In our previous post, we reported about new breed of Remote Access Tool (RAT) called PlugX, which was used in targeted attacks using Poison Ivy. At first glance, this RAT appears to be a simple tool with limited remote access capabilities. However, further analysis of PlugX reveals that it might be keeping more tricks up its sleeves.
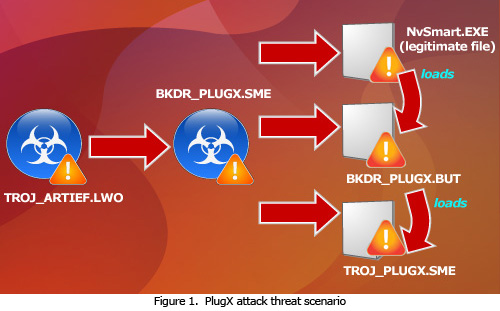
In a typical attack, PlugX usually comes with the three file components, namely:
- A legitimate file
- A malicious DLL that is loaded by the legitimate file
- A binary file that contains the malicious codes loaded by the DLL.
The attack starts with a phishing email containing a malicious attachment, usually an archived, bundled or specially crafted document that exploits either a vulnerability in Adobe Acrobat Reader or Microsoft Office (in particular CVE-2010-3333). In this example, it arrives via a specially crafted document (detected as TROJ_ARTIEF.LWO). The said Trojan drops and executed BKDR_PLUGX.SME that drops the following files:
- All Users’ %User Profile%\Gf\NvSmart.exe – a legitimate NVIDIA file (NVIDIA Smart Maximise Helper Host)
- All Users’ %User Profile%\Gf\NvSmartMax.dll – BKDR_PLUGX.BUT
- All Users’ %User Profile%\Gf\boot.ldr – TROