From May 6 to December 31, 2019, Trend Micro recorded and analyzed cyberattacks on a factory honeypot that precisely mimicked a factory environment. This blog describes the results of a 240-day cyberattack sting based on research published by Trend Micro on January 21, 2020. What cyberattacks on factories were actually observed and how often did they occur? And to what extent did those attacks affect the factory environment?
Attack Frequency: 30 cyberattacks observed in 240 days
First, let's look at the frequency of cyberattacks on the factory honeypot. During the 240-day sting operation, 30 cyberattacks were observed, which equates to about one intrusion a week.
Table 1 lists the 30 cyberattacks in chronological order.
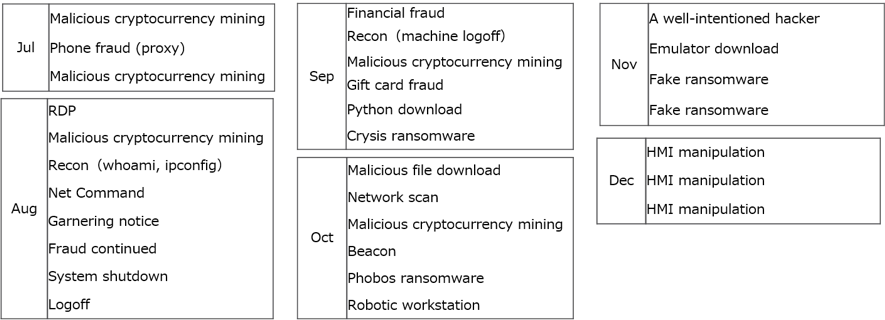
<Table 1> List of cyberattacks observed in the honeypot
Attack Types: Mainly IT-based but no ICS-specific attacks
Let's look at the details of these attacks. The following attacks have something in common.
- Unauthorized cryptocurrency mining x5
- Using the system as a proxy for cyberattacks x4
- Ransomware infections x2
- Fake ransomware infections x2
These 13 cyberattacks, which account for about 40% of the total, seek to directly or indirectly make financial gains. However, those attacks are IT-based, not OT-specific attacks.
The rest of the cyberattacks were as follows:
- Changing/manipulating environment settings x8
- Program downloads from outside x5
- Internal reconnaissance x2
- Warnings from security researchers x2
15 of these attacks, excluding warnings from security researchers, were so-called ad hoc attacks whose purpose could not be clearly read. In this research, Trend Micro recorded and analyzed all attacks that infiltrated the honeypot, but these 15 cases did not show the attackers' capabilities or potential. In other words, there were no signs of environmental changes or manipulations after thoroughly observing the environment under attack, or no intentional movements intended to steal or disrupt data.
Surprisingly, no data was stolen from the honeypot despite a total of 30 intrusions. Based on these facts, it seems that the attackers did not set out to infiltrate a factory; instead, we can conclude that the victim happened to be a factory.
Attack Impacts: Six attacks affecting factory operation
Let's see if there was any effect on factory operation. In this research, we confirmed six cases of factory shutdown due to cyberattacks. The red cases in Figure 2 are the cyberattacks that shut down the factory. The breakdown by attack type is as follows.
- Ransomware infection x2
- Changing/manipulating environment settings x4
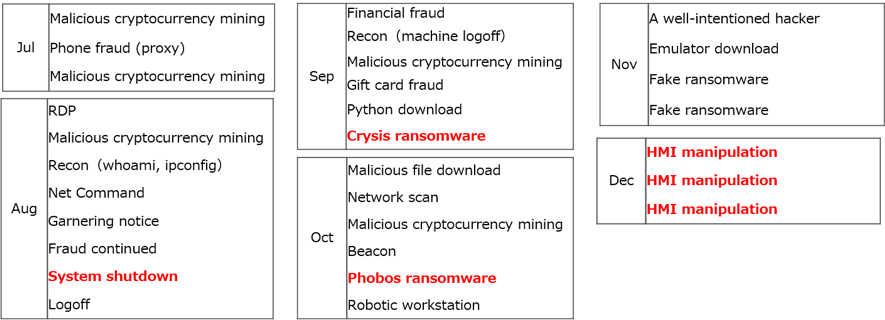
<Table 2> Cyberattacks affecting factory productivity
It should be noted that even attacks that aren't specifically aimed at factory environments can still affect factory operation. For example, ransomware attacks encrypt PLC logic files or other data, rendering them unusable unless a ransom is paid. This results in the termination of factory operation. Even if an attacker is not aiming specifically at a factory, a cyberattack can still stop a factory.
Attackers are unlikely to be familiar with factory environments
Let's take a look at an interesting case study. Trend Micro, posing as the victim, contacted the person behind the September Crysis ransomware attack. The steps were as follows.
- A Crysis ransomware attack encrypted data on a file server.
- Trend Micro pretended to be the CISO of the honeypot company and sent an email to the address listed on the warning screen displayed after encryption.
- The attacker replied to the email, demanding payment of the ransom in cryptocurrency.
- Trend Micro (pretending to be the CISO) told the attacker that, "There is no guarantee that you are the attacker and that the data will be recovered. I cannot pay under these circumstances."
The attacker then replied to the email. Picture 1 is the actual email.
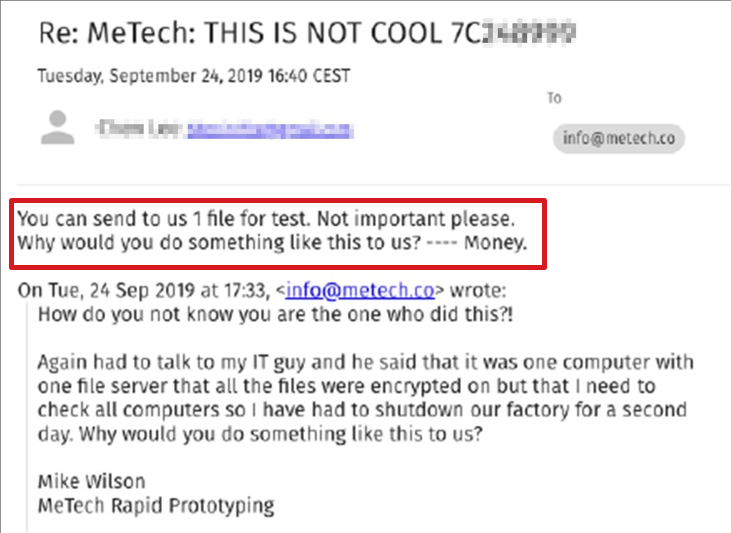
<Picture 1> Email from Crysis ransomware attacker
The sentences in the red frame are from the attacker. Trend Micro followed these instructions and sent a file to the attacker. However, the selected file was the PLC logic file at the core of factory operation. If the attacker had sufficient knowledge of factory environments and data, he would not have decrypted the file. If the victim could get back this essential data, they wouldn't have to pay the ransom. Shortly thereafter, the attacker replied with the decrypted PLC logic file. There may not be many attackers who are familiar with factory environments at the moment. However, it should be noted that such cyberattacks still affect factory operations.
Conclusion: Factories need cybersecurity
In this blog, we have examined the results of cyberattacks on the honeypot. From our research and analysis to date, we have gained the following insights into the frequency and impact of cyberattacks on factories:
- Factories suffer cyberattacks. On average, cyberattacks are observed once every eight days.
- Many cyberattacks on factories are unlikely to be specifically aimed at factories.
- Even if the attack is not specifically aimed at a factory, it will affect the operation of the factory.
Not surprisingly, there are factory-specific cyberattacks; however, knowing the type and frequency of cyberattacks helps us prioritize security investments. We hope that the results of this Trend Micro research will serve as an indicator of the type and frequency of attacks and provide hints for factory security.

