Phishing
Post Office Phishing Hits Credit Card Users in 26 Countries
Trend Micro has been tracking a wide-spread phishing campaign since last year. The campaign distributors attempt to steal people’s credit card number by sending phishing emails related to deliveries from national postal systems.
Phishing remains a popular and effective tactic that malicious actors continue to deploy against internet users. The current retail climate brought about by the global health crisis has only worsened the problem. Many countries across the globe have seen a surge in online shopping, and malicious actors are quick to deploy campaigns that take advantage of that trend. Trend Micro has noted a particular wave of phishing emails that has been targeting credit card users since late last year.
Trend Micro has been tracking this phishing campaign since last year. The campaign distributors attempt to steal people’s credit card number by sending phishing emails related to deliveries from national postal systems. The emails try to lead users to phishing websites that capture their credit information. This is a widespread attempt that affects at least 26 countries, including the United States, Switzerland, China, Japan, and Singapore. There have already been reports about this campaign in the Hong Kong press and the United States.
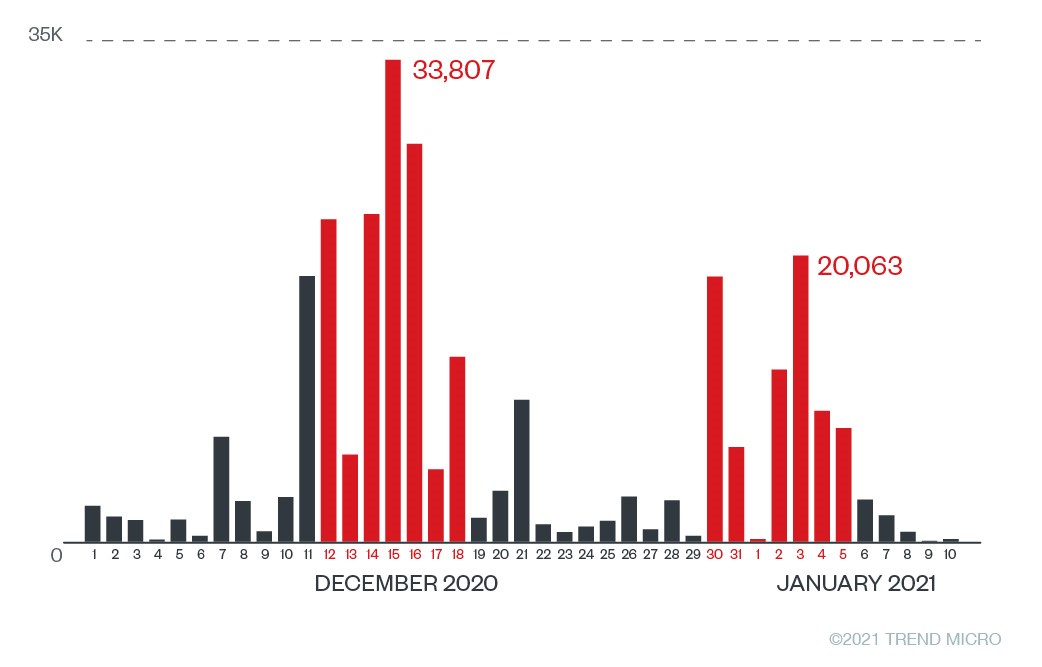
From December 1, 2020 to January 10, 2021, a total of 279,308 suspicious post office phishing URLs (an average of 6,812 URLs per day) were detected by Trend Micro email products. We also found that the number of URLs increased in two periods: first from December 12 to 18 and then from December 30 to January 5. Given this data, we reasonably expect that these post office phishing attacks will continue in the future.
Although the targets are from multiple countries, the phishing pages and email subjects are similar. These phishing sites in particular have comparable wording and HTML structure. There is a high probability that these phishing sites were actually generated by a toolkit. Toolkits are designed to help an actor to quickly create multiple phishing sites, as well as other elements that make an effective campaign. These types of kits are readily available and sold in underground forums. They allow malicious actors who do not have coding or malware expertise to easily craft and deploy phishing campaigns.
We can classify the malicious parts of the campaign into two elements: phishing emails and phishing websites.
Phishing Emails
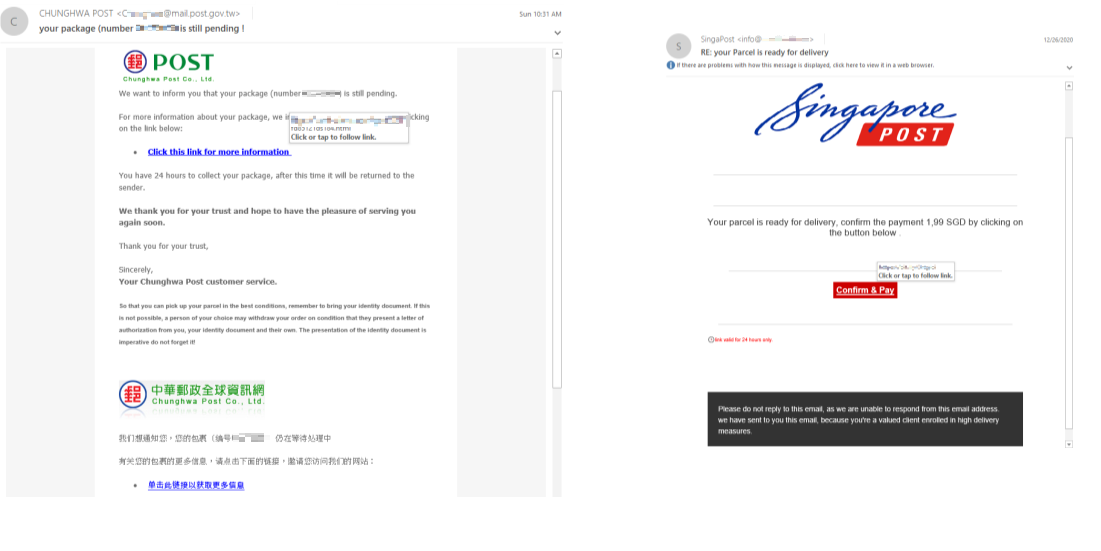
The content of the phishing email creates a sense of urgency, prompting users to take immediate action. It broadly states “There is an issue with your package,” pushing receivers to select the button and open the phishing page.
Figure 2 shows some samples of these phishing emails.
Most of the email titles contain the keyword “your package.” Here are some sample headlines that show how the malicious actors use urgent-sounding phrases to compel users to open the emails:
- Your package could not be delivered on 05.01.2021
- 您的包裹無法在06.01.2021上交付 | Fwd: Your package cannot be delivered on
- RE: [ Important ] Your package xxxxx is waiting for delivery
- Shipping notification : Your package XXXXXXXXXX is ready for delivery
- Your package could not be delivered on 05/01/2021 because no customs duties were paid (MYR 31.66). Follow the instructions
- We tried to deliver your package today
- Last Reminder : Your package could not be delivered on 10.12.2020
- JapanРоstから、発送XXXXXXXXXXがまだご指示をお待ちしております
Below is a list of countries with their postal services that malicious actors impersonate for their campaign:
| Australia: Australia Post | Netherlands: PostNL |
| Brazil: Correios Post | New Zealand: New Zealand Post (NZ Post) |
| Canada: Canada Post | Philippines: PHL Post |
| Chile: Correos de Chile (aka CorreosChile) | Portugal: Correios de Portugal (Portugal CTT) |
| Finland: Posti | Singapore: Singapore Post |
| France: Chrono Post | Slovakia: Slovakia Post |
| Germany: Deutsche Post | Sweden: Post Nord |
| Hong Kong: Hong Kong Post | Switzerland: Swiss Post |
| Ireland: An Post | Taiwan: Chunghwa Post |
| Israel: Israel Post | Turkey: Posta ve Telgraf Teşkilatı (PTT) |
| Japan: Japan Post | UK: Post Office |
| Korea: Korea Post | United Arab Emirates: Emirates Post |
| Malaysia: Malaysia Post | US: United States Postal Service (USPS) |
Table 1. List of affected countries and their related postal services
Phishing Websites
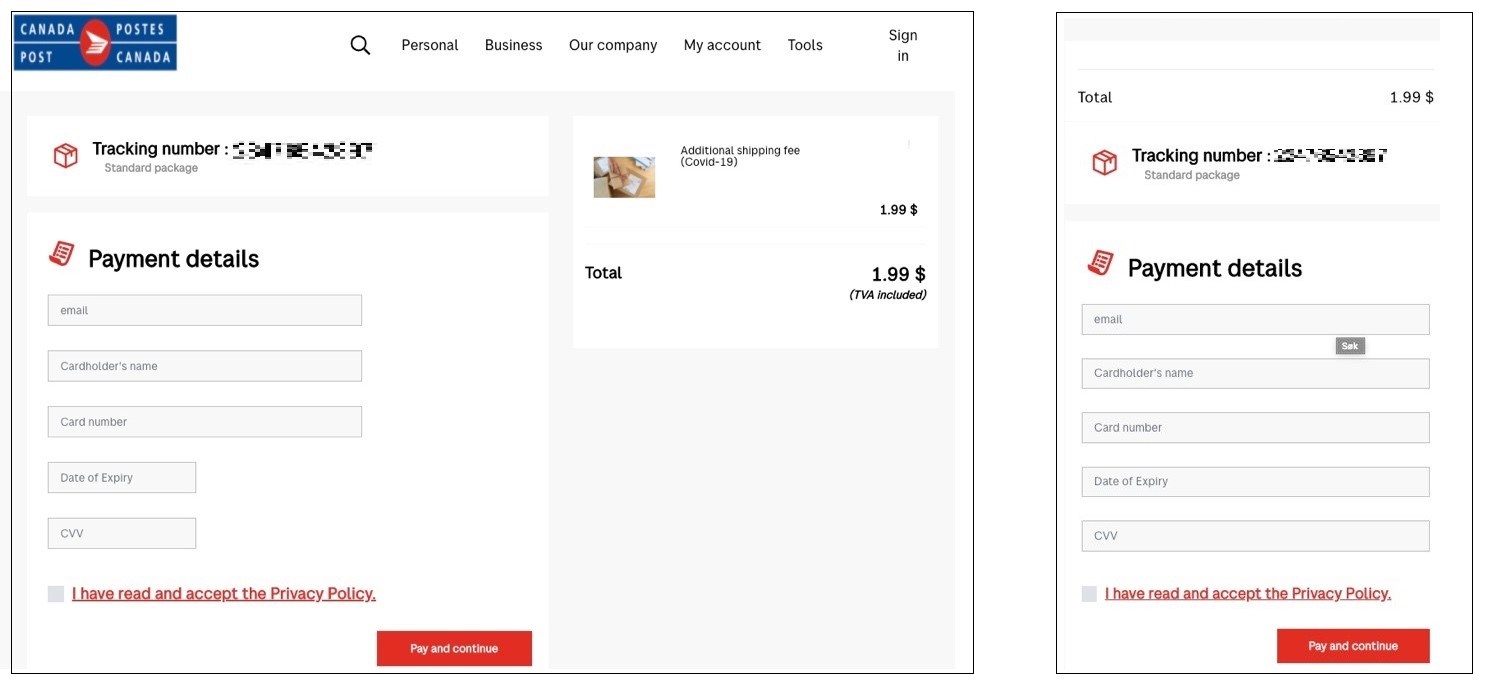
Most of the phishing pages operate the same way. The following Canada Post case illustrates the strategy.
When a user clicks on the link in the phishing email, they are led to a phishing page that requests their credit card information for payment. The display layout depends on the postal service that the malicious actors are impersonating.
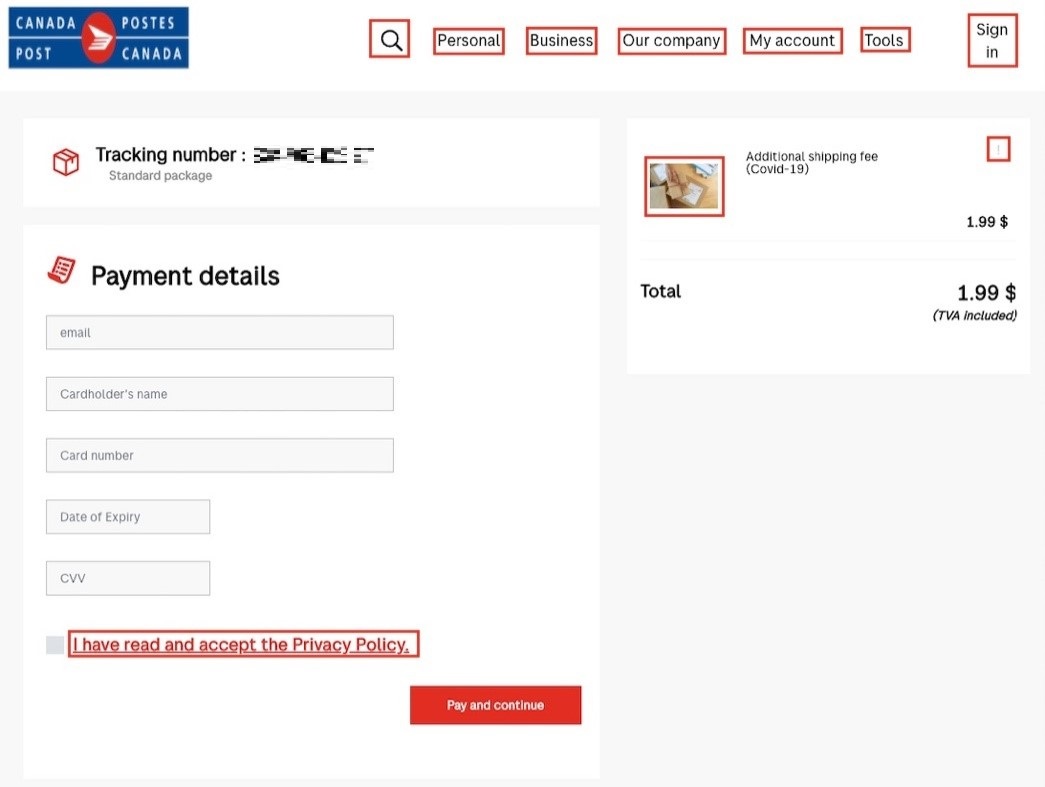
Although all links can be selected, no actions will be triggered. The only button that leads to an action is “Pay and continue.” The inactive links are marked in red in the following image:
The phishing page accepts any and all data that a user inputs. If incorrect information or information in the wrong format is entered in the empty text fields, a user can still continue to the next page.
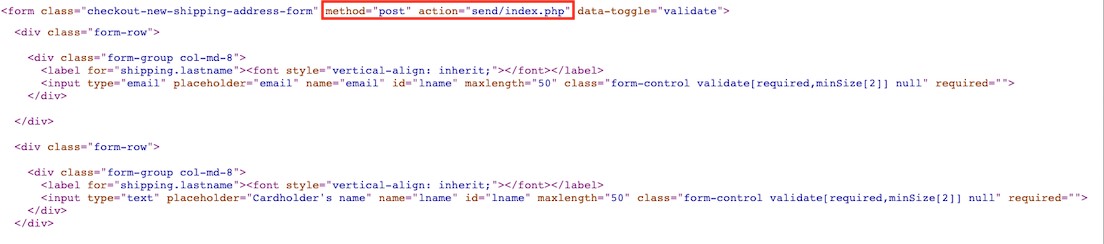
When a user selects the “Pay and continue” button, the information is sent to “send/index.php” using the post method:
After sending the information, users are led to a fake loading page. From there, users are automatically redirected to the next page after 25 seconds of “loading.”
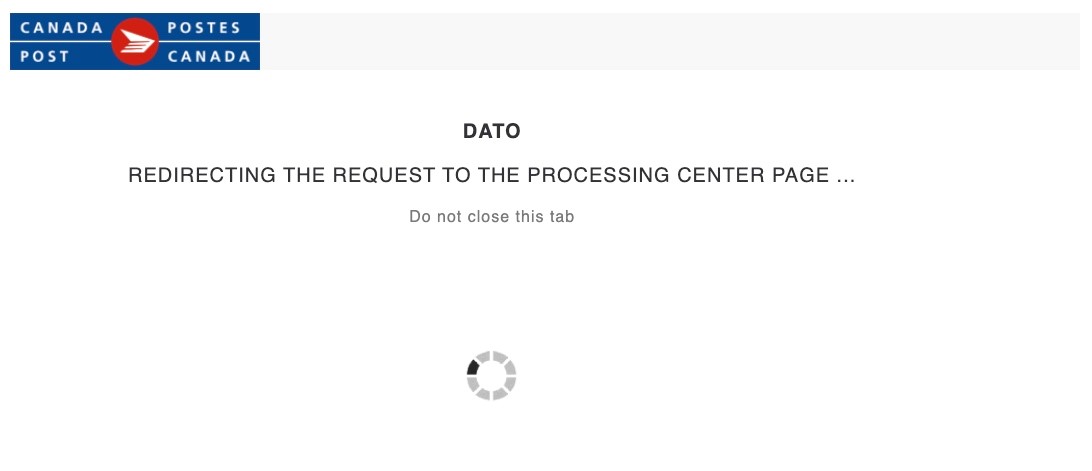
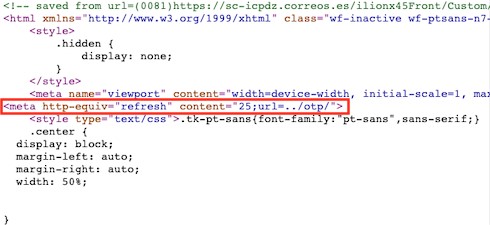
The following is the code to redirect to “/otp/” after 25 seconds:
After the loading page, users will see a fake confirmation page. The “date” and “card number” are fixed texts and as such, never change. The “back” and “new code” buttons have no function.
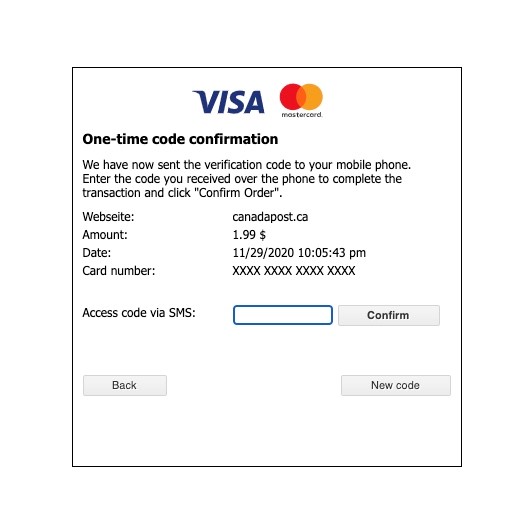
After users select the “Confirm” button, the page will redirect to “/send/sms1.php”, but connecting to this page reveals a “Page Not Found” message.
Avoiding Phishing Scams and Malicious Emails
Due to the health crisis in 2020, the retail landscape has drastically changed. Many people around the world are now relying more heavily on postal services and deliveries for ordinary shopping and essential goods, just as many are using email and online payment services more regularly. It is therefore safe to assume that cybercriminals are actively trying to take advantage of this trend and creating tailored scams to trick more users out of their credit card information. As we noted in our security roundup last year, email is a particularly popular avenue for attack.
Here are a few best practices for avoiding email phishing scams:
- Check the email content properly. Inspect all pieces of information to see if email addresses, message texts, or links are inconsistent.
- If you select a link from an email, inspect the website. Keep in mind that just because the homepage does not seem to display non-malicious content does not mean that the website is not malicious. Template texts within the website are usually tell-tale signs.
- If you happen to find potentially malicious phishing or scam emails on your work computer, alert your security and IT services immediately. They are equipped to inspect further.
For organizations, following security best practices will help minimize the success of similar phishing campaigns. Stopping threats from their initial entry prevents losses. Here are some general security practices to implement:
- Secure email gateways. Secured email gateways thwart threats that are delivered via spam and phishing. They also help users to avoid opening suspicious emails and attachments.
- Regularly back up files. The best way to do this is follow the 3-2-1 rule: Create at least three copies of the data, use two different storage formats, and have at least one copy located off-site.
A multilayered security approach is recommended to protect all possible threat entry points. Solutions such as Trend Micro™ Email Security, which uses enhanced machine learning and dynamic sandbox analysis, can stop email threats.
A full list of the Indicators of Compromise can be found here.

