By The Numbers: Ransomware Rising
By the end of 2015, Trend Micro predicted that 2016 would be "the year of online extortion." Thanks to the growing number of new ransomware families—and the ensuing rise of ransomware victims—recorded in the first half of the year, the prediction is turning out to be quite an understatement.
While ransomware isn't new, the malware type is certainly seeing a surge in development, both on the technical and the social engineering side. More cybercriminals are turning to the use of ransomware because it's easy to deploy, and the scare tactics that it uses—involving the prevention of access to files and systems unless a ransom is paid—makes it more likely for victims to pay. And it's not just taking on individual users, as the past months have shown how ransomware can take down entire networks, or severely hamper critical systems of healthcare and educational facilities, as well as other large organizations.
The extortion model has since evolved to the point where Ransomware-as-a-Service (RaaS) has become a viable distribution model. The service lets would-be cybercriminals earn from spreading ransomware without needing any advanced coding or malware creation knowledge, and the proceeds are shared between the operator and the distributors.
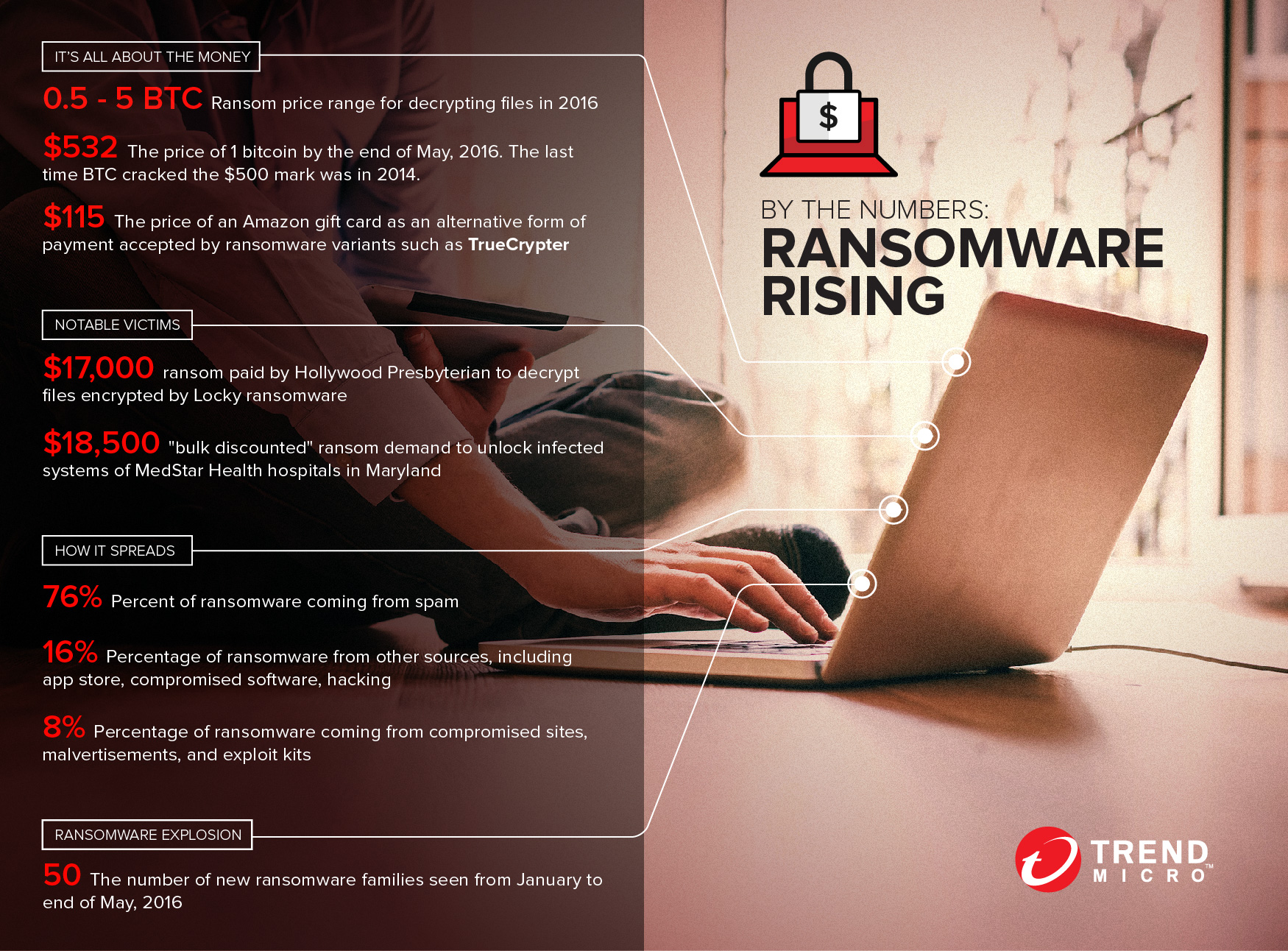
The rapid development of ransomware families, updated variants, as well as new business and distribution models ultimately point to one thing: ransomware is popular because it works. There were 50 new ransomware families released in the first five months of 2016 alone, averaging to 10 new ransomware families a month. With the way things are going, that number is expected to rise—along with the number of victims.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One