Best Practices: Identifying and Mitigating Phishing Attacks
 Despite being one of the oldest scams on the internet, phishing continues to be a significant problem for both individuals and organizations. In fact, our telemetry have noted an increasing trend since 2016. We predict a marked increase in phishing activity in 2019, as shown in our 2019 Security Predictions.
Despite being one of the oldest scams on the internet, phishing continues to be a significant problem for both individuals and organizations. In fact, our telemetry have noted an increasing trend since 2016. We predict a marked increase in phishing activity in 2019, as shown in our 2019 Security Predictions.
A number of notable phishing attacks, such as the series of phishing emails—estimated to have been sent to as many as 100 million users—that led users to a page that served the ransomware Locky in 2016, have been observed through the years. Cybercriminals have also been seen impersonating popular services such as Netflix, whose users were found to have been the target of phishing attacks designed to steal passwords and other credentials.
How to identify typical phishing attacks
Given the prevalence of phishing attacks, it is important to be aware of what an actual phishing attempt looks like. While cyber criminals will often try to make their attacks look as legitimate as possible, there are indicators that can be used to identify the authenticity of a message. Here are some examples of actual phishing attempts targeting users of some of the world’s most well-known brands to illustrate what to look out for.
Example 1:
LinkedIn is used by people as a way to network and keep in touch with other professionals, making it a prime focus for cyber criminals who are looking to steal personal information from the millions of employees who use the social media website.
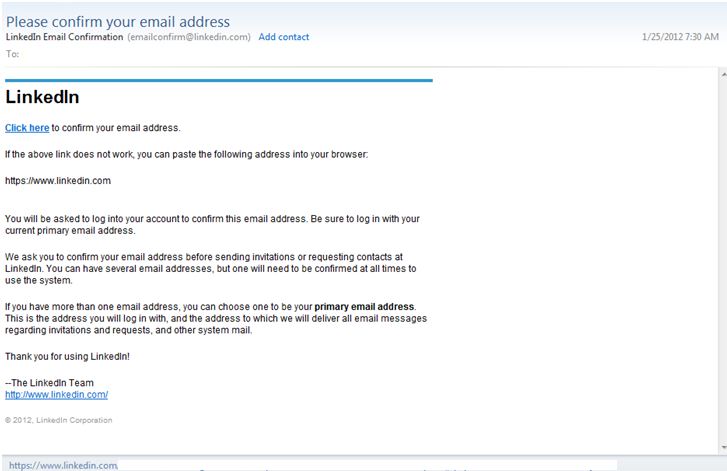
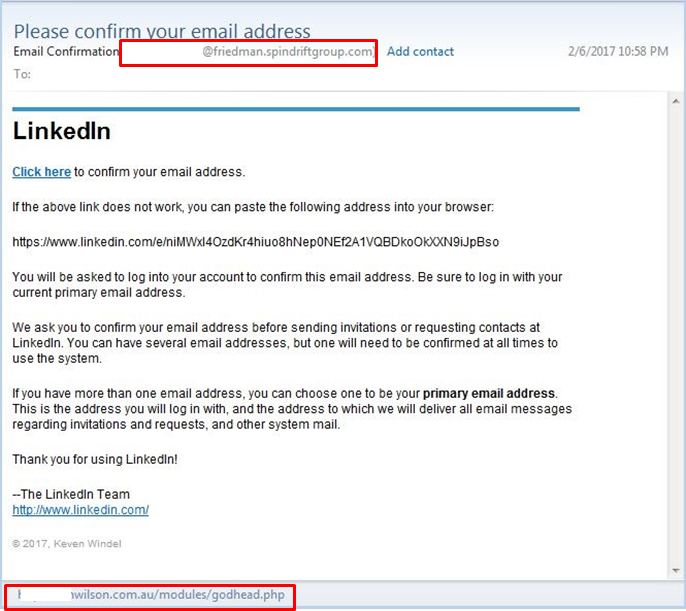
Figure 1: Comparison of a legitimate LinkedIn confirmation email with a phishing email
Before even getting into the actual content of the message, users should first consider why they received a confirmation email in the first place. Most companies will only send confirmation emails for new registrants or customers who change something in their settings. Unsolicited ones should be deemed as highly suspect.
The example shown here is a comparison of an actual LinkedIn confirmation email with a phishing attempt that tries to mimic the legitimate one. The sender did a good job of copying the logo and text of the real email. However, the two primary indicators that this is a phishing attempt is the identity of the sender - the LinkedIn email contains the website’s domain, whereas the phishing email uses a different domain. The other red flag is the destination of the embedded link. The legitimate email leads to a LinkedIn page, while the phishing email leads to a “phishy” website. Users should take note that they do not need to click on a link to check where it leads since hovering their mouse cursor above the URL will also show the link destination.
Example 2:
PayPal is the most popular online payment service in the world, with millions of dollars’ worth of payments being processed on a daily basis. It is also tied to credit card and bank account credentials, which makes it a lucrative target for cyber criminals.
Figure 2: Comparison of a PayPal update message with its phishing counterpart
Cyber criminals will often resort to using an alarmist tone in order to pressure potential victims into clicking links or downloading files. Comparing the legitimate email with the fake one, the former contains a straightforward message that mentions changes to the policy updates while the latter tries to frighten PayPal customers into giving out their private information by threatening to restrict their accounts. The real PayPal email also greets customers with their given name and surname while the phishing email only contains a member number, which is suspicious given that PayPal uses emails for unique IDs.
In addition, a quick glance at the phishing email shows images that have failed to load properly. As a precautionary measure, some email clients either block images by default or flag HTML-based emails from unknown sources as spam. Many companies use Multi-part MIME (Multipurpose Internet Mail Extensions) as a way to bundle both the HTML and plain-text versions of an email. Cyber criminals usually do not bother with this step, so users should be wary of emails and messages that do not load or are not formatted properly.
Example 3:
Apple has earned a reputation as one of the most trusted names in the consumer electronics industry due to its perception as an intrinsically reliable and secure brand. However, the ubiquity of its products and services has made its users frequent victims of phishing attacks.

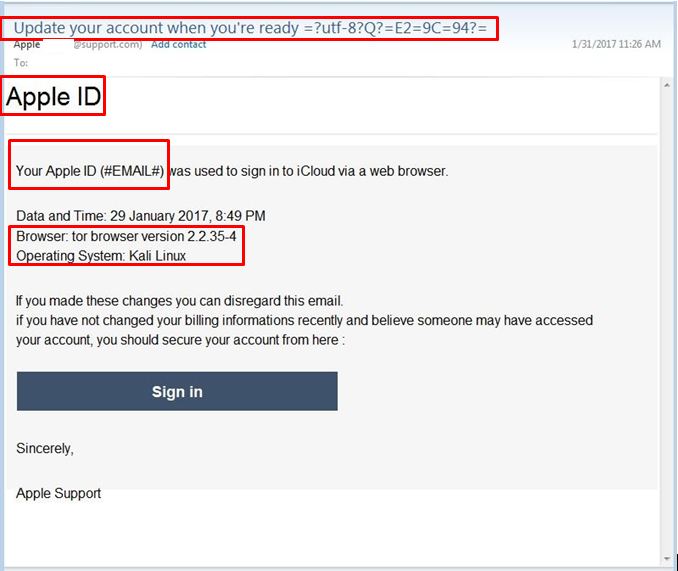
Figure 3: Comparison of an Apple ID warning with a phishing attempt
In this phishing attempt, the most notable red flag is the nonsensical email subject. The real Apple warning email has a concise subject line that states exactly what the email is about while the phishing email’s subject line is vague and contains gibberish. Another difference is the greeting. Instead of a personal greeting that mentions a name or an account email, the phishing message does not even contain any reference to the recipient. Also noticeable is the misleading domain name that tricks the Apple customer by using a domain that contains the words “support”. However, it lacks the apple.com domain that the company uses on their emails. Most organizations, especially large ones, have consistent branding across all their URLs and email addresses, so an email that uses a different domain name from the official one is likely to be a phishing attempt.
Example 4:
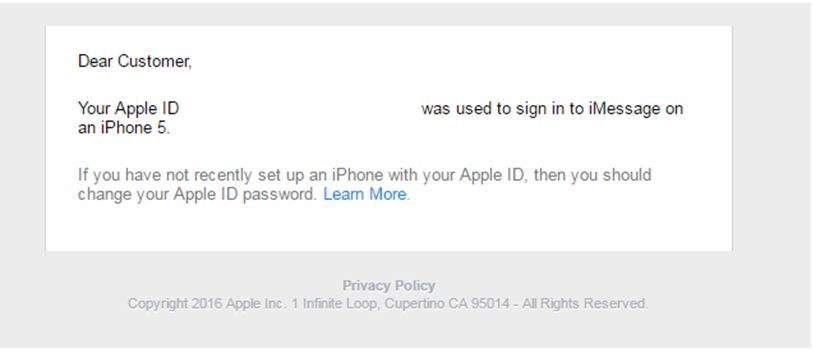
Figure 4: A fake Apple ID warning email
This message, purportedly from Apple, was sent to a Trend Micro employee via his work email. At first glance, there seems to be nothing wrong with the warning. However, two signs give away this message as a phishing attempt. First, the employee’s Apple ID is not connected to his work email, which makes it highly improbable for Apple to send the email to this address. Second, it mentions an older iPhone model. Cyber criminals will often recycle their social engineering tactics over the years, resulting in phishing attacks that reference outdated technology. The lesson here is to take not just the content of the message, but also its context into account.
Tips for mitigating phishing attacks
Here are some recommendations to help protect users from falling victim to phishing scams.
- Users should always be cautious of individuals or organizations that ask for personal information. Most companies will not ask for sensitive data from its customers. If in doubt, users should verify with the company itself to avoid any potential issues.
- Users should always take a close look at the sender’s display name when checking the legitimacy of an email. Most companies use a single domain for their URLs and emails, so a message that originates from a different domain is a red flag.
- As a general rule, users should not click links or download files even if they come from seemingly “trustworthy” sources.
- Check for mismatched URLs. While an embedded URL might seem perfectly valid, hovering above it might show a different web address. In fact, users should avoid clicking links in emails unless they are certain that it is a legitimate link.
- Users should always be on the lookout for any grammatical errors and spelling mistakes. Legitimate companies will often employ proofreaders and editors who ensure that the materials they send out are error-free.
- Users should not be frightened or intimidated by messages that have an alarmist tone. They should double check with the company if they are uncertain about the status of their accounts.
- Phishing emails are designed to be sent to a large amount of people, so they need to be as impersonal as possible. Users should check whether the message contains a generic subject and greeting, as this can be a sign of a phishing attempt.
- Although not every end user has access to advanced anti-phishing software, they can still use the built-in protection of their email clients to filter messages. One example is setting the email client to block all images unless approved.
- Legitimate companies will never send confirmation emails unless there are specific reasons for doing so. In fact, most companies will avoid sending unsolicited messages unless it’s for company updates, newsletters, or advertising purposes.
- Users should always take the context of an email or message into account. For example, most online accounts do away with viewable member numbers, so users should be wary if they receive emails containing a “member number” for services that generally don’t use them.
- It is important to take note of unusual information in the text of the message. Any mentions of operating systems and software that are not typically used by consumers can often be indicators of a phishing attempt.
- If it seems suspicious, it probably is. Users should always err on the side of caution when it comes to sending out personally identifiable information through messages and emails.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- The Hidden Risk in Your AI Rollout: Your Endpoints
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation