New HC7 Ransomware Variant First to Accept Ethereum (ETH) as Ransom Payment
As Ethereum (ETH) continues to soar in its market price, cybercriminals are quick to jump in on new opportunities to make a profit. A new variant of the HC7 Planetary ransomware appears to be the first ransomware to accept the Ether cryptocurrency as ransom payment.
The HC7 Planetary variant is distributed via hacking into networks using remote desktop. Once the malicious actor hacks into the network, the ransomware is manually installed on all machines that can be accessed.
The ransomware, which is currently in the wild, encrypts files and appends them with a .PLANETARY extension. As seen in the ransom note below, the author demands US$700 per machine or $5,000 for all of the machines on the network.
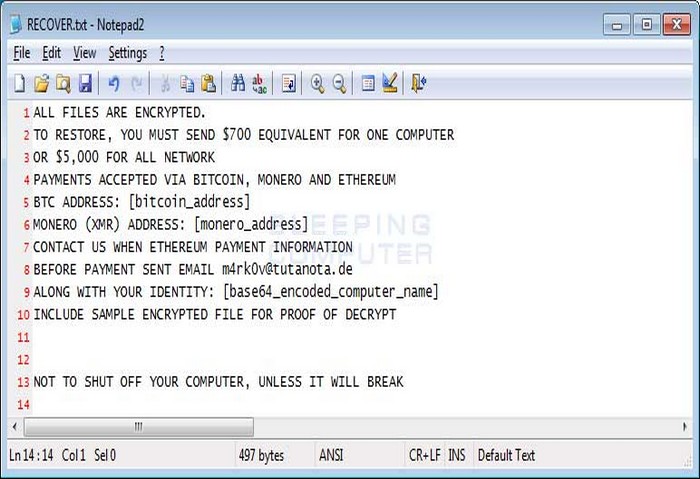 Figure 1. HC7 Planetary ransomware ransom note (via bleepingcomputer.com)
Figure 1. HC7 Planetary ransomware ransom note (via bleepingcomputer.com)
Notably, the ransomware lists Ethereum along with Bitcoin and Monero as an accepted cryptocurrency for payment. Ethereum is currently the second most valuable cryptocurrency after Bitcoin at over $1,200 per coin, and is projected to triple in value in 2018.
In December 2017, security researchers discussed how HC7-encrypted files can be decrypted by performing memory forensics on a victim's machine in order to retrieve the password used on the command line when the ransomware was installed. However, it is not clear if this method can be used to decrypt files hostaged by this new HC7 variant.
Users and enterprises can adopt these best practices to lower or eliminate the risk of ransomware infection.
Trend Micro Solutions
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation