Business Process Compromise, Business Email Compromise, and Targeted Attacks: What’s the Difference?
In 2015, an Ecuadorean bank suffered a $12 million loss after attackers obtained the codes used for transferring funds via the SWIFT financial network. The following year, a cyber heist also involving SWIFT was pulled off against the Bangladesh Central Bank, resulting in an $81 million loss. Also in 2016, a Vietnamese bank thwarted a similar attempt of attackers to transfer $1.13 million into their own accounts.
We have classified this new breed of attacks as Business Process Compromise (BPC), in which threat actors silently alter critical processes and the systems behind them, such that they continue to function as normal but yield unauthorized results. But how does BPC work? What makes it unique or similar to Business Email Compromise (BEC) or targeted attacks? How can enterprises spot BPC?
BEC vs. BPC
BPC and BEC have the same end goal (i.e., financial gain), but their similarities end there.
BEC is a scam that relies heavily on social engineering tactics to lure its victims into transferring funds to accounts owned by fraudsters. In carrying out BEC, attackers often impersonate CEOs or any high-ranking executives related to finance or wire transfer payments. BEC has five types, according to the FBI:
- Bogus Invoice Scheme
- CEO Fraud
- Account Compromise
- Attorney Impersonation
- Data Theft
[Read: How does Business Email Compromise work?]
On the other hand, BPC is a more complex attack — it involves modifying processes to generate a different outcome than originally intended. This often leads to significant financial gain for the attackers. Based on the cases we’ve observed, BPC can be classified into three types:
- Diversion
- Piggybacking
- Financial Manipulation
[Read: Types of Business Process Compromise and their sample incidents]
Targeted Attacks vs. BPC
There is a thin line separating targeted attacks from BPC as both use the same tools, techniques, and components to infiltrate and sustain their presence in the target network without being detected. Both remain undetected in the network for an indefinite period. However, the goal of targeted attacks is to exfiltrate the company’s “crown jewels” (trade secrets, intellectual property, etc.) for espionage or sabotage purposes. On the other hand, fraudsters behind BPC are after profit. BPC may also follow the same components as targeted attacks, from intelligence gathering and lateral movement to maintenance and data exfiltration.
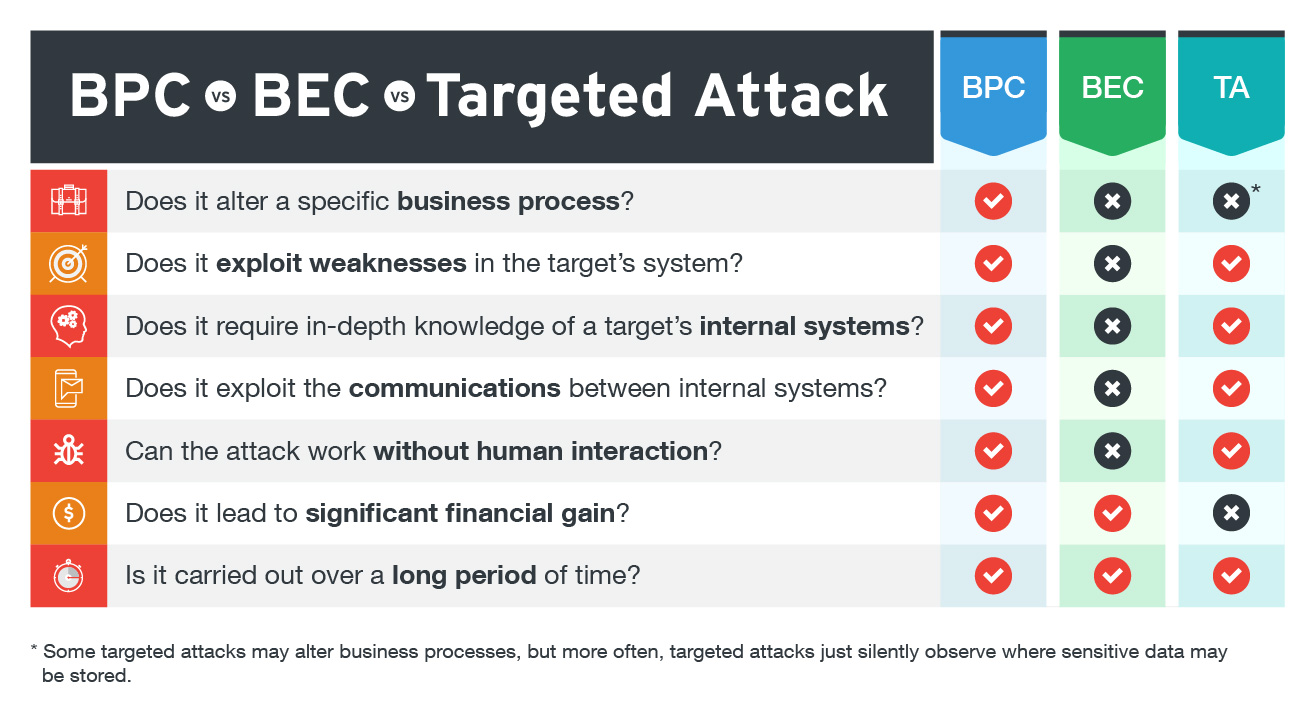 Figure 1. Differences and similarities between BPC, BEC, and targeted attacks
Figure 1. Differences and similarities between BPC, BEC, and targeted attacks
Securing your network against BPC
How can enterprises avoid becoming the next BPC victims? Companies should secure not just their network perimeter but also their business processes or logic, which can be potentially abused. Pen-testing and auditing can spot critical gaps in systems or networks, but these tests should also verify if the security technologies or solutions in place can thwart any attack in case threat actors obtain a high level of access. We also highly recommend hiring an external red team to simulate attack scenarios from various points (technologies, processes, systems, etc.) to cover all bases.
Another key strategy against BPC is separating the responsibilities of employees as this could eliminate the risks of insider threats who could introduce malicious variables. Security trainings and awareness programs on BPC can also aid executives and employees in identifying and reporting BPC.
Learn how you can protect your organization against this threat with these BPC defense strategies.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One