Compliance & Risks
Survey 3 Standard is way to institute collaboration
This is the final installation of our three-part blog series, explaining the state of industrial cybersecurity based on the result of survey. This article focuses on issues related to people and process. We also compared these issues by country.
Posts in this series
- Part 1: IT and OT with people, process, technology
- Part 2: Factories took measures but are developing
The State of Industrial Cybersecurity Part 3
Standard/guideline are the leading methods to institute collaboration
This is the final installation of our three-part blog series, explaining the state of industrial cybersecurity based on the result of survey Trend Micro conducted in the US, Germany and Japan in November 2021.
This article focuses on issues related to people and process. We also compared these issues by country.
Defining the CSO of a factory is the most important first step
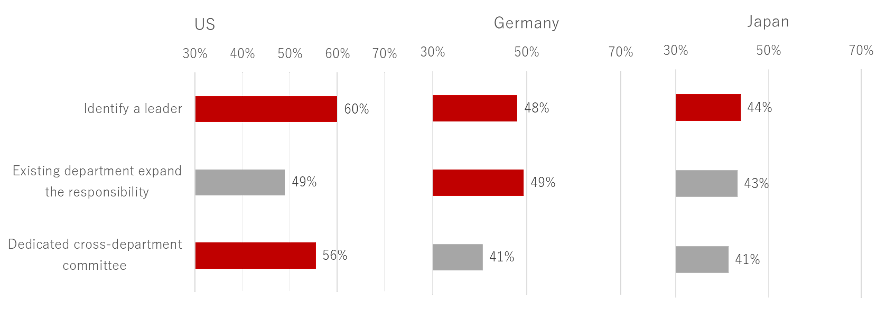
We start by looking at the people, which includes an organizational measure and human knowledge of cybersecurity. We asked respondents how have manufacturing changed its organizational structure to work industrial cybersecurity. We then presented three categories:
- Clarifying who is the officer responsible for cybersecurity
- Adding scope of responsibility to existing department
- Establishing a dedicated cross-department committee or group to drive digital transformation
Then, we asked them about the degree to which the measure is implemented.
The most common organizational structure measure was clarifying who is the officer responsible for cybersecurity, such as Chief Security Officer. In the US, 60% of respondents said the leader has been already clear. In addition, a cross-departmental ICS security team is also organized (56%)?both of which are higher than others.
Meanwhile, in Germany, the largest number of respondents (49%) said they were expanding the role of existing organizations to cover ICS security. In Japan, every item is lower than those in the other two countries. It seems that there are not many cases where the organizational structure is modified for the purpose of strengthening cyber security in smart factories.
Figure 3-1. Organization structure
Providing internal training to employees involved in cybersecurity remains paramount
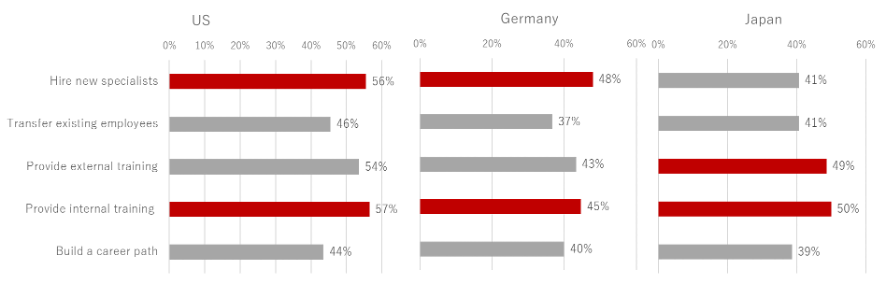
We then looked into human resource management. The US and Germany had similar results. However, the US ranked higher at 56% when it comes to the recruitment of specialists, with Germany has 45%. Fifty-seven percent of respondents in the US also said internal training is provided, while 45% of Germany respondents said the same.
In addition, other items such as transfer employees, external training, build a career path do not have significantly low ratings. Organizations in both the US and Germany seem to take various efforts to manage the human resource for cybersecurity.
On the other hand, Japan has distinctive results in human resources management. More organizations provide internal and external training than hiring specialists, which ranked top in the other two countries. It seems that there is a stronger direction in developing existing internal human resources.
Figure 3-2. Human resource management
Standards and guidelines are the leading methods to institute collaboration
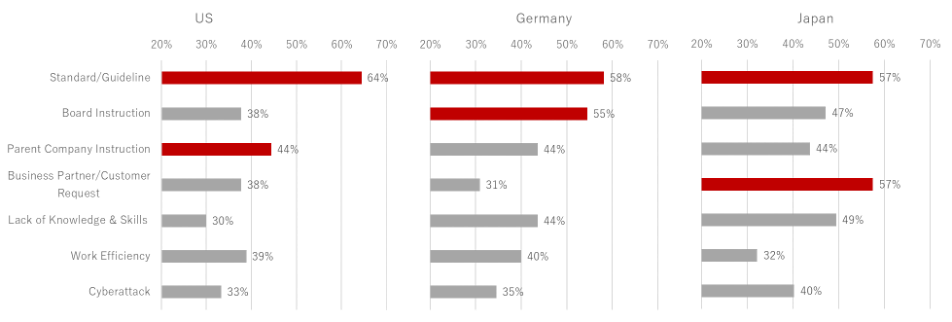
We asked respondents what the reason was for having cybersecurity across the organization. Based on the results, the biggest reason in each country is compliance with regulations and guidelines.
Smart factories must comply with cybersecurity regulations and industry guidelines in each country, and it requires them to work across organizations. Sixty-four percent of US respondents, 58% in Germany, and 57% in Japan said that complying with industry standard or guideline was the reason cybersecurity is implemented in their organizations
In the US, 38% of the respondents said that implementing cybersecurity guidelines is an instruction given by the parent company. Meanwhile, in Germany, 58% said that it is the management's instructions to do so. In Japan, 57% of respondents said it is the decision made by the business partner or at the request of customers.
Organizations in the US and Germany seem to move forward with cybersecurity with instructions given by higher-ups, while in Japan bottom-up decision-making that responds to external demands are the driving factors.
Figure 3-3. Impetuses to institute collaboration
NIST CSF and ISO 27001 are the most common guidelines
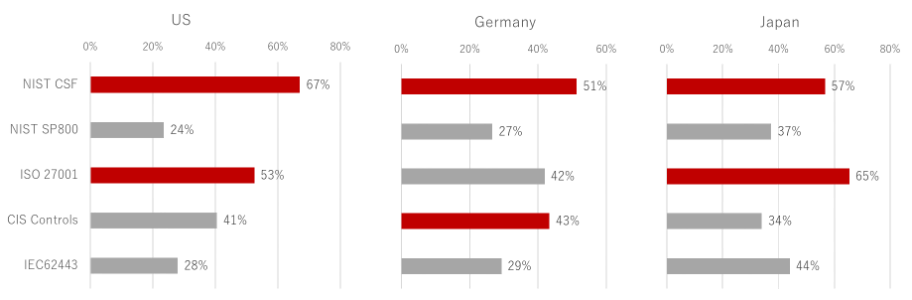
In Fig 3-3, compliance with regulations and guidelines were the biggest cause of instituting collaboration. NIST CSF and ISO 27001 were the most common guidelines used in the US, Germany, and Japan to comply with regulations and industry standards.
The respondents of this survey are from the private manufacturing industry. It is interesting that NIST CSF, which originated in critical infrastructure cybersecurity in the US, was the most popular. NIST CSF is just a framework, not a regulation. Although many of the respondents don't need to comply directly, it seems that they see NIST CSF as a reference for practicing smart factory cybersecurity.
Meanwhile, ISO27001 is an Information Security System Standard (ISMS) that belongs to the world of IT. However, it seems that organizations are trying to manage information in the same way as IT in the ICS environment.
Lastly, IEC62443, an international standard for ICS security, is ranked slightly higher in Japan but low overall. This standard is possibly not well recognized among the respondents.
Figure 3-4. Regulations & standards
The survey revealed that many manufacturing has already implemented industrial cybersecurity not only in technology but also in organization and process. However, there are still challenges that remain. Organizations are rushing to take technical measures, but it's important that IT and OT teams would participate in the decision-making process to achieve this.
To read the survey's full report and results, click here.
If you want to learn more about ICS security guidelines and how Trend Micro can help your organization and process, check out the following resources:

