Cyber Threats
Mirai-like Scanning Detected in China, Targets Brazil
Our network monitoring system recently detected an enormous amount of Mirai-like scanning activity from China. Brazil appeared to be the target location of the scanning of networked devices, including routers and IP cameras.
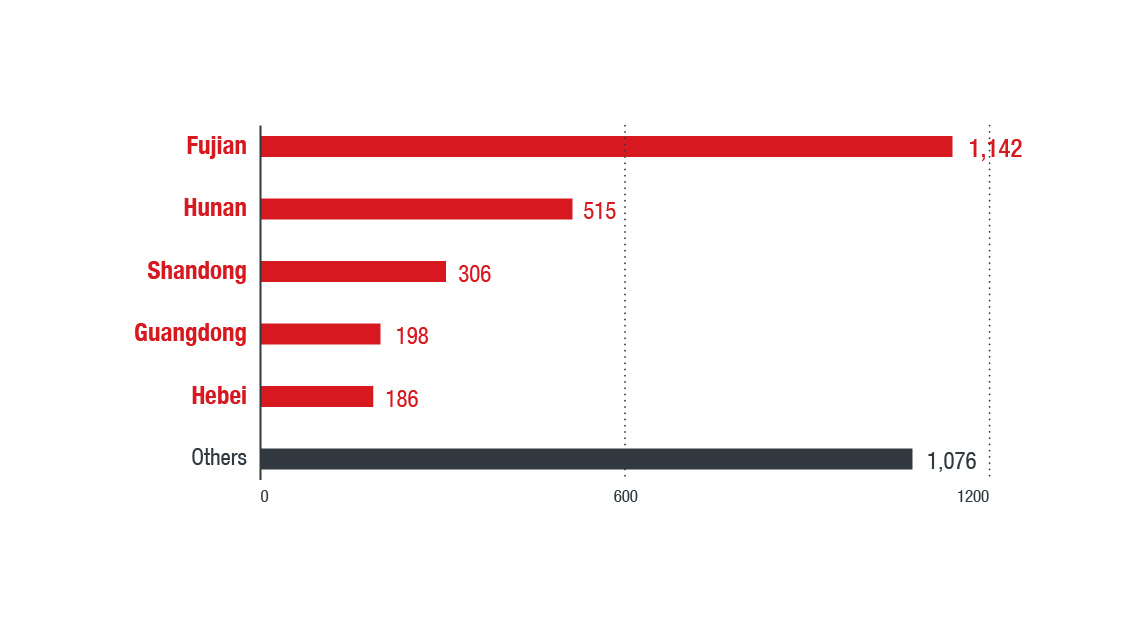
Our network monitoring system recently detected an enormous amount of Mirai-like scanning activity from China. From 1:00 p.m. UTC on March 31 to 12:00 a.m. UTC on April 3, our team detected an influx of activity coming from 3,423 IP addresses of scanners. Brazil appeared to be the target location of the scanning of networked devices, including routers and IP cameras.
Figure 1. Mirai-like scanning activity from China
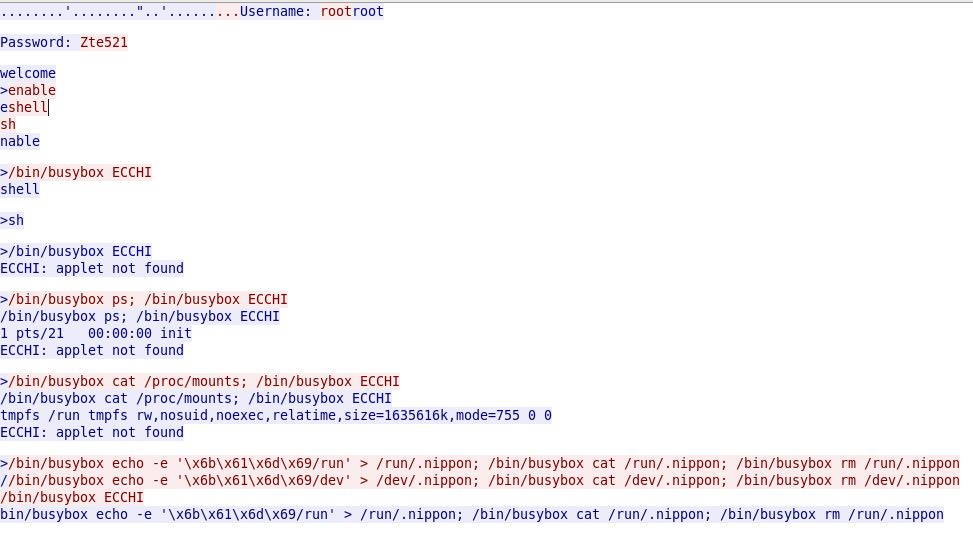
This attack behavior is similar to that of the Mirai botnet. Its infection chain involves continuously searching the internet for potentially vulnerable devices and then using default credentials to hijack them. But this time, some new usernames and passwords were employed.
Figure 2. Scan behavior
China-made routers and some new default credentials used
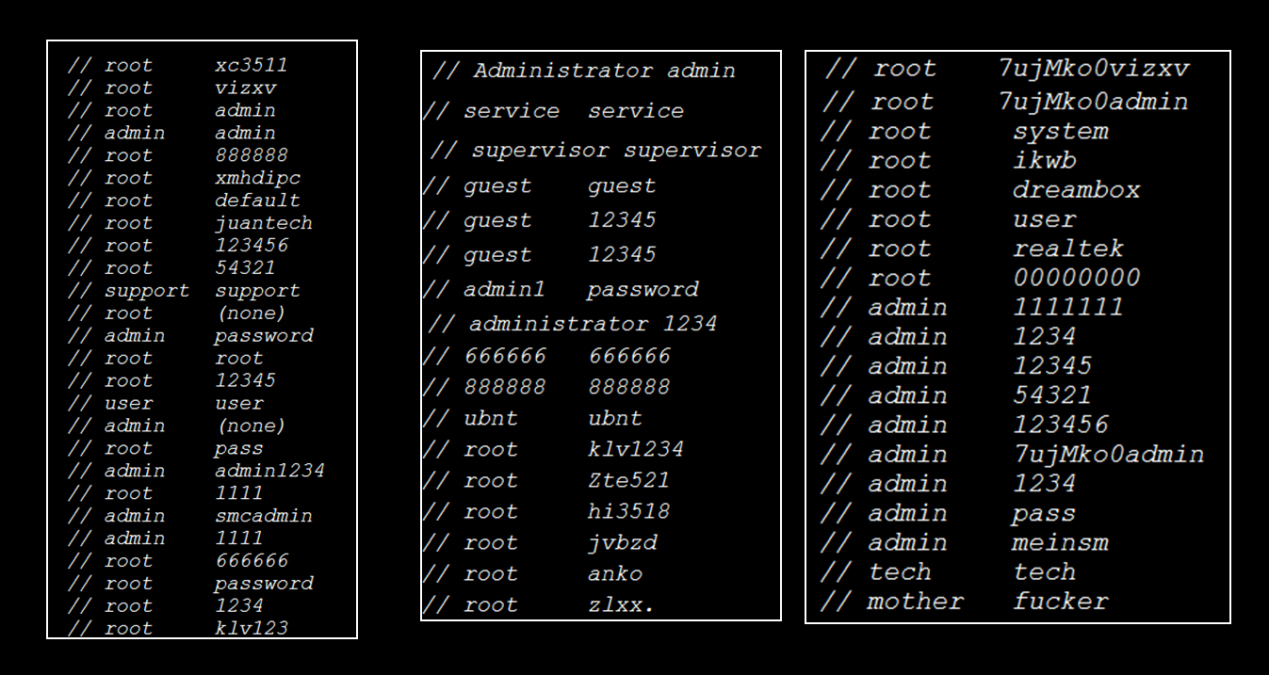
Usually, new username and password pairs indicate new targets. Some of the username and password pairs we found were the default settings of telecom home routers in China.
Figure 3. Default usernames and passwords used in the original Mirai botnet
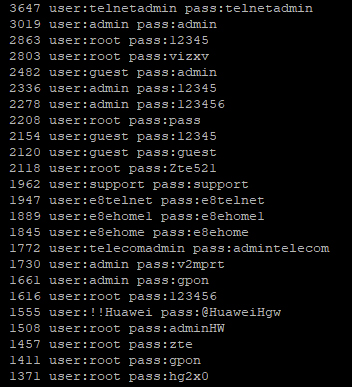
Examples included the telnetadmin:telnetadmin, e8telnet:e8telnet, and e8ehome:e8ehome pairs, which are used in the E-140W-P, HGU421v3, and E8C models, respectively. The scanner seemed to probe if there were any similar routers in Brazil.
Figure 4. Top 24 username and password combinations used in this operation
Routers, IP cameras, and DVRs used to probe targets
We checked some of the scanner’s IP addresses in historical databases, and found 167 routers, 16 IP cameras, and four digital video recorders (DVRs) to be involved in the scanning activity. This result indicates that the botnet master used the compromised devices to probe the targets.
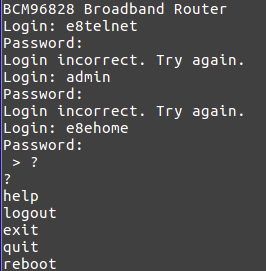
Figure 5. Login attempts to a broadband router
Most of the identified bot routers were Broadcom-based routers with default passwords. This finding checks out, considering that Broadcom is a leading home router software development kit (SDK) provider.
Figure 6. IP geographical distribution of top areas in China with scanning activity
Trend Micro recommendations and solutions
Default passwords have been notorious for being taken advantage of by malicious actors to access vulnerable devices, and this particular threat that we just encountered is another case in point. We therefore reiterate our advice to device users to avoid using default passwords and easy-to-guess credential combinations. It’s best to refrain from using common words found in the dictionary, familiar names, or personally identifiable information (PII). We recommend using at least 15 characters and mixing uppercase and lowercase letters, numbers, and special characters for passwords.
In addition, owners of devices that connect to the internet of things (IoT) can implement network segmentation and isolate devices from public networks — restricting traffic to specific ports can also be an added measure. Manufacturers, for their part, also shoulder the responsibility of securing device users by ensuring that overarching security is implemented from the device to the cloud. This includes paying close attention to potentially vulnerable product components and delivering patches whenever needed.
In addition to carrying out our aforementioned best practices on securing IoT devices, users can look into employing security solutions that will be able to monitor internet traffic, identify potential attacks, and block any suspicious activities on devices connected to the network. Our IoT Reputation Service (IoTRS), provided by the cloud-based Trend Micro™ Smart Protection Network™ infrastructure and integrated into several Trend Micro IoT security solutions, has updated its real-time block list to offer relevant safeguards against this threat and other malicious web accesses and aberrant behaviors associated with smart devices, including home routers, DVRs, and networked security cameras.
Users of the Trend Micro Home Network Security™ solution are also protected from this threat via these intrusion prevention rules:
- 1134550 TELNET Default Password Login -24
- 1134551 TELNET Default Password Login -25
- 1134552 TELNET Default Password Login -26
- 1133796 TELNET Default Credential Login Attempt -1