Ransomware
Leveraging Data Science to Minimize the Blast Radius of Ransomware Attacks
In this blog entry, we present a case study that illustrates how data-science techniques can be used to gain valuable insights about ransomware groups' targeting patterns as detailed in our research paper, “What Decision-Makers Need to Know About Ransomware Risk.”
In partnership with: Erin Burns, Eireann Leverett of Waratah Analytics
As ransomware groups continue to build on their arsenal of tactics, techniques, and procedures (TTPs), it's essential for cybersecurity professionals to assess the levels of risk to their organizations using multiple sources of information for a comprehensive outlook on this ever-evolving threat. Common Vulnerabilities and Exposures (CVE) data, for example, can guide defenders in determining which areas they need to concentrate on when it comes to patching priorities. In this blog entry, we present a case study that illustrates how data-science techniques can be used to gain valuable insights about ransomware groups' targeting patterns as detailed in our research paper, “What Decision-Makers Need to Know About Ransomware Risk.”
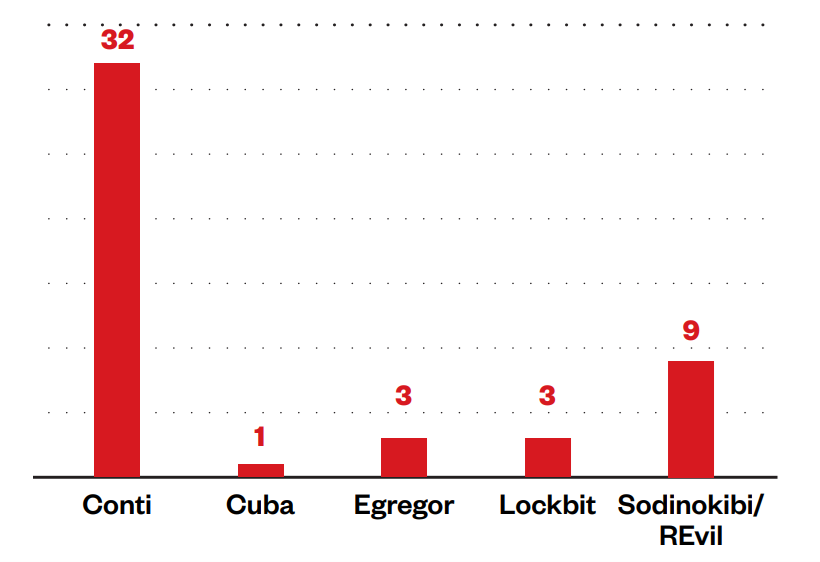
In this joint research, researchers at Trend Micro and Waratah Analytics identified 120 CVEs that were used by various ransomware groups, which revealed their tendency to target communications and collaboration software, virtual private networks (VPNs), and remote access and file storage technologies. The top five ransomware groups by volume of activity — Conti, Cuba, Egregor, LockBit, and REvil (aka Sodinokibi) — utilized 46 CVEs and were able to compromise 30 unpatched products across 15 vendors. Among these five groups, Conti has exploited the highest number of vulnerabilities at 32 CVEs (Figure 1).
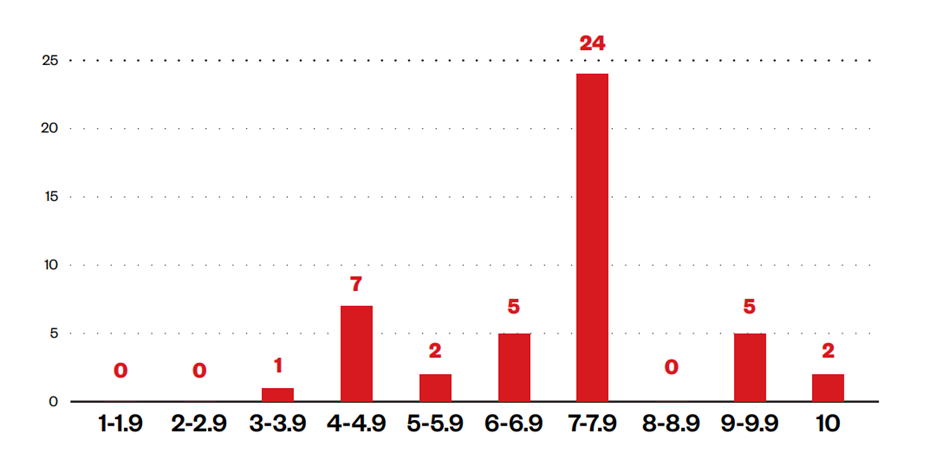
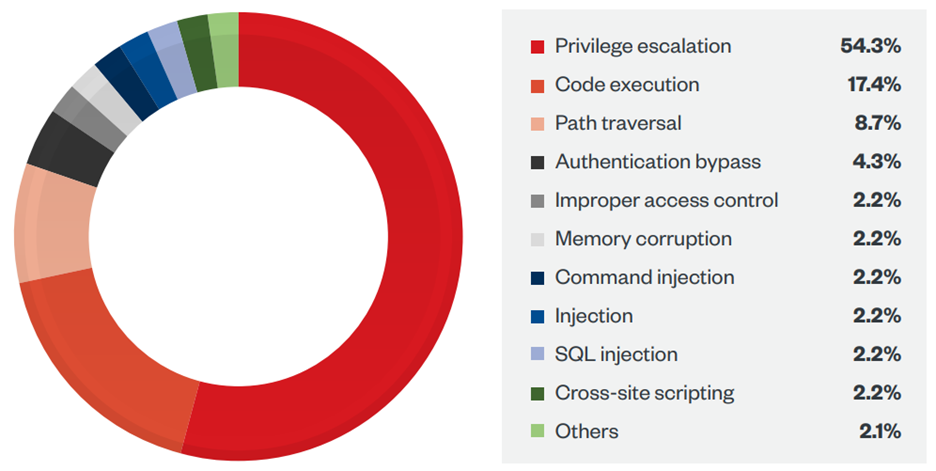
The CVEs used by the top five groups varied in severity (Figure 2), though most of these CVEs had a score of at least 7.2 on the Common Vulnerability Scoring System (CVSS). As Figure 3 shows, the bulk of these vulnerabilities were exploited as a means of privilege escalation at 54.3%, followed by those for remote code execution (RCE) at 17.4%.
Vulnerabilities exploited by the top five ransomware groups
CVE-2021-30119, which has the lowest CVSS score of 3.5, is an authenticated and reflected cross-site scripting vulnerability in Kaseya VSA products that REvil exploited in July 2021, along with CVE-2021-30116 and CVE-2021-30120, as part of its supply-chain ransomware attack on managed service providers.
Meanwhile, the RCE vulnerabilities CVE-2018-15982 and CVE-2020-0609 ranked the highest in severity, both with a 10 CVSS score. Reports emerged in 2020 of Egregor possibly exploiting CVE-2018-15982, an Adobe Flash Player vulnerability. The historic Conti ransomware group used CVE-2020-0609 — a vulnerability affecting Windows Remote Desktop Gateway — as a means of gaining initial access into victims’ systems.
Building defenses to the left of the ransomware kill chain
These findings suggest that cybersecurity teams can defend their organizations from the most active ransomware groups by focusing on patching RCE and privilege escalation vulnerabilities. More importantly, these results demonstrate that analyzing CVE data to determine where vulnerability exploits factor in the cyber kill chain can prove useful for defenders by providing them with information about a particular ransomware group’s technical capabilities and preferred targets.
This knowledge also makes them better equipped to make informed decisions and set priorities regarding patch management, especially for vulnerabilities that are exploited in the early stages of an attack, such as weaponization, delivery, and exploitation. Preventing attackers from getting a foothold in an organization’s system via initial access vulnerabilities, for example, would cut short their opportunity to exploit lateral movement vulnerabilities entirely.
Examining ransomware ecosystems from as many angles as possible using disparate information sources, including CVE data, is essential for security teams to shift left in the cyber kill chain. By detecting and mitigating attacks long before they reach the encryption and data exfiltration stages, organizations can minimize the impact of ransomware attacks.
The increasing sophistication of modern ransomware attacks necessitates a holistic defense strategy on the part of both organizations and end users, who should keep their systems up to date with the latest patches to mitigate the risk of ransomware infection and stay vigilant by enforcing the following security best practices:
- Enabling multifactor authentication (MFA) to prevent attackers from performing lateral movement inside a network
- Following the 3-2-1 rule when backing up important files by creating three backup copies on two different file formats, with one of the copies stored in a separate location
- Updating their systems regularly, as patch management protocols can help deter malicious actors from exploiting any software vulnerabilities in operating systems and applications
Organizations can also benefit from the use of multilayered detection and response solutions such as Trend Micro Vision One™, which provides powerful XDR capabilities that collect and automatically correlate data across multiple security layers — email, endpoints, servers, cloud workloads, and networks — to prevent attacks via automated protection, while also ensuring that no significant incidents go unnoticed. Trend Micro Apex One™ also provides next-level automated threat detection and response to protect endpoints against advanced issues, like human-operated ransomware.
To read our full report on how data-science approaches can help security experts and industry leaders assess the risk of ransomware attacks on their business, read our research paper, “What Decision-Makers Need to Know About Ransomware Risk.”

