Security 101: Zero-Day Vulnerabilities and Exploits
 View Infographic: Security 101: Zero-Day Vulnerabilities and Exploits
View Infographic: Security 101: Zero-Day Vulnerabilities and Exploits
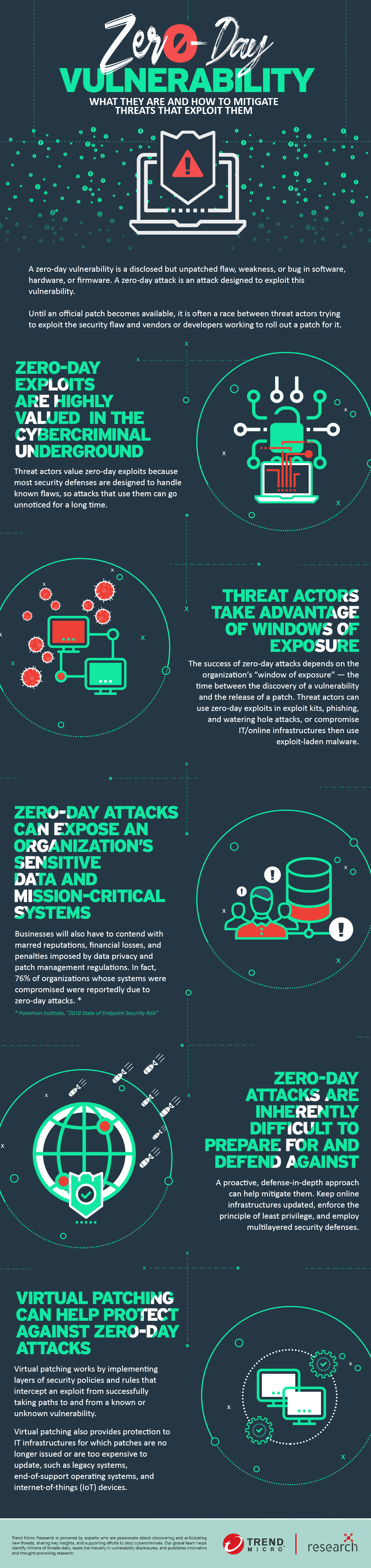
A zero-day attack exploits an unpatched vulnerability, and could significantly affect organizations using vulnerable systems. Until a patch becomes available, it is often a race between threat actors trying to exploit the flaw and vendors or developers rolling out a patch to fix it.
Here's an overview detailing what businesses need to know about zero-day vulnerabilities — what they are and how they work — so they can better mitigate the risks and the threats that exploit them.
What is a zero-day vulnerability?
A zero-day vulnerability is a flaw, weakness, or bug in software, firmware, or hardware that may have already been publicly disclosed but remain unpatched. Researchers may have already disclosed the vulnerability, and the vendor or developer may already be aware of the security issue, but an official patch or update that addresses it hasn’t been released.
The flaw is referred to as a “zero-day” vulnerability because the vendor or developer — and accordingly, the users and organizations whose systems are affected by the vulnerability — have just learned of the vulnerability. Once the vulnerability becomes public and the vendor or developer already deployed a patch for it, it becomes a known, or “n-day” vulnerability.
What is a zero-day exploit or attack?
When hackers or threat actors successfully develop and deploy proofs of concept (PoCs) or an actual malware that exploits the vulnerability while the vendor is still working on rolling out a patch (or sometimes, unaware of the vulnerability’s existence), it becomes a zero-day exploit or attack. While developers and vendors, as well as researchers and security experts, continuously invest time and effort to find and fix security flaws, the same can be said for threat actors, too. The result is an arms race between threat actors finding and trying to exploit a vulnerability and the vendors working to release a patch to fix it.
Why are zero-day vulnerabilities and exploits significant?
Zero-day exploits aren’t only highly valued in legitimate bug bounty programs — with one even fetching up to US$2 million — they are also valuable in underground marketplaces. For threat actors, zero-day exploits are a boon because most security defenses are designed to handle known flaws. Attacks based on unknown and unpatched vulnerabilities can thus go unnoticed for a long time.
The success of zero-day attack also depends on the organization’s “window of exposure,” or the time between the discovery of a vulnerability and the release (and installation) of a patch that fixes it. Even known vulnerabilities can have a lengthy window of exposure — whether due to the organization’s patch management policies or the level of difficulty in developing the patch. A longer window of exposure makes it more likely for an attack to remain undetected.
How are zero-day exploits used in an attack?
Threat actors use zero-day exploits in a number of ways:
- Spear phishing emails attached with files (e.g., Microsoft Office documents, Adobe PDFs, or other software executables or components) embedded with a zero-day exploit
- Phishing and spam emails socially engineered to lure unwitting recipients to click URLs and links to malicious or compromised websites hosting an exploit (watering hole attack)
- Exploit kits whose attack chains involve malvertisements and malicious sites that host zero-day exploits
- Compromising a system, server, or network — either through brute-force and dictionary attacks, misconfigurations, or inadvertent exposure to the internet — where attackers can then use exploit-laden malware
What is an example of a zero-day exploit or attack?
During the peak of their activities, exploit kits were known to integrate zero-day exploits for Internet Explorer and Adobe Flash. Perhaps the most notorious example is Stuxnet, a worm that exploited several zero-day vulnerabilities and was mainly designed to affect components of an industrial control system (ICS). A series of attacks also resulted from the trove of exploits that The Shadow Brokers hacking group leaked. The most infamous of these was EternalBlue, which was used by the WannaCry and Petya/NotPetya ransomware families.
Other recent examples are the PoCs and exploit codes that the independent researcher, going by the handle SandboxEscaper, publicly released. These PoCs and exploits demonstrated how a (then) zero-day vulnerability in Windows 10’s Task Scheduler (CVE-2019-1069) can be taken advantage of to gain access to normally protected files. And if chained with other security flaws, the hacker can escalate privileges to hijack the vulnerable system.
What risks do zero-day vulnerabilities pose?
A zero-day vulnerability poses significant security risks, with effects that mostly depend on the attack's intent. BlueKeep (CVE-2019-0708), a zero-day vulnerability in remote desktop services, made headlines in May due to its “wormability.” Successfully exploiting BlueKeep can enable malware to propagate, similar to the way WannaCry used the EternalBlue exploit. The risk BlueKeep posed was so significant that Microsoft even released patches for Windows 2003 and Windows XP, which were out-of-support and end-of-life operating systems.
What is the potential impact of zero-day vulnerabilities to organizations?
Beyond the exposure of an organization’s sensitive data and mission-critical systems, businesses will also contend with marred reputations, financial losses, and penalties imposed by data privacy and patch management regulations.
Cybercriminals and threat actors can capitalize on the gap between the discovery and patch of a vulnerability — a gap that, on average, reportedly takes an organization around 69 days to fix. In a 2018 survey by the Ponemon Institute, 76% of organizations whose endpoints were successfully compromised were due to attacks that used zero-day exploits. In today’s era of digital transformation, where newfangled technologies are constantly put together and integrated into existing (and sometimes, outdated) ones, vulnerabilities are inevitably introduced into systems that use them. In fact, zero-day attacks are predicted to increase from one per week to once per day in 2021.
How can users and businesses defend against zero-day attacks?
Given their nature, zero-day attacks are inherently unpredictable and difficult to prepare for and defend against. This is especially true for organizations whose security measures are developed around known and already-patched flaws. A proactive, defense-in-depth approach, however, can help mitigate them.
Here are some of the other countermeasures that organizations can adopt to defend against zero-day attacks:
- Regularly update the online infrastructures. While this may seem like a reactive strategy, applying patches to systems, servers, and networks as soon as they’re available lowers the number of flaws and the exploits that target them. Accordingly, organizations should also factor zero-days into their patch management policies as well as incident response and remediation strategies.
- Secure the email gateways, servers, and networks. Zero-day attacks can take the form of threats that may target different parts of an organization’s online infrastructure — either to facilitate the execution of malware, deliver payloads, or perform lateral movement — which is why it’s important to secure them equally.
- Enforce the principle of least privilege. Many threats abuse legitimate and open-source penetration testing and system administration tools to successfully exploit a vulnerability. Restricting and securing their use helps reduce the risks of attackers gaining access to the entire network or system.
- Nurture and practice cybersecurity hygiene. Fostering a culture of cybersecurity, which includes increasing user awareness on phishing attacks, helps just as much as the security solutions that are deployed by the organization.
- Employ multilayered security defenses. Additional layers of security reduce an organization’s attack surface. Firewalls and intrusion detection and prevention systems, for instance, help filter malicious traffic and network activities. Application control and behavior monitoring prevents dubious executables and malware-related routines from running, while sandboxes quarantine suspicious and malicious files.
How does virtual patching protect against zero-day exploits?
Virtual patching (also known as vulnerability shielding) is one of the mechanisms that can complement an organization’s existing security measures. It functions as a countermeasure against threats that exploit known and unknown vulnerabilities by implementing layers of security policies and rules that intercept an exploit from successfully taking paths to and from a vulnerability. This can buy organizations additional time, enabling their IT and system administrators to test official patches before they are applied.
Virtual patching also provides protection to IT infrastructures for which patches are no longer issued or are too expensive to update, such as legacy systems, end-of-support OSs, and internet-of-things (IoT) devices.
To learn more about zero-day vulnerabilities and exploits — what they are, how they work, and how to mitigate them — view our infographic, “Security 101: Zero-Day Vulnerabilities and Exploits.”
The Trend Micro™ Deep Security solution provides virtual patching that protects cloud workloads, servers, and containers from threats that exploit network-based vulnerabilities in critical applications, operating systems (Linux kernels, AIX, Solaris, and Windows including those in end-of-support status like Windows Server 2008 and Server 2003), and platforms like Docker and Kubernetes.
The Trend Micro Apex One™ security solution’s virtual patching delivers the timeliest vulnerability protection across a variety of endpoints, including point-of-sale (PoS), internet of things (IoT) devices, and systems with end-of-support (EoS) operating systems.
The Trend Micro™ TippingPoint® Threat Protection System provides virtual patching and extensive zero-day protection against network-exploitable vulnerabilities via Digital Vaccine® filters.
The Trend Micro™ Deep Discovery™ solution provides detection, in-depth analysis, and proactive response to attacks using exploits and other similar threats through specialized engines, customized sandboxing, and seamless correlation across the entire attack lifecycle, allowing it to detect threats even without any engine or pattern update.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation