SCADA In The Cloud - A Security Conundrum? [blog]
Two of the hottest buzzwords circulating in the IT world today are “SCADA” and “cloud computing.” Combining the two technologies has been talked about and is starting to garner more attention because of the potential cost savings, system redundancy, and uptime benefits.
Like most IT companies, industrial control system (ICS) devices can benefit from cloud use. The cloud is and will remain a viable business additive for traditional IT worldwide. SCADA devices do not differ from IT devices in that they also require redundancy, security, reduced costs, and uptime. There are several ways that SCADA in the cloud can be approached and installed, but each has their own potential security issues.
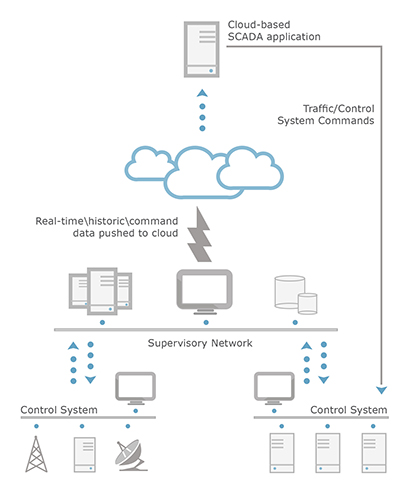
Figure 1. Example of SCADA application hosted in the cloud
Broadly speaking, there are two ways SCADA can be deployed in the cloud. It can either be completely in the cloud, or only partially. Whichever method is used, there are security concerns that should be considered and addressed prior to implementing SCADA in the cloud in any fashion. These include:
- lack of authentication
- lack of control
- lack of encryption
- nature of data
- the logging conundrum
- web application attacks
My paper SCADA in the Cloud- a Security Conundrum discusses not only these concerns, but also how to address these potential problems.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation