New Sextortion Scheme Demands Payment in Bitcoin Cash
 Trend Micro researchers uncovered a sextortion scheme targeting Italian-speaking users. Based on IP lookups of the spam/phishing emails’ senders, they appear to have been sent via the Gamut spam botnet. The scheme also seemed to be part of a campaign. The spam emails were caught on April 19, peaking from 9 to 10 A.M. CEST (Central European Summer Time). Feedback from Trend Micro’s Smart Protection Network™ identified 25,000 related spam emails.
Trend Micro researchers uncovered a sextortion scheme targeting Italian-speaking users. Based on IP lookups of the spam/phishing emails’ senders, they appear to have been sent via the Gamut spam botnet. The scheme also seemed to be part of a campaign. The spam emails were caught on April 19, peaking from 9 to 10 A.M. CEST (Central European Summer Time). Feedback from Trend Micro’s Smart Protection Network™ identified 25,000 related spam emails.
The spam emails are also notable in that the hackers are now also using Bitcoin Cash as one of their preferred cryptocurrencies. The use of a Bitcoin Cash address likely just serves as an alternative, as other sextortion schemes that the researchers observed still use Bitcoin wallet addresses.
[Trend Micro Research: Sextortion in the Far East: Blackmail Goes Mobile]
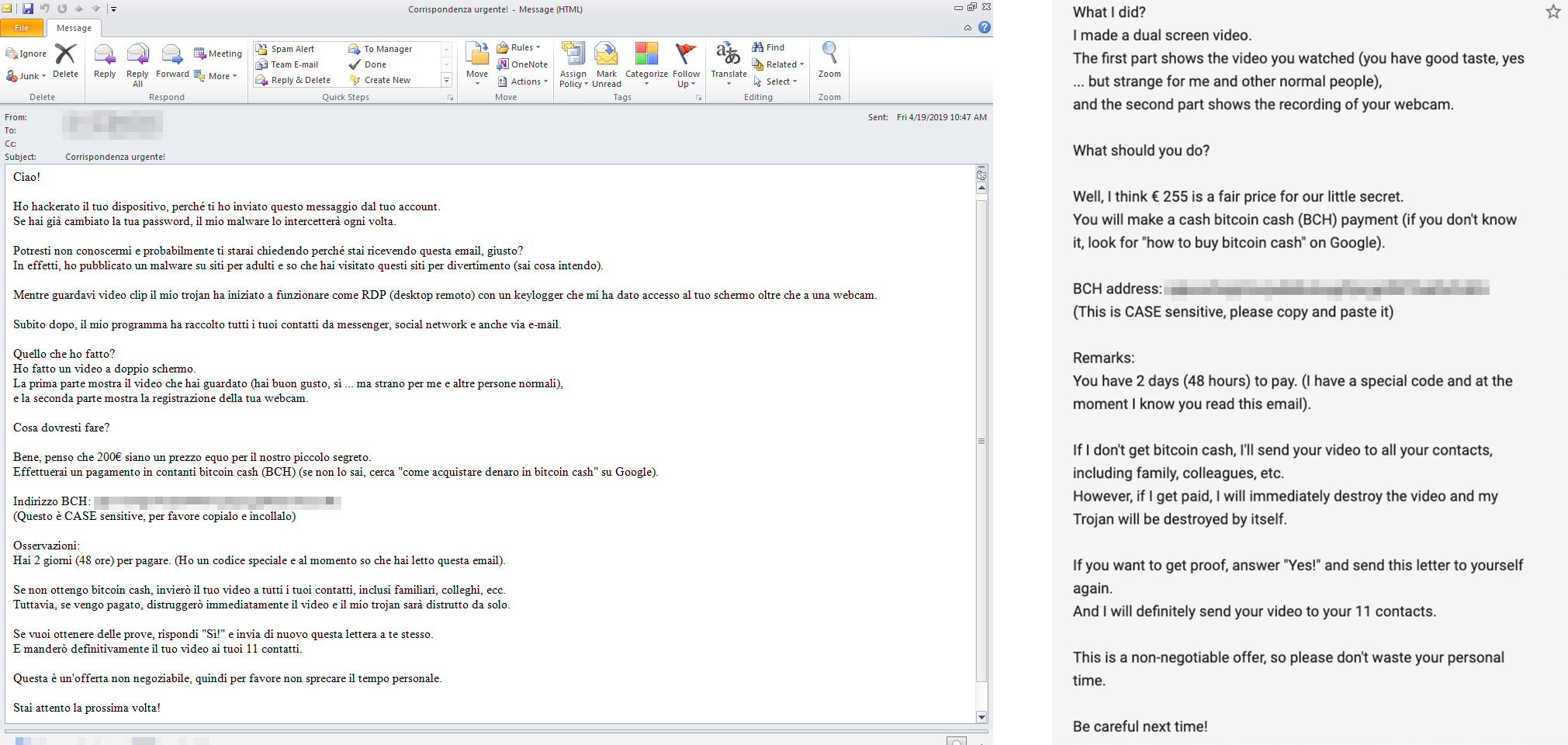
The spam email’s modus is simple. The hacker claims to have hijacked the recipient’s device as well as social media and email accounts. The hacker further claims to have supposed recordings of the recipient watching pornography and the websites the victim supposedly visited at the time. The hacker threatens to send the compromising videos to the victim's contacts unless the victim sends a payment of €255 (around US$258 as of April 24, 2019) within 48 hours. The actual amount varies per email.
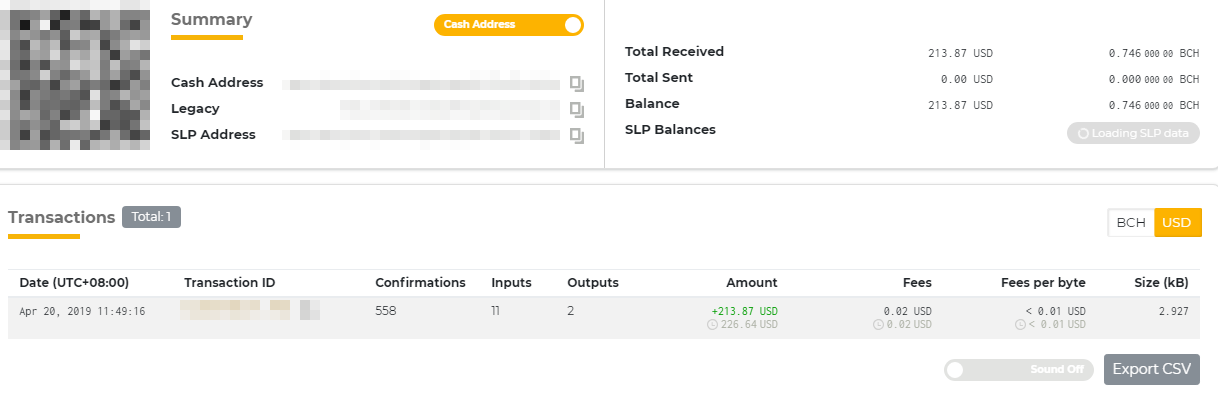
Preying on the victim’s fear could be enough to coerce some into acquiescing to the hacker’s demands. In fact, a look into the Bitcoin Cash wallet indicated in the spam emails showed that a transaction was made on April 20.
Also of note is the actual content of the spam email. It doesn’t appear to be written by a native Italian speaker. The fraudsters most likely used a translation application.
[READ: Digital Extortion: A Forward-Looking View]
This modus comes at the heels of another sextortion scheme that also targets Italian-speaking users, demanding a payment of €600 in bitcoin (US$672) from its victims.
The scam is also a reflection of what Trend Micro predicted: cybercriminals diversifying tactics to extort potential victims. Sextortionists, for instance, reportedly earned over US$330,000 in just seven months using compromised credentials. Sextortion appeared so lucrative that they’re even offering an annual salary of US$360,000 to fellow fraudsters who can help them wrest money from high-income professionals.
Fraudsters also profit from their victim’s fears by posing as a government agency to intimidate them into forking over bitcoins. Other scammers combine sextortion with threats like ransomware and Android malware.
Some of the previous sextortion scams Trend Micro researchers saw also employed techniques to avoid being tagged as spam, such as using misleading subject lines, obfuscating the content (by adding characters) or sending it as an image.
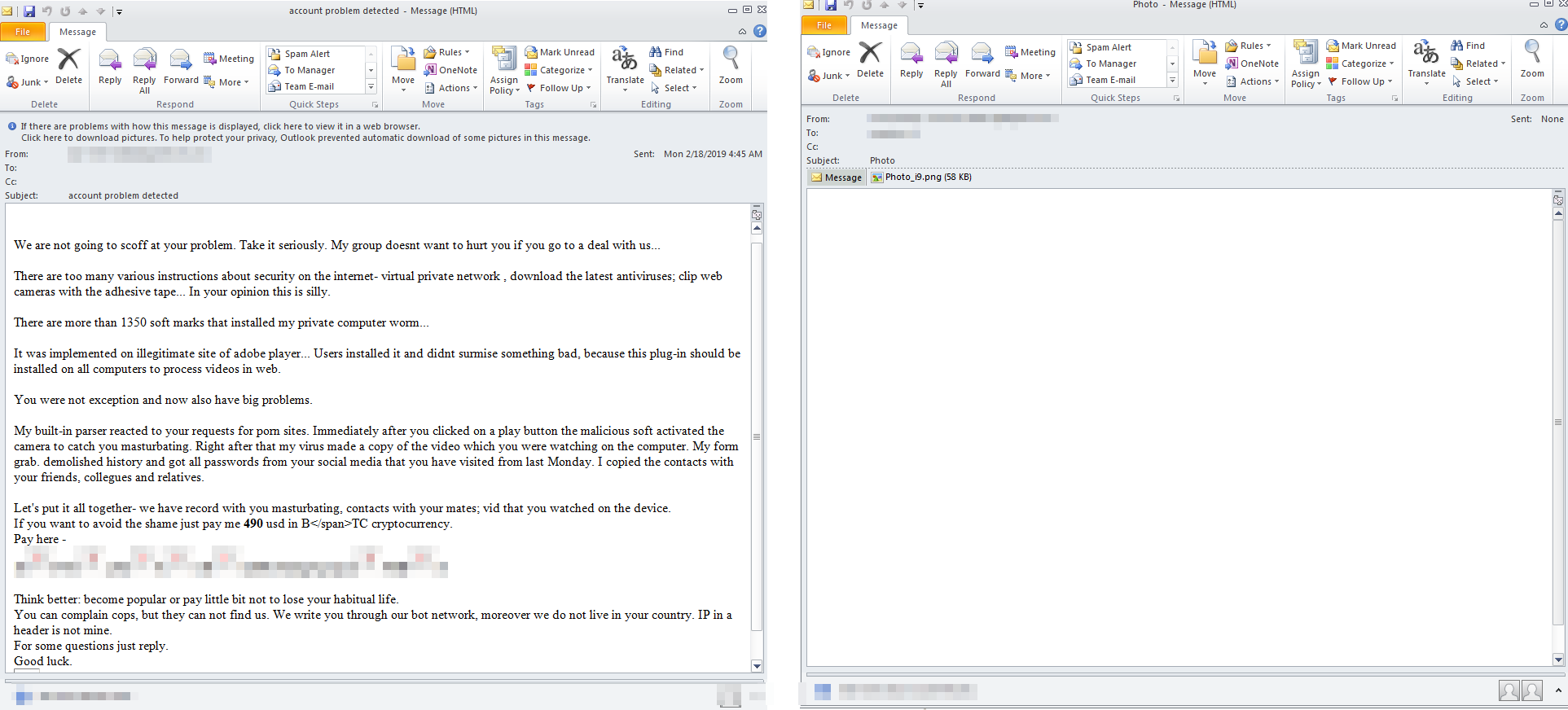
Samples of sextortion emails demanding bitcoin as payment, using techniques to evade being detected as spam
A sample sextortion email targeting Italian-speaking users (left), and a partial English translation via Google Translate (right)
Screenshot showing a transaction made on the Bitcoin Cash wallet address
Dealing with sextortion scams can be tricky given the purposefully sensitive nature of this threat. Here are some best practices that can help users avoid falling for sextortion scams:
- Mind where your personal data is shared or stored.
- Don’t pay and don’t respond. Immediately report the incident to local authorities.
- Strengthen and regularly update your credentials and accounts to lessen the risk of getting your accounts compromised.
- Be wary of links and attachments in unsolicited email.
- Nurture cybersecurity awareness both at home and in the workplace.
Trend Micro™ Security, Smart Protection Suites, and Worry-Free™ Business Security provide comprehensive multi-device protection against threats and phishing scams by identifying and blocking malware and malicious links on websites and in social networks, emails, and instant messages to shield privacy and guard against identity theft. These solutions are powered by Trend Micro XGen™ security, which provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints.
Analysis and insights by Loseway Lu, Marshall Chen, and Jim W. Hsu (Threats Analysts)
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One