Cyber Threats
Experimental analysis of smart factories Part 1
Trend Micro released a research paper on new security risks associated with smart factories. Part one introduces the concept of "smart manufacturing,” and explains the research methods and attack vectors that are unique to smart factories.
On May 11, 2020, Trend Micro released a paper showing the results of proof-of-concept research on new security risks associated with smart factories. In this series of 5 columns, based on the results of this research, we will look at the security risks to be aware of when promoting smart factories by examining overlooked attack vectors, feasible attack scenarios, and recommended defense strategies. This first column introduces the concept of "smart manufacturing," and explains the research methods and attack vectors that are unique to smart factories.
What is "smart manufacturing?"
The "smart factory" is an inevitable strategy. Every factory has two ultimate aims: "to increase productivity" and "to reduce the defect rate." Smart manufacturing refers to the use of technology and IT-OT integration in order to increase productivity and to reduce the defect rate - or, even better, to measure and control the same. More technically, smart manufacturing is an effort to achieve a high automation level of production processes and management through software-defined control, network connection, and data analysis. As digitalization progresses, factories around the world are starting to become smarter.
On the other hand, smart-factory architects, engineers, and operators must also examine the potential security risks associated with technological innovation. Making factories "smarter" is an effort to use digital technology to automate and speed up the entire manufacturing process. To do so, software control and network connectivity are essential requirements. This also means that there is an increase in the number of potential attack targets and entry points for cyber attackers (Fig. 1). In other words, cyber security risks increase as a factory gets smarter; smart factories and security are inextricably linked.
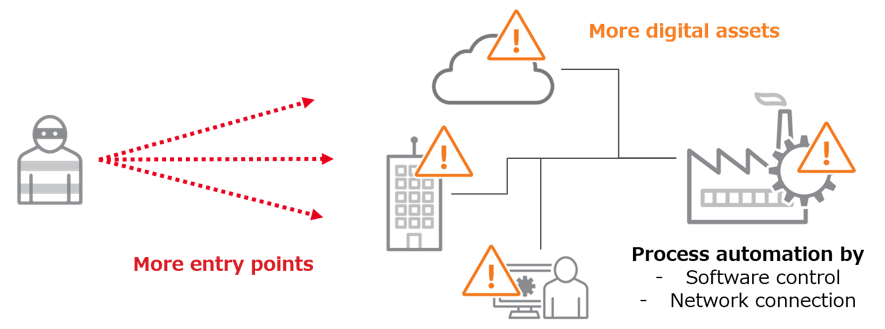
<Fig.1> Smart factories have more potential cybersecurity risks
Overlooked security risks
Smart manufacturing will become mainstream, so we must prepare for it. Many people would be well-served by knowing how to build a safer smart factory. Therefore, Trend Micro conducted this research with the goal of clarifying the security risks to be taken into consideration when building one's own smart factory. Specifically, the research had 4 areas of focus.
- Attack entry points that are unique to the typical smart-factory environment
- Possible attack scenarios
- Damage to the factory caused or facilitated by cyber attacks
- Recommended countermeasures
Experiments on a real smart manufacturing system
In order to achieve the goals, Trend Micro used a real smart manufacturing system. By reproducing a cyberattack in an actual manufacturing environment, we were able to verify the feasibility of the cyberattacks and visualize the effects of the attack on factory equipment. As shown in Figure 2, in factory manufacturing processes, there are 5 layers according to the roles and systems linked to each layer. To fully reproduce a smart factory, in addition to the MES and HMI shown below, it is necessary to have physical equipment such as robots and conveyor belts. To this end, Trend Micro worked with Politecnico di Milano, which has a proven track record in engineering research related to Industry 4.0. For more information about Politecnico di Milano, check out this blog.
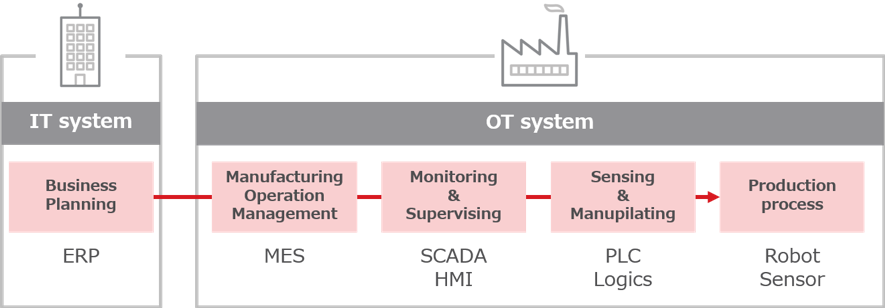
<Fig.2> The 5-layered manufacturing process
- ERP: Enterprise Resource Planning, MES: Manufacturing Execution System, SCADA: Supervisory Control And Data Acquisition, : Human Machine Interface, PLC: Programmable Logic Controller
Photo 1 shows the smart manufacturing system used in this research. There are 7 stations in total, each consisting of a PLC, HMI (both manufactured by Siemens), and actuators (drill, presser, etc.). In addition, various sensors, conveyor belts, and Mitsubishi industrial robots were installed to automate all manufacturing processes. Also, we were advised by external experts in OT environments, which enabled us to make it as close as possible to an actual environment. We used this system to analyze cybersecurity risks in smart factories.

