The SMB Problem: PoS Malware, Skimmers, and Compromised PoS Machines
 In the third quarter of 2015, small and medium-sized businesses (SMBs) accounted for 45 percent of the incidents involving PoS malware, and it's not difficult to explain. SMBs hit the sweet spot of being easy and lucrative targets compared to bigger companies with more sophisticated security measures. Trend Micro researchers recently found a botnet that looks for PoS systems within networks. Tagged as Black Atlas—as a nod to BlackPOS, the malware primarily used—the operation doesn’t specifically target SMBs, but they're likely to be the most affected.
In the third quarter of 2015, small and medium-sized businesses (SMBs) accounted for 45 percent of the incidents involving PoS malware, and it's not difficult to explain. SMBs hit the sweet spot of being easy and lucrative targets compared to bigger companies with more sophisticated security measures. Trend Micro researchers recently found a botnet that looks for PoS systems within networks. Tagged as Black Atlas—as a nod to BlackPOS, the malware primarily used—the operation doesn’t specifically target SMBs, but they're likely to be the most affected.
Unfortunately, malware isn't the only threat that affects card payment systems. Cybercriminals have another way of getting their hands on payment data through skimming.
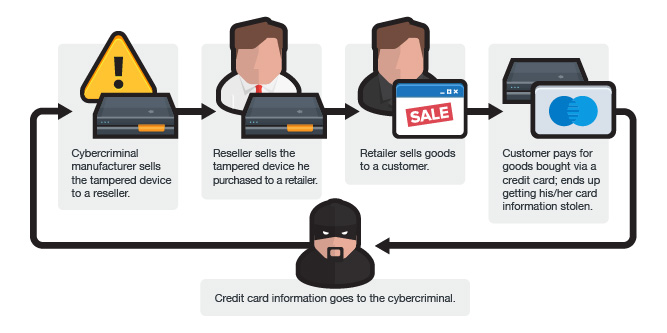
Skimming involves installing a device called a skimmer in a merchant’s card payment system to collect payment card data. Some SMBs unknowingly buy PoS devices sold for cheap in underground markets that have already been compromised even before it gets used. Once these are installed as part of a retailer's payment system, it can collect customers' payment data when a card is swiped at the till during a transaction.
[More: The Evolution of Point-of-Sale (PoS) Malware]
Modified PoS devices can be found being peddled on underground forums. Our research on the Chinese cybercriminal underground activities shows that skimmers can also feature SMS-notification, allowing cybercriminals to instantly receive stolen data via SMS the moment the tampered devices are used. This way, they won’t even need physical access to collect information from the devices.
This year, US merchants have been adopting EMV payment technology, which addresses some of the weaknesses that have facilitated PoS malware attacks. While chip-and-PIN cards can help curb card fraud by adding a number of verification processes, it's not a guaranteed solution since a skimmer can still access data. Some PoS skimmers have also been found featuring PIN pad skimmers, essentially busting the security layer provided by personal identification numbers on newer payment card tech.
Learn more about PoS, ATM, and credit card skimmers sold in underground markets in Prototype Nation: The Chinese Cybercriminal Underground in 2015.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation