What Are the Different Types of Phishing?
Types of phishing attacks range from classic email phishing schemes to more inventive approaches such as spear phishing and smishing. All have the same purpose – to steal your personal details.
What are the different types of phishing attacks?
Phishing attacks are social engineering attacks, and they can have a great range of targets depending on the attacker. They could be generic scam emails looking for anyone with a PayPal account.
Phishing can also be a targeted attack focused on a specific individual. The attacker often tailors an email to speak directly to you, and includes information only an acquaintance would know. An attacker usually gets this information after gaining access to your personal data. If the email is this type, it is very difficult for even the most cautious of recipients not to become a victim. PhishMe Research determined that ransomware accounts for over 97% of all phishing emails.
What is spear phishing?
Fishing with a pole may land you a number of items below the waterline – a flounder, bottom feeder, or piece of trash. Fishing with a spear allows you to target a specific fish. Hence the name.
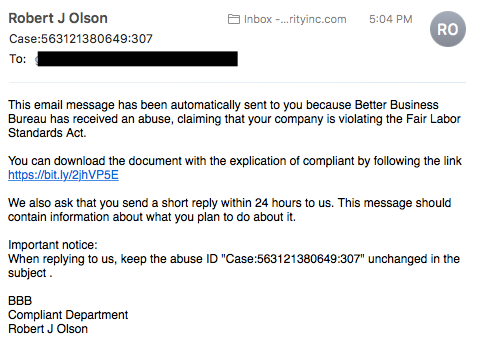
Spear phishing targets a specific group or type of individual such as a company’s system administrator. Below is an example of a spear phishing email. Note the attention paid to the industry in which the recipient works, the download link the victim is asked to click, and the immediate response the request requires.
What is whaling?
Whaling is an even more targeted type of phishing that goes after the whales – a marine animal even bigger than a fish. These attacks typically target a CEO, CFO, or any CXX within an industry or a specific business. A whaling email might state that the company is facing legal consequences and that you need to click on the link to get more information.
The link takes you to a page where you are asked to enter critical data about the company such as tax ID and bank account numbers.
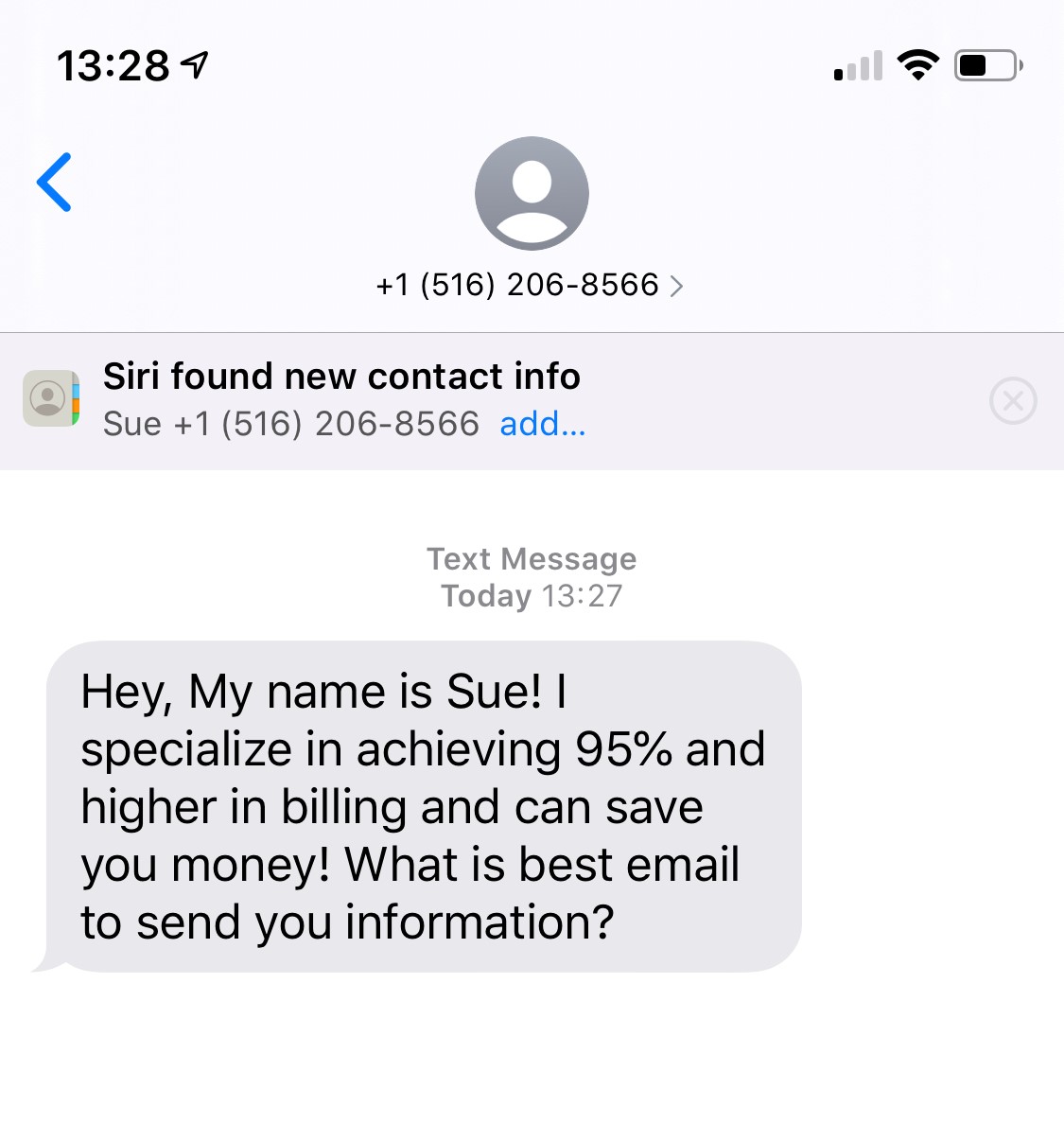
What is smishing?
Smishing is an attack that uses text messaging or short message service (SMS) to execute the attack. A common smishing technique is to deliver a message to a cell phone through SMS that contains a clickable link or a return phone number.
A common example of a smishing attack is an SMS message that looks like it came from your banking institution. It tells you your account has been compromised and that you need to respond immediately. The attacker asks you to verify your bank account number, SSN, etc. Once the attacker receives the information, the attacker has control of your bank account.
What is vishing?
Vishing has the same purpose as other types of phishing attacks. The attackers are still after your sensitive personal or corporate information. This attack is accomplished through a voice call. Hence the “v” rather than the “ph” in the name.
A common vishing attack includes a call from someone claiming to be a representative from Microsoft. This person informs you that they’ve detected a virus on your computer. You’re then asked to provide credit card details so the attacker can install an updated version of anti-virus software on your computer. The attacker now has your credit card information and you have likely installed malware on your computer.
The malware could contain anything from a banking Trojan to a bot (short for robot). The banking Trojan watches your online activity to steal more details from you – often your bank account information, including your password.
A bot is software designed to perform whatever tasks the hacker wants it to. It is controlled by command and control (C&C) to mine for bitcoins, send spam, or launch an attack as part of a distributed denial of service (DDoS) attack.
What is email phishing?
Email phishing is the most common type of phishing, and it has been in use since the 1990s. Hackers send these emails to any email addresses they can obtain. The email usually informs you that there has been a compromise to your account and that you need to respond immediately by clicking on a provided link. These attacks are usually easy to spot as language in the email often contains spelling and/or grammatical errors.
Some emails are difficult to recognize as phishing attacks, especially when the language and grammar are more carefully crafted. Checking the email source and the link you’re being directed to for suspicious language can give you clues as to whether the source is legitimate.
Another phishing scam, referred to as sextortion, occurs when a hacker sends you an email that appears to have come from you. The hacker claims to have access to your email account and your computer. They claim to have your password and a recorded video of you.
The hackers claim that you have been watching adult videos from your computer while the camera was on and recording. The demand is that you pay them, usually in Bitcoin, or they will release the video to family and/or colleagues.
What is search engine phishing?
Search engine phishing, also known as SEO poisoning or SEO Trojans, is where hackers work to become the top hit on a search using a search engine. Clicking on their link displayed within the search engine directs you to the hacker’s website. From there, threat actors can steal your information when you interact with the site and/or enter sensitive data. Hacker sites can pose as any type of website, but the prime candidates are banks, money transfer, social media, and shopping sites.