Exposed Devices and Supply Chain Attacks: Overlooked Risks in Healthcare Networks
 View Securing Connected Hospitals: A Research on Exposed Medical Systems and Supply Chain Risks
View Securing Connected Hospitals: A Research on Exposed Medical Systems and Supply Chain Risks
Healthcare systems were held hostage by WannaCry in May 2017. The ransomware attack painted a vivid picture of what a digital-borne threat can do to paralyze real-world processes, including actual hospital procedures such as life-saving surgeries. This IT security nightmare prompted discussions specific to the problem of securing connected hospitals. While patients get better and more efficient services when healthcare facilities adopt new technologies, add smart devices, and embrace new partnerships, the digital attack surface becomes broader as well.
To shed light on healthcare network risks that are not getting enough attention, we partnered with HITRUST for the research paper Securing Connected Hospitals. Trend Micro Forward-Looking threat researchers explored two aspects: exposed connected medical systems and devices, and supply chain cyberthreats.
 View Executive Series: Exposed Medical Devices and Supply Chain Attacks in Today's Connected Hospitals
View Executive Series: Exposed Medical Devices and Supply Chain Attacks in Today's Connected Hospitals
Our previous studies regarding exposed devices in internet of things (IoT) or industrial internet of things (IIoT) environments in different states and sectors in the United States, and subsequently in different countries in Western Europe, were a wakeup call for organizations who are not sufficiently securing connected printers, webcams, databases, and even ports. The risk is much more nuanced in the healthcare industry.
We discovered exposed medical systems — including those that store medical-related images, healthcare software interfaces, and even misconfigured hospital networks — which should not be viewable publicly. While a device or system being exposed does not necessarily mean that it is vulnerable, exposed devices and systems can potentially be used by cybercriminals and other threat actors to penetrate into organizations, steal data, run botnets, install ransomware, and so on. Furthermore, it shows that a massive amount of sensitive information is publicly available when they shouldn’t be.
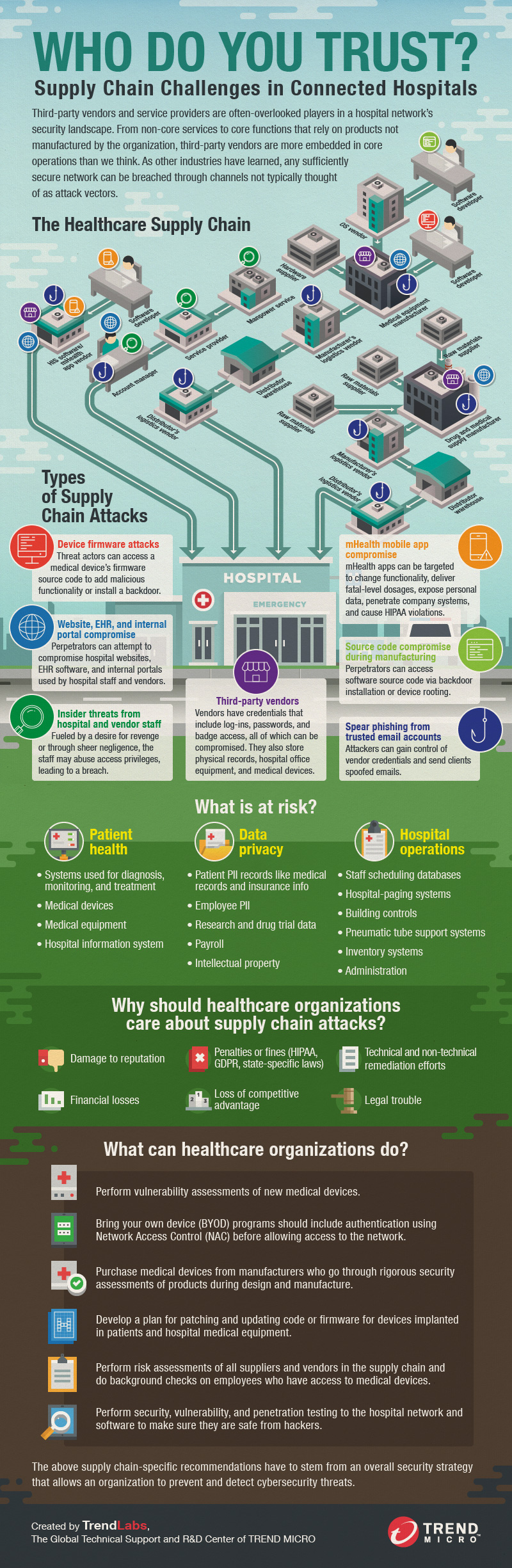
 View infographic: Who do You Trust? Supply Chain Challenges in Connected Hospitals
View infographic: Who do You Trust? Supply Chain Challenges in Connected Hospitals
Supply chain threats, likewise, are potential risks associated with suppliers of goods and services to healthcare organizations: A perpetrator can exfiltrate confidential/sensitive information, introduce an unwanted function or design, disrupt daily operations, manipulate data, install malicious software, introduce counterfeit devices, and affect business continuity. The healthcare industry is more dependent than ever on cloud-based systems, third-party service providers, and vendors in the supply chain. With that in mind, we examined the different entry points that can render a network susceptible to a supply chain attack, and the different kinds of attacks that can be deployed by cybercriminals.
After identifying exposure and supply chain risks, we performed a DREAD threat modeling exercise on healthcare networks in order to understand where, among various threats, the greatest risk lies.
Through this research, we sought to arm healthcare IT security teams with a broader perspective about the kinds of threats that they should defend their networks against. Most importantly, we have provided a set of actionable recommendations, technical and non-technical, to address exposure and supply chain risks. To gain more insight into threats to healthcare-related systems and security measures to address these threats, read our research paper, Securing Connected Hospitals.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Guarding LLMs With a Layered Prompt Injection Representation
- From Anarchy to Authority: Closing the Governance Gap in Agentic AI
- Unconventional Attack Surfaces: Identity Replication via Employee Digital Twins
- Old Vulnerabilities, New AI Era, Amplified Risk: How Outdated Flaws Continue to Fuel the N-Day Exploit Market
- Ransomware Spotlight: Agenda

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation