Credential phishing is still on the rise. This form of cyberattack, which involves the theft of email account credentials via fake or compromised login pages, can expose organizations to a wide range of crimes that include fraud, espionage, and information theft, which in turn make them vulnerable to monetary loss and operational disruption.
In the first half of 2019 alone, the Trend Micro™ Cloud App Security™ solution detected and blocked 2.4 million attacks of this type — a 59% increase from 1.5 million in the second half of 2018.
Figure 1. Trend Micro Cloud App Security credential phishing detections in 2018 2H and 2019 1H
The countries with the highest numbers of credential phishing attack detections were the Netherlands, the U.S., and Japan.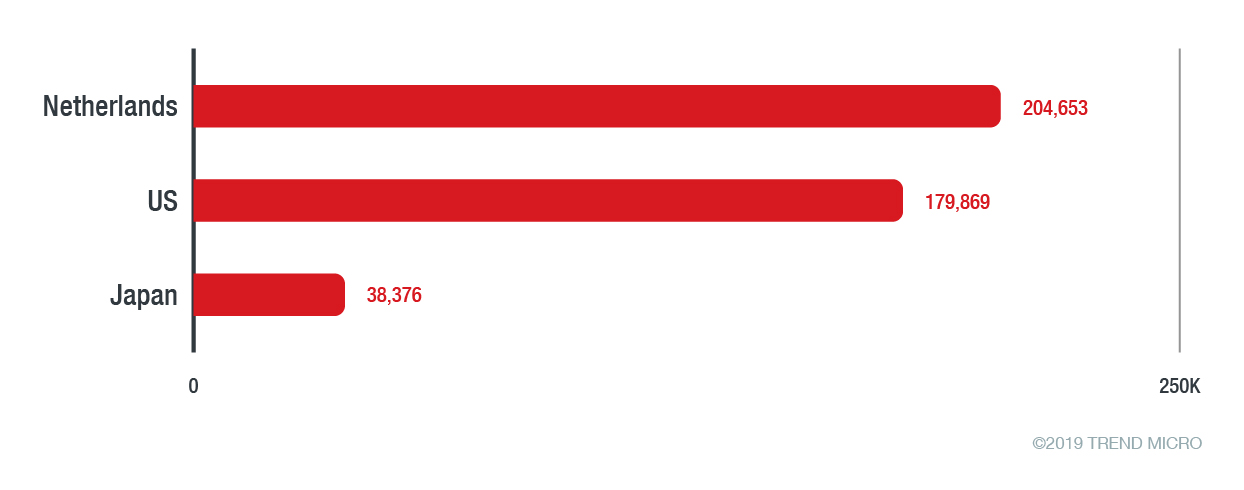
Figure 2. Top three countries with the most credential phishing attacks detected
Given these numbers, organizations worldwide must continue to be vigilant against credential phishing. The risk of falling victim to an attack is increased not only due to its prevalence — cybercriminals are also crafting new techniques for a greater chance of deceiving email users.
[Read: How AI and machine learning in email security solutions boost detection efficacy]
New credential phishing techniques observed in 2019 1H
The Trend Micro Cloud App Security Report 2018 covered a variety of credential phishing techniques notable for their deceptiveness. In just a span of six months, cybercriminals developed new ones that relied on certain tools and tricks that no other campaign has done in the past. By combining the unique functionality of a tool and social engineering elements, cybercriminals managed to produce techniques that are on par with those from 2018.
In April, a Trend Micro researcher discovered a campaign that used SingleFile to produce an identical copy of legitimate login pages. Attackers accessed the login page of the website to be spoofed and then used SingleFile to save and generate a file that contains the whole page. They were able to set up identical login pages for stealing email account credentials.
In July, Bleeping Computer reported on two types of credential phishing techniques. The first technique used OneNote audio as a lure to lead recipients to a fake login page. The second one attempted to manipulate administrators using fake Office 365 alerts that appeal to their need to deal with time-sensitive concerns.
Cybercriminals continue to impersonate Microsoft
Aside from Cloud App Security’s massive credential phishing detections, data from other reports on phishing in the first half of the year confirm its growing prevalence. For many attacks observed, Microsoft services are the most spoofed.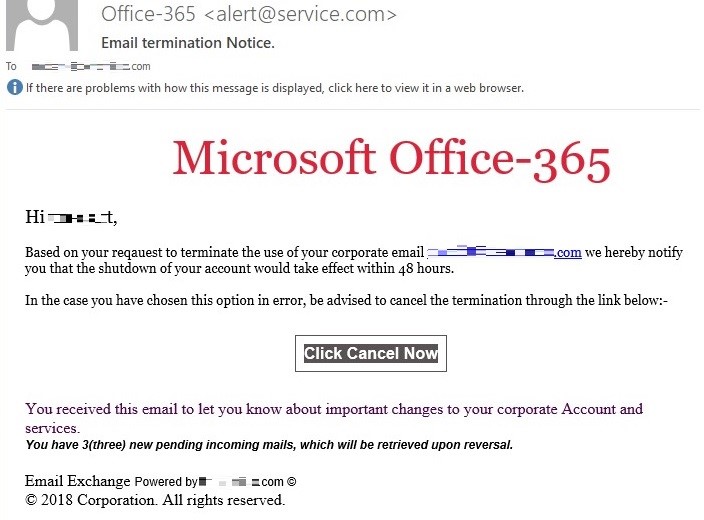
Figure 3. Sample email spoofing an Office 365 alert detected by Cloud App Security
The Trend Micro Annual Security Roundup 2018 reported an increase of 319% in the number of unique phishing URLs posing as Office 365 and Outlook login pages. Cybercriminals impersonated Microsoft in one out of three attacks attempting to phish email account credentials via a fake login page, according to Barracuda Networks. Vade Secure, in its 2019 Q1 report, noted that Microsoft is at the top of the list of most impersonated brands in phishing attacks. Meanwhile, Avanan’s 2019 report on the phishing landscape found that Microsoft was used in 43% of brand impersonation attacks.
The choice of Microsoft for credential phishing attacks can be attributed to the profitability of Office 365 credentials. The reason: Attackers only require one key to the entire Office 365 platform, allowing them to conduct various attacks through compromised accounts.
Additional security layer needed to keep credential phishing at bay
Organizations need an enhanced cybersecurity defense to stop attackers that continue to cast wider phishing nets. The Trend Micro Cloud App Security solution helps businesses with existing email security by detecting and blocking email threats missed by previous security layers. In the first half of 2019, businesses that integrated Cloud App Security into their email gateways were protected from credential phishing attacks.
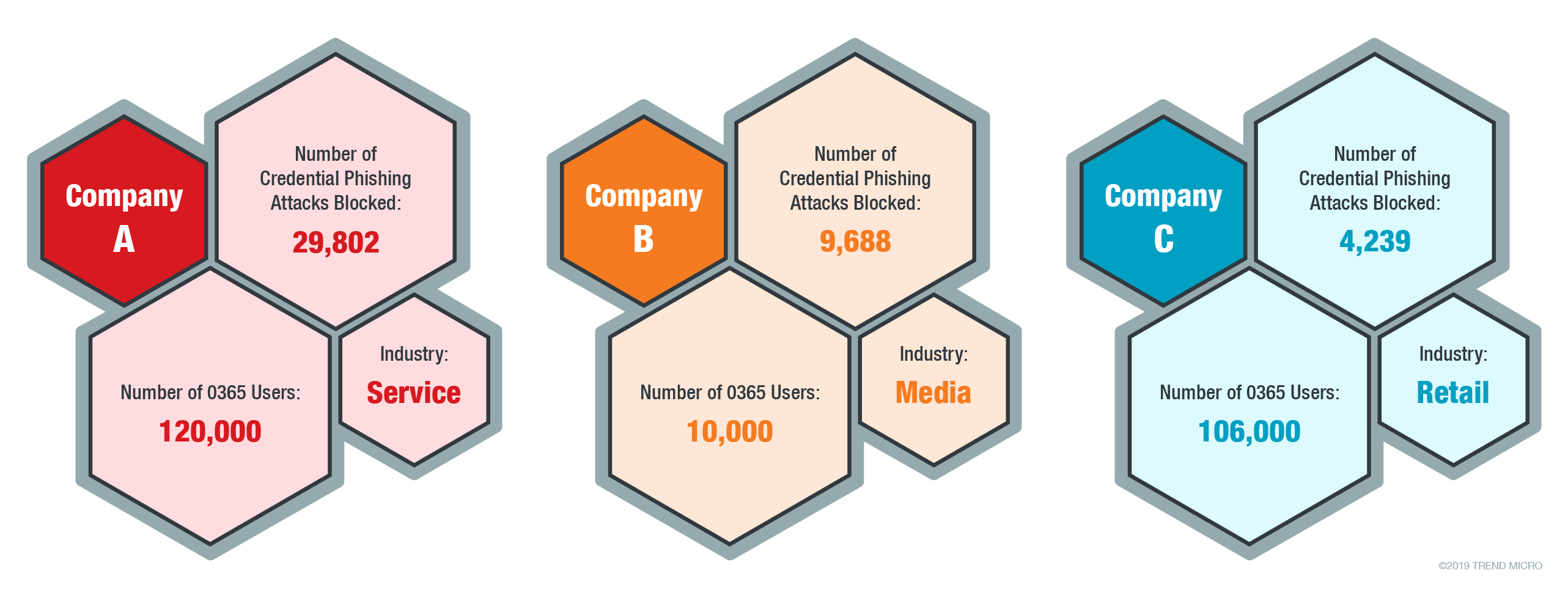
Three companies with Cloud App Security protection and the number of credential phishing attacks blocked in 2019 1H
Apart from using machine learning to perform web reputation and URL dynamic analysis, Cloud App Security uses artificial intelligence (AI) and computer vision technologies to protect organizations from credential phishing attacks that deploy tactics like brand impersonation. After pre-filtering via email sender, URL, and web reputation analyses, computer vision and AI will examine the remaining suspicious URLs to check if a legitimate brand’s login page is being spoofed.
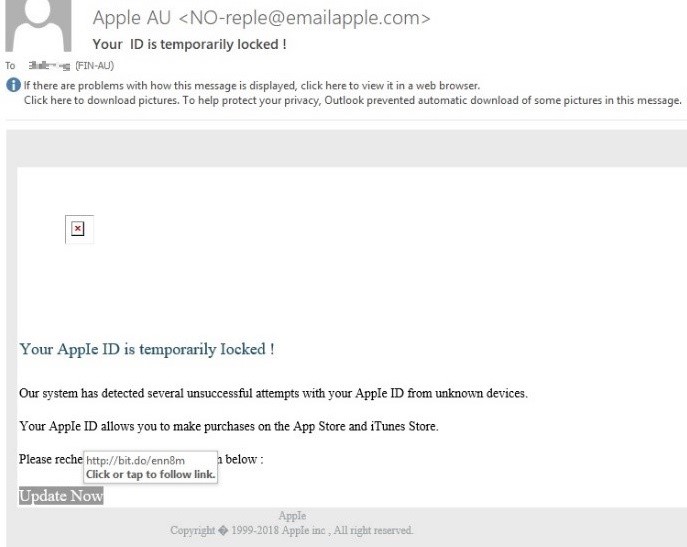
Figure 4. Screenshot of a Cloud App Security-flagged email that shows typographical errors, a fake Apple domain address, and text with an urgent tone
[READ: Trend Micro predicts social engineering via phishing will replace exploit kits as attack vector]
Workforce tips for identifying credential phishing attacks
Workforce cybersecurity awareness is essential in keeping organizations safe from cyberattacks. To stay protected from credential phishing attacks, employees can look into the following best practices to help them identify such attacks.
- Emails should be examined for grammatical errors and spelling mistakes. Emails from legitimate companies are often proofread to ensure that the materials they send out are error-free.
- The email sender’s display name should be given a closer look to check the email’s legitimacy. Since most companies only use a single domain for web pages and emails, an email with a different domain can be considered a red flag.
- Be cautious of emails from individuals or organizations that ask for personal information. Most companies will not ask for sensitive data from its customers, especially with stricter data privacy laws implemented across the globe.
- Emails that call on a sense of urgency or have an alarmist tone should not be hastily acted on. If in doubt, recipients should verify the status of their accounts with their company’s system administrator or service provider.
- Closely examine included URLs. An embedded URL might seem perfectly valid, but hovering above it might show a different website address.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One