
Car hacking is a reality the general public will have to deal with.
Nothing can be as intrusive and dangerous as strangers taking over your car while you are driving it. Last week, Valasek and Miller’s digital car-jacking stunt using 3G connectivity on a Jeep Cherokee’s infotainment system illustrated how life-threatening this situation can get. The discovery of the bug has since led to the recall of of 1.4 million vehicles. A similar hack—but off-road this time—was also demonstrated a few days after, but this time via digital audio broadcasting (DAB) radio signals.
Last week’s revelations are not the first time that car security has been in the spotlight, earlier in 2015, German security specialist Dieter Spaar discovered vulnerabilities in BMW ConnectedDrive. We have been monitoring and researching this security area as well (Automotive Security: Connected Cars Taking the Fast Lane).
High Visibility Can Mean High Risk
Currently, we are investigating the SmartGate System, first introduced by Škoda Auto in its Fabia III cars, which allows car owners to connect a smartphone to a car to read and display data such as how fast your car is going, how much fuel you are using on average, how many days till your next oil change or service and the like. Škoda Auto, more known as Škoda, is a Czech auto manufacturer that is a subsidiary of the Volkswagen Group.
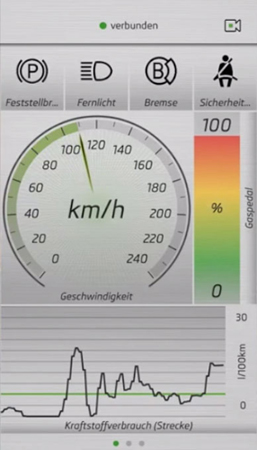
Figure 1. Škoda SmartGate sample telemetry screen
During our research with the default Wi-Fi configuration, we discovered that any attacker can read more than twenty parameters similar to the above and even lock out the owner of the car from the SmartGate system. All the attacker needs to do is to stay within the SmartGate’s in-car Wi-Fi range (which is by default pretty long/wide), identify the car’s Wi-Fi network, and then break the password, which is secured quite weakly. Interestingly, staying within the Wi-Fi range would not be so difficult, because the attacker can be lurking within up to fifty feet of the vehicle and still be within range. The Wi-Fi range could be even wider if the attacker is using a high-gain antennae. From there, the attacker can read all the car’s data. In our real-world test, we were able to break into the Wi-Fi even as we were driving behind the target car. Both cars were moving at approximately 30 to 40 kph. Meanwhile, reading the car data worked up to 120 kph, as for safety reasons we did not want to try higher speeds. We also found out that Wi-Fi Direct makes it incredibly easy for attackers to determine the PIN. SmartGate firmware shipped with recently built cars (or cars where a Škoda car owner or his dealer updated the SmartGate firmware) supports Wi-Fi Direct. You may say that this is more a privacy concern and less a severe security issue, i.e. we cannot stop the engine or blow up the gas tank or anything like that, however, unlike the possible attacks being discussed in the news which require the IP address of the car, which is quite hard to get, the Škoda SmartGate security issue has much less barriers to success: you only need the VIN (Vehicle Identification Number), which is often clearly printed on the car’s dashboard windshield. But, to make it clear, our attack is not just reading the VIN from the windshield. With the default Wi-Fi config we can connect to the SmartGate of a car even if we drive behind that given car, but for this attack to work we need that at least one smartphone is connected to the victim's SmartGate system. Sufficiently motivated attackers can stalk targets using the leeched information. An attacker can wait for you to turn on the ignition in your car, and once your Wi-Fi gets online, the attacker can learn your SmartGate device password, change your Wi-Fi settings, and basically lock you out of the system. An attacker can then wait for you in some location knowing you will need to go back to your car dealer to have your settings reset.
Škoda Car Owners and Maker Need to Act Now
Furthermore, we found out that more recent versions of SmartGate support Wi-Fi Direct, sometimes called Wi-Fi P2P, which can provide an unseen advantage for the attacker: the system does not need the owner’s smartphone to be connected and, as mentioned earlier, the Wi-Fi PIN is easy to crack. Right now, Trend Micro recommends all owners of Škoda cars that support SmartGate (in Germany it’s the Fabia, Octavia, Rapid, Yeti, and Superb, but it may vary in different countries) to do the following, where at least step 1 is highly recommended:
- Change the Wi-Fi transmission (Wi-Fi TX) power to 10% 5%
- Change the Wi-Fi password and change the Wi-Fi Direct PIN (if Wi-Fi Direct is supported)
- Change the Wi-Fi network name
Note: When setting the TX power to a lower setting, the attack still works, but the attacker needs to be (much) nearer to the car compared to the default Wi-Fi TX power of 50%. Changing only this setting reduces the likelihood of an attack to be successful from a farther distance. The advantage of doing just step 1 is that only the SmartGate settings needs to be changed, changes as described in step 2 and 3 require changes to the Wi-Fi settings of the smartphone(s)/tablet(s) being used. For improved security we recommend changing the default Wi-Fi password and the default Wi-Fi Direct PIN (if Wi-Fi Direct is supported). SmartGate is currently rolled out to other Škoda car models, so it is high time for Škoda to take action as well. These are good places to look into:
- Re-consider to set the Wi-Fi TX power to 10% 5% as default via a firmware update.
- Add a strong recommendation in the car's manual for owners to change the password and PIN.
- Design an “on/off” switch for SmartGate.
The SmartGate (Wi-Fi) is on when the ignition is on. But sometimes you just don’t need the SmartGate functionality. Admittedly, there is a workaround—you can unplug the cable of the SmartGate device which is located below the driver’s seat. However, that isn’t convenient for users, especially those who want to use the SmartGate function at times. There should be either a physical on/off switch or you can easily switch it on/off in the car settings menu of the on-board multimedia unit. Governments and other regulatory bodies have taken great strides in ensuring road safety throughout the years, where the impact of physical components on physical security are scrutinized. With the integration of smart devices into everyday lives, security conversations should include the impact of digital components as well. The Internet of Things may be a much-abused buzz word, but it is happening now and has clear and dangerous consequences if security is not built in.
Vendor Statement
We asked Skoda Auto a.s. for an official statement, but we have yet to receive one. According to an article in a Slovakia magazine, which quotes the PR manager of Skoda Auto a.s., future versions of the manual will include the recommendation to change the default Wi-Fi password. Furthermore, it seems the app(s) will refuse to work when the default password is used. We’re still trying to verify this statement from Skoda a.s., as the Google Translate version of this text reads a bit rough. We had been in contact first with Volkswagen AG (the parent company of Skoda a.s.) some time in mid-April and later with Skoda a.s., as the following vendor disclosure timeline shows:
- Mid-April: Reached out to Volkswagen multiple times
- May 29: Sent follow-up email to Volkswagen
- May 29: Received response from Volkswagen
- June 2nd: Received response from Skoda
- June 18th: Meeting with Skoda
All tests have been performed with a Škoda Fabia III car, SmartGate HW version 0004, SmartGate SW version 0884, and SW version 0928. As of this writing, SW version 0928 appears to be the latest version. More details and information about this security concern will be discussed at length in an upcoming entry. Updated on July 29, 2015, 6:36 A.M. PDT (UTC-7) to update the list of cars that support SmartGate. Updated on August 11, 2015, 1:36 A.M. PDT (UTC-7) to clarify the research details, the Wi-Fi setting recommendation, and to add a section regarding vendor interaction.
Legal disclaimer: The information provided in this statement is only of a general nature and only meant to serve as information. It is not intended to give any practical or legal advice and must not be interpreted as such. Without any specific practical or legal advice obtained from a third party, the contents of this document must not be relied on or interpreted as instructions for any action to be taken. Trend Micro reserves the right to change this information at any time and without any previous warning. Trend Micro does not assume any warranty or liability, in whichever form, for this document or its use, neither expressly nor tacitly.

