Apple Pay, Google Wallet, NFC, and RFID: Is Your Mobile Payment Option Holiday-Safe?
 They say the holidays bring out the best in people. However, in a world where evolving cybercrime tactics are out to get people’s information, the holidays can also cause the worst digital life experiences.
They say the holidays bring out the best in people. However, in a world where evolving cybercrime tactics are out to get people’s information, the holidays can also cause the worst digital life experiences.
Come Thanksgiving, Black Friday, or Cyber Monday, you might be inclined to either go online to do some shopping or fall in line in actual stores to take advantage of the sales to mark the start of the shopping season. Either way, you’re probably buying something.
[Read: A Guide to Avoiding Cyber Monday Scams on Mobile]
If you’re shopping online using your mobile device on Thanksgiving Day, you’re not alone. Analysts predict that more than half of all online shopping transactions on Thanksgiving, roughly 53 percent, will come from a mobile device, up 23 percent year-over-year.
Mobile payments may be convenient for people armed with smartphones that support it, especially over the busy holiday shopping season. The problem with using popular technology is that threats are always sure to follow, the same way they did with cloud computing and the Android platform.
“New mobile payment methods will introduce new threats,” say security experts in the Security Predictions for 2015 and Beyond report by Trend Micro.
Before you whip out your devices to pay for something, check out this roundup of mobile insights and incidents we've seen so far:
Apple Pay
Even before it rolled out, Apple's new mobile payment system got the public excited despite constant reports of other companies with competing systems rejecting it. Apple Pay presents itself as a secure payment option, going as far as saying, “Apple doesn’t know what you bought, where you bought it and how much you paid for it. The transaction is between you, the merchant and your bank.”
Since its release last October, we have yet to see threats targeting the Apple Pay technology. However, we can't discount the fact that cybercriminals will still bank on its popularity. As such, everyone has to watch out for social engineering attacks that mention Apple Pay, either through related ads or posts that may have poisoned links or downloads.
Google Wallet
The Google Wallet app has gone through a bit of a rough patch on its first version. In February, a proof-of-concept software exposed a vulnerability in the Google Wallet app that can be used to reveal the PIN code of the user in seconds. This flaw has since been patched by Google.
In answer to this, Google has released a new cloud-based version of the app. "The Google Wallet app now stores your payment cards on highly secure Google servers, instead of in the secure storage area on your phone," posts Robin Dua, Head of Product Management, on the company blog.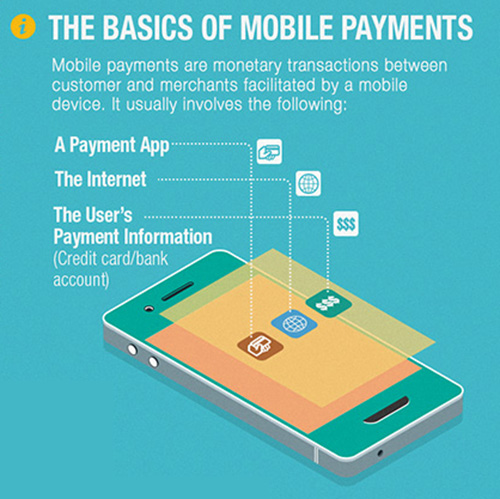 [View Infographic: The Security of Mobile Payment Options]
[View Infographic: The Security of Mobile Payment Options]
NFC/RFID
In the case of NFC and RFID, two very similar technologies with varying uses and range of smart tag reading/writing capabilities, security problems are a well-known risk, though not quite yet in mobile devices.
However, the possibility exists that the NFC and RFID technologies found in mobile devices can be attacked for data theft purposes. This is especially as we have already seen a high-risk Android app hacking into RFID payment cards.
“Using widely available tools, the attacker cracked the card’s authentication key. With the cracked key and the native NFC support in Android and the device, cloning a card and adding credits can be easily implemented in a mobile app,” writes Trend Micro mobile threats analyst Veo Zhang in a blog post.
In addition, three other kinds of MIFARE-based smart cards, a social security card with banking service, a payment card for transportation and shopping, and a dining card, were previously known to be vulnerable to attackers. If this family of chips widely used in contactless smart cards and proximity cards was already compromised, chances are that cybercriminals are working on how to attack NFC and RFID technologies in mobile devices as well.
Safe Online Shopping During the Holidays
Enjoy the convenience without having to worry about your privacy leaks or data theft. Here's how to ensure a safe mobile shopping experience:
- Lock your mobile device. In general, devices have to be turned on or unlocked before they can read any NFC tags.
- Turn your NFC off when not in use, both for security and to save on your mobile's battery.
- For passive tags, use an RFID/NFC-blocking device (such as a wallet). Passive tags will emit fixed information in the presence of a NFC field, which means that there is a slight privacy risk carrying around these devices – if a blocking device is not used.
- Use an NFC reader app on your mobile device. By default, most mobile devices will simply open a URL if one is detected on an NFC tag. The apps will be able to tell you what information is on the tag – allowing you to make an informed decision if you want to scan it or not.
- Be wary of social engineering scams that use the hook of popular mobile payment options to get you to click. This might lead to malicious sites that download malware on your device.
- Scan your mobile devices for unwanted apps, spyware, or other threats that may siphon information from your mobile payment apps.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation