Windows 10 Privacy Issues: There's an "Off" Button for That

Following months of beta testing, Microsoft caused quite a stir last month with the highly-anticipated July 29 release of its PC operating system upgrade Windows 10. And thanks to a lot of hype brought about by its offer of a free upgrade, the new OS was downloaded into 14 million devices in less than 24 hours after its public release. The number of downloads has since more than quadrupled to 67 million in less than a week after the rollout.
This means that a huge chunk of Windows users have already begun experiencing added features and improvements that came with the update—from the return of the missing Start menu and the introduction of a personal assistant named Cortana, to a faster web-browsing experience courtesy of Edge.
Security enthusiasts have called it the “Goldilocks version“of Microsoft’s operating system that manages to merge the dependability of Windows 7 with the forward-looking touchscreen vision of Windows 8. Collective feedback from a mixture of users, Microsoft employees, and other sources have also recognized efforts put forth to address modern security threats by adding features that improve identity protection, access control,data protection, and threat resistance.
Windows 10 privacy issues?
Shortly after the initial hype of the launch, Microsoft also received flak about several security deficiencies that came with such developments, particularly those that pertain to user privacy. Windows 10 got some backlash over claims of extensive power the operating system gets over a user’s personal information. According to online privacy group European Digital Rights (EDRi), Microsoft “grants itself very broad rights to collect everything you do, say, and write with and on your devices”.
This means that the moment you agree to install the update, the OS—or Microsoft rather—is given autonomy over your information from telephone numbers, credit card credentials, GPS locations, your browsing history, and even your video and audio messages. All of this are carefully stipulated and outlined in the Microsoft privacy statement. However, the contention is on the why. Questions and reactions have sprung up regarding the motivation that drives this collection of supposedly private data.
Microsoft states in its term of service that this is done primarily to learn more about the user, leaning more on personalizing services that it offers. Privacy advocates, on the other hand, stressed that this merely serves the purpose of selling mined data to third parties for more targeted advertising.
For instance, one issue involves the assignment of an automatic advertising ID set to each user with a device linked to a registered email address. This means that your web browsing history and app-use actually shape how future ads will look like. So, don’t be surprised if you see ads that involve your favorite band or even the latest shopping trends you keyed in on your search engine.
Another privacy issue involves the way it synchronizes your personal data with Microsoft servers, which means that every time you log in to navigate your system, data like browsing history, recently-visited pages, downloaded apps, and even Wi-fi network details get collected and uploaded to the company servers.
WiFi Sense, a feature which basically allows your Wi-fi connection to be shared to anyone on your contact list, be it on Skype, Outlook and Hotmail, raised red flags for some concerned parties. However, this is not the case. Amidst criticisms received by this feature, there are those who argue that WiFi Sense is not a violation of privacy because the user is given the liberty and control whether to share his or her network or not—and it's clearly not something that can be shared “by accident”. And even if this is turned on, WiFi Sense merely shares access to Internet connection, not your password or more importantly, your personal files.
Cortana has also received negative attention as it was deemed a rather nosy virtual assistant. While it's designed to provide personalized experiences and relevant suggestions, how it does this looks highly-intrusive. According to its privacy policy, “Microsoft collects and uses various types of data, such as your device location, data from your calendar, the apps you use, data from your emails and text messages, who you call, your contacts and how often you interact with them on your device.”
The biggest concern involved the perceived power given by the users to Microsoft to share and disclose data, “We will access, disclose and preserve personal data, including your content (such as the content of your emails, other private communications or files in private folders), when we have a good faith belief that doing so is necessary to protect our customers or enforce the terms governing the use of the services."
Such is the case with BitLocker. Users who utilize this to encrypt hard drives are given decryption keys that are automatically uploaded and backed up via their OneDrive accounts, making it within reach to parties and agencies who have access to the company’s cloud.
Just turn it off
While there is no denying that Microsoft is far from being the only company that offers personalized services by collecting user information, the ire directed towards these so-called violations are all anchored on the fact that these are default settings that users could easily disable once they click install. And even if Microsoft is transparent in outlining the breadth of data they collect from their users, privacy advocates note that it could have been more appealing to the public had they taken a more “privacy-friendly stance” in allowing Windows 10 users to opt-in if they are interested to enable these said features rather than having them running by default.
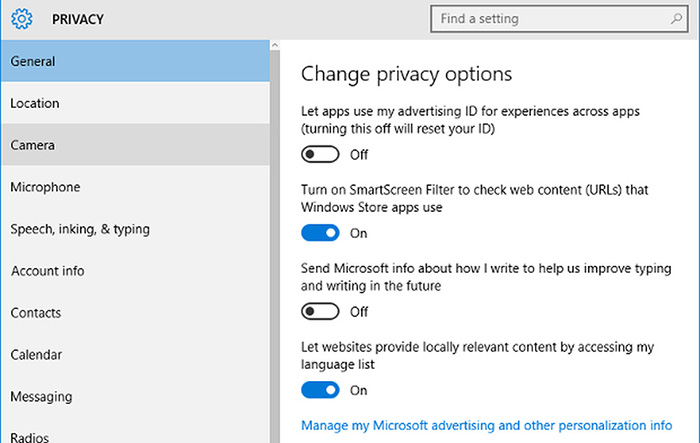
Are users really exposing way too much information when they use Windows 10? They might—if they just accepted everything without knowing what they're enabling. It's more of a question about user awareness. Start by reading the Terms of Service (for anything you download and install) to know which information is being collected. Just like in the case of WiFi Sense, the settings of these said features can be managed to control what kind of information you are willing to share. Just visit the Privacy menu to change how the system handles your data.
For further protection from a wide range of threats, Maximum Security 10 by Trend Micro is fully compatible with Windows 10 and works on multiple devices. Click the link for a free trial.Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter
- 2025 APT Report: Staying Ahead of the Modern Threat Landscape

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation