Malware
RAMNIT: The Comeback Story of 2016
Cybercriminals have taken advantage of generous individuals by sending phishing emails that falsely promoted a link to a supposed donations page. The user, instead, unwittingly downloads a tenacious malware: the veteran Trojan known as RAMNIT.
Earlier this year, Action Fraud, the UK’s fraud and cybercrime reporting center, issued a warning that cyber criminals were taking advantage of generous individuals by sending phishing emails purportedly from Migrant Helpline, a charity organization dedicated to assisting migrants across the country. These emails contain a link that is supposed to lead to a donations page. However, instead of landing on a legitimate website, the user instead unwittingly downloads one of the most tenacious malware in the wild: the veteran Trojan known as RAMNIT, which staged a comeback in 2016.
In our 2016 roundup, we discussed how banking trojans continue to be a significant threat for organizations. According to our Smart Protection Network™ data, several RAMNIT variants were detected in several computer systems as the top banking malware by detection name for every quarter of 2016, a surprising revelation given its February 2015 takedown which saw Europol shut down several of its command-and-control servers. At the time of the Europol takedown, RAMNIT was believed to have infected up to 3.2 million users.
Given the scope of the operation, it would have been reasonable to assume that there would be a significant decrease in RAMNIT infections post-takedown. But while there was a dip in infections for February 2015, it bounced back almost immediately the next month, maintaining an infection mark of more than 10,000 for the rest of 2015. The malware was reported to have resurfaced in December 2015 and August 2016, which might account for the spikes seen in the succeeding months.
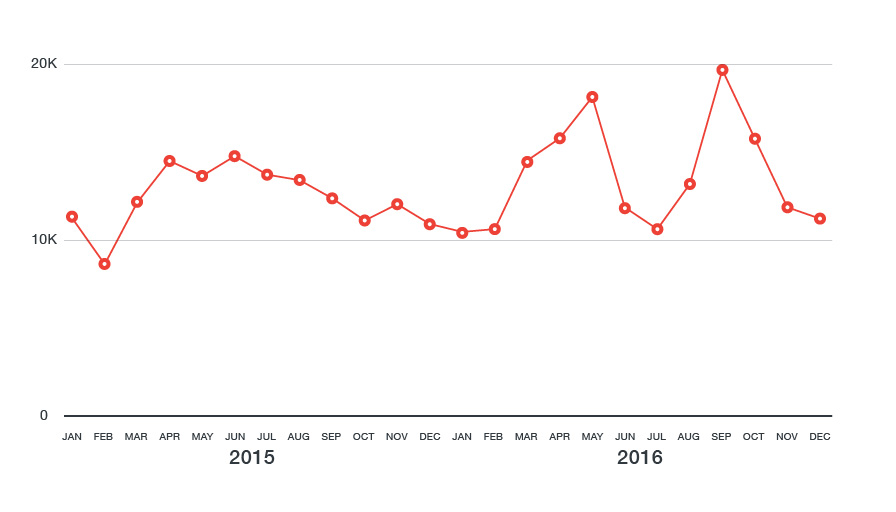 Figure 1. RAMNIT infection data for 2015 and 2016
Figure 1. RAMNIT infection data for 2015 and 2016
One important point that needs to be made is that RAMNIT the malware should be distinguished from the cyber criminals responsible for its spread. We’ve already seen a similar case with DRIDEX, which was targeted by the FBI in 2015 and reemerged under similar circumstances, proving that takedowns do not necessarily correlate to a drop in infections. We can surmise that RAMNIT has grown beyond the scope of the original threat actors as seen through its continued persistence throughout 2016.
An ever-evolving threat
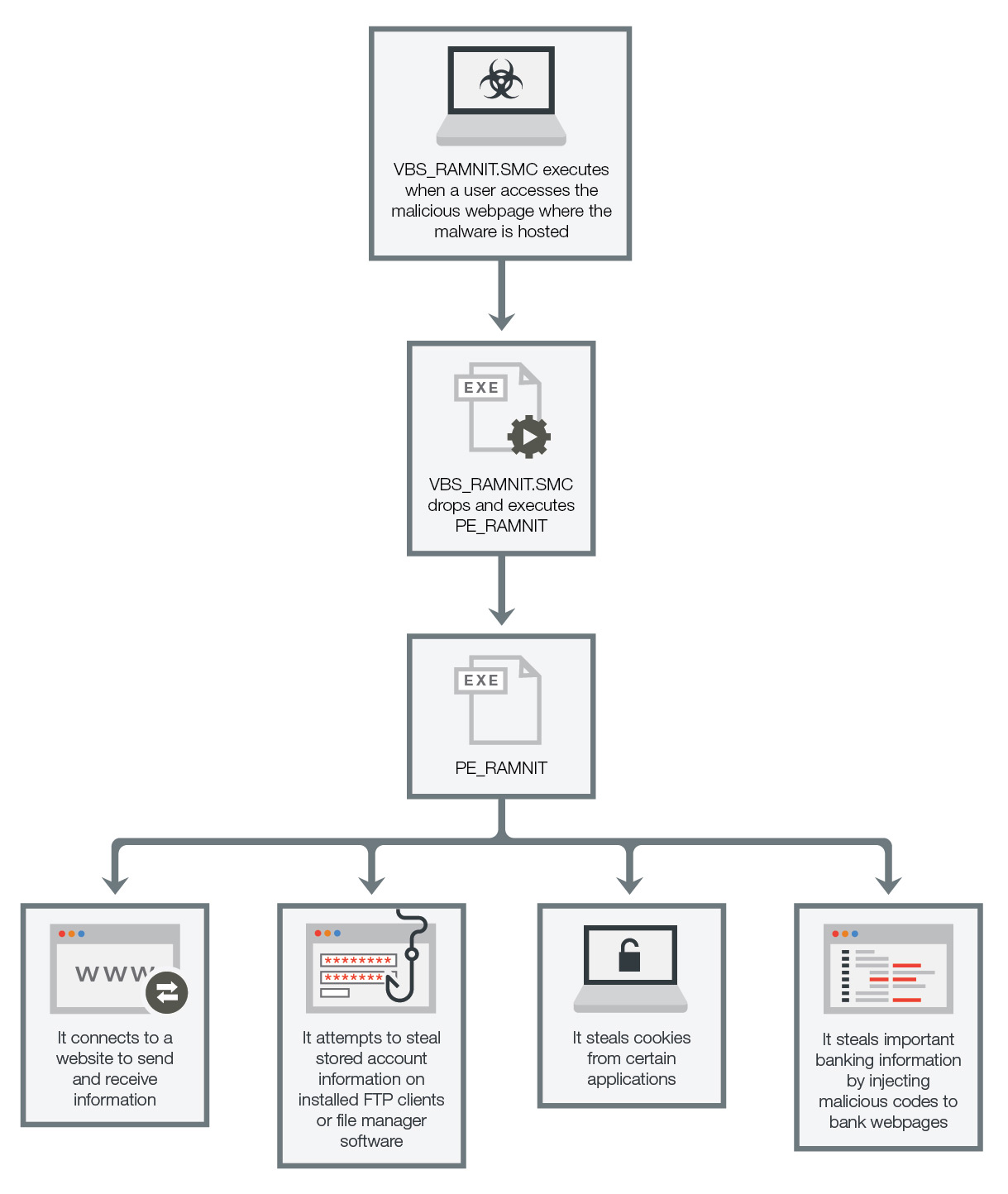
In 2010, we detected our earliest variant of RAMNIT, HTML_RAMNIT.ALE, which is a basic HTML Trojan that drops and executes its payload on the infected system. Its relative simplicity contrasts with VBS_RAMNIT.SMC and PE_RAMNIT, two variants we discovered in 2016 post-takedown.
Figure 2: RAMNIT Infection Flow
VBS_RAMNIT.SMC executes once a user accesses the website in which it is hosted, after which it drops and executes PE_RAMNIT, a malware which is notable for having high damage potential with both backdoor and information theft capabilities. PE_RAMNIT then uses C&C communication to receive remote commands and send information such as stolen cookies and sensitive account data. It also injects malicious codes into bank webpages in order to access confidential client information from unsuspecting victims. Furthermore, PE_RAMNIT proves itself to be a stubborn malware by injecting itself into all running processes to remain memory-resident, and deleting antivirus-related registry keys to make it undetectable.
|
|
Table 1: RAMNIT attempts to steal account information used in the following installed FTP clients or file manager software
RAMNIT’s ability to evolve and spread is a key factor to its prevalence. First encountered in 2010, the original RAMNIT variant was a worm that propagated through removable drives and FTP servers. In 2011, it was discovered that RAMNIT copied portions of the Zeus source code, transforming it into a banking Trojan that stole user credentials and other personal information. Its perpetrators have also expanded the malware’s capabilities over the years, adding features such as web injection mechanisms, allowing it to compromise the websites of financial organizations.
RAMNIT’s proliferation can be attributed to its wide variety of distribution channels, which includes traditional phishing scams such as email spam and social engineering attacks. Recently, RAMNIT was also found to have been spreading via an Angler exploit kit found embedded in a compromised website, adding to its already impressive list of attack vectors. As an infector, RAMNIT can easily spread to new victims who are unable to clean up the infected files, making them prone to reinfection.
Prevention is the best cure
RAMNIT’s rise proves that users can still fall victim to “classic” threats. Not only is there a need to be extra vigilant, it is also important to implement guidelines and best practices to protect the organization against evolving threats like RAMNIT:
- Organizations need to educate their end users on the best practices for email and social media security such as never clicking links or downloading attachments, especially if it comes from suspicious sources.
- Network administrators should also look into shoring up their email security by implementing an effective antispam strategy, which includes optimizing their organization’s web filters and detection level thresholds. Furthermore, any suspicious emails with embedded links should be reported to the IT department for further analysis.
- As we’ve observed in the Migrant Helpline case, the use of phishing plays a large part in RAMNIT’s spread. Users should be aware of what to look out for when it comes to the social engineering tactics used by cyber criminals to get them to click links or download files.
- Implementing two factor authentication and managing account passwords on a regular basis will help protect users from cyber criminals who are looking to steal confidential information.
Trend Micro Solutions
Trend Micro protects users and organizations through Trend Micro™ Smart Protection™ Suites and Trend Micro™ Security, which provides comprehensive multilayered solutions, including the ability to detect malware and block malicious URLs that spread Trojans such as RAMNIT. For small businesses, they can use Trend Micro Worry-Free™ Business Security to secure their systems.
With additional insights from Nikko Tamaña