Compliance & Risks
Guidelines to secure factories 4: NIST SP800
The purpose of this series is to explain typical examples of general-purpose guidelines for ICS and OT security. Part 4 explains SP800-53, SP800-82, and SP800-171, which are considered to be particularly relevant to general manufacturing industries.
Posts in this series
- Part 1: IEC62443 overview
- Part 2: IEC62443 system
- Part 3: NIST CSF
- Part 5: CIS Controls
- Part 6: MITRE ATT&CK
The purpose of this series is to explain typical examples of general-purpose guidelines for ICS and OT security and understand the concepts required for security in smart factories. Based on the NIST CSF that was introduced in Part 3, from the SP800 series which are guidelines with high specificity, Part 4 explains SP800-53, SP800-82, and SP800-171, which are considered to be particularly relevant to general manufacturing industries.
Laws, regulations, and guidelines in the U.S.
Materials such as guidelines and technical specifications, which are issued by the National Institute of Standards and Technology (NIST), are called Special Publications (SP), and for documents issued by the computer security sector, numbers starting with 800 are assigned, and they are published as the SP800 series.
In laws and regulations in the U.S., FISMA Federal Information Security Management Act of 2002 is included, and as standards specified in this law, FIPS Federal Information Processing Standards is provided.
FIPS199 (Standards for Security Categorization of Federal Information and Information System requires analysis of three security requirements: confidentiality, integrity, and availability in the government's information and information systems, and the degree of impact (high, middle, and low). FIPS200 (Minimum Security Requirements for Federal Information and Information Systems) defines the minimum security requirements for government information and information systems, and the processes for selecting management measures necessary to satisfying the requirements.
SP800-53 is provided as a guide to be used when an organization manages risks and selects security management measures according to the requirements and processes specified in this FIPS.
Based on SP800-53, SP800-82 is prepared for ICS, SP800-161 is for the risk management of ICT supply chains in the government, and SP800-171 is for information management in non-government organizations.
- SP800-53: Security and Privacy Controls for Federal Information Systems and Organizations
- SP800-82: Guide to Industrial Control Systems (ICS) Security
- SP800-161: Supply Chain Risk Management Practices for Federal Information Systems and Organizations
- SP800-171: Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations
SP800-53: Security and Privacy Controls
This is a guideline for security and privacy management measures, and processes for selecting management measures.
When this guideline was revised as rev4 in 2013, descriptions of ICS and supply chains were added to the guidelines. In rev5, which has been released as a draft, it is under consideration that "Federal" will be removed from the title. Therefore, it is considered that various non-government organizations will also be included as targets of this guideline.
First, the selection of management measures is considered as part of a risk management process across organizations, and multi-layered approaches in an organization are specified in these guidelines. Tier 1: the organization level, Tier 2: the mission/business process level, and Tier 3: the information system level. The risk management process is a process for continuously improving an organization's activities by means of effective communication between layers among all stakeholders and effective communication inside each layer.
The organization level in Tier 1 is for prioritizing mission and business functions. This prioritizing determines the financing and investment strategies. Tier 2 is the definition of a business process. Determine the security category necessary for that business process, incorporate requirements into the process, and then establish an architecture. The risk management process in Tier 3 can be indicated in six steps. As a security life cycle, the following steps are specified: Step 1: Categorize, Step 2: Select, Step 3: Implement, Step 4: Assess, Step 5: Authorize, and Step 6: Monitor. SP800-53 corresponds to Step 2: Select.
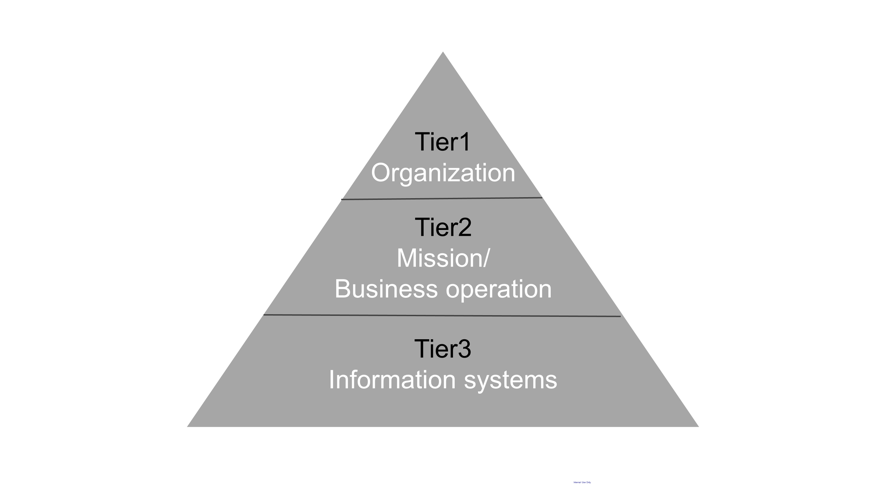
Fig. 1: Three-layered Risk Management Approach (NIST SP800-53)
Next, management measures are shown in the following table. Security management measures (Security Controls) consist of 18 families.
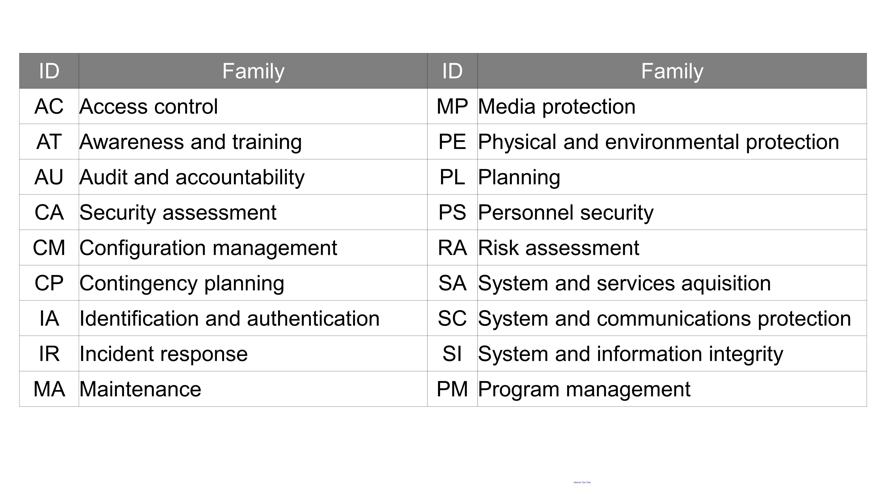
Table 1: IDs and Family Names in Security Controls (NIST SP800-53)
For these security controls, a concept called Baseline is described. The approach of this concept is as follows: classify the degree of impact on systems into three levels expressed as Large, Middle, and Small, define an initial baseline and adjusted baseline, and then analyze the gap between the initial and adjusted baselines. Furthermore, for each security control, its priority is shown in four levels. P1 must be performed with the highest priority. P2 is performed next, and then P3. P0 means out of the target range. According to security controls, multiple reinforcement measures may be specified, and required security controls differ depending on the baseline level.
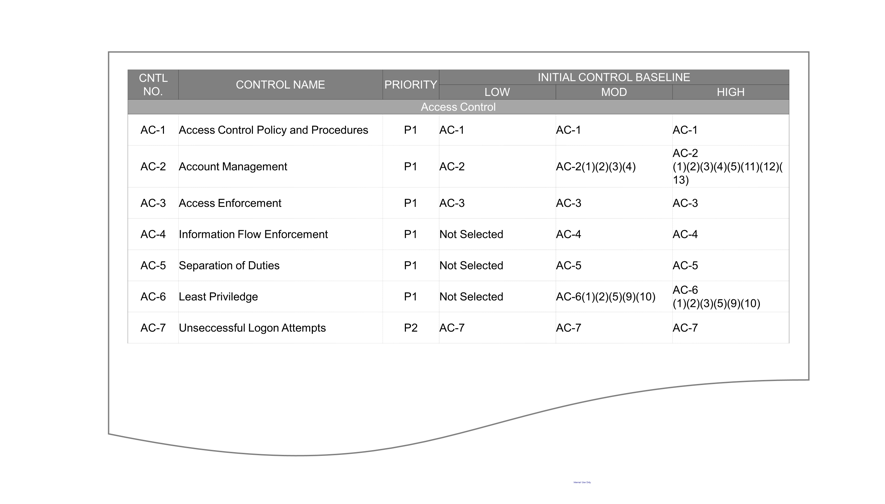
Table 2: Baselines of Security Controls (Appendix D in NIST SP800-53)
Additionally, to enable application of these security controls and baselines to special organizations and systems, a concept called Overlay is also described. A guidance is also attached as an Appendix for application to specific technologies, operation environments, industries, and legal requirements, and adding or removing security controls.
SP800-53 is a massive document with a total of 460 pages, where the catalogs of detailed security controls are attached as appendixes. This is a document that should be referenced from other guidelines as a dictionary for security controls.
SP800-82: Guide to ICS Security
A security guide to industrial control systems (ICS). This is a document that describes how to protect and how to deal with industrial control systems (ICS), including supervisory control and data acquisition systems (SCADA), distributed control systems (DCS), and programmable logic controllers (PLC).
This document carefully describes background ICS environments using many figures of various systems. After the explanation of each of SCADA, PLC, and DCS that are used in ICS environments, differences between IT and ICS are also clarified.
On top of that, it describes the following items which should also be included in the policies of major security controls for implementation in ICS environments.
- Restrictions on logical access to ICS networks and network activities
- Restrictions on physical access to ICS networks and devices
- Protecting individual ICS components from being abused
- Restrictions on illegal modification of data
- Detecting security events and incidents
- Maintaining functions even under adverse conditions
- Recovering a system after the occurrence of an accident
Based on the level of impact, some examples of the definitions of high, middle, and low security levels are described, from the viewpoint of risk management. Definitions based on apprehensiveness in products to be manufactured, industries, and security are also described, and can be used as a guide when you measure impact levels.
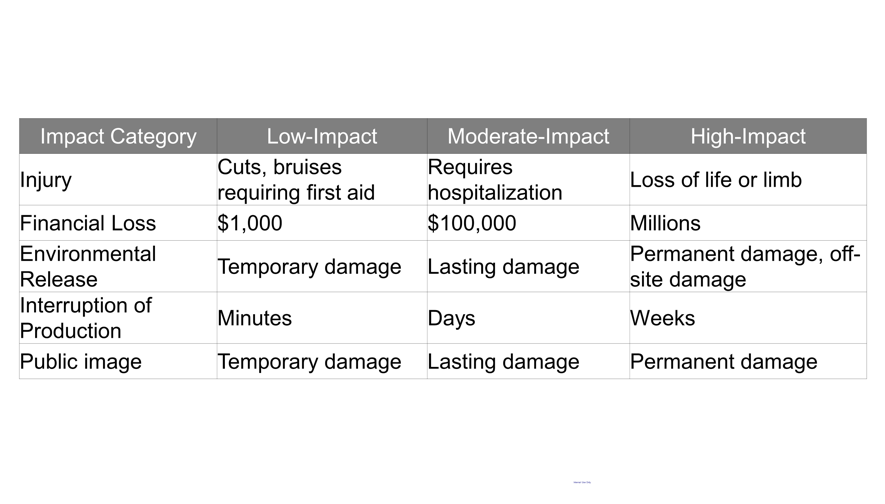
Table 3: Definition Examples of ICS Impact Levels Based on ISA99 (NIST SP800-82)
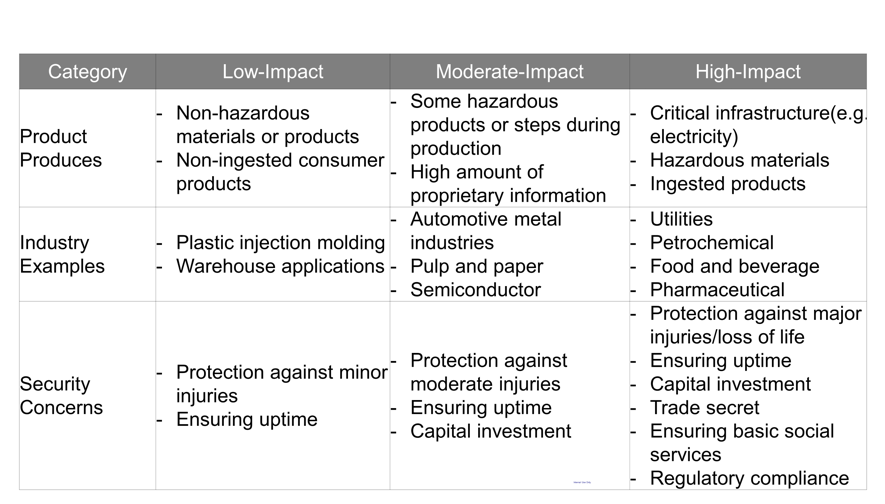
Table 4: Examples of ICS Impact Levels Based on Apprehensiveness in Products, Industries, and Security (NIST SP800-53)
This document describes various points in system design as an ICS security architecture.
First, separate IT networks from ICS networks. Separate these networks so they are independent from each other. If they are connected, it is recommended to keep connections between them to a minimum via a DMZ and a firewall. Next, as one of the most effective architectures, the segmenting and separating of an ICS network are described in this document. Separate a single large ICS network into small networks, from the viewpoints of management authority, policy, reliability, functional importance, communication volume, and so on. The purpose of segmentation and separation is to keep unnecessary access to the systems and confidential information of people to a minimum while the organization continues to keep operating effectively. In addition, system design methods specializing in ICS security, such as various methods for separating networks and the setting of firewall rules, are also described in the document.
For security controls, the document describes that many controls in SP800-53, mentioned above, can be applied to ICS environments. On the other hand, for some controls, additional information is described regarding application to the environments because ICS-specific changes or extensions of interpretation are needed.
SP800-171: Protecting Controlled Unclassified Information
SP800-171, for which rev.1 was issued in 2018 and rev.2 was issued in February, 2020, can be said to be requirements for private organizations directly related to procurement by the U.S. federal government, but it gets much attention as a document that could be a standard for global supply chains.
This is an information management guide for Controlled Unclassified Information (CUI). However, as a paired term, there is a term, Classified Information (CI). This is an image where CI covers a country/government's confidential information and CUI covers other critical information.
The feature of SP800-171 is that it does not target organizations, but targets the acquisition of security requirements for organizations and systems that handle information. Therefore, as organizations that handle information on the job, not only companies and institutions but also so-called subcontracting companies are required to comply with these guidelines.
On the website of the U.S. National Archives and Records Administration (NARA), the list of CUI categories is available, and it may be acceptable to consider the list as including all information handled as confidential information in general companies because the list includes a wide range from critical infrastructures and national defense to privacy.
In CUI, security requirements for protecting confidentiality are grouped into 14 categories, and for each category, basic security controls and derived security controls are described. In total, 110 security controls are described.
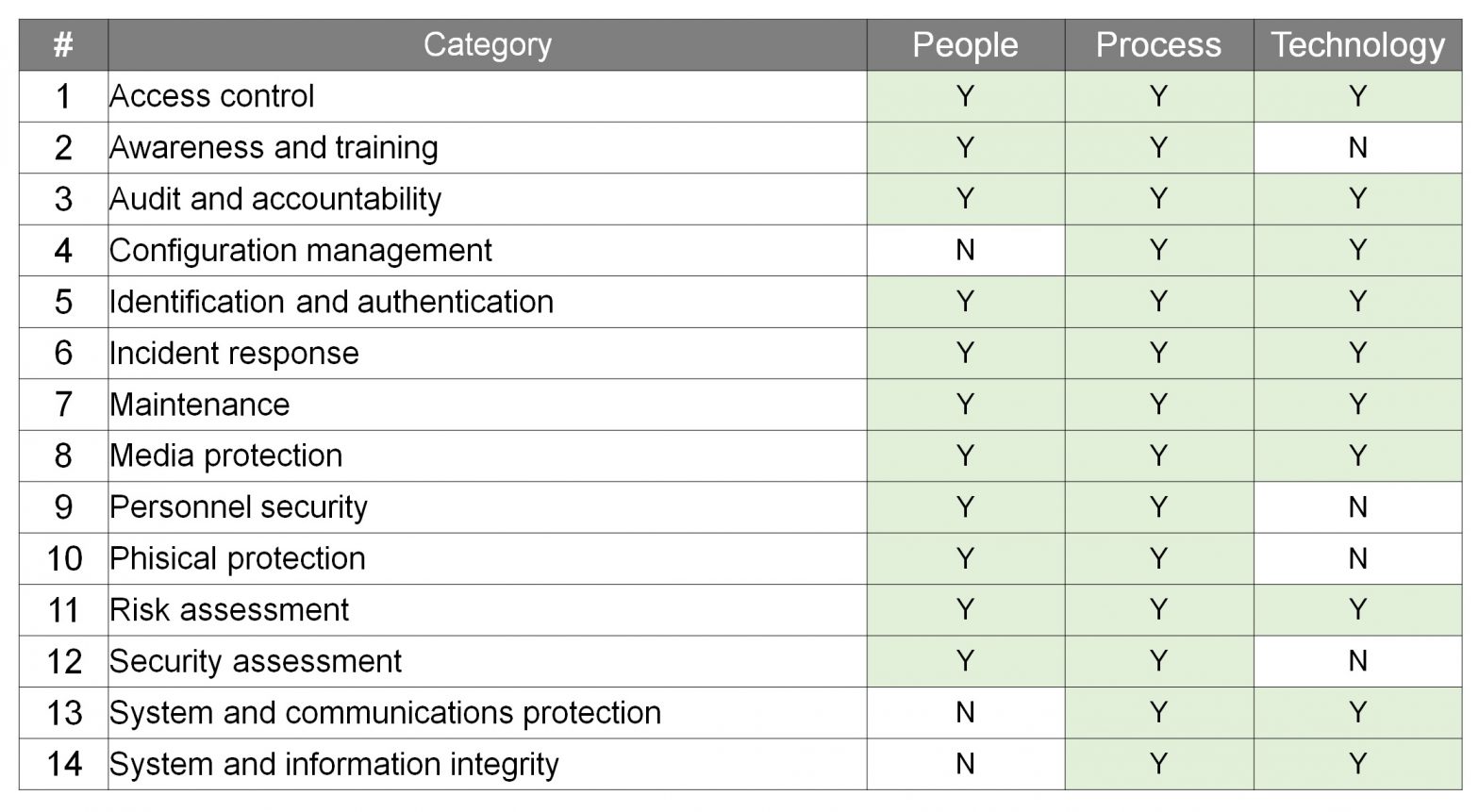
Table 5: Security Requirements and Classification in SP800-171 (Trend Micro)
If security controls for categories are tagged according to organization/person-based controls, rule/operation-based controls, and technology/tool-based controls, then it can be considered that the guidelines are generally based on management in the rule/process phases. In addition to technical measures, risk-assessment processes, and as organizational measures, training, accountability, and reporting to supervisory agencies upon the occurrence of an incident are also included in the requirements.
Part 4 has dealt with and explained some topics from the NIST SP800 series. Originally, they were guidelines that started as procurement requirements by the U.S. government, but it can be said that the integrated management of IT and ICS environments in the security phase and the protection of critical information in a supply chain are essential for promoting organizations and businesses, regardless of specific countries and businesses.
The next Part 5 will deal with CIS Controls, which are defined as a subset of SP800-53.
*References:
NIST SP800-53 rev.4
NIST SP800-82 rev.2
NIST SP800-171 rev.2
NARA: CUI category

