2020 was a most unprecedented year given the circumstances under which it unfolded. The Covid-19 pandemic and the other significant events that occurred throughout the year had a lasting impact on the cybersecurity landscape, causing upheavals on many fronts. As we head deeper into 2021, let’s take a look back on some of the most notable security stories and trends from the past year, all of which are covered in our 2020 annual cybersecurity report.
Covid-19 plays prominent role in shaping cybersecurity landscape
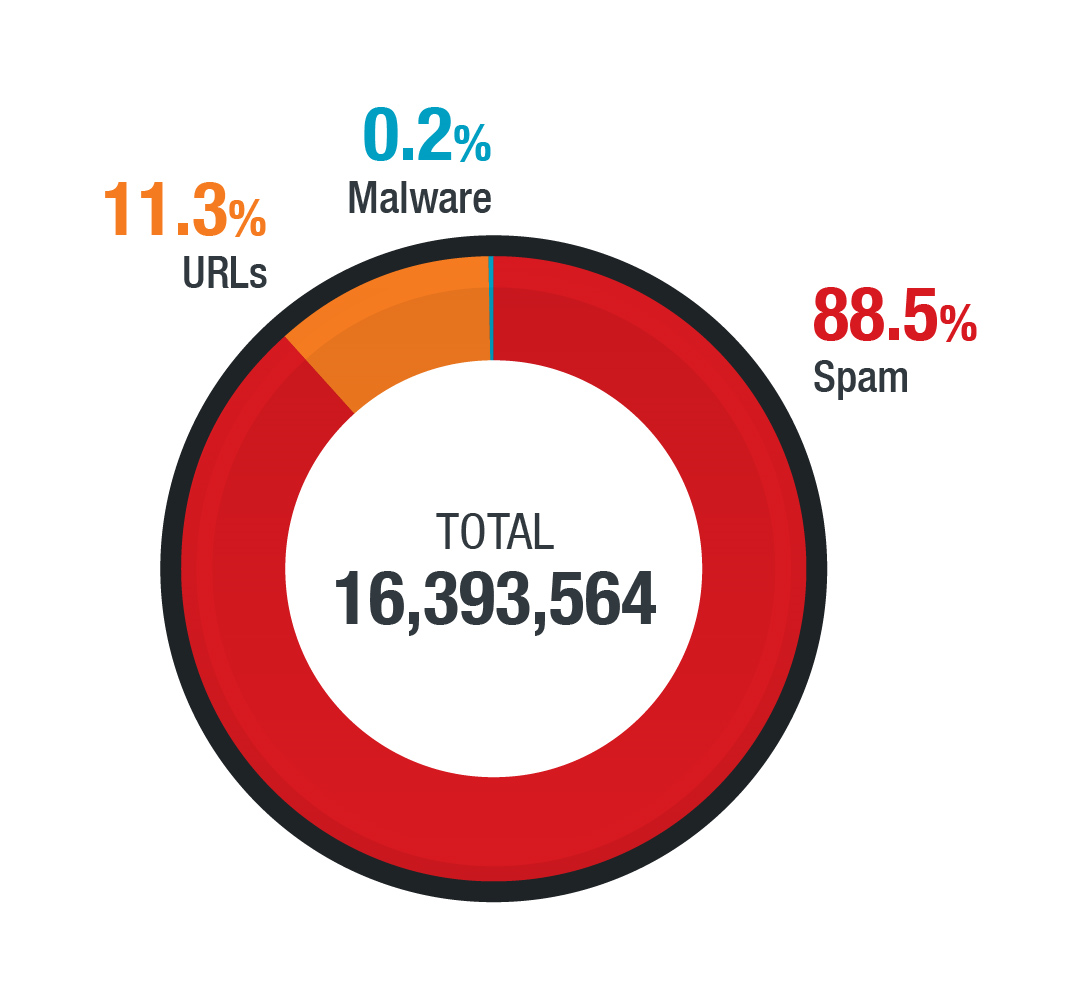
Malicious actors took advantage of the ongoing pandemic through a number of Covid-19-themed threats, including malicious URLs, spam, and malware. The bulk of these threats were spam, accounting for nearly 90% of the more than 16 million threats we detected.
The pandemic forced many organizations to shift to work-from-home arrangements for their employees, leading to significant changes in both operation and security policies and to the adoption of technologies needed for remote work. Virtual private networks (VPN), in particular, became indispensable tools for many organizations. But they were far from immune to attacks even as they were used to secure systems, as a single VPN vulnerability, CVE-2019-11510, accounted for nearly 800,000 detections in 2020 alone.
Ransomware continues to plague organizations
Ransomware operators continued going after high-value targets in a bid to wring larger ransom amounts from their victims. A recent trend that persisted in 2020 was the use of a two-pronged extortion scheme in which an attacker would threaten to publish stolen data on a leak site in addition to encrypting files on the victim’s systems.
Ryuk, one of the pioneers of this extortion method, saw a few quiet months in the middle of the year. But it came back strong toward the end of the year when it targeted organizations in the healthcare industry using a new variant with additional features, including a new dropper called BazarLoader.
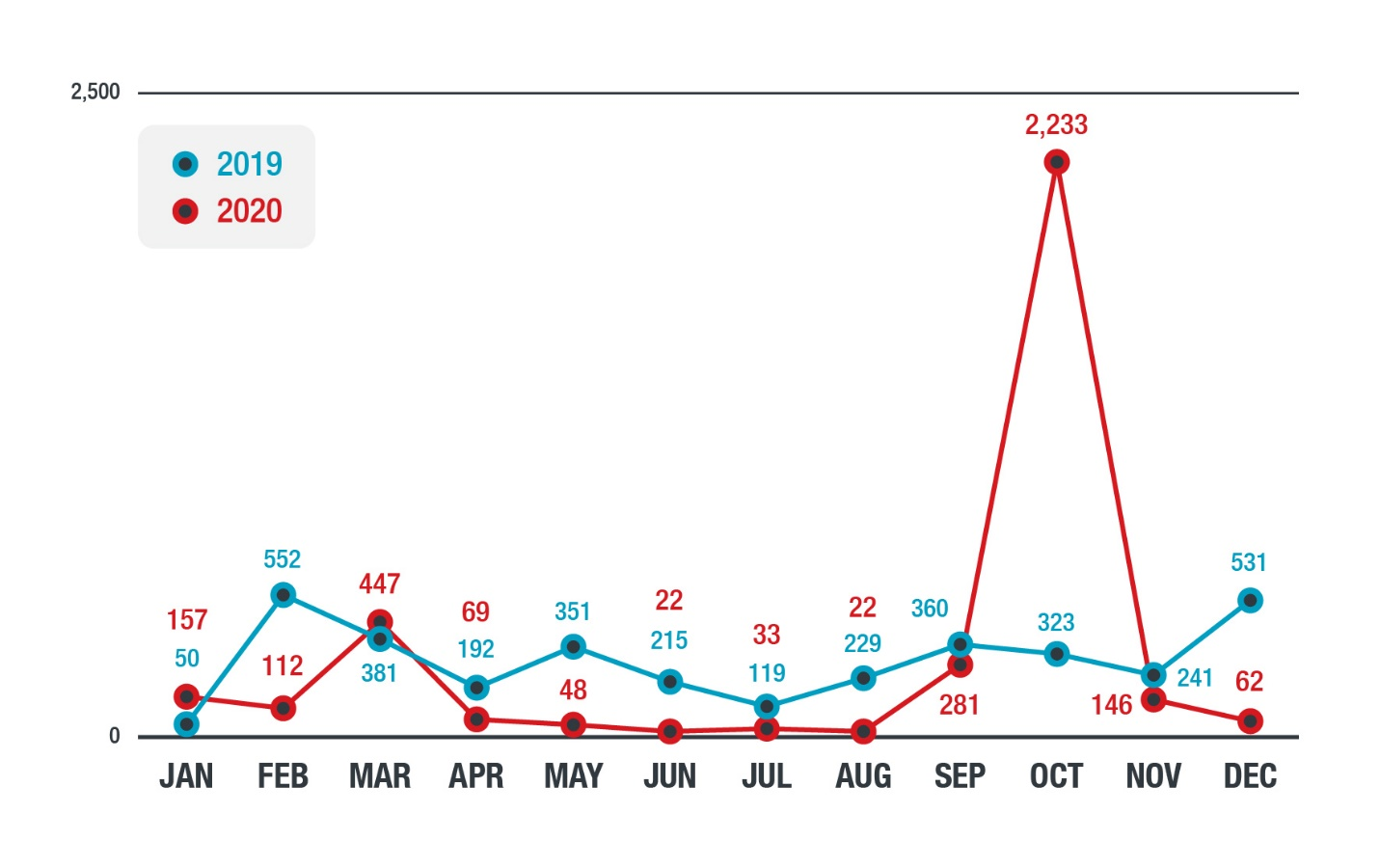
Another noteworthy ransomware family that used the double extortion technique was Egregor. It first appeared in September and was eventually deployed in a series of high-profile attacks on major retailers in December.
Critical industries, including those directly involved in pandemic response such as healthcare and manufacturing, were frequent targets of ransomware operators. An attack on an organization in these industries could have dire consequences. For example, a ransomware infection on a hospital could result in patient deaths, while a sabotaged vaccine manufacturing facility could lead to disruptions in an already strained global supply network.
Risks to cloud, IoT, and mobile environments come into focus
The importance of the cloud, the internet of things (IoT), and mobile devices to the pandemic-disrupted workplace threw the risks and security challenges involved in their use into stark relief.
Misconfiguration remained a major issue with cloud infrastructure. We observed a number of incidents that occurred because of misconfigured cloud implementations, often leading to cryptocurrency miner payloads.
Our data showed that, compared to the corresponding figures from 2019, inbound attack events more than tripled while outbound attack events nearly doubled in 2020. Routers were prime targets, as 15.5% of them were possibly victimized in inbound attacks while 5.1% were possibly compromised for outbound attacks.
We observed a decline in the number of malicious mobile apps from 2019 to 2020, from almost 60 million to just over 35 million. However, the number of malicious mobile device-related samples jumped by almost 70% — an indication that malicious actors might have been forgoing the use of malicious mobile apps in favor of other techniques such as phishing.
These and more are covered in our roundup, “A Constant State of Flux: Trend Micro 2020 Annual Cybersecurity Report,” which revisits the stories, trends, and numbers that defined the year from a cybersecurity perspective.

