Cyber Threats
Hacking LED Wristbands: A Recap of RF Security Basics
We’re always eager for new research and learning opportunities, but this time, serendipitously, the opportunity found us--in the form of RF wristbands. In this we delve into the security risks of these unassuming devices.
Early this year, we published a security analysis of industrial radio remote controllers. In that research, we examined different vulnerabilities in the implementation of radio frequency (RF) communication and the possible impact of an attack on these weaknesses. We believe that RF security research is of great importance especially in light of the realization that a growing number of internet of things (IoT) and industrial internet of things (IIoT) ecosystems are and will be based on RF communication. For this reason, aside from our research activity, we take the time to share in depth our learning experiences with the research community. For example, Trend Micro Research is in its fifth edition of the Capture the Signal (CTS) contest, a challenge-based game that focuses exclusively on the reverse engineering of radio signals, where researchers, white-hat hackers, and practitioners can learn about RF security while playing.
We’re always eager for new research and learning opportunities, but this time, serendipitously, the opportunity found us. At the closing party of the Hack In The Box Amsterdam conference — where we presented our industrial radio research and ran a CTS contest — we were given LED wristbands to wear. They’re flashing wristbands meant to enhance the experience of an event, party, or show. At the beginning, we were not interested in the security impact; we just wanted to learn. Later on, however, we discovered that the RF link was used to transport an industrial protocol: DMX512 (Digital MultipleX 512), the same protocol used to pilot large light exhibitions.
So, despite being small and inexpensive, devices such as LED wristbands offer a good learning opportunity, and the indirect impact of an attack against their underlying technology can be substantial. For example, in the case of an important show organized by a well-known company, attended by thousands of people and broadcast to be seen by many others, a failure in the lighting system can affect the brand reputation.
In this blog post, we provide a high-level and simplified overview of our analysis. We discuss in detail how we performed — and how technical readers can reproduce — each step in our technical brief, “Hacking LED Wristbands as a Learning Opportunity to Jump on RF Security.”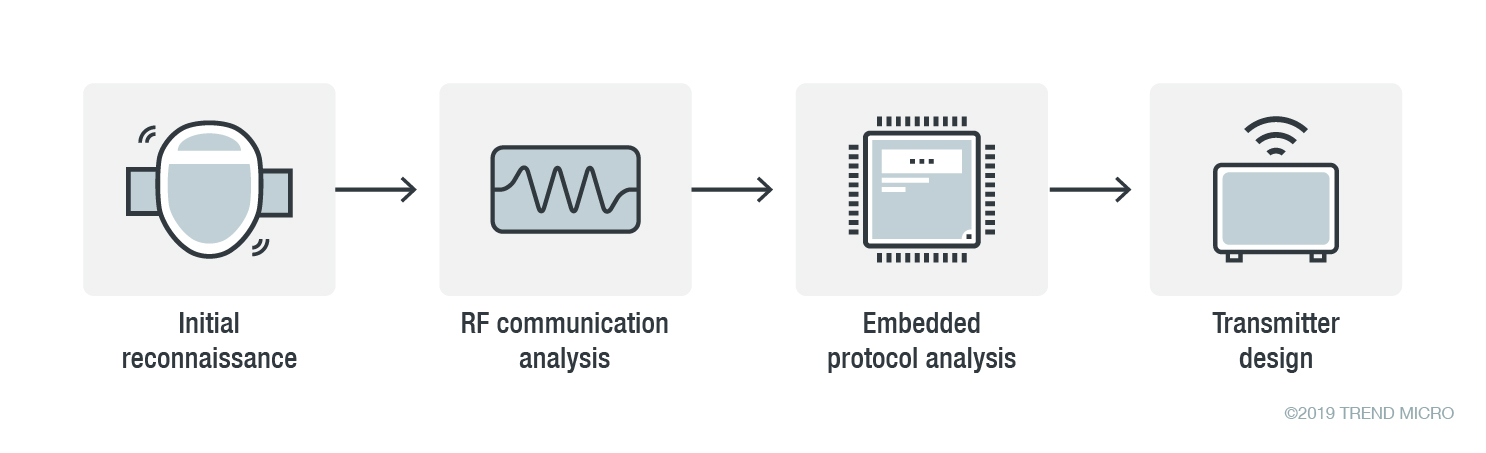
Figure 1. Summary of the analysis process
The LED wristband
While attending the party, we came up with the idea of doing an RF security analysis of the wristbands on the spot. Initially done just for fun, our impromptu research soon made us realize that these little devices made for a good and within-reach target, perfect for learning and sharing. Having noticed how the wristbands would light up and flash in sync with the music playing, we wondered what kind of RF components could be behind the wristbands.
While standing near the DJ stage, we found what looked like a transmitter. A quick web search of the brand name (Drome) revealed that, despite being based in the Netherlands, the vendor has customers around the world who use its products. Considering the wide range of similar products marketed by other vendors, it’s safe to say that devices such as LED wristbands have significant adoption.
Opening one of the wristbands at the event, we found out that it is based on a CC113L receiver, which is the receiver-only version of the well-known CC1101 transceiver made by Texas Instruments.
Capturing signals
Having confirmed that we were indeed dealing with an RF-based device, we proceeded with the analysis. We had out our software-defined radio (SDR) equipment in our backpack, a BladeRF SDR, and we used it to make as many RF captures as possible. Multiple captures allowed us to compare different packets and reveal the overall packet structure. Packets in this context determine the light’s colors and flash speeds or the displayed “effects.”
With the help of the DJ, who got intrigued by seeing us focused on our work, we were able to capture different packets corresponding to different effects or commands. Although not surprising, we confirmed that there was no anti-replay mechanism, so we were able to interfere with the expected “color” commanded by the DJ during the party.
RF analysis
After capturing the signals, we started a more in-depth analysis. Since the signals we captured were imperfect, we had to do some filtering and custom error correction in post-processing. Fortunately, Universal Radio Hacker (URH) has built-in configurable filters, noise reduction features, and scriptable packet processors, which come in handy in such cases.
Since we were dealing with a digital radio, we needed to demodulate the captured signal to “see” the bits. From this, we were able to find the preamble, which is necessary in any digital packet radio communication to “wake up” the receiver and provide a reference to set the symbol rate. After this step, our bitstream started to look cleaner.
We then created a custom post-processor to fix the demodulation error in the first two bits of the preamble. With the preamble fixed, we proceeded with diffing — comparing packets to determine how they differ — to reverse-engineer the packet structure.
Embedded protocol analysis
Although we had obtained the packet structure, we still needed to know the exact radio parameters. To ascertain these, we dug deeper into the radio configuration.
Typical of embedded packet radios, the radio chip and the microcontroller unit (MCU) are connected via the serial peripheral interface (SPI). Intercepting the SPI communication can allow anyone to determine the modem parameters (e.g., frequency, modulation, frequency deviation, and bandwidth).
We used Sigrok, an open-source signal analysis software, to interpret the signals captured with a logic analyzer and decode the SPI transactions. Back when we looked at the CC1120 transceiver, there was no decoder available, so we had to write our own. This time, we were lucky because Sigrok recently included support for the CC1101 chip, which is of the same family as the CC113L. With this, we obtained an almost perfect reconstruction of the register values. Using SmartRF Studio, a configuration tool developed by Texas Instruments (the very manufacturer of the analyzed radio chips), we derived the RF parameters from the register values.
By the end, we had successfully reconstructed 99% of the packet structure and had the right parameters to reconstruct a transmitter. We could now forge packets and control the wristbands in whatever way we want. But we leave this as an exercise to readers who are looking for an opportunity to test RFQuack, our open-source RF analysis framework, which can be used to analyze virtually any radio protocol, without the need for building custom software receivers.
Conclusion and security considerations
This experience is a useful exercise that allowed us to review and add to our knowledge of RF technology and share it with the community. From a security perspective, this case is worth looking into, as it demonstrates the ubiquity of RF technology and consequently the attack opportunities. While devices like LED wristbands may seem innocuous, looking at the big picture (e.g., application variety, vendor reach, brand reputation damage) makes it clear that there is more to these devices than meets the eye.
Our technical brief, “Hacking LED Wristbands as a Learning Opportunity to Jump on RF Security,” details our analysis and describes how we performed — and how interested readers themselves can reproduce — each step outlined here.

