Cyber Threats
A Blind Spot in ICS Security: Protocol Gateway Part 1
Focusing on potential protocol gateway security risks, we released a white paper summarizing these risks. In the first of this series, we describe the importance of the protocol gateway in ICS environments, and sets the scope of this research.
A protocol gateway is a small network device, also called a "protocol converter" or "IoT gateway." It is similar to an "interpreter" in the digital word, and acts as a communications intermediary between different protocols. As the integration of networks accelerates with IoT, protocol conversion grows increasingly important. However, the security of protocol gateways has not been fully verified so far. Focusing on potential protocol gateway security risks, Trend Micro released a white paper summarizing these risks on August 6, 2020. In this blog series, based on the results of this research, we will analyze the impacts of the serious vulnerabilities detected in the protocol gateways essential when shifting to smart factories, and we will propose the security countermeasures that security administrators in those factories must take. In the first of this series, Part 1 describes the importance of the protocol gateway in ICS environments, and sets the scope of this research.
What is a protocol gateway?
When people communicate with each other, a rule is required in advance for the communication methods between the people in the communication. This rule is called a protocol. For example, people living in a certain region may use English for their protocol, and those people living in another region may use Japanese as theirs. In the region where you live, yet another protocol may be used. Setting up a protocol and obeying it can be said to be a fundamental principle for establishing communications. Therefore, if you want to communicate with someone in a different cultural region, in other words someone using a different protocol, you need to learn their protocol, or to arrange for an interpreter.
The above principle is the same in the IT world. In fact, a more rigorous principle is required. Machines speak their own languages (= protocols), and need to communicate with other machines. As examples, many devices connected to the Internet comply with the TCP/IP protocol, and factory devices communicate via serial ports using the Modbus protocol. As with communications between humans, when one industry device tries to communicate with another, an intermediary is needed, like an interpreter mediating between different cultures. This intermediary is called a protocol gateway, and the "cross-cultural exchange" between these communication devices is called the Internet of Things (IoT). The protocol gateway supports IoT implementation from behind the scenes.
Protocol conversions essential to smart factories
By its very nature, the protocol gateway rarely becomes a popular topic of conversation, but many gateways have been introduced in environments where old and new devices, and IT/OT, must be integrated. The industrial control system (ICS) can be a representative of such an environment. The ICS network integrates Ethernet-based control system networks with serial communication OT protocol-based field networks. The intention to promote Industry 4.0 and Smart Factories spurs on this tendency. As shown in Fig. 1, a protocol gateway is placed between the control-system and the field networks. The gateway converts the protocol on one side to the protocol on the other, allowing devices such as the <>and EWS to communicate with the PLC, and to indirectly exchange data with the actuators controlled by the PLC.<>
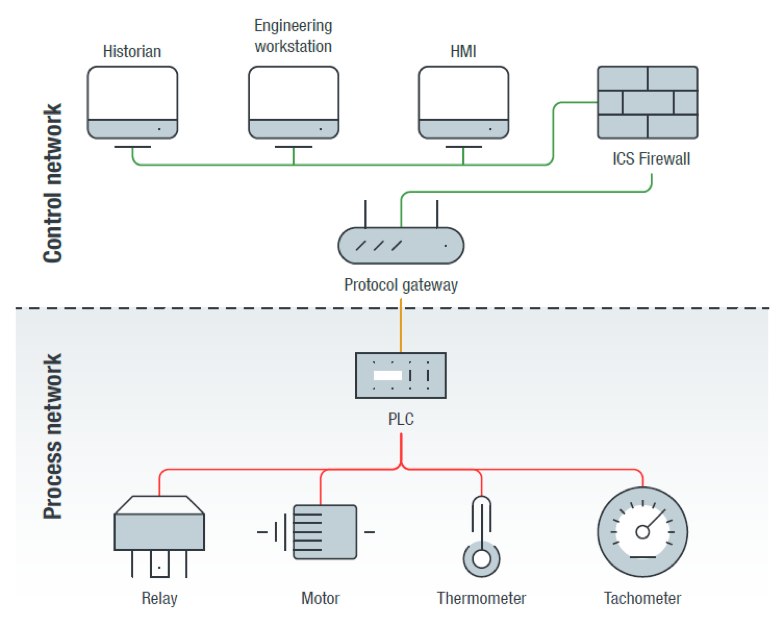
<Fig. 1> An Example of a Factory Network with a Protocol Gateway
As factories, electrical power plants and dams become smart, the protocol gateway function becomes more complicated. This is because the scope of the ICS network is no longer restricted to those factories, but now extends to office networks and cloud services. Therefore, the scope of services covered by the protocol gateway also extends to not only protocols like Modbus TCP, EtherNet/IP, DNP3, PROFINET and MQTT, but also to cloud services such as Amazon Web Services (AWS) and Microsoft Azure. Compared to IT devices, the life cycles of factory devices are longer, so the opportunities for utilizing protocol gateways have been increasing.
A case where a protocol gateway is abused: Power plant attack in Ukraine
A protocol gateway is as large as a home router, with a price range around $300 USD, making it affordable. Since it is an embedded device, the specifications for the CPU and memory are relatively low, compared to routers. However, as described previously, protocol conversion plays an important role in highly diverse network environments. Therefore, if the protocol conversion has a flaw, the impact can be large. A case in point is the cyber-attack on a power plant in Ukraine, reported in 2015.
If a failure occurs in the protocol gateway, communications between the control system and the machines will be disrupted. In this situation, operators in the field who usually run the <>and workstations to control the machines can do nothing. This weakness was attacked on the Ukraine power network. According to the E-ISAC report, the attacker accessed the electric power network control system, and then triggered a power outage by executing a command to open a breaker. The attacker had uploaded modified firmware in advance to disable the electric power substation protocol gateway. As a result, the operator was unable to send the control command to close the breaker. This allowed the power outage to continue over a longer period, resulting in more difficult recovery work. As just described, a small intermediary between IT and OT was lost, causing heavy damage to society.<>
The protocol gateway is a "blind spot" in ICS security
This incident in Ukraine was widely reported, and is well-known. However, few people pay attention to the fact that the protocol gateway vulnerability was abused in this cyber-attack. The reasons are:
- The protocol gateway is a low-cost embedded device with low-level specifications, and is considered to be a simple device for converting protocols. So, it is rare for this device to be treated as a security asset to be monitored.
- If there is a flaw, or abuse in the design of the protocol conversion function, it is very difficult to detect or analyze an attack. This is because even if an error, or intentional fraud, occurs during protocol conversion, the communications itself continue according to a legitimate protocol.
As described above, we predict that few users recognize the protocol gateway as an asset requiring security measures. From a cyber-security viewpoint, the protocol gateway can be called a "blind spot" in the ICS environment. The purpose of this research is to focus on this blind spot and clarify the cyber-security risks so that the appropriate countermeasures will be taken. Specifically, this research aims to identify design flaws in the protocol conversion function shown in point 2 above, and to clearly give security countermeasures that can be taken by users that have introduced protocol gateways in their facilities.
Scope of this research
To achieve the objectives described above, Trend Micro has focused on research on Modbus, which is the world's de facto OT protocol standard. There are a wide variety of communication protocols used in ICS environments, but Modbus is an open standard and can thus provide interoperability between various devices produced by different manufacturers. In addition, for the verification targets for this research, we have selected five protocol gateway models that support Modbus and are widely distributed in the market, and we have evaluated security by using actual machines. Table 1 shows the list of verified protocol gateways.
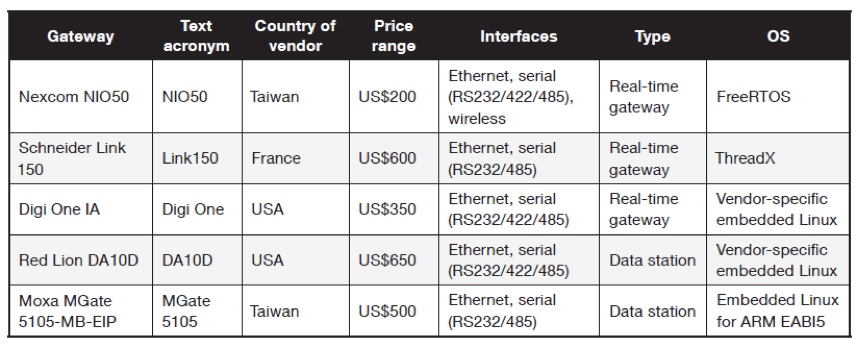
<Table 1> List of Protocol Gateways Verified in This Research
In Part 2, we will present an overview of the verification methods and results of this research, and describe the "flaws in the protocol conversion function," one of the security risks revealed through our experiments.

