Real Threats Found in Virtual Gaming Consoles
10 września 2014
 View infographic: Ahead of the Game
View infographic: Ahead of the Game
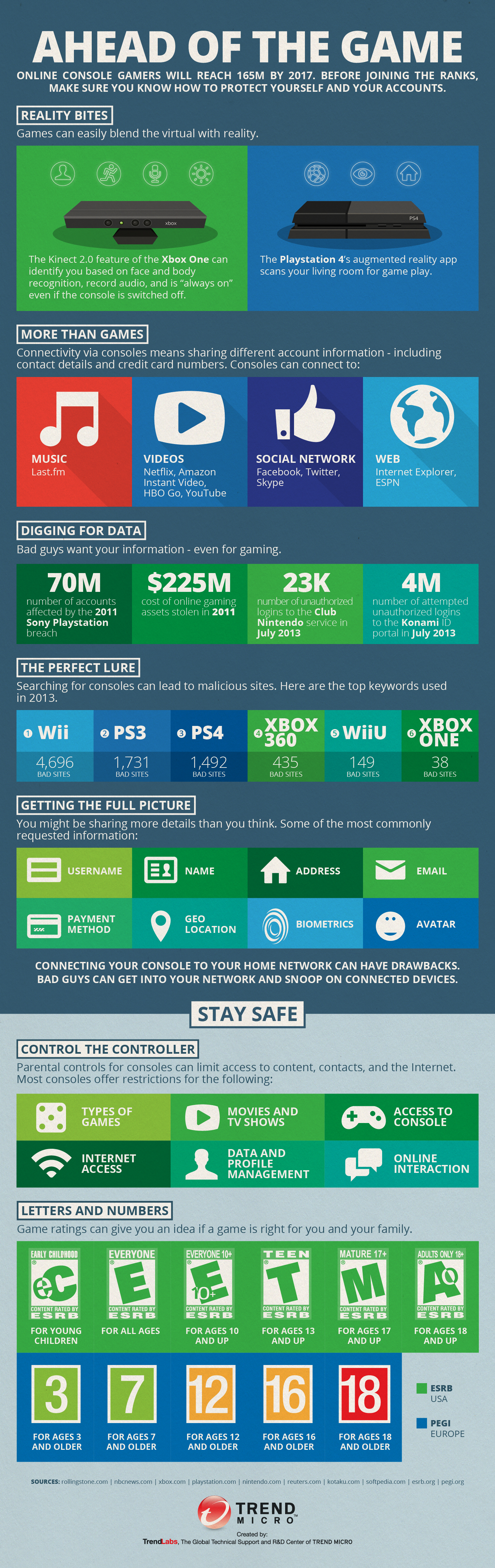
Truth is: games can easily blend the virtual with the real.
For example, you get the Xbox One Kinect 2.0 feature. It records your voice and takes note of your face and body details. And since it’s “always on,” you know that your information is already saved and stored. Pair that with the PlayStation 4 scanning your living room for gameplay—data of you and your living room are fed into the virtual realm.
Games today are very unlike yesteryears’ playing cards and board games. They now ask for account information and contact details so they can link you to your favorite music, play your subscribed videos, browse the web, and even post on Facebook or Twitter on your behalf. Since these details are linked to your name and gaming profile, cybercriminals deem them valuable. In 2011, for example, cybercriminals stole 70 million Sony PlayStation accounts. In the same year, $225 million online gaming assets were stolen. That’s a lot of money, but how do cybercriminals get to it?
Cybercriminals set up lures for online gamers. They poison search results for gaming consoles. When you type in Wii on a search engine, chances are you will land on one of 4,696 bad sites that lead to data-stealing threats, including phishing pages that solicit your information. Before you hand over your personal information or payment details, ensure you are on the official site by double-checking links and branding marks.
Stay safe while playing by staying in control. For instance, be aware that connecting your console to your home network may lead to bad guys snooping in your system. For those with kids, restrict access to common features like type of games, movies and TV shows allowed, Internet use, and online interaction so consoles can only connect to kid-friendly and secure sites. It’s all about being ahead of the game.
HIDE
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation