Year in Review: Notable Data Breaches for 2017
Data breaches have become one of the most prevalent cybersecurity incidents around the globe, and it seems the trend is going to continue. In fact, more records were stolen and leaked in the first half of 2017 alone compared to the total in the whole of 2016.
Many of the incidents that occurred in 2017 were due to the same causes, which include, but are not limited to:
- Security issues with data storage
- Misconfigured security settings
- Lack of actual security solutions to protect data
- Use of unpatched and unsupported software with exploitable vulnerabilities
It is also important to understand that data breaches are neither purely technical nor are they caused solely by human error. Most times, they are caused by a combination of both.
Organizations can mitigate the impact of data breaches through the use of best practices, which include:
- Patching and updating systems on a regular basis
- Implementing measures that can help identify weak spots in an organization’s security requirements
- Creating contingency plans that can address data breaches, including communication with affected parties
- Use security solutions such as Trend Micro™ Hybrid Cloud Security that can offer effective protection against data breach attacks on the cloud, and Trend Micro Deep Security, which protects millions of physical, virtual, and cloud servers around the world. In addition, TippingPoint can help organizations manage their legacy systems and control their patch management life cycle by providing added protection for legacy, out-of-support software, delivered weekly or when critical vulnerabilities emerge.
To give a better perspective on the impact data breaches had on both users and organizations, here’s a rundown of the most notable incidents of the year, based on the type of breach, impact, and significance of the organization involved.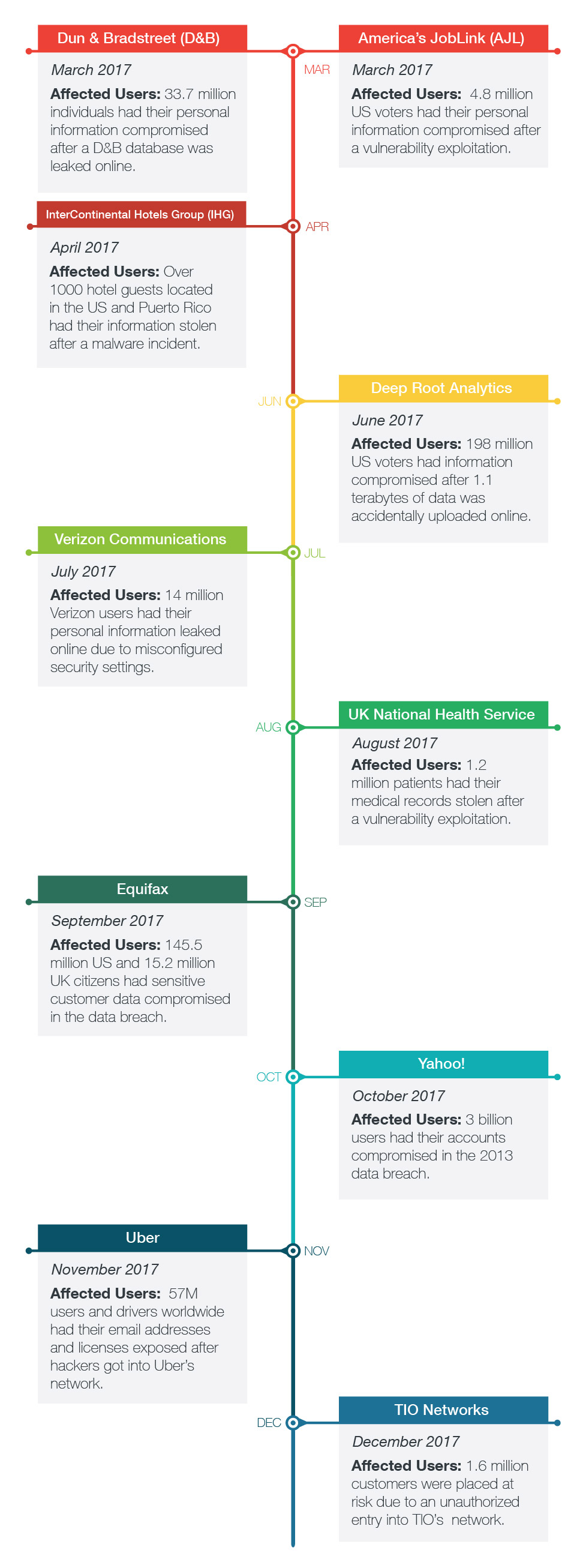
Dun & Bradstreet (D&B) – March 2017
What happened: Data service companyDun & Bradstreet (D&B) was in the hot seat in March after reports emerged that one of its databases was leaked online. The leaked data supposedly included the information of 33.7 million unique individuals in the database.
America’s JobLink (AJL) – March 2017
What happened: A major data breach affected a large number of job seekers across ten states in the US. A hacker managed to exploit a vulnerability in America’s JobLink’s application code, allowing access to the information of 4.8 million job seekers. The exposed data included the names, birthdates, and social security numbers of applicants across multiple states.
InterContinental Hotels Group (IHG) – April 2017
What happened: One of the world’s largest hotel chains, InterContinental Hotels Group (IHG), posted a now-deleted announcement back in April detailing that malware was found in its systems. The malware was designed to access credit card data at multiple hotel locations. Reports put the number of potentially affected hotels at over 1000 in the US and Puerto Rico.
Deep Root Analytics – June 2017
What happened: A major data breach incident in June involved the exposure of 1.1 terabytes of information on more than 198 million US citizens, representing roughly 61% of the voting population. The data was accidentally uploaded to a publicly accessible server by a data firm contracted by the Republican National Committee (RNC).
Verizon Communications – July 2017
What happened: US telecommunications company Verizon made headlines in July after it confirmed that the personal data of its users were leaked online due to misconfigured security settings on one of its cloud servers. The leaked data, which comprised of the information of an estimated 14 million of the company’s 108 million subscribers, included names, phone numbers, and account PINs.
UK National Health Service – August 2017
What happened: The UK NHS was targeted by the hacktivist group Anonymous in August after the group exploited unpatched vulnerabilities in software that developer SwiftQueue uses to manage hospital booking systems. The stolen information included PII, contained 32, 501 lines of administrative data. The attackers also claimed that 1.2 million medical records were stolen in the attack.
Equifax – September 2017
What happened: Equifax announced that sensitive customer data that included millions of credit card and driver’s license numbers were stolen.The hackers reportedly stole the personal information of roughly 145.5 million users as well as driver's license information of an estimated 10 million US citizens. 15.2 million records were stolen in the UK.
Yahoo! – October 2017
What happened: In October 2017, Yahoo! announced that a massive 3 billion accounts—an amount that encompasses all the Yahoo! users at that point—were compromised in a data breach incident that occurred in 2013. Initial reports in December 2016 pegged the number of affected accounts at 1 billion.
Uber – November 2017
What happened: Rideshare application Uber revealed that a data breach potentially involving the data of their drivers and users occurred in October 2016, after hackers managed to log into accounts on Uber’s network hosted on AWS servers. The breach, which was further complicated by the fact that Uber paid the hackers $100,000 to delete the data, wasestimated to affect 57 million drivers and users across the globe.
TIO Networks – December 2017
What happened: Just a few months after acquiring payment processing company TIO Networks, PayPal announced a suspension of operations after discovering that unauthorized access to TIO’s network potentially placed their customers at risk of data theft. The breach itself was announced to have compromised the accounts of around 1.6 million customers.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter
- 2025 APT Report: Staying Ahead of the Modern Threat Landscape

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation