Industry-leading
AI Security Platform

Built for AI.
Ready for next.
Eliminate risk, defeat threats, and accelerate innovation. Built for the AI age, TrendAI Vision One™ secures the entire enterprise to protect your people, operating infrastructure, and data against AI-enabled adversaries.
Visibility
Eliminate security blind spots with a comprehensive view of your entire digital estate.
Prioritization
Focus on what matters most - our platform evaluates and ranks security issues based on business impact and urgency.
Mitigation
Using proactive security, we identify, prioritize, and resolve risks in real time, so you can lead your market, not chase threats.
Adaptive platform. Real security outcomes.
TrendAI Vision One™ is an easy-to-deploy, AI-ready enterprise platform, backed by world-leading threat intelligence and a relentless commitment to your success. Turning insight into action, TrendAI™ transforms security from reactive threat response to strategic risk management – making security an enabler of growth, not a barrier.
70%
Reduction in cybersecurity costs
99.6%
Reduction in daily alerts
65%
Reduction in dwell time
92%
Reduction in cyber risk

Economic valuation from ESG
See how TrendAI Vision One™ delivers measurable ROI.
Use, build, and run AI securely.
TrendAI Vision One™ protects AI usage and development to deliver seamless governance and threat protection at every layer, ensuring enterprise compliance without slowing innovation.
- Adopt and scale AI initiatives without fear of security gaps or compliance violations.
- Gain clear insight into AI risks and usage patterns, enabling informed decisions and policy enforcement.
- Protect AI apps and agentic systems from development through production – reducing exposure to prompt injection, data leakage, runtime attacks, and autonomous agent misuse.
Autonomous security operations leave attackers nowhere to hide.
TrendAI Vision One™ is the only enterprise cybersecurity platform that centralizes cyber risk exposure management, security operations, and robust layered protection. It empowers you to predict and prevent threats while accelerating proactive security outcomes.
- Context-rich detection for faster response
- AI-driven threat hunting and analytics
- Automated workflows for improved efficiency
Lead the future of AI with proactive security
– where innovation thrives without risk
We protect your entire enterprise – safeguarding people, infrastructure, and data against AI‑enabled threats. We take the cyber worry out of AI so you are free to be your AI best.

AI Security
Protect AI usage and development to deliver seamless governance and threat protection at every layer, ensuring enterprise compliance without slowing innovation.

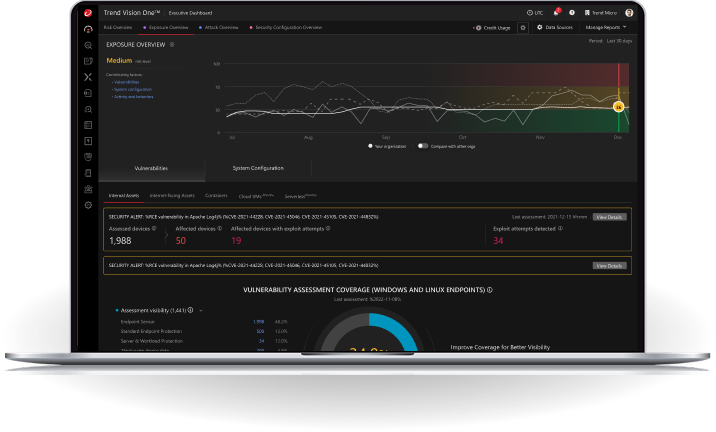
Cyber Risk Exposure Management
Proactively uncover, predict, assess, and mitigate cyber risks – prioritizing impact, reducing exposure, and building cyber resilience.

Security Operations
Detect, investigate, and respond proactively with the power of XDR, Agentic SIEM, and Agentic SOAR.

Data Security
Comprehensive protection for sensitive data spanning on-premises and cloud environments.

Cloud Security
Comprehensive security for rapid prediction, protection, and response to threats. Enhance visibility, cloud risk management, and operational efficiency on your cloud and hybrid cloud security journey.

Endpoint Security
Secure all endpoints, laptops, PCs, mobile, servers, and workloads against sophisticated threats. Gain centralized visibility, threat correlation, and rapid response to contain attacks before they spread.

Email Security
Proactively manage human risks and stop threats with speed, ease, and accuracy. Stay ahead of phishing, BEC, ransomware, and scams with AI-powered email security.


Identity Security
Eliminate breaches in today's boundaryless workplace with complete visibility, intelligent prioritization, and automated mitigation of identity risks.

Network Security
Gain unparalleled network insight, detect threats, protect unmanaged devices, and prevent attacks. Accelerate real-time threat prevention, intrusion detection, and zero trust access controls.
Predict, prevent, and protect with elite actionable threat intelligence
Stay ahead of emerging threats with deep insights from TrendAI™ Research, one of the world’s largest cybersecurity research networks.
Global threat visibility
Access context-rich visibility into active attacks, threat actors, and global trends from our research network.
Real-time threat detection
Predict and prevent attacks using AI-driven analytics to identify emerging threats before they impact your business.
Proactive defense strategies
Stay ahead of adversaries with industry-leading TrendAI™ Zero Day Initiative™ (ZDI) intelligence, detecting and mitigating vulnerabilities before they can be exploited, up to 3 months ahead of a patch.
Our expertise is your security advantage
Augment your security teams with services that bring you peace of mind. Focus on strategic priorities while improving overall security efficiency.
Managed detection and response (MDR)
The expertise, technology, and resources you need to detect threats in real time across all security layers.
Incident response services
Expert assistance to contain, remediate, and recover from attacks.
Comprehensive 24/7 support
Priority issue resolution, on demand training, and expert guidance.
One license, unlimited access
Unlock a flexible, scalable, easy-to-use universal licensing model. Allocate or reallocate credits across 30+ TrendAI Vision One™ solutions and capabilities – anytime, hassle-free.
See it in action:
Experience proactive security designed to inspire innovation and eliminate risk.
Get a closer look at the AI-ready enterprise platform and services, powered by world-leading threat intelligence, and a relentless commitment to your success.
Measurable results. Measurable impact.
Leader in cloud security
Top performance in end-to-end cybersecurity



Thrive in the AI era.
Stay ahead of emerging threats with proactive, intelligent security.








