Securing the Industrial Internet of Things: Protecting Energy, Water and Oil Infrastructures
 Innovations in critical infrastructure (CI) sectors have started augmenting traditional operational structures for “smart” facilitation, and more industries are expected to follow suit: According to Gartner’s research, 25% of on-site industrial assets will replace traditional assets with information technology (IT) and operational technology (OT) assets by 2023.
Innovations in critical infrastructure (CI) sectors have started augmenting traditional operational structures for “smart” facilitation, and more industries are expected to follow suit: According to Gartner’s research, 25% of on-site industrial assets will replace traditional assets with information technology (IT) and operational technology (OT) assets by 2023.
Unfortunately, security becomes a mounting concern as more industrial control systems (ICS) equipment enter the market and businesses become a part of the larger and interdependent supply chain. Previous research found that organizations involved in these industries may not have the security procedures and policies in place to mitigate threats.
Given the expected expansion of industrial internet of things (IIoT), this guide looks into the possible security risks, threats, and scenarios that could compromise the energy, water, and oil industries. This review also includes some recommendations on how to defend against these attacks based on Trend Micro (TM) research.
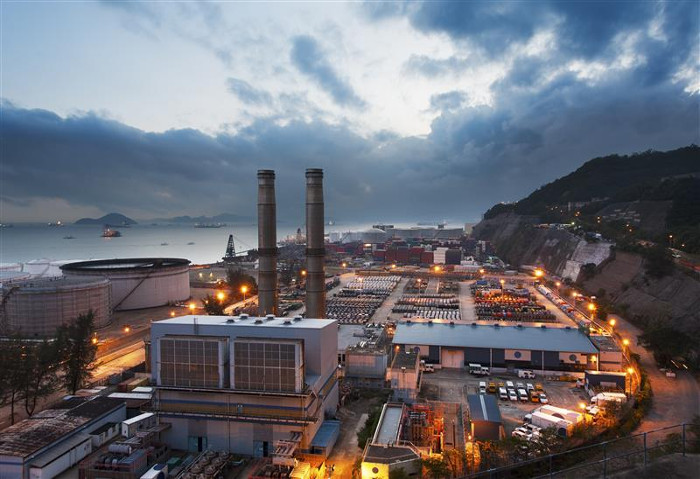
Energy and power
Vulnerabilities and exploits: The energy and power sector is one of the CIs with the most reported vulnerabilities. Vulnerabilities such as Aurora and malware such as BlackEnergy allow attackers to shut down distribution grids and disrupt other industries. Successful attacks on these vulnerabilities can render expensive industrial hardware useless and destabilize the city or country’s facilities, homes, and businesses.
Exposed SCADA/HMI: Sophisticated attacks can be executed via exposed supervisory control and data acquisition (SCADA) systems. Malicious actors behind such attacks gather information on the facilities such as the layout, the devices and machinery used, the hardware’s enabled settings, and the structural and machinery thresholds that can be used to trigger dangerous attacks. SCADA’s human machine interfaces (HMIs) gives real-time information to operators, and attackers can exploit vulnerabilities in HMI software to gather the necessary data, take command of the systems, or use them in an attack.
Malware: Cybercriminals use malware attacks to profit from the urgency to restore affected services as soon as possible. This was the case in the Ukrainian Power Grid attack in 2015, which left residents in the dark for hours towards the end of the year. Ransomware attacks on power plants and other CIs have also become more common, likely because cybercriminals are hoping that affected organizations would pay to immediately restore systems and files. Availability and uptime are key in OT environments, which makes them ideal targets for ransomware-based attacks.
Recommendations: Establish a regular patching and update policy for all systems. Download patches as soon as possible to prevent cybercriminals from exploiting these security flaws. Research found that manufacturers take an average of 150 days to patch reported vulnerabilities from the day of notification, thereby giving IT and security teams ample time to prepare for the needed system updates. Businesses should implement a regular cybersecurity awareness campaign to keep employees aware of the latest techniques that cybercriminals use in their attacks. IT administrators should apply the principle of least privilege to make monitoring of inbound and outbound traffic easier. Install a multilayered protection system that can detect and block malicious intrusions from the gateway to the endpoint.
[Read: Protecting critical infrastructure and roadways: How smart cities create new risks]

Figure 1. Threats to water, power, and oil industries.
Water
Vulnerabilities and exploits: CIs commonly have more than one infrastructure function to maximize the facility's space and energy. For instance, water treatment plants will usually have a wastewater treatment plant, a sewage treatment plant, or a connected man-made water source such as a dam. And according to the Environmental Protection Agency’s (EPA) Homeland Security Research Program, infrastructure resilience and incident response not only pertains to water treatment facilities but also the defense and integrity of sources, related peripherals, components, and structures from intentional contamination and natural disasters.
In a manuscript prepared for the Department of Energy, researchers pegged water treatment plants as the fourth most vulnerable CI in the U.S. after the EPA recorded 25 cybersecurity incidents involving water treatment plants and related infrastructures between 2014 and 2015. While citing no specific details on these events, the research cites that water facilities should defend against advanced persistent threats (APT), attacks, and vulnerabilities. Some of the vulnerabilities they included in the report include the organizations’ failure to integrate older SCADA systems with newer business networks, network configurations, media protection, remote access, policies and procedures, and personnel. One cited example is the intrusion attack on the Maroochy Shire Sewage Spill in Australia, where a disgruntled former employee dumped raw sewage water into other fresh water sources such as parks, rivers, and hotel grounds.
Exposed SCADA/HMI: As HMI systems manage the entire process of CI systems, compromising the HMI allows the attacker to cause a lot of damage, from harvesting data and proprietary information to attacking the critical architecture that controls the equipment. Scanning for exposed HMIs related to water treatment and wastewater facilities on Shodan, Trend Micro researchers were able to observe real-time data and information pertaining to processes such as filtration and disinfection, emergency trigger conditions, subsystem status, and flow control functions affecting distribution. One HMI console in Colombia even showed an unauthenticated window, though it is unclear if the menu access was already authenticated prior to the observation. However, changing screenshots mean that the systems were live and none of the operators noticed that their systems were visited by Shodan crawlers more than once.
HMI interfaces accessible via unauthenticated servers exposed to scanning tools not only provide attackers with data that they can use to access other parts of the plant and the network, but also allows them to control the entire system. If exploited, attackers can control the use of chemicals, or overload and affect temperatures to disrupt or cause malfunctions to machines, affecting the drinking water distributed to the area and the public’s health with waterborne diseases. Verizon reportedly disclosed one such close call in Syria in 2016, while another report summarized that various malware seen in a number of regions were targeting ICS/SCADA systems in Latin America.
Malware: In 2018, a Monero cryptocurrency mining malware reportedly infected four servers connected to an OT network in Europe. The malware caused the CPU and network bandwidth consumption to increase, slowing down the HMI and SCADA servers monitoring the operations and responses needed for distribution. For the first quarter of 2019, it was reported that close to 70,000 water and wastewater facilities in the U.S. struggled to keep up with evolving cybersecurity threats. Ransomware is a constant concern for a number of CIs, with some cybercriminals taking advantage of disasters to attack.
Recommendations: Deploy redundant security measures throughout the ICS/SCADA environment. Basic measures such as a firewall/IPS between the business network and the ICS network, multiple authentication measures restricted to a limited number of authorized personnel, and a patch management procedure reduces the attack surface for cybercriminals. Practice network segmentation to partition the systems into distinct security zones to isolate the critical parts of the system, especially in instances of a breach or attack. Physical and environmental security should also be enforced and limited only to those authorized to be around critical ICS assets or handle the equipment.
[Read: How the industry 4.0 era will change the cybersecurity landscape]
Oil and gas
Vulnerabilities and exploits:Considering the industry’s dependence on computer automation because of the remote operation required between onshore locations, plants, and business units, an attack in one system may inevitably lead to a chain reaction. This was among the instances that exposed Norway’s oil and energy companies to attacks in 2011 and 2014, where attackers breached the systems and spread across the networks and systems of around 300 organizations. Investigations revealed that the unidentified cybercriminals studied the affected companies and authorized personnel and sent them malicious emails that infected the companies' networks.
Exposed devices, SCADA/HMI/SIS: Given the volatility of gas and the risks accompanying the business, oil and gas retailers invest in automation to monitor and handle daily operations. Employees oversee these systems from the rigging wells for extraction, to transporting the resources via pipelines, and refining in plants before being distributed for commercial and industrial purposes. These plants and their respective activities can be tracked online.
Geostalking, or finding the actual location of plants via gathered online data, can be used to conduct a vulnerability assessment by validating the IP addresses to match the ICS devices. Once the attackers find their targets, the attacker can check for similar devices and security gaps in the entire network. Since an organization is likely to have a similar device, network, and security setup for the entire facility, an attacker could cause massive damage using a single attack routine.
Researchers found exposed HMI controllers and safety instrumented systems (SIS) exposed and vulnerable to attacks, respectively, when they discovered TRITON/TRISIS, a malware designed to target a specific SIS model used by oil and gas facilities in the Middle East. In another study, researchers deployed a GasPot, or gas-tank-monitoring system honeypots, to observe and monitor for malicious interests despite the legal implications of attacking CIs. They saw several intrusions via remote access of a hypothetical automated tank gauge (ATG), which was used in a distributed denial of service (DDoS) attack, defacements, and code modifications.
Unauthorized access to an exposed HMI could lead to more damaging repercussions, as it allows a malicious actor to control valve flows, reconfigure parameters, and cause heavy losses and shutdowns down the supply chain with one attack. A pump failure can cost an organization $100,000 to $300,000 per day, aside from possibly shutting down related industries like electricity and power supplies in an area.
Malware: Similar to the water sector, the oil and gas industry have a number of derivative byproducts that affect a number of businesses, especially large petroleum plants. Plastics, textiles, detergents, and fertilizers are just some of the businesses related to oil companies via chemical synthesis, therefore making the supply chain more viable, dynamic, and dependent. In the case of Iran’s petrochemical attack in 2016, a number of equipment were found preinstalled with malware that infected two of the plants.
In 2012, a targeted scam email sent to an employee of Saudi Arabia’s national oil company contained Shamoon, causing a downtime that lasted for months and costing millions of dollars. A report also cited the same company as the target of another malware attack in 2017, though the company denies any breach into their computer system.
Recommendations: Review and implement access policies and controls relevant to specific personnel, network, devices, services, electronic, and physical authorization. This encourages a culture of security and awareness among the relevant employees. Perform periodic assessments and audits of the systems’ life cycle to make sure configurations are secure. Check the cybersecurity policies and procedures, and conduct regular vulnerability assessments of supply chain partners, especially those who may have remote or direct access to the network or any of the ICS systems.
[Read: Water and energy sectors through the lens of the cybercriminal underground]
Conclusion
While critical infrastructures integrate smart platforms and enterprises develop better cybersecurity awareness, security — integrated into planning and design for these smart technologies and infrastructures — is still far from adequate. Despite the investment needed for attacks to such infrastructures, cybercriminals still choose to take advantage of security gaps in systems as this could lead to bigger issues due to the interdependent nature of CIs. Businesses will have to be vigilant — online and offline — to secure these critical infrastructures.
While cybercriminals' motivations vary, all organizations involved in the supply chain of critical infrastructures will have to defend against these threats. Even if it is expected that larger companies involved in the main service distribution will have better security measures in place, smaller businesses acting as third party suppliers will have to secure their respective channels with equal priority. Given the interest and discussions in the underground for the systems used in these industries, the similarities — from the kind and function of devices used, to the specific devices themselves — imply that an attack on one industry can inflict the same damage on another in an otherwise completely different sector.
As breaches and unauthorized intrusions have become more rampant, companies will have to establish effective monitoring, blocking, notification, containment, and mitigation procedures, in place — besides establishing policies, and employee awareness programs. IT and security teams not only have to keep themselves abreast with the latest threats pertaining to their respective industries, but will also have to ensure uninterrupted services and operations by installing multilayered protection systems. While this may imply redundancies and increased resource allocation, the integration of IIoT with CIs for increased productivity, combined with the assurance of security, shows that enterprises understand the threats that they face and the consequences of inaction or complacency.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One