Microsoft Detection Tools Sniff Out Fileless Malware
 Microsoft recently reported that their advanced threat protection tools were able to detect and block two heavily obfuscated and malicious scripts. The threats were apparently using the Sharpshooter technique, which was documented and published in a 2017 blog post from a British security firm.
Microsoft recently reported that their advanced threat protection tools were able to detect and block two heavily obfuscated and malicious scripts. The threats were apparently using the Sharpshooter technique, which was documented and published in a 2017 blog post from a British security firm.
A report from the company details the elusive payload—it did not trigger antivirus scanning, was loaded using a legitimate process that executed the scripts, and also left no trace on the disk. Given the characteristics, they classified the scripts as fileless threats.
Typically, a fileless malware manages to elude traditional detection techniques because it doesn't deliver a payload onto a victim's device. Instead, it injects malicious code into the memory of a running application or abuses legitimate tools already on the system or device.
For these detected fileless threats, the attack was done in two fileless stages, involving an elusive .NET executable payload that downloads data using DNS queries (which has been done before), which is then used to initialize and decode the core of the malware. The core is also a fileless threat since it executes in the memory without writing to the disk.
In their report, they concluded that the malware was probably a testing activity, not an actual attack.
Malware detection has and is continuously keeping up with advancing threats, forcing malicious actors to look for new evasion methods and avenues of entry. Our mid-year security roundup detailed the rising number of malware that challenged file-based detection technologies. Different types stood out—small-sized malware, macro malware, and of course fileless malware.
Fileless malware have been significant threats on the security landscape for a little over a year. In June of 2017 we saw the self-destructing SOREBRECT fileless ransomware; and later that year we reported on the Trojan JS_POWMET, which was a completely fileless malware. We also noted increased security events involving these types of malware.
From the beginning of the year to June 2018, we saw a 56% increase in events blocked by Trend Micro products.
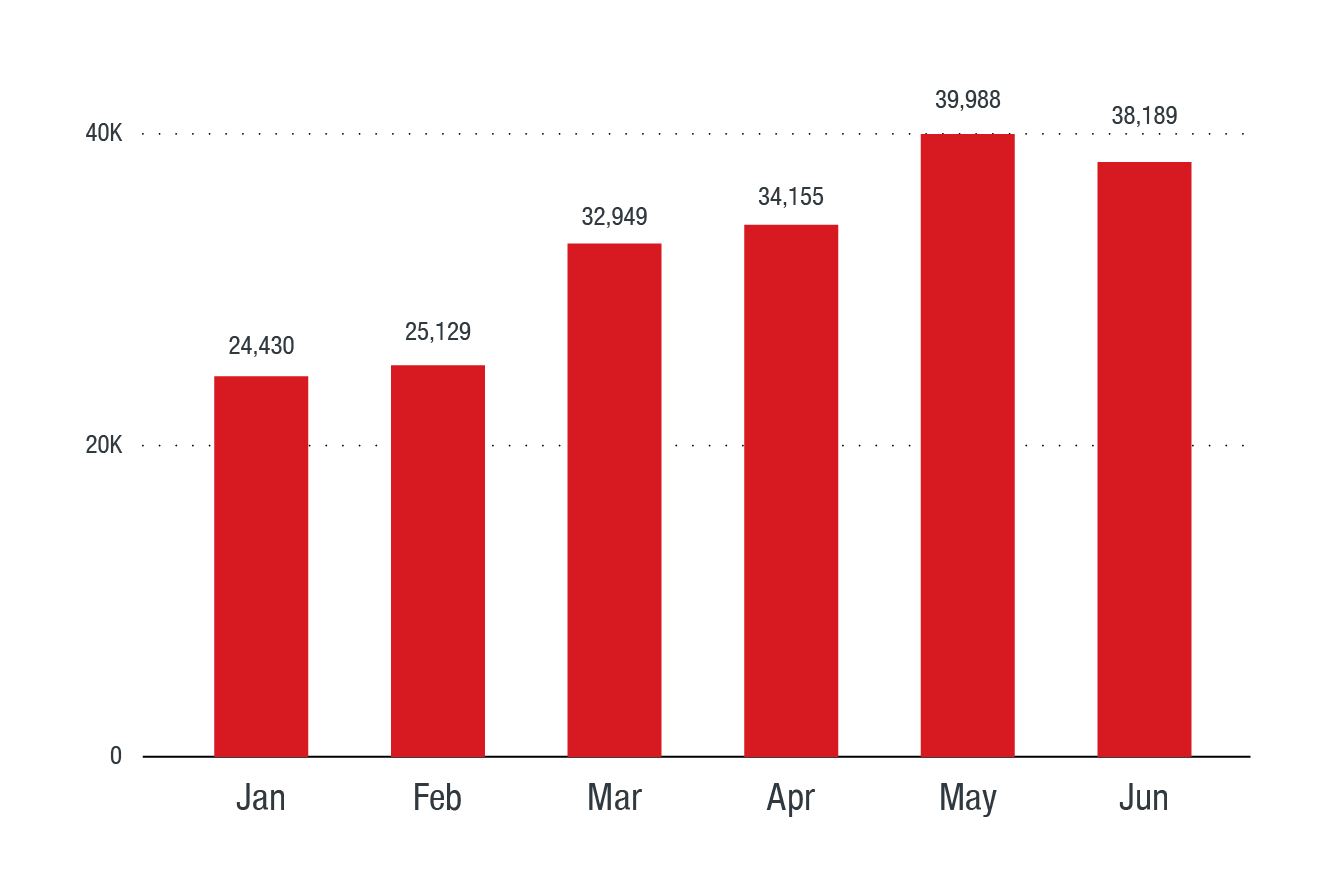
Figure 1. Fileless events blocked in the first half of 2018
A recent incident reported in July 2018 showed that malware authors continue to innovate with fileless techniques. There were reports of a fileless cryptocurrency-mining malware called PowerGhost that was targeting corporate systems. The malware took advantage of legitimate software tool PowerShell as well as the EternalBlue vulnerability to spread undetected across devices and servers in different organizations.
Containing the problem
Most threats are multi-component, and leave clues beyond files—emails or links from their delivery mechanisms, evidences from payloads that come via servers, or behavioral clues in network or system logs. According to Microsoft, as soon as the Sharpshooter technique became public, they knew that it would be abused and used in attacks. To detect the fileless threats, they used a multi-layered approach with their Antimalware Scan Interface (AMSI), behavior-monitoring, and boot-sector protection.
It shows that enterprises need to combat fileless threats with cross-generational security solutions and employ integrated layers of protection across the network. Trend Micro Smart Protection Suites deliver several capabilities like high fidelity machine learning, web reputation services, behavior monitoring, and application control, and vulnerability shielding that minimize the impact of this threat. Trend Micro Endpoint Sensor will also be effective in monitoring events, as this product will help quickly examine what processes or events are triggering the malicious activity.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- The Hidden Risk in Your AI Rollout: Your Endpoints
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation