Phishing Site Uses Netflix as Lure, Employs Geolocation
Additional insights and analysis by Monte de Jesus

A phishing site was found using a spoofed Netflix page to harvest account information, credit card credentials, and other personally identifiable information (PII), according to a twitter post by PartnerRe Information Security Analyst Andrea Palmieri. We looked into the malicious site, hxxp://secure-up-log.com/netflix/, to learn more about the operation and found that the sites have geolocation features.
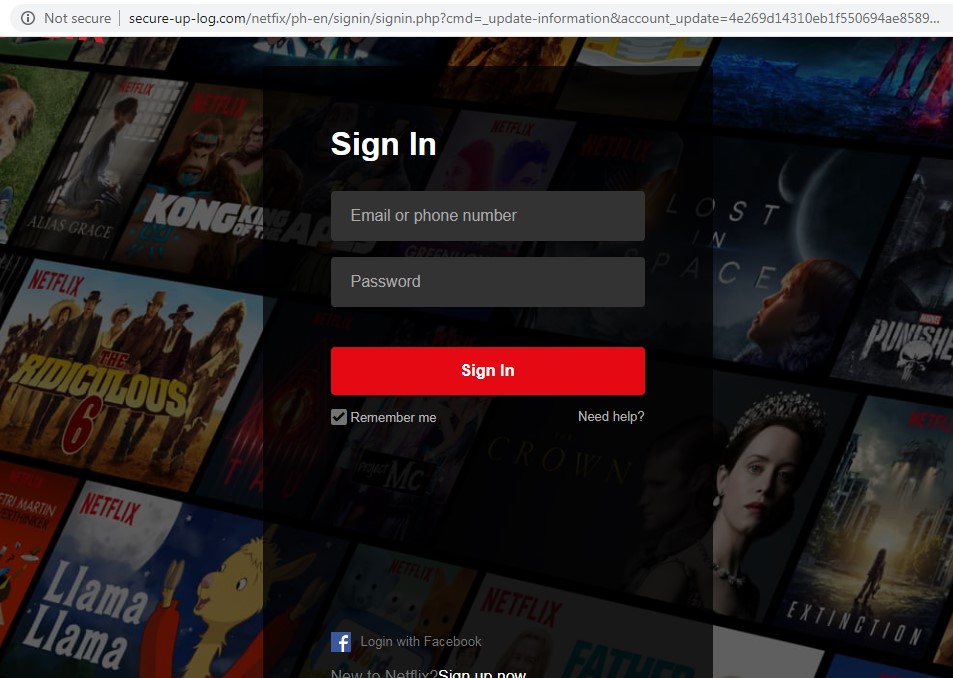
Figure 1. Fake Netflix login page
The site features a fake Netflix login page. Once the users enter credentials such as an email address or phone number and a matching Netflix account password, it leads to a page that requests the users to update their account information. We have observed that the site has geolocation features that can detect the user’s location. This is witnessed as the site automatically fills details under City, State/Province/Region, and Zip Code. The URL of the page also features the country abbreviation.
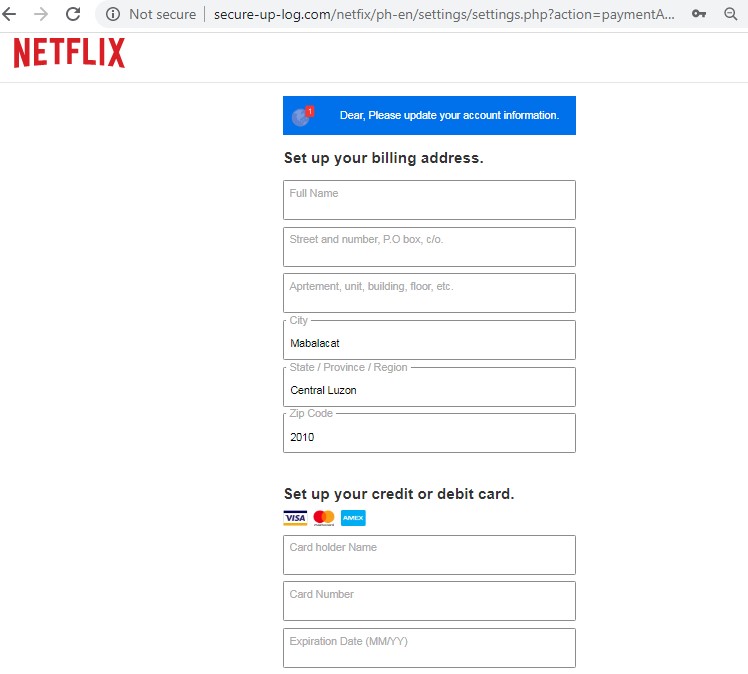
Figure 2. Fake Netflix page requesting for updated account information
After supplying the requested information, the page will display a message that confirms the “success” of the transaction, indicating that the user has now restored their account access.
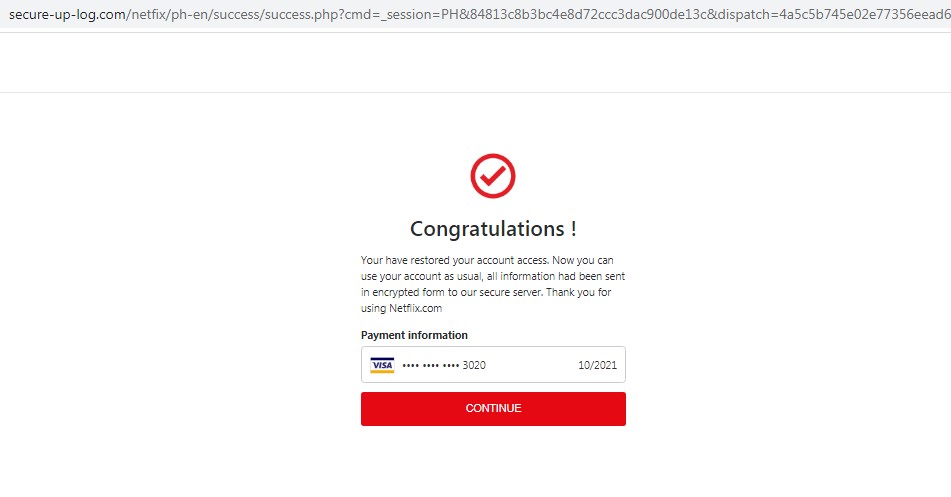
Figure 3. Fake Netflix restored account access page
The page then redirects to the legitimate Netflix page based on the user’s region.
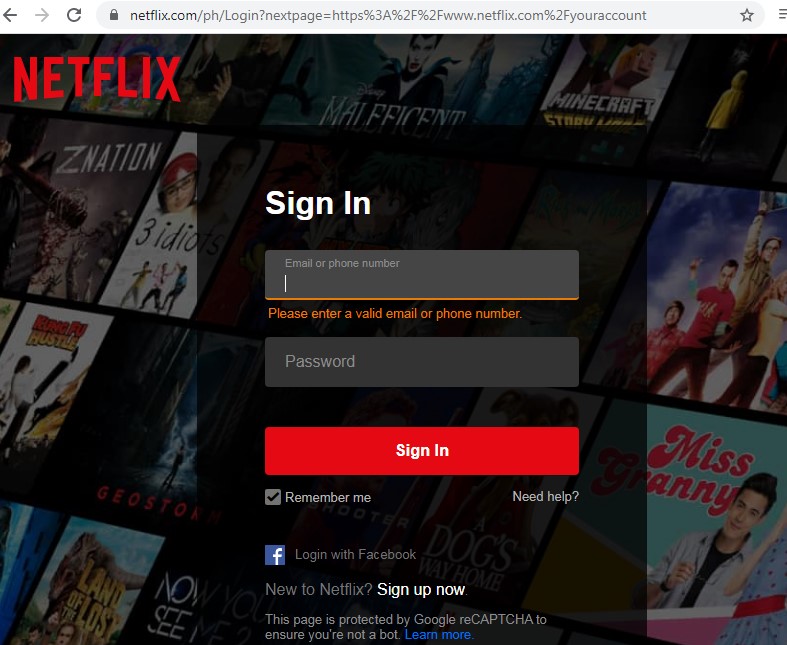
Figure 4. Legitimate Netflix login page
A few days after his initial post, Palmieri also found other Netflix-related phishing sites:
- austupdatenetflixnetwork.lekommerce[.]com/logintv/home/myaccount/a9ab3163e155d72/login/
- hxxp://updatenetflixaus.humillacionyestrella.org/login/myaccount/
- hxxp://secured-update-server-configuration.breitfam.com
Over the past few, we have seen other phishing campaigns that similarly use Netflix as bait; some threats even reference the Covid-19 outbreak at the same time. As people are spending time in quarantine due to coronavirus pandemic, video streaming platforms such as Netflix have become one of the most popular means to pass the time. Cybercriminals are taking advantage of this by using these apps to deceive unwitting users for phishing and other social engineering schemes.
Defense Against Phishing
Phishing sites seek to harvest sensitive information from victims. As they copy the user interface and spoof the website names, these malicious pages can be tricky to tell apart from legitimate log in sites. Below are some ways to avoid these threats:
- Check the URL of the site to confirm if it’s the authentic URL.
- Never click links in emails from unfamiliar senders. Hover the pointer over the embedded link to reveal where it will lead to.
- Avoid sharing sensitive personal information online.
Security solutions can also provide added protection against phishing. Trend Micro™ Web Security™ has URL filtering that helps block malicious websites. Security solutions for email and collaboration can also help protect users against phishing, as many phishing links are propagated through email.
Indicators of Compromise
URLs
- austupdatenetflixnetwork.lekommerce[.]com/logintv/home/myaccount/a9ab3163e155d72/login/
- hxxp://updatenetflixaus.humillacionyestrella[.]org/login/myaccount/
- hxxp://secured-update-server-configuration.breitfam[.]com
- hxxp://Secure-up-log[.]com/netflix/
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation