By The Numbers: The Price of Ransomware
When looking at the overall ransomware landscape and how it has exponentially grown over the past couple of years, there is no more poignant number than "50". That's the number of new ransomware families seen within the first five months of 2016 alone—and it only represents the known families.
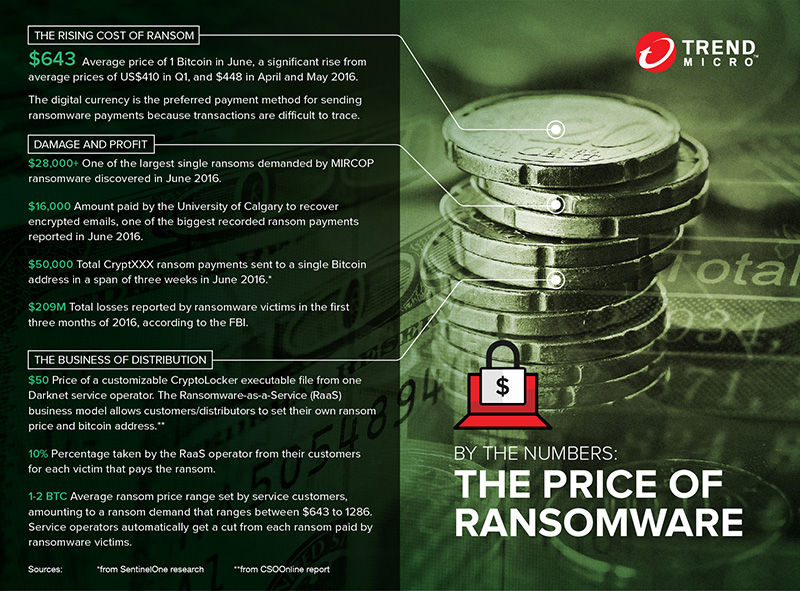
Within that same period, an even greater number of ransomware variants have been spread across different regions and industries, causing more than US$200 million in damages within the first three months of the year, as reported by the FBI. This number only represents reported losses, though. Considering that there are countless victims who either never bothered to report paying the ransom, or chose to not report for fear of reputation loss, the actual number is likely to be far greater than 200 million.
The rapid development and spread of ransomware only points to the fact that it works. And it doesn't just provide a way for independent cybercriminals to make a quick profit, but also as a scalable business model for those who prefer to let others work for them. The ease and profitability has paved the way for Ransomware-as-a-service business models to proliferate in the cybercriminal underground, allowing would-be cybercriminals, termed as "service customers" or "distributors" to purchase a customizable ransomware executable from a service operator or "boss". In return, the boss automatically gets a percentage of each ransom paid to the ransomware distributor.
Each part of the chain, from boss to customer, gets paid big money for little effort. And all it needs to run is to distribute extortion malware that forces victims to make a difficult choice. In a highly digital and connected world where any cybercriminal—from newbies with little to no coding know-how to malware creators with a distribution platform—can profit from extorting individuals and organizations across different industries, these numbers should come as no surprise.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation