Compliance & Risks
Guidelines to secure factories 2: IEC62443 system
In this seres, we describe typical examples of general-purpose guidelines for ICS and OT security and understand the concepts required for security in smart factories. Part 2 describes the concepts of system design and security levels in IEC62443.
Posts in this series
- Part 1: IEC62443 overview
- Part 3: NIST CSF
- Part 4: NIST SP800
- Part 5: CIS Controls
- Part 6: MITRE ATT&CK
The purpose of this series is to describe typical examples of general-purpose guidelines for ICS and OT security and understand the concepts required for security in smart factories. Part 2 describes the concepts of system design and security levels in IEC62443.
Zones and conduits
In system design in IEC62443, a concept called Zones and Conduits is recommended for the network segmentation of Industrial Automation Control System (IACS) according to Defense in Depth. This is the concept that restricts requirements for a conduit connecting a group to another group by separating assets (devices and systems) into groups with common security requirements.
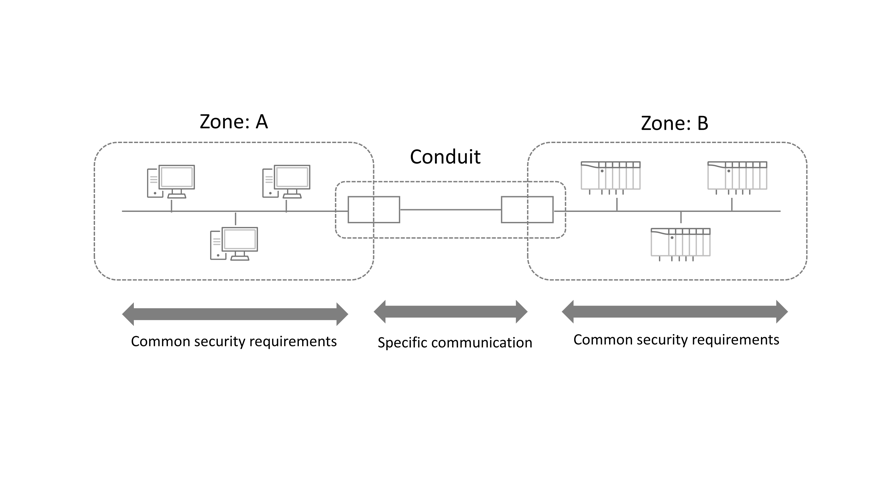
Fig. 1: Zones and Conduits (by Trend Micro, based on IEC documents)
A point on how to separate assets into zones is to identify security requirements and define them as common requirements. Define a level for each Foundation Requirement (which is described later), and then separate assets into groups according to common requirements and levels. Then, separate assets physically and logically, and clarify boundaries between zones. It may be difficult in the field not only to separate assets according to logical requirements, but also to set physical boundaries. However, if an asset with a different requirement or level coexists in the same group, then the security technologies and operations to be used are not fixed, and thus inefficient.
Levels 0 to 4, which are defined in the Purdue Enterprise Reference Architecture (PERA) model, may become big zones, but it is said that the practical approach is to set sub-zones in each level if needed.
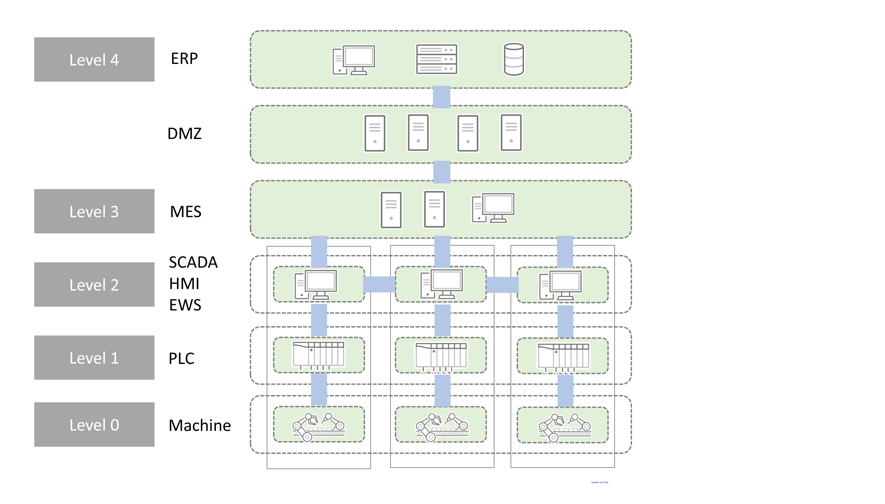
Fig. 2: An Architecture Image (by Trend Micro)
Security requirements and levels
Basic security requirements for the assets and zones of IACS are defined in seven standpoints called Foundation Requirements (FR).
Foundation Requirements (FR)
- IAC (Identification and Authentication Control)
- UC (User Control)
- DI (Data Integrity)
- DC (Data Confidentiality)
- RDF (Restricted Data Flow)
- TRE (Timely Response to Events)
- RA (Resource Availability)
Each requirement for assets and zones is set by assigning a level for each of these seven items (e.g. FR1 in a certain zone is assigned Level 2, FR2 is Level 1, FR 3 is Level 2, and so on).
The security level (SL) is a five-level rating system, and each level is conceptualized as follows: SL0 is where there are no requirement definitions nor protections, SL1 is where there is a basic protection for preventing accidental violations, and SL4 is where there is a sophisticated protection for preventing intentional attacks.
To measure a security level, System Requirements (SR) are specifically defined for each Foundation Requirement (FR). Furthermore, for each System Requirement (SR), Requirement Enforcements (RE) are specified to satisfy each Security Level (SL).
For example, in the System Requirement (SR) that specifically defines "FR5. Restricted Data Flow,"
- SR5-1. Network segmentation,
- SR5-2. Zone boundary protection,
- SR5-3. General purpose person-to-person communication restrictions,
- SR 5-4. Application partitioning
are included.
In "SR5-1. Network segmentation" described above, as requirement enforcements (RE),
- RE (1) Physical network segmentation,
- RE (2) Independence from non-control system networks,
- RE(3) Logical and physical isolation of critical networks
are specified.
In SR 5.1, if RE (1) is satisfied, then it is SL2, if RE (1)(2) are satisfied, then it is SL3, if RE (1)(2)(3) are satisfied, then it is SL4, and so on. For all of the seven Foundation Requirements (FR), if it is considered to be SL4, then it is necessary to satisfy at least 100 requirements.
In addition, for the system design of zones and conduits in IEC62443, documentation is required, including the stocktaking of assets, preparation of network configuration diagrams, requirements, and levels.
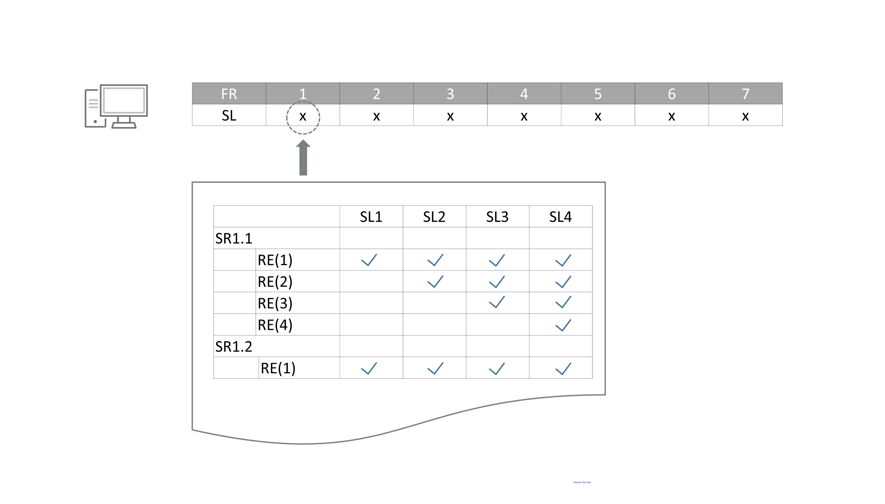
Fig. 3: FR, SL, SR, and RE (by Trend Micro, based on IEC documents)
Security level and efficiency
What should be noted here is the following: it is not good that simply all security requirements are satisfied and the security level is high. The important thing is to separate assets into groups according to common requirements.
For example, if an EWS for design and a PLC for controlling a machine exist in the same zone, then the same security requirements and levels are their target values, but their capabilities and operations are different and thus the measures for filling in the gaps between their capabilities and target values may be different. In addition, if a certain Windows machine is used for both the monitoring of a system and the programming of control programs, then it is desirable for the promotion of streamlining to prepare another machine and separate the machines according to their application, and place them in separate zones.
By establishing zones according to security requirements and levels, it is possible to standardize countermeasure technologies and operations in zones. Furthermore, this concept is considered as follows: in a conduit for connecting a zone to another zone, it is possible to simplify the role of the conduit by restricting the protocols used, by identifying the type of data, and by restricting the direction of communication, which will lead to the improvement of the efficiency and effectiveness of security in total.
If communication in a certain conduit requires many protocols and is complicated, then it is suspected that the target zone is too large, and thus it is necessary to review the zone. Set up a new conduit by separating a zone into sub-zones. A general tool to control the security of a conduit is a firewall. This is because it is possible to set determined requirements as rules to permit or reject communication between zones. By identifying assets with IP and MAC addresses in a zone, it is possible to restrict the communication protocols used by conduits. In addition, it is also said that the protocol filter provided by IPS is a valid technology to enhance the control of communication.
Trend Micro provides solutions for smart factories as layered solutions as follows:"Prevention", "Detection", and "Resilience". When you consider the construction and operation of a system according to the concept of Zones and Conduits, it is recommended to visit and view the solution page of Trend Micro.
In the concept of Zones and Conduits in IEC62443, a concept called Defense in Depth is underlain, but in the relationship between the importance of assets and security levels, there is a difference between IACS and IT.
For IT, in many cases, more important systems and data should be placed on a deeper layer away from the outside world, and protected more strictly with more sophisticated technologies. On the other hand, for IACS, in most cases, sophisticated security technologies are not suited for assets that are essential in operation. On a terminal with limited computing resources, a sandbox with a heavy load and machine learning will not operate, and when you need to try the emergency stop of a manufacturing machine, if the entry of an at least 8-character password is requested like a PC, or if a retrial occurs in the fingerprint or face authentication like a smartphone, then such a system is inefficient. When you need to protect a region that is not suited for the security of individual assets or the enforcement of local security capability, it is also said to be meaningful to separate all of the assets and stratify the security according to both technical and operational aspects.
Part 1 and Part 2 have explained IEC62443, which is an international standard for industrial control systems. The next Part will deal with NIST CSF, which is another general-purpose international standard.
Reference: https://webstore.iec.ch/searchform&q=62443#

