Mobile
GhostClicker Adware: a Phantomlike Android Click Fraud
We’ve uncovered a pervasive auto-clicking adware from as much as 340 apps from Google Play, one of which, named “Aladdin’s Adventure’s World”, was downloaded 5 million times. Our detections/sensors saw the prevalence of this adware in Southeast Asia.
We’ve uncovered a pervasive auto-clicking adware from as much as 340 apps from Google Play, one of which, named “Aladdin’s Adventure’s World”, was downloaded 5 million times. These adware-embedded applications include recreational games, device performance utilities like cleaners and boosters, and file managers, QR and barcode scanners, multimedia recorders and players, device charger, and GPS/navigation-related apps.
While the majority of the said apps have been taken down, 101 were still downloadable as of August 7, 2017. Our detections/sensors saw the prevalence of this adware in Southeast Asian countries as well as Brazil, Japan, Taiwan, Russia, Italy, and the U.S.
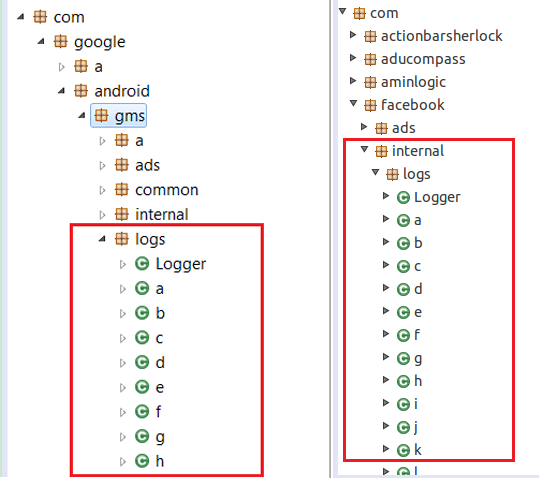
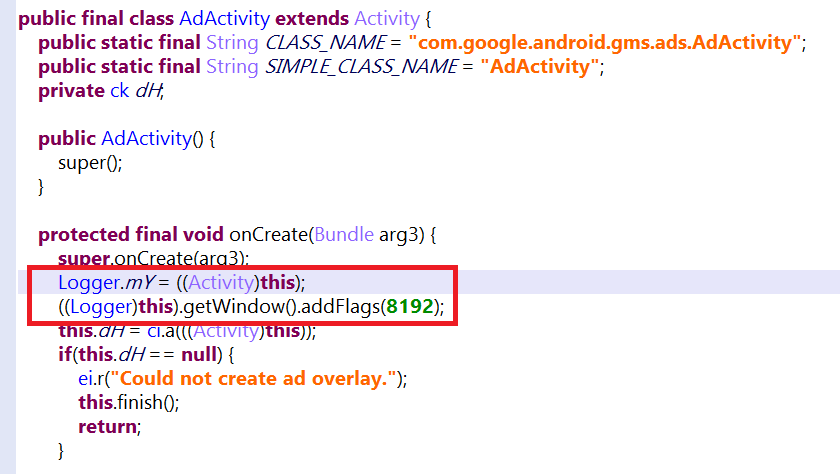
Trend Micro detects these adware as GhostClicker (ANDROIDOS_GHOSTCLICKER.AXM) given its auto-click routine and the way it hides itself in Google Mobile Services (GMS), the set of Google’s most popular applications and application program interfaces (APIs). GhostClicker also hides in Facebook Ad’s software development kit (SDK). It embeds itself into these two services disguised as a package named “logs”, possibly to avoid rousing suspicion by pretending to be a legitimate app component.
Figure 1. Snapshot of a GhostClicker-embedded app downloaded by as much as 5 million times
Figure 2. GhostClicker’s codes hides in GMS or Facebook Ads’ SDK
GhostClicker is pervasive and persistent—but finicky
The adware comes with a few requirements. Once launched, the affected app will retrieve the device’s system property (http.agent), which is used to configure the User-Agent string in Android devices. If the string contains “nexus”, GhostClicker’s routines will not be triggered. We construe this routine as a way to evade sandboxes like Android’s built-in Android Application Sandbox, as Android emulators/sandboxing environments are usually named “Nexus XXX”.
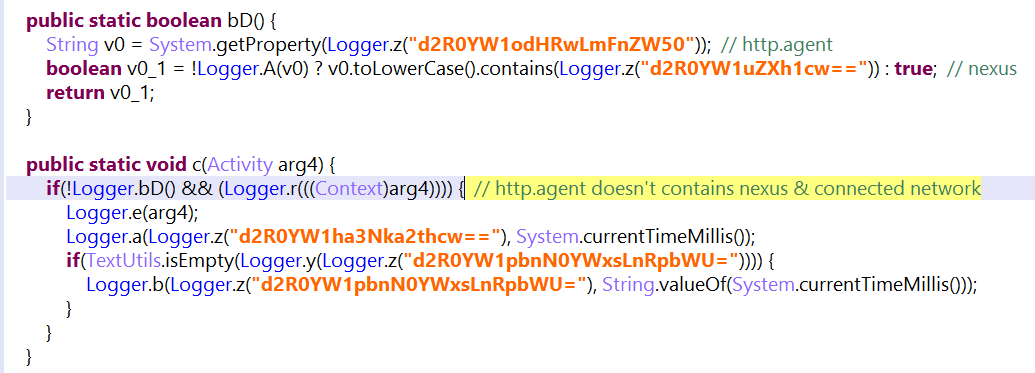 Figure 3. GhostClicker triggering its routines when the device’s http.agent doesn’t contain “nexus”
Figure 3. GhostClicker triggering its routines when the device’s http.agent doesn’t contain “nexus”
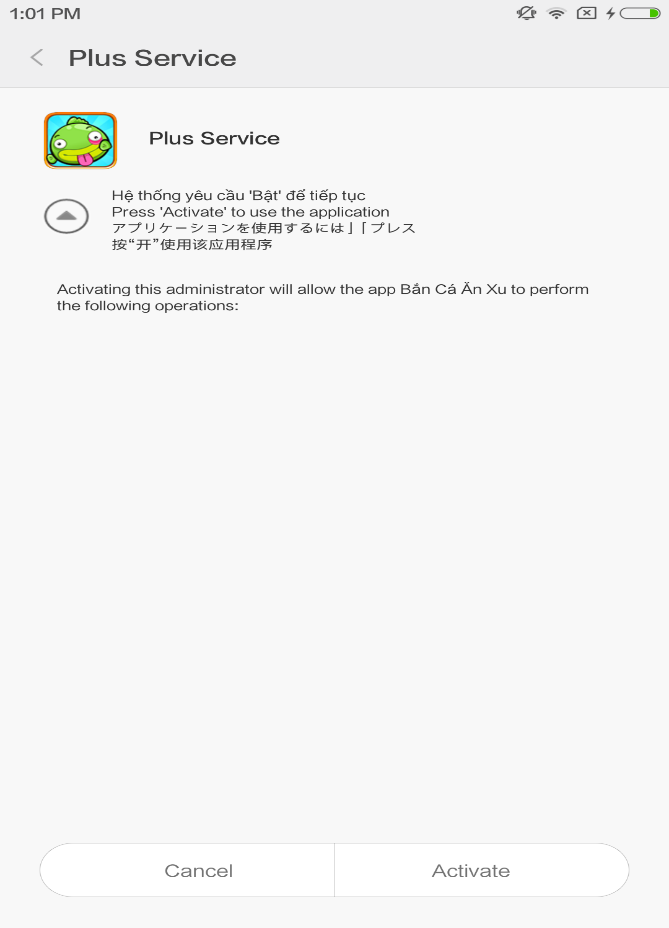
Some of the GhostClicker-embedded apps we analyzed also requested device administration permission when first run, but they do not declare the security policies used in metadata, such as wiping data and resetting password. This can be a way to deter users from removing the app, taking advantage of the lengthy and nebulous process of uninstalling apps. It’s certainly not a user-friendly process: uninstalling an app with device administration requires that it be disabled first before an app can be removed.
Figure 4. GhostClicker-affected app requesting device administration permission
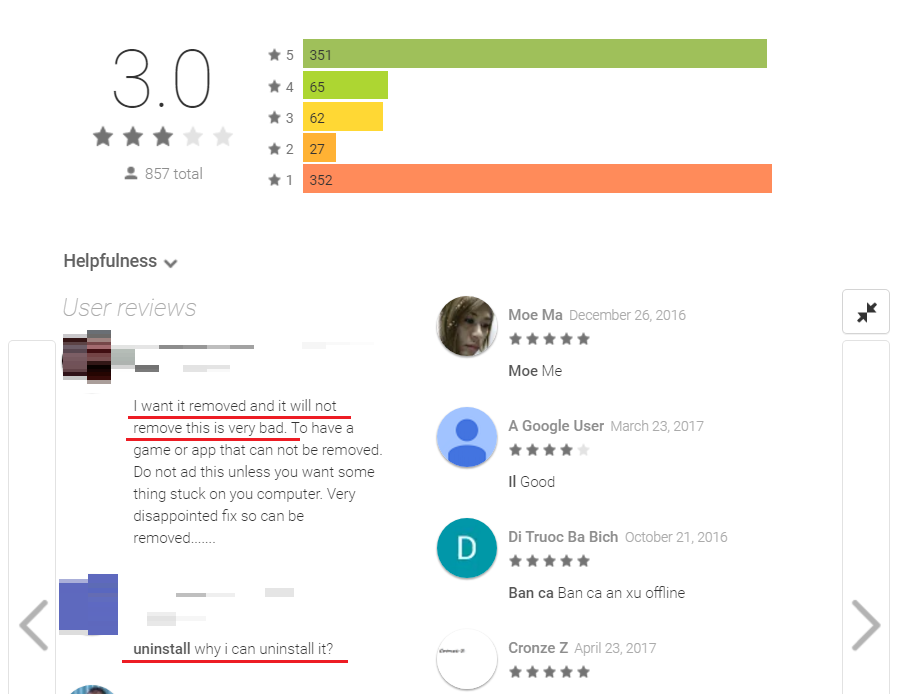
Figure 5. Snapshot of some users who can’t uninstall the app
GhostClicker earns its fraudulent keep through auto-clicks
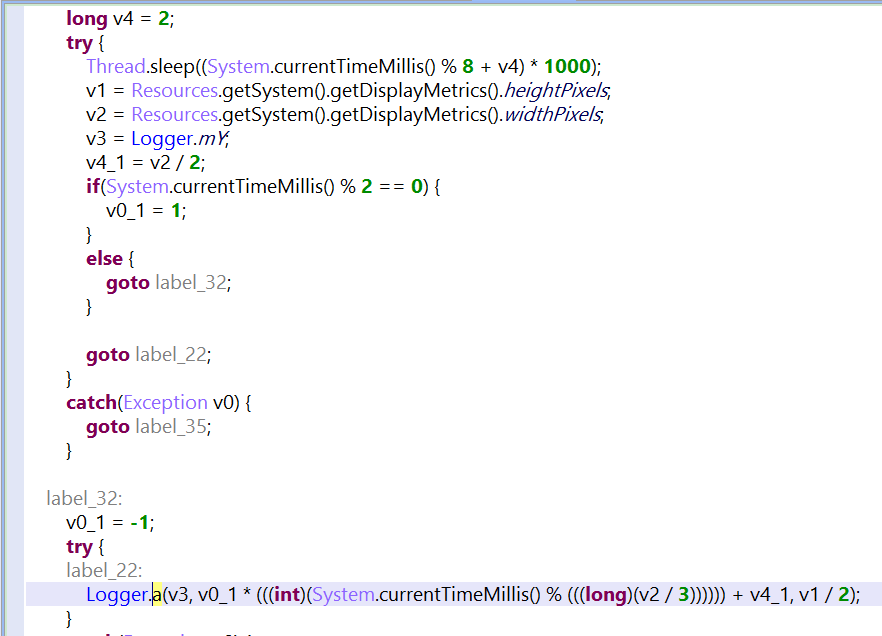
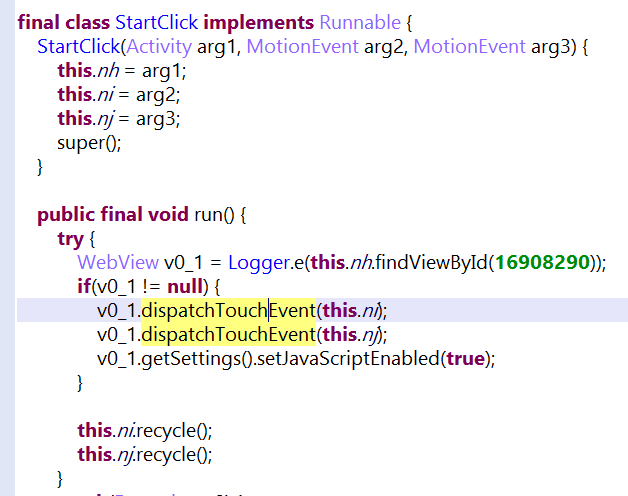
Unlike other adware, GhostClicker doesn’t use JavaScript code to locate/retrieve and click on advertisements. It instead inserts its code into Admob’s (a Google-owned mobile advertising platform) to get the ad's location. After getting the device’s screen dimensions (width and height), it calculates the appropriate XY coordinates then uses the dispatchTouchEvent API to simulate clicking. Indeed, it’s true to its moniker: ghosting over the device’s screen to click ads.
To earn more revenue, GhostClicker generates fake traffic. It will pop up in other apps’ download links in Google Store or open a YouTube video link in the device’s browser via communication with its command and control (C&C) server. Upon activation of device administration, GhostClicker will execute those auto-clicks every minute.
Figure 6. GhostClicker inserting code to get AdMob’s Context View
Figure 7. GhostClicker generating coordinates
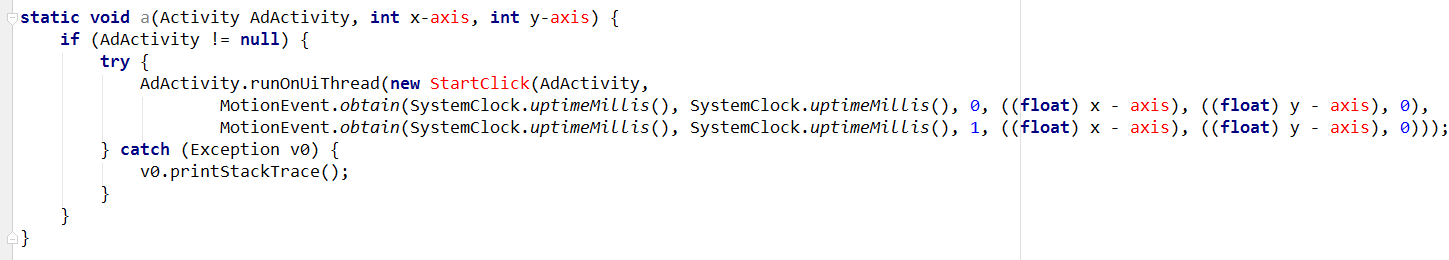 Figure 8. GhostClicker building a MotionEvent (simulating a touch) according to XY coordinates
Figure 8. GhostClicker building a MotionEvent (simulating a touch) according to XY coordinates
Figure 9. GhostClicker using the dispatchTouchEvent API to automatically click the ad
GhostClicker is actually an earlier version of itself
We hunted GhostClicker’s trail and found that it was an earlier iteration of itself. A later version removed the auto-click feature and device administration permission request, likely to make the adware stealthier. After the user unlocks the screen, the adware will pop up interstitial advertisements at certain intervals if the device is connected to a network with data . We encountered this version of GhostClicker in Aladdin’s Adventure’s World.
Retracing the adware’s timeline, we also saw that apps embedded with GhostClicker were continuously released for nearly a year. GhostClicker manifested as early as August 2016 hiding in GMS’ SDK. By March 2017, GhostClicker eschewed auto-clicks and leveraged Admob, Startapp, and Facebook Ads to pop up interstitial advertisements when receiving C&C commands. By May, it reintegrated auto-clicks and hid in Facebook Ads’ SDK. The notable updates and consistency in distribution points to a possible click fraud campaign, if not an actual cybercriminal operation.
Mitigation and Best Practices
Advertisements are an innocuous staple in the mobile ecosystem. GhostClicker, however, exemplifies how adware is intrusive, not to mention how it drains the device’s resources—CPU, battery, and internet data, to name a few. It puts the user’s privacy at risk by collecting personal information, often without knowledge or consent. Adware can also expose users to actual malware that go beyond showing bland advertisements.
GhostClicker can be mitigated by restricting the use of the device administration feature, which is typically used to create security-aware applications like enterprise device or BYOD management and antivirus apps. Everyday users won’t really miss out on much when doing this.
Keeping the OS updated (or asking your OEM about update availability) and adopting best practices for securing personal mobile devices is recommended. Enterprises should also do the same to their company devices or BYOD environment, as they’re the ones that use device administration. Reading app reviews also helps identify if the app performs certain suspicious behaviors.
Trend Micro Solutions
End users and enterprises can also benefit from multilayered mobile security solutions such as Trend Micro™ Mobile Security for Android™ which is also available on Google Play. Trend Micro™ Mobile Security for Enterprise provides device, compliance and application management, data protection, and configuration provisioning, as well as protects devices from attacks that leverage vulnerabilities, preventing unauthorized access to apps, as well as detecting and blocking malware and fraudulent websites.
We have disclosed our findings to Google and worked with them to take down the adware-laden apps on Google Play. Updates have also been made to Google Play Protect to take appropriate action on those apps that have been verified as violating Play policy. Google Play Protect has implemented expanded protections to ensure robust and scalable protections across the ecosystem. A list of Indicators of Compromise (IoCs) comprising related hashes (SHA256), package names and app labels, can be found in this appendix.