<Photo 1> The smart manufacturing system at Politecnico di Milano
Overlooked entry points: "MES" & "EWS"
The first thing that became apparent when actually conducting our analysis was that smart factories indirectly exchange data with locations outside the factory, and there were several potential entry points to break into the smart-manufacturing installation. Figure 3 is a simplified diagram of a smart factory's data flow based on the environment used in this research.
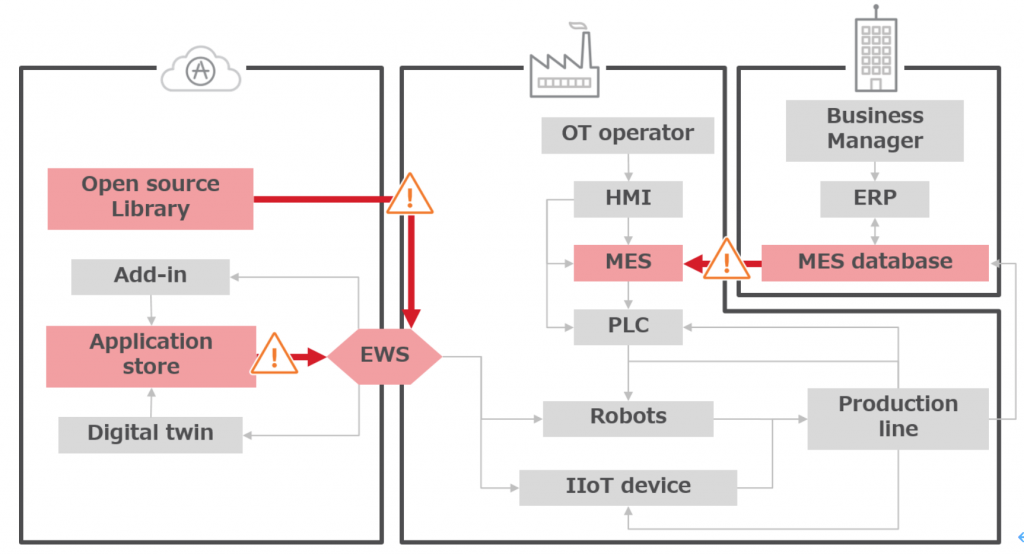
<Fig.3> Overlooked entry points in smart factories
As you can see, there are several intricate interplays between IT, OT, and cloud systems. Trend Micro focuses on the overlooked entry points in such smart environments, namely the MES (Manufacturing Execution System) and EWS (Engineering WorkStation). As shown in Figure 3, MES and EWS are responsible for exchanging data with external systems. Of course, in addition to these two, mobile HMIs and IIoT devices can also be points of entry into a factory. However, since the MES and EWS are systems that are indispensable for smart manufacturing, and critical issues were discovered in this study, these two entry points are the most relevant. In this series of articles, we will introduce the following three experiment-verified scenarios.
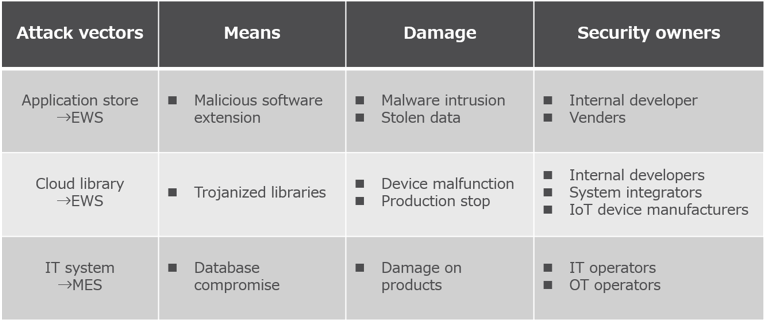
<Fig.4> 3 attack scenarios in the research
In the next post, we will examine the first attack scenario: Security risks in industrial application stores.

