Exploits & Vulnerabilities
Industrial Router Risks in the Industry 4.0 Ecosystem
In our latest report, we analyzed how easily an industrial grade robot could be actually ”hacked”. We demonstrated how easily an attacker is able to alter an industrial robot’s accuracy without changing the program code.
The increased connectivity of computer and robot systems in the industry 4.0. ecosystem, is, and will be exposing robots to cyber attacks in the future. Indeed, industrial robots—originally conceived to be isolated—have evolved, and are now exposed to corporate networks and the internet.
While this provides synergy effects and higher efficiency in production, the security posture is not on par. In our latest report Rogue Robots: Testing the Limits of an Industrial Robot’s Securitywe analyzed how easily an industrial grade robot could be actually ”hacked”. We demonstrated how easily an attacker is able to alter an industrial robot’s accuracy without changing the program code so that that minor defects can be (maliciously) introduced into work pieces. Needless to say, defective products can have repercussions on the production floor and, depending on the security and QA practices of the target factory, may have some financial consequences down the line.
In order to see how easily a network attacker could gain access to the robots in a smart factory, that might be used in a mining business, by an automotive manufacturer or even in critical sectors that deliver public services, we considered possible entry points. One major entry point is provided by the existence of remote access and industrial routers Previous research by the Trend Micro Forward-Looking Threat Research (FTR) Team, specifically Exposed US Critical Infrastructure in Shodan, has shown that routers in general are among the most heavily exposed devices in the United States. At first, this may seem unsurprising, because a router’s main purpose is to connect to the Internet. However, given that industry-level routers connect more sensitive resources than generic (consumer-level) ones handle, we were surprised to find just how insecure they were.
Exposed Industrial Routers
An increasing number of industrial robots embed remote access devices (sometimes called “service boxes”) already used by the vendor for remote monitoring and maintenance. These devices are essentially industrial routers because they allow remote users to connect to a robot as if they were on a local network. Industrial routers provide an interesting attack surface for gaining access to a robot controller and other industrial machines. For example, attackers could target a widespread vendor of such appliances whose products are also resold by various robotics OEMs as part of their support contracts. Our market overview, summarized in Table 1, revealed about a dozen vendors who specialize in building industrial routers for various applications.
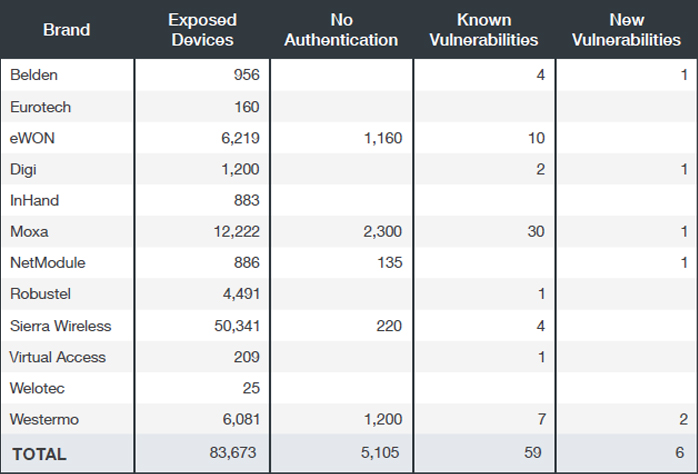
Table 1. Exposed industrial routers, according to Censys, ZoomEye, and Shodan search results as of late March 2017 (Note: We obtained the number of “known vulnerabilities” by querying Vulners.com while the number of “new vulnerabilities” is based on our own findings. “Potentially no authentication” refers to the presence of strings (e.g., “authentication disabled”) reported on the network service banners: we haven’t actively attempted to access any of these devices)
To focus specifically on exposed robots, for about two weeks we monitored Shodan, ZoomEye and Censys, three search services that index data from Internet scans to see if we can find connected robots from the top robot vendor companies.
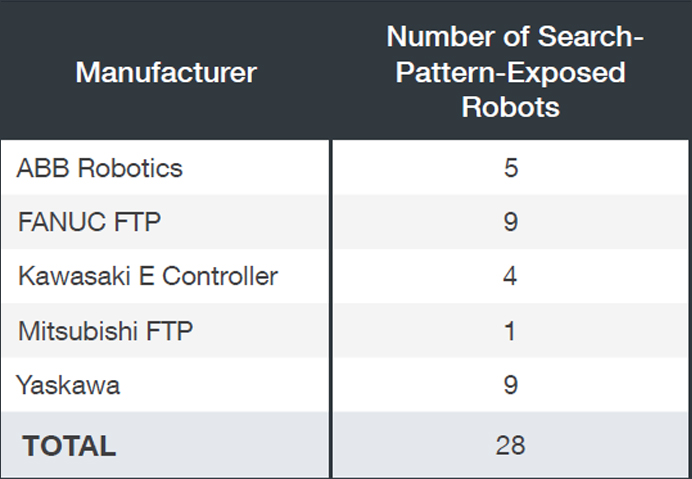
Table 2. Industrial robots exposed via their FTP servers according to Censys, ZoomEye, and Shodan search results as of late March 2017
Not all of the aforementioned vendors in Table 1 were as ready to respond and interact with us. However, ABB Robotics, eWON and Moxa have been very open to hear our suggestions for security improvements. ABB Robotics specifically already started creating an improvement and response plan that will influence their current product line.
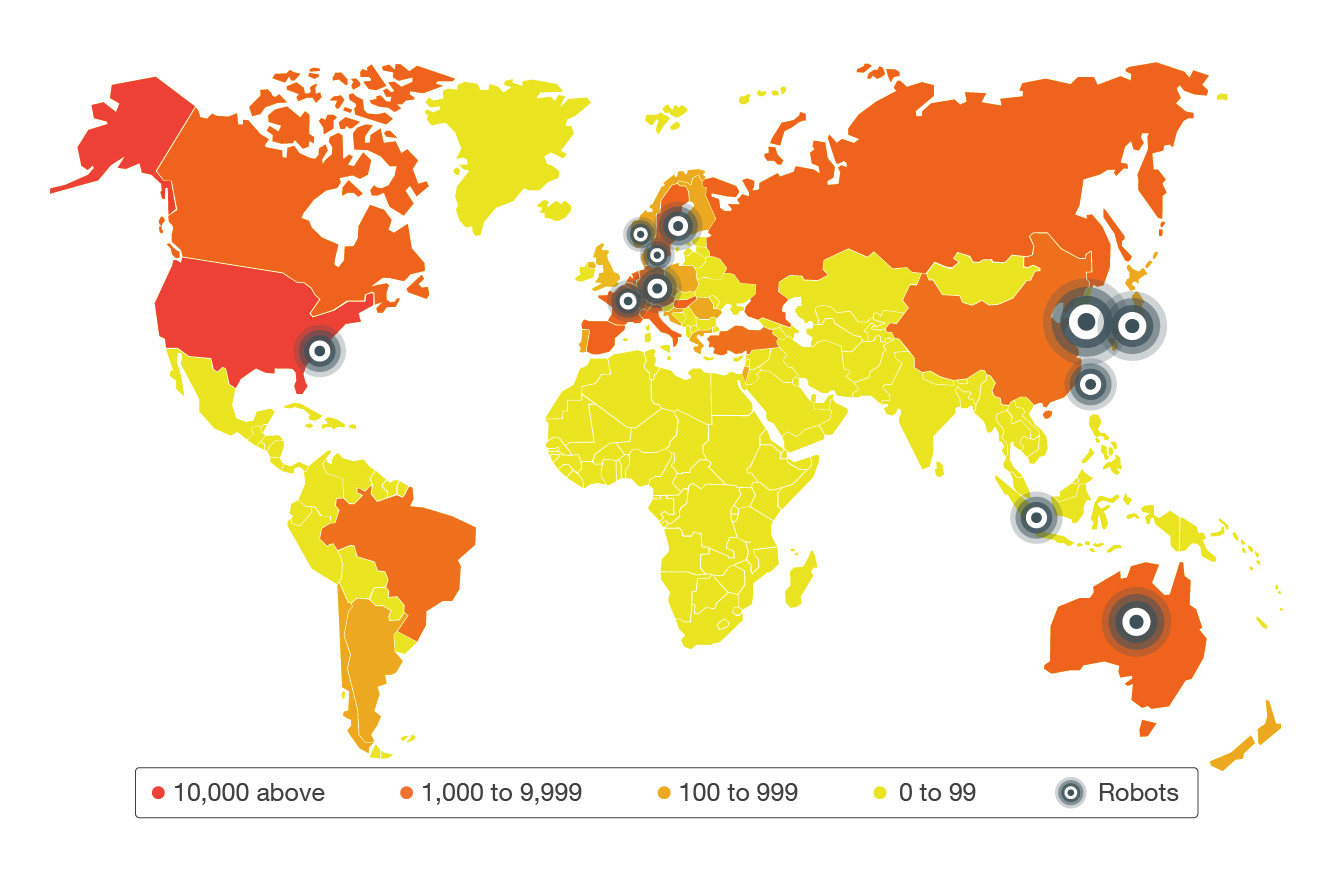
Figure 1. Map showing volume of exposed industrial routers (heat map) and presence of exposed robots
The United States has the most number of exposed routers based on our study, while Canada and several countries in Europe are among the top ten. Meanwhile, we found a handful of exposed robots in eleven countries including Korea, Japan, Australia, Germany and Sweden.
Exposed AND Unsecure
As we were continuing our case study on how an attacker might use what’s available to him outside the network in order to infiltrate a target facility, we found several industrial devices that exposed the configuration web interface to the internet, most of them through a cellular network. The web-based console, when enabled also for the interface, provides an easily “finger-printable” attack surface for exploiting vulnerabilities or misconfigurations in the router and gaining access to the industrial robot (as well as to other industrial devices connected to them). In addition to known vulnerabilities, we found new vulnerabilities that can be exploited by an attacker who wants to gain access to a network and the industrial robots connected therein. They can be summarized under the following macro classes:
- Information disclosure and “finger-printability”
- Outdated software components
- Default credentials or poor authentication
- Poor transport encryption
- Insecure web interface
- Poor software protection
These classes of vulnerabilities are by no means new. As a matter of fact, they are well known to both security researchers and router vendors. Unfortunately, the vendors themselves are not always in a position to address these issues because, once sold, these devices are not always under their control—the clients might not even want the vendors to be able to do that. We were told by the vendors that they were aware of the sheer number of easily-finger-printable devices that can be found on Shodan, and even when vendors roll out updates, clients would simply not apply them.
An easy way to keep these devices from being exposed on the public internet would be to connect them to a centralized, multi-tenant management portal that would completely replace the classic web interface. Several vendors are adopting this “ala reverse-shell” approach, which we believe is a step forward to making (industrial) routers manageable, indirectly reachable from the outside, and unexposed. Clearly, this would shift the attention of the attackers towards the centralized management portal, which in turn would have the advantage of being easier to manage in terms of security.
More details on our findings are in our latest research paper Rogue Robots: Testing the Limits of an Industrial Robot’s Security, which includes a video of the attack demonstration. Our full research will be presented in the upcoming Institute of Electrical and Electronics Engineers (IEEE) Security and Privacy Conference in San Jose this coming May.