommodate work-from-home (WFH) arrangements, but organizations that were unprepared for the shift to remote operations may have been left scrambling. This may have resulted in unsecured systems left running in the office or vulnerable hardware that employees took home.
Threat actors are aware of this situation, and they’re capitalizing on it: Trend Micro has detected an increase in attack attempts and malicious routines targeting remote systems and connected devices. The attacks on remote and home devices from December 2019 to the end of the first quarter of 2020 shows a significant increase compared to the activity detected within the same period the previous year.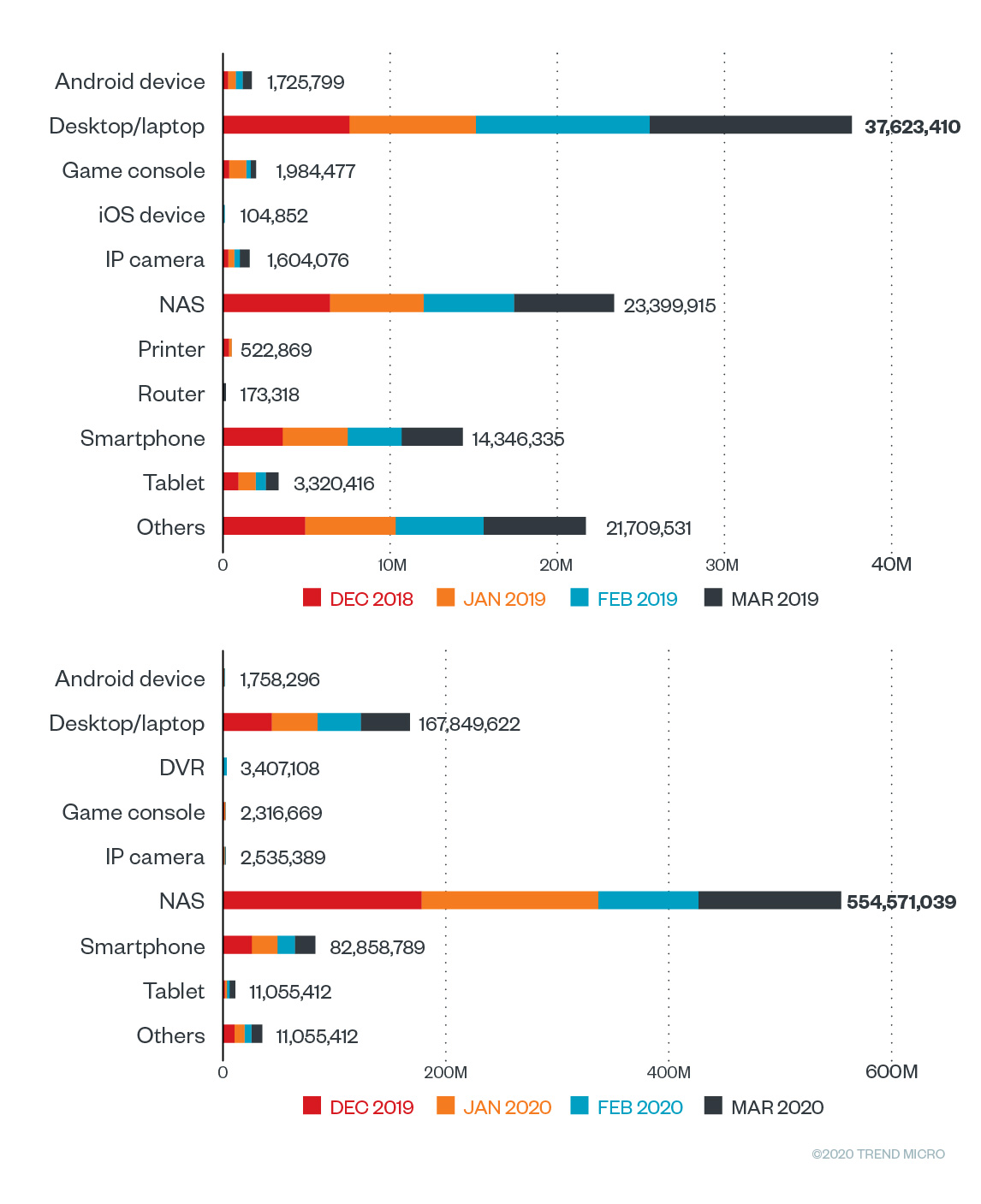
Figure 1. Inbound infection and attack attempts on devices from December 2019 to March 2020, detected by Trend Micro’s Smart Home Network (SHN)
Cybercriminals have been employing known techniques and attacking common entry points to get into users’ home networks and devices. From exhausting default passwords and revisiting unpatched vulnerabilities, to scanning for open ports and services and installing backdoors, these malicious actors have noticeably increased their deployments over the last four months.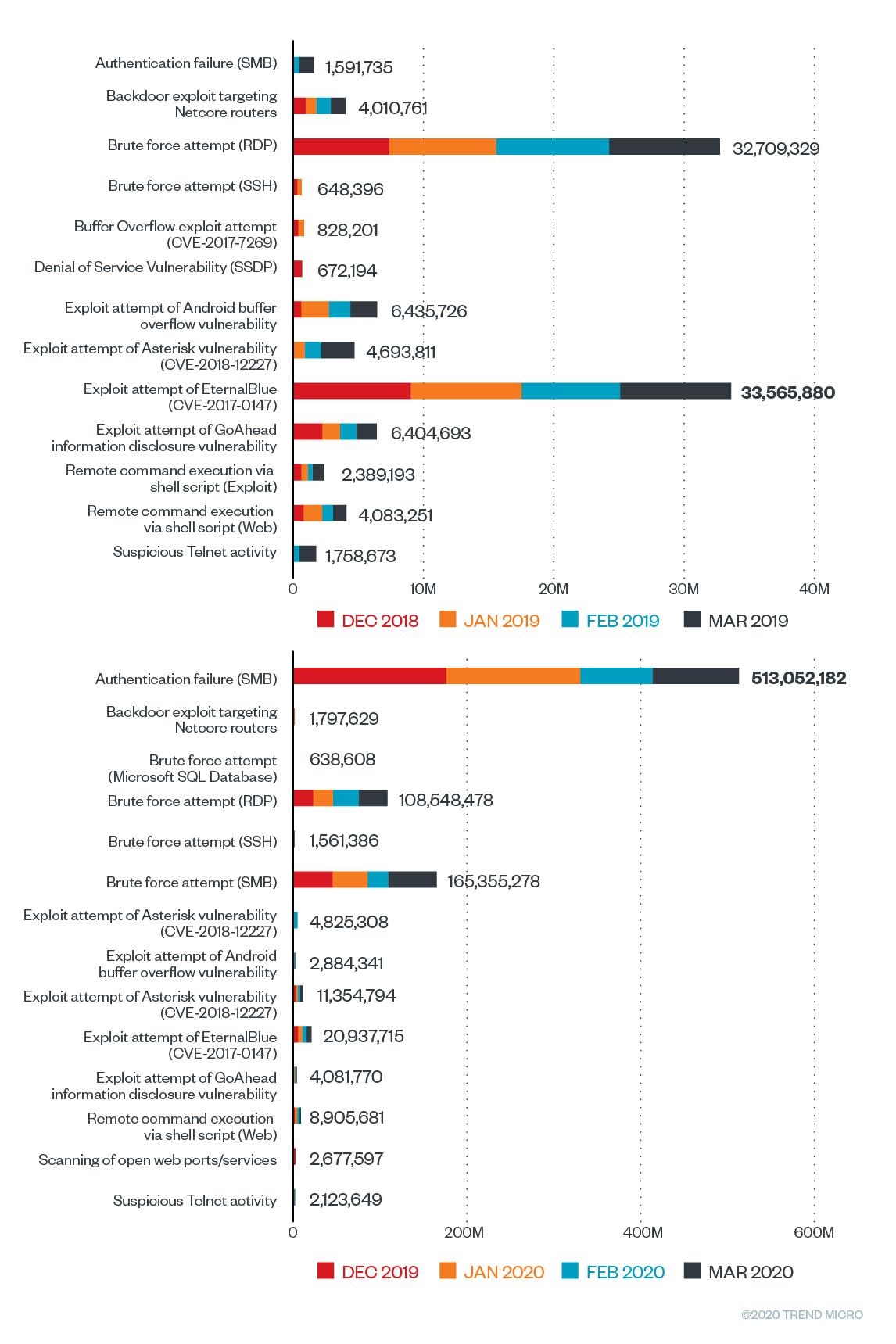
Figure 2. Comparison of the top intrusion methods from December 2019 to March 2020
As more news related to the pandemic came in, malicious routines targeting or luring users with coronavirus-related messages also increased as more professionals became dependent on their home networks and devices to accomplish their tasks. And while not all intrusions, malicious routines, and attacks have observable signs, there are telltale symptoms that non-technical employees can check to determine if their devices have been hacked or infected with malware.
What are the symptoms of compromise?
Some malicious routines don’t exhibit any obvious signs of infection or intrusion, while some symptoms become evident after specific user actions. But while these are not encompassing signs of a possible infection or attack, these are the common and observable signs of malware infection and intrusion.
How did the device get compromised?
Cybercriminals constantly change or improve their techniques for infecting and attacking a growing array of mobile and smart devices. Here are the possible ways they can get through:
- Downloading apps, software, and/or media from third-party marketplaces or websites. These apps may be embedded with malicious components, impersonate other popular apps, or have functions unrelated to its stated purpose.
- Connecting to public Wi-Fi networks. Threat actors can intercept and steal information that goes through these networks. In other instances, the available connection may be a fake hotspot that captures data from devices that connect to it.
- Clicking on phishing and/or SMShing links. Threat actors use malicious URLs embedded in email or text messages to gain device access, steal banking or personal data, or spread malware.
- Visiting malicious and/or infected websites or apps. Malicious websites can be used to infect devices that intentionally or unintentionally visit these pages. Cybercriminals can inject malware and other malicious commands, or create an overlay that impersonates legitimate pages to redirect or infect visitors.
- Jailbreaking. As this involves intentionally removing software and telecommunication restrictions to override the device’s embedded exclusive functions, the process provides openings that malicious actors can exploit whenever the user goes online.
- Leaving system and/or media vulnerabilities unpatched. Security gaps in the OS, hardware, and apps can leave openings that cybercriminals can abuse.
- Using default access credentials. Default usernames and passwords in routers and devices assigned by manufacturers and network service providers tend to be similar or the same for all its subscribers. Cybercriminals can refer to a common list to access these devices for attacks.
- Targeted attacks. High-profile individuals in specific industries are high-value targets. Their respective devices can be used to trace and track their movements, have other high-value contacts, and contain sensitive information.
Overnight remote work schemes that the coronavirus pandemic has caused may be overwhelming to the current infrastructure, but every business should regard it as the new norm. These new business continuity procedures have increased the use of personal equipment and work devices connected to home networks, and this could lead to issues considering the possibly lower security measures at home compared to the workplace. As such, short term solutions focused on output delivery may have to be changed for long-term and sustainable business solutions. More than ever, users have to secure data access between their homes and the office.
Trend Micro continues to monitor all attacks and malicious routines related to Covid-19 that can compromise your businesses and devices. Multilayered protection is also recommended for protecting all fronts and preventing users from accessing malicious domains that could deliver malware. Trend Micro endpoint solutions such as the Smart Protection Suites and Worry-Free™ Business Security detect and block malware as well as and the malicious domains they use.
As an added layer of defense, Trend Micro™ Email Security thwarts spam and other email attacks. The protection it provides is constantly updated, protecting the system from both old and new attacks. Trend Micro™ InterScan™ Messaging Security provides comprehensive protection that stops inbound threats and secures outbound data, as well as blocks spam and other email threats.
Users can employ comprehensive protections such as the Trend Micro™ Security and Trend Micro™ Internet Security solutions, which offer effective safeguards against threats to IoT devices through features that can detect malware at the endpoint level. Connected devices can also be protected by security software such as the Trend Micro™ Home Network Security and Trend Micro Smart Home Network™ (SHN) solutions, which can check internet traffic between the router and all connected devices. The Trend Micro™ Deep Discovery™ Inspector network appliance can monitor all ports and network protocols for advanced threats and protect enterprises from targeted attacks.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation