While more enterprises have adjusted to the new normal, so have cybercriminals who take advantage of the ever-changing work, home, and security landscape. As described in our Midyear Roundup, the numbers pertaining to ransomware no longer tell the story at first glance. While the number of infections, company disclosures, and ransomware families has gone down, the estimated amount of money exchanged for the retrieval of encrypted data has steadily gone up. By going after institutions and companies with the urgent need to retrieve their data and get their systems running again, cybercriminals are able to demand exorbitant amounts of ransom.
Threat actors no longer target individual users and machines for random ransomware infections, hence the lack of updates and word-of-mouth information on their spread within the general public. Enterprises and agencies who fall victim try to stay mum on the matter until it is internally resolved. Meanwhile, the public is only made aware of these incidents when inquiries are made or when they are finally reported, not to mention the fact that these reported statements offer scant details (if any) with regard to how these organizations were victimized or if ransom was paid in the process. Unfortunately, paying cybercriminals to resolve these types of targeted attacks offers no guarantee that files can be retrieved or that there will be no subsequent attacks in the future.
Kinds of ransomware
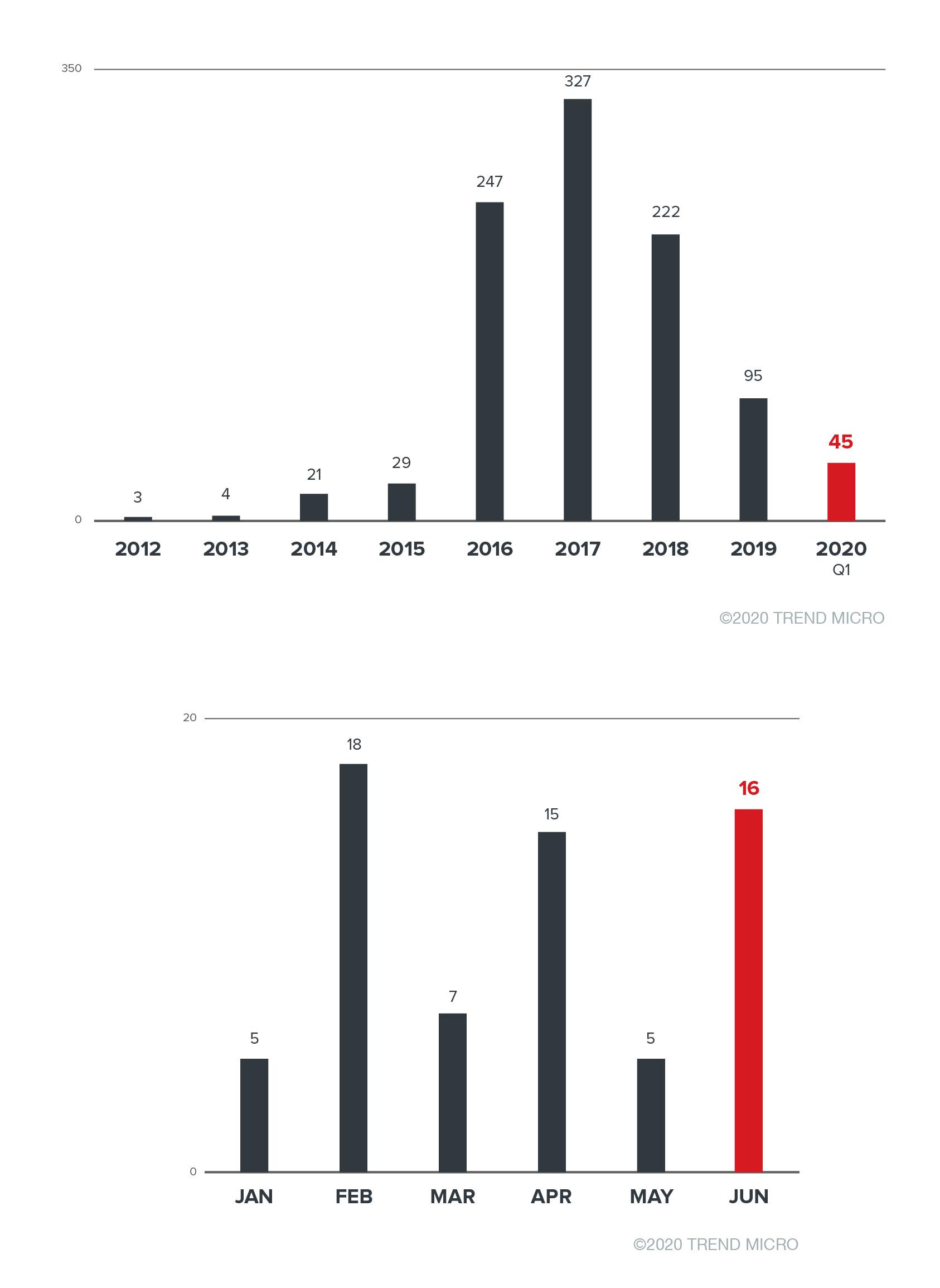
As mentioned, comparing the number of detections in previous years only reveals a small part of the story. Looking at the techniques and routines of ransomware previously and currently deployed makes it clear that cybercriminals have shifted their attention to specific targets and larger amounts of money that they can demand from their victims, who are often from industries or organizations involved in crucial public operations and infrastructures.
Although it has not become impossible for threat actors to randomly send spam emails to a directory of email addresses in order to lure at least one victim, recent deployments are currently more targeted and researched to yield the most profit. Here are three different kinds of ransomware that have been observed through the years and a general description of the routines that they employed for entry.
Worm-based or legacy ransomware
Worm-based ransomware spreads through systems much like how worms replicate copies of themselves, while legacy ransomware exploits the discontinued support for operating systems. These two exploit vulnerabilities for use as entry points and affect other systems in the network even without human interaction. Some of these threat vectors can be prevented by applying patches released by manufacturers or by downloading the virtual patches released by security vendors if the operating system is no longer supported.
However, ransomware routines that exploit zero-day vulnerabilities can inflict the most damage on systems. An example of this is WannaCry when it was deployed in 2017, months after the cybercriminal group Shadow Brokers published the existence of several hacking tools, among them EternalBlue. The ransomware spread quickly in enterprises worldwide, holding systems hostage and operations suspended until researchers found the kill switch included in the coding of the routine.
Opportunistic ransomware
These types of ransomware infect and spread via spam. Cybercriminals do not know the victims and simply send the infected emails to a roster of addresses that they might have collected, stolen, or bought. The cybercriminals employ social engineering techniques to deceive victims into opening the email or the malicious attachment, thus infecting their systems with ransomware.
In most opportunistic-type routines, the malware encrypts almost all kinds of files that a system might have, such as media files, documents, executables, and applications. These routines will likely also include a file or executable stating the amount of ransom and support instructions on how the victims can purchase cryptocurrencies to restore their files. Still, there is no guarantee that the decryption key will be sent to them or that their files will be restored after they pay the ransom.
| 2016 | 2017 | 2018 | 2019 | 2020 1H | |||||
|---|---|---|---|---|---|---|---|---|---|
| LOCKY | 82,805 | WCRY | 321,814 |
WCRY | 616,399 |
WCRY | 416,215 |
WCRY | 109,838 |
| KOVTER | 50,390 | CERBER | 40,493 |
GANDCRAB | 14,623 |
LOCKY | 7,917 | LOCKEY | 6,967 |
| NEMUCOD | 46,276 | LOCKY | 29,436 |
LOCKY | 10,346 |
CERBER | 5,556 | CERBER | 2,360 |
| CERBER | 40,788 | CRYSIS | 10,573 |
CERBER | 8,786 |
GANDCRAB | 4,050 | CRYSIS | 1,100 |
| CRYPTESLA | 26,172 | SPORA | 8,044 |
CRYSIS | 2,897 | RYUK | 3,544 | SODINOKIBI | 727 |
Table 1. Top five ransomware families from 2016 to the first half of 2020. Data taken from Smart Protection Network (SPN).
Since first appearing in 2016, cryptoransomware Locky and Cerber have consistently appeared in the top five detected and reported ransomware families. Locky was discovered infiltrating systems through a malicious macro in a Word document, which was delivered via email using social engineering techniques. It continues to be one of the most versatile ransomware families as newer iterations and routines have been employed for massive campaigns targeting users. A month after Locky, Cerber was reported as the first cryptoransomware variant with a voice capability that verbally prompted victims to pay to retrieve their files. In just a few months, newer variations of Cerber were discovered targeting cloud platforms, using exploit kits and malvertisements, targeting bitcoin wallets, and adding capabilities such as distributed denial-of-service (DDoS) and machine learning evasion. Given their record in the last few years (and despite changes in their targets), the rapid evolution of both ransomware families shows that the devious email techniques continue to succeed in luring unwitting victims. Furthermore, both ransomware families run a ransomware-as-a-service (RaaS) business model in the underground and appear to rake in profit for cybercriminals.
Fortunately, opportunistic ransomware is now of less concern to companies. Often, security systems available in the market today, as well as patches released, have mechanisms that allow detection using behavior and file monitoring technologies.
Targeted or breach-based ransomware
Targeted or breach-based ransomware involves the techniques in routines that have been observed in recent years. These kinds of ransomware use a breach to get into the system, such as stolen RDPs, unpatched vulnerabilities, and weak applications. From underground websites, cybercriminals can purchase credentials such as RDP usernames and passwords. They can also use social engineering techniques to phish for the credentials they need, or infect the targeted computers with data-stealing malware such as InfoStealer to find them the threat vectors that they can abuse.
Cybercriminals also use the said credentials to break into a company’s systems. Sometimes, this is combined with privilege escalation, tools, or methods that turn off the installed security. For better technological systems that might be in place such as behavioral/file detection installed by companies, Living Off the Land Binaries and Scripts (LOLBAS) is a way to evade detection in running ransomware.
Similar to opportunistic types of ransomware, the cybercriminals include instructions in the amount demanded for the retrieval of files. They might also suggest steps to the company on how they can purchase bitcoins to pay the ransom. Considering that these malicious actors know their targets, their demanded ransom is often higher than the ones demanded by other malicious actors using other ransomware types because the former actors are confident that these institutions need immediate remediation to retrieve their files and run their systems again. Cybercriminals can also set time limits in which it might be considered impossible for security teams to remediate the infection on their own before time is up. As a result, an institution would be forced to pay instead. In recent demands, some cybercriminals have also threatened their victims that the encrypted files will be published, or that the stolen information will be sold on underground sites if the ransom is not paid on time.
Compared to opportunistic types of ransomware, not all files in breach-based ransomware attacks are encrypted. Rather, cybercriminals choose specific types of files or applications that are integral to the everyday operations of institutions, such as system files and executables. It also bears repeating that despite payment, there is still no guarantee that files can be retrieved. There is also the danger that cybercriminals might have installed other kinds of malware that can remain undetected in the system and could be used by the said malicious actors for subsequent attacks.
Moreover, the targets in these types of ransomware are not always large enterprises or state and federal governments. Some industries and targets are modestly sized institutions such as hospitals that are viewed as being profitable targets because although their security systems and procedures might be less sophisticated, their resources could still be enough to pay the ransom.
In 2016, Crysis and Dharma struck by starting out as opportunistic-types of ransomware. However, both routines’ techniques quickly changed to exploit higher-paying potential victims through the use of other software and stolen RDPs. While not the first to use these techniques, Dharma showed how versatile ransomware can be as it adjusted its routines and used other legitimate software to redirect monitoring and attention. Meanwhile, Crysis targeted businesses and regained access even after the malware was removed, a feat that it managed by infecting other connected devices such as printers and routers for subsequent attacks. Offered as an RaaS in the underground, these kinds of ransomware could be easily available even to new hackers who might then be able to attack vulnerable companies and trick users to downloading the ransomware manually themselves.
Characteristics of new techniques and targets
These ransomware intrusion techniques for targeting victims are not new. Nonetheless, their combination with the damage from encrypting files and systems results in disrupted operations and the endangerment of the public’s sensitive information since data is potentially stolen. These enterprises and critical infrastructure institutions are considered high-value targets, which implies that instead of the spray-and-pray routine that prioritizes quantity and entails more effort, these malicious actors are now going after ideal targets for larger profits with less effort required. Additionally, with more stolen data available for exchange in the underground such as RDP credentials, risky online habits (like recycling usernames and passwords) can prove damaging not only to individual users, but also to a whole enterprise as well.
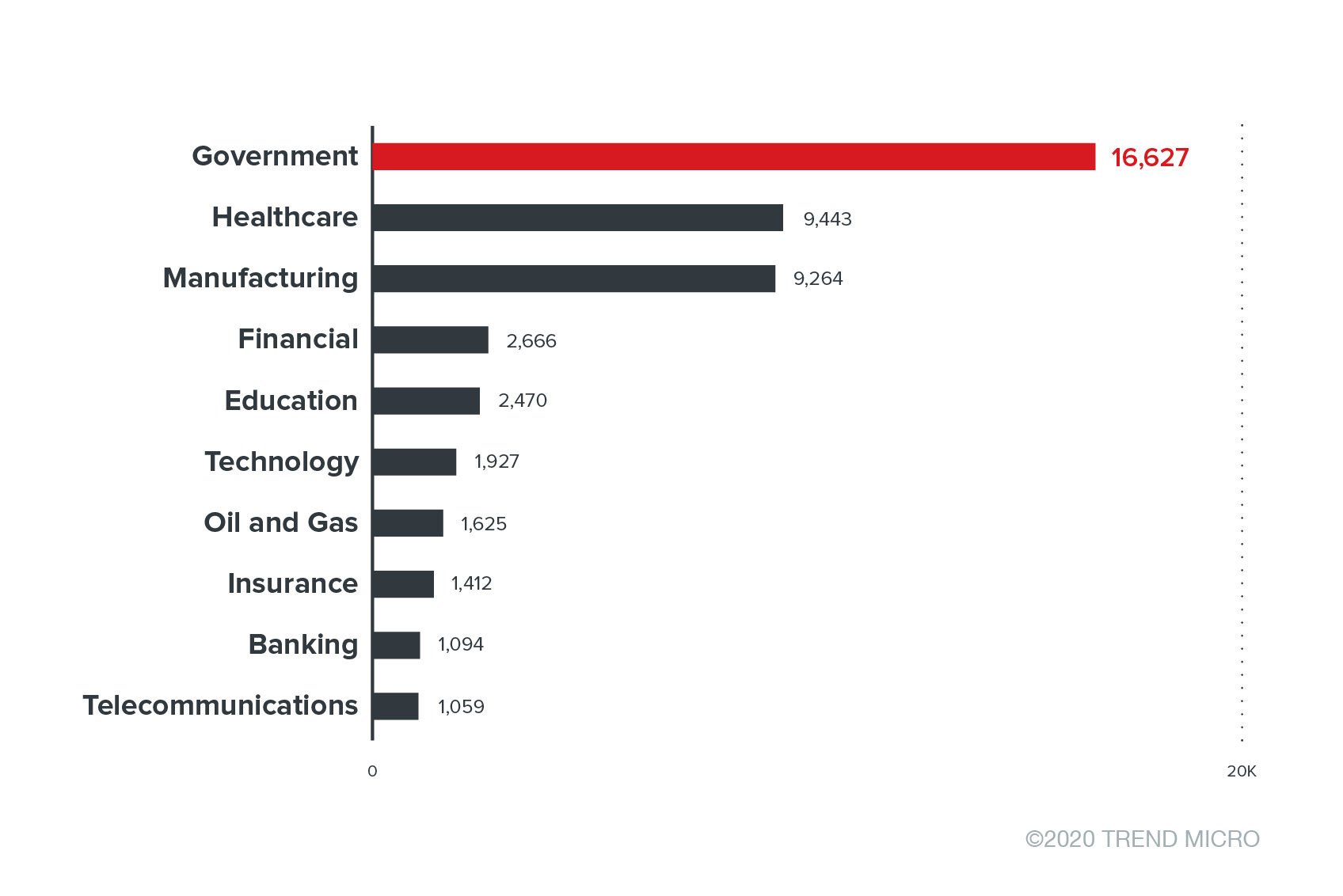
As an observation of the trend reveals, the ransomware routines themselves are now capable of evading detection with more sophisticated obfuscation techniques. By limiting the number and types of files targeted for encryption, these routines might bypass some security systems, especially those without file and behavior monitoring. As with the routines employed by ransomware Ryuk, infecting the network allows cybercriminals to move laterally and search for systems that yield the most potential: critical, safety, business, and mission systems such as those used in hospitals, government, transportation, and finance industries.
Upcoming ransomware trends
With the numerous evolutions that ransomware has undergone, it is to be expected that the routines employed by cybercriminals will only increase in complexity with respect to installation and obfuscation. That said, more companies and public agencies will become targets as system administrators and security teams juggle their different responsibilities like managing devices and servers remotely, implementing institutional updates, and accounting for an increasing number of work devices with intermingling personal usage, and vice versa.
Likewise, more government and large-scale enterprises will continue to be targeted for their assets and external-facing systems. From websites, apps, emails, files, and centralized control systems, to proprietary business and confidential security information, customers and employees alike could be at risk.
Considering the growing business of automation, the industrial internet of things (IIoT) and industrial control systems (ICS) could also be profitable targets for these cybercriminals. Production lines and supply chains serve as targets and threat vectors for various industries, and disruptions in these automated sectors could prove disastrous not only for the company, but also for a country’s economy and reputation.
Keeping in mind that these cybercriminals might be after higher payouts, however, there is also the possibility that internet of things (IoT) devices used by consumers for personal use could be less of a target for breach-based ransomware. Except for select individuals, personal devices could entail more effort in deployment but yield lower payouts and involve no high-value enterprise or public information. However, consumer IoT devices could still be affected by opportunistic and worm/legacy types of ransomware, considering that not all personal devices have installed security software.
Conclusion
Even with techniques and trends that are seemingly after big enterprises and public infrastructure, both small and medium-sized businesses (SMBs) and consumers will likely remain ransomware targets. In fact, it is unlikely that they would be regarded as any less in the near future. As the first half of the year’s telemetry data shows, consumers, SMBs, and households continue to be significant in ransomware deployments.
Here are some best practices for individuals, businesses, and institutions to protect themselves from these targeted ransomware threats:
- Practice good password hygiene. Do not recycle usernames and passwords for all online accounts and devices. Change the default credentials for all devices.
- Practice network segmentation, implement the principle of least privilege, and limit access to important data and system administration tools.
- Check your RDP server settings by monitoring and updating them regularly. Consider employing an RDP server brute-force protection system. Also, make sure that the number of users and accounts with RDP access is always up to date. Ensure that users with RDP access use complicated and strong passwords that are changed regularly.
- Monitor external-facing servers and ensure that patching schedules are kept. For instances of implementation difficulties, consider virtual patching solutions.
- Keep backup copies of important information. Practice the 3-2-1 method: Keep three backup copies in at least two different formats, with one kept separately and off-site.
- Avoid opening unverified and suspicious emails and embedded links. If the sender is unknown and the message and its attachments are unverified, delete the message and/or report the email to your security team immediately.
- Consistently patch and update systems, networks, software, devices, servers, and applications once manufacturers release patches or updates to prevent leaving vulnerabilities open for threat actors to exploit.
- Avoid paying ransomware demands. Paying the cybercriminals only encourages them to continue with their activities. There is also no guarantee that any data encrypted will be retrieved or not stolen, or that no other subsequent attacks will occur.
Trend Micro solutions
A multilayered approach can prevent ransomware from reaching networks and systems. Enterprises should secure their entire IT infrastructure against malware and mitigate risks or breaches, especially with regard to email and web gateways, endpoints, networks, servers, and the cloud. Meanwhile, SMBs can opt to protect their endpoints from business disruptions using Trend Micro™ Worry-Free™ Services Advanced. For home users, Trend Micro Internet Security provides powerful protection for up to 10 devices, while the Trend Micro Ransomware File Decryptor Tool can decrypt files locked by certain ransomware variants without targets having to pay the ransom or use a decryption key.
As ransomware threats continue to evolve and target critical systems and data, mitigating technologies and procedures will play a decisive role in keeping them at bay. For crucial everyday operations, security solutions should provide and enable control of operational integrity while efficiently reducing the chance of downtime and cost of maintaining resilience.

