Ransomware has been one of the most prevalent, prolific, and pervasive threats in the 2017 threat landscape, with financial losses among enterprises and end users now likely to have reached billions of dollars. Locky ransomware, in particular, has come a long way since first emerging in early 2016. Despite the number of times it apparently spent in hiatus, Locky remains a relevant and credible threat given its impact on end users and especially businesses. Our detections show that it's making another comeback with new campaigns.
A closer look at Locky’s activities reveals a constant: the use of spam. While spam remains to be a major entry point for ransomware, others such as Cerber also employ vectors like exploit kits. Locky, however, appears to concentrate its distribution through large-scale spam campaigns regardless of the variants released by its operators/developers. Here’s a visualization of its distribution from January 2 to September 8:
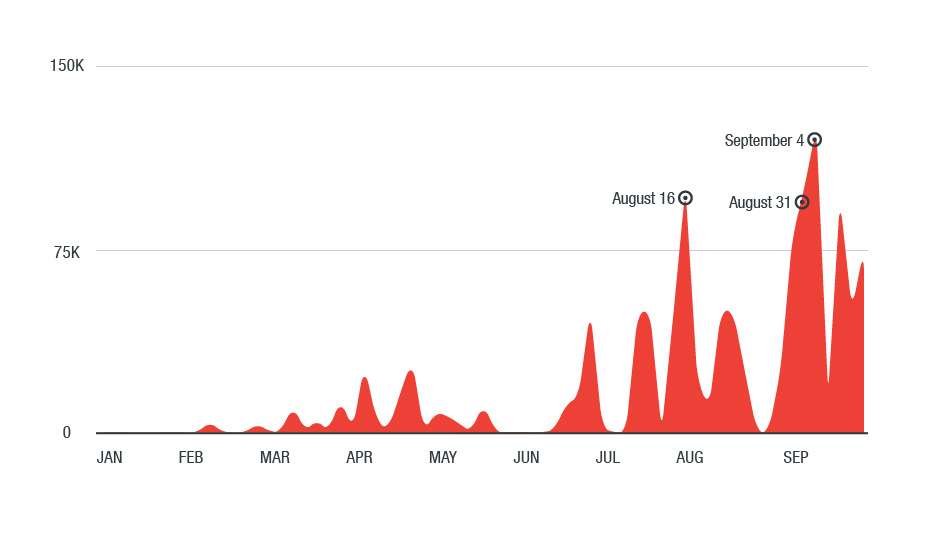 Figure 1. A timeline of Locky ransomware detections based on partial feedback from our email-based sensors
Figure 1. A timeline of Locky ransomware detections based on partial feedback from our email-based sensors
The Necurs Connection
We’ve also found how the scale and scope of Locky’s distribution are fueled by the Necurs botnet, a spam distribution infrastructure comprising zombified devices. It churns out a sizeable amount of spam emails carrying information stealers like Gameover ZeuS, ZBOT or Dridex, and other ransomware families such as CryptoLocker, CryptoWall, and Jaff.
Necurs is Locky’s known and long-time partner in crime, and it’s no coincidence that the surge of Locky-bearing spam emails corresponds with the uptick in Necurs’ own activity. In fact, we saw that Necurs actively pushed Locky from August to October. Here’s a timeline:
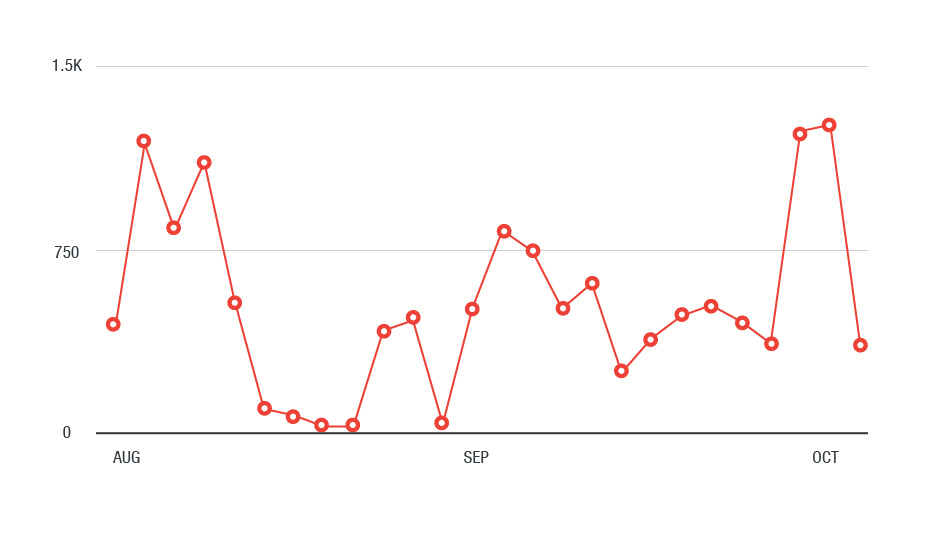 Figure 2. Necurs botnet distributing Locky variants from August 29 to October 11, 2017
Figure 2. Necurs botnet distributing Locky variants from August 29 to October 11, 2017
It’s also worth noting that Necurs also distributed Locky via URL-only spam emails—that is, the messages didn’t have any attachments, but rather links that divert users to compromised websites hosting the ransomware. The use of HTMLs embedded with links to the compromised site also started gaining traction this year.
Interestingly, we saw a sizeable URL-only spam campaign that delivered the Trickbot banking malware (TSPY_TRICKLOAD) separately. The routine is similar to another campaign we observed, where cybercriminal operators rotated their payloads between FakeGlobe and Locky. In some of our tests, we found that the payload depended on the region: western countries are more likely to be served with Trickbot, while countries like Japan and Taiwan, for instance, are more likely to get Locky.
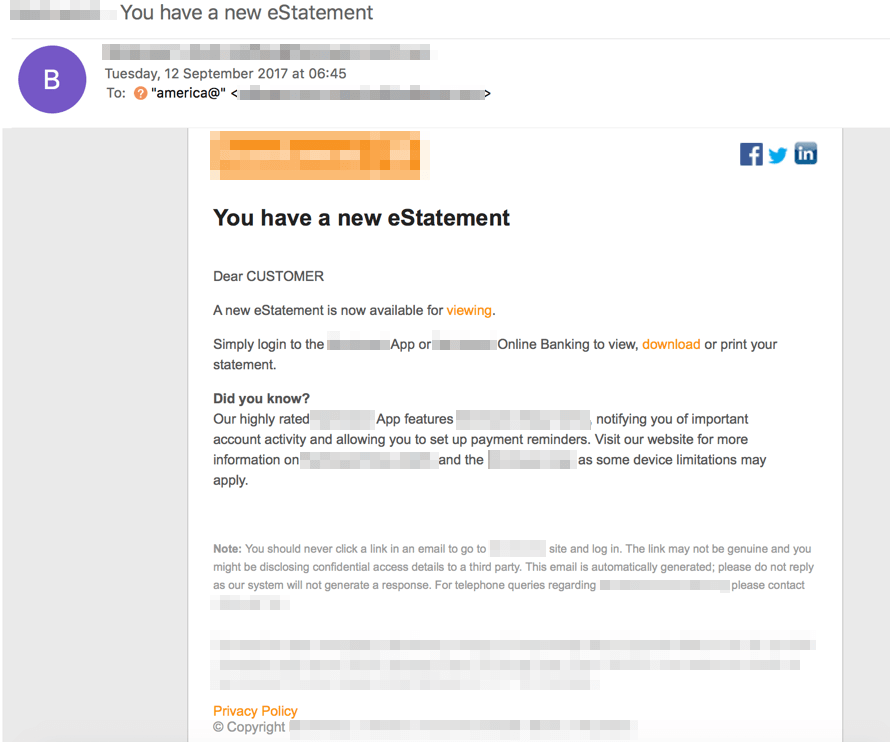 Figure 3. A sample URL-only spam email that delivered either Trickbot or Locky
Figure 3. A sample URL-only spam email that delivered either Trickbot or Locky
Spam attachments: Locky’s testing ground?
The timing of Locky’s lulls and surges matches other cybercriminal activities. They can also be construed as intervals used to fine-tune and diversify Locky’s infection chains. This is the likeliest case with the recent Diablo and Lukitus variants, which used malicious (or posed as) PDF and image files (i.e., JPEG, TIFF). They are deviations from the usual vectors, Word documents embedded with malicious macro code or Visual Basic scripts (VBS).
And indeed, we’ve seen Locky diversify in terms of the spam email attachments it uses. Necurs botnet, for instance, increasingly favors the distribution of spam emails with HTML files. The Locky spam campaign we monitored in mid-September also used Word documents with malicious macro, but coded to run and download Locky after the user closes the file. Locky also abused Windows Script File (WSF) and dynamic-link libraries (DLL) as infection vectors, so it's not implausible for the ransomware to misuse other file types and expand beyond macros, VBSes, or HTML files. Here’s a breakdown of the file attachments used by Locky-laced spam emails we’ve seen so far:
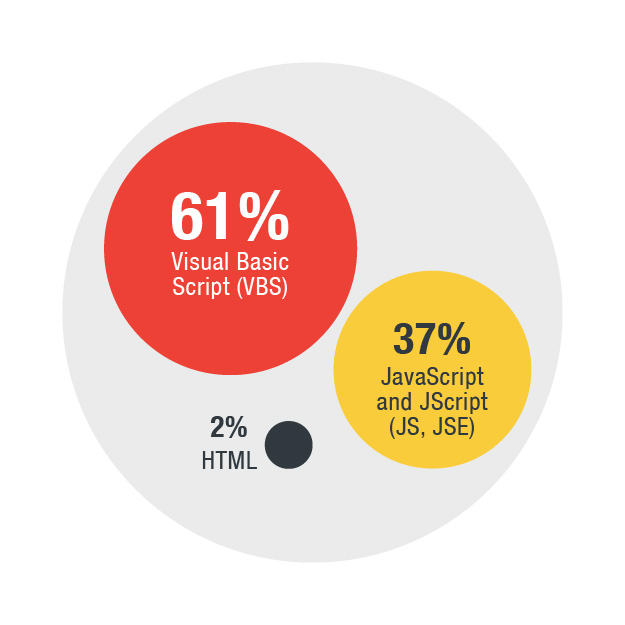
Figure 4. The file types used by Locky-carrying spam emails in from January to September 2017; note that the VBS, JS, and JSE files are archived via RAR, ZIP or 7ZIP files
Locky’s common social engineering lures
Indeed, the continuous changes in Locky’s use of file attachments are its way of adjusting its tools to evade or bypass traditional security. But despite the seeming variety, there are common denominators in Locky’s social engineering, particularly in the email subjects and content. They appear to have the same old flavors, but with relatively different twists. Some of the recent lures we saw were:
- Fake voice message notifications (vishing, or the use of voice-related systems in phishing attacks)
- HTML attachments posing as invoices
- Archive files masquerading as business missives from multinationals, e.g., audit and budget reports
- Fraudulent emails that involve monetary transactions such as bills, parcel/delivery confirmations, and payment receipts
Mind your gaps
The delivery mechanism is a critical component for any ransomware. Locky’s infection vectors—and its adverse impact on affected systems—demonstrate the significance of a multilayered approach to safeguarding the privacy, security, and integrity of the gateways, endpoints, networks or servers that manage or store mission-critical, corporate or personal data. Follow and apply best practices against ransomware: keep the system patched, secure the email gateway, and regularly back up data. Enterprises should implement defense in depth: enforce the principle of least privilege, keep the system and its applications updated (or employ virtual patching), and incorporate additional layers of security against malicious files and network activities that can be exploited by ransomware. More importantly, foster a culture of cybersecurity—the technologies that thwart threats are only as effective as the people who use them.
Trend Micro Solutions
Trend Micro™ Hosted Email Security is a no-maintenance cloud solution that delivers continuously updated protection to stop threats like Locky before they reach the network. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro™ Smart Protection Suites, powered by XGen™ Security, deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes Locky’s impact.
Trend Micro™ Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud. Trend Micro™ Worry-Free Services Advanced offers cloud-based email gateway security to small businesses through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware. For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.

