Cyber Threats
Fake Company, Real Threats Part 1
Trend Micro recorded and analyzed cyberattacks by building and using a factory honeypot that precisely mimicked a factory environment. This first part of the series explains the quantity and quality of cyberattacks on the factory based on a research.
From May 6 to December 31, 2019, Trend Micro recorded and analyzed cyberattacks by building and using a factory honeypot that precisely mimicked a factory environment. This column examines the quantity and quality of cyberattacks on the factory based on research released by Trend Micro on January 21st, 2020.
We explain the purpose of this research and the features of the Trend Micro factory honeypot below.
Purpose: To measure the frequency and impact of factory cyberattacks
"How often are factories under attack, and what kinds of attacks do they suffer?"
This is a very important question for manufacturers because knowing the type and frequency of cyberattacks on your plant can help you decide what security measures to take and how much to invest in them. To answer this question, Trend Micro conducted a survey using a "real" factory as a honeypot.
Malware such as Stuxnet is a common example of a cyberattack on industrial control systems (ICS). Such malware is unique in that it's designed for specific environments like factories. However, attacks that intentionally target manufacturing environments are only the tip of the iceberg of all cyberattacks on plants. When considering security, it's important to understand the full picture of attacks to determine the most effective security measures. In making that assessment, knowing the frequency and type of cyberattacks on factories provides a great hint for making correct cybersecurity investment decisions.
So, what's the best way to measure the actual status of cyberattacks on factories? Trend Micro decided to build a factory honeypot indistinguishable from a genuine factory to observe and analyze real cyberattacks on the honeypot.
Method: Building a factory honeypot and a fictitious company
1. Deceiving scanners with a sophisticated honeypot
It is surprisingly difficult to create a fake factory system that is indistinguishable from the real thing. To make this decoy investigation successful, you need to deceive two types of opponents: an attacker (human) and a scanner, for attackers often use scanners to search for vulnerable IP targets. Picture 1 is an actual example where a scanner has determined an IP as a honeypot.
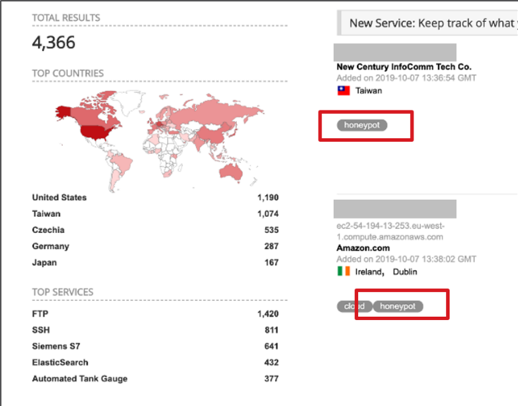
<Picture 1> Scanner screen example: "Honeypot" tag is attached.
How does the scanner know that it's a honeypot? Because some honeypots have unusual settings which never appear in real environments. For example, the scanner determines a honeypot if all network ports are open, it's linked to a well-known honeypot program such as Honeynet, it operates only in a virtual environment despite being a factory, or it has zero internal communication. This means that building and running a sophisticated honeypot takes not only time and effort but also highly specialized knowledge of cybersecurity, factory networks, and equipment.
Based on the above conditions, Trend Micro built a honeypot system that was as close as possible to an actual factory environment with feedback from factory security experts. Figure 2 shows the overall architecture of the system.
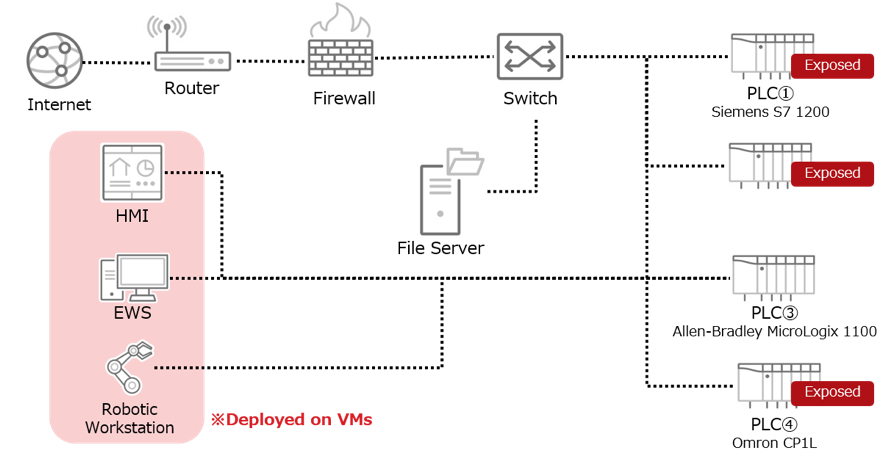
<Picture 2> Overall architecture of the honeypot
This honeypot consists of IT components such as a router, firewall, and file server as well as widely used OT components, including PLCs and HMIs. Another major feature of this honeypot is the use of physical equipment used in actual factory environments. As a result, the scanner judged the honeypot to be an ICS (Industrial Control System).
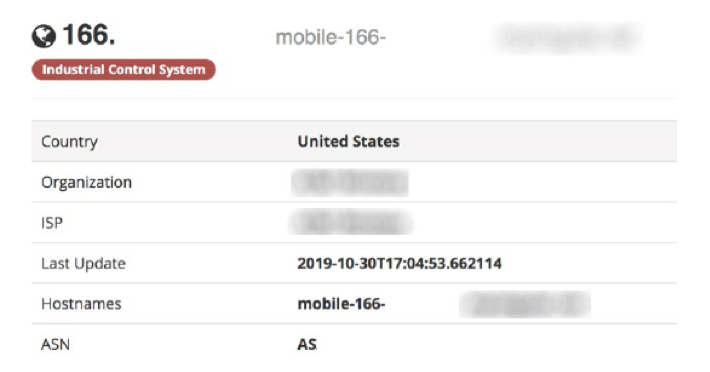
<Picture 3> Scanner showing Trend Micro honeypot
2. Deceiving attackers with a "honeypot company"
The ruse also required cyber actors to believe this was a real factory. Moreover, the target had to be attractive enough for attackers. So, Trend Micro created a "honeypot company," posing as a small industrial prototyping boutique working for special customers. The honeypot company is fictitious but looks realistic. We also created a website and fictitious employee data with AI-generated photos (Picture 4). These employees look real but do not exist.
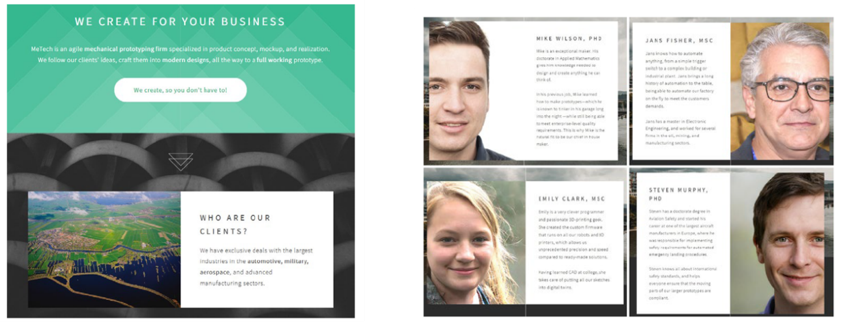
<Picture 4> Homepage of "honeypot company" and employee data
The fake company also has a phone number and email address, which could be contacted. In order to make it an attractive target for attackers, the website stated that the company was a contractor for large enterprises.
This attempt was successful. In fact, external security researchers even warned us that there was a problem with the security measures at this honeypot plant. During the 240-day honeypot operation, we had two such reports from security researchers hackers, meaning the honeypot factory was realistic enough to deceive third-party security researchers hackers.
After careful preparation, the honeypot was released on the internet on May 6, 2019. 30 cyberattacks were observed during the 240 days, six of which affected factory productivity.
In the second part of this blog, we'll take a closer look at the cyberattacks we observed.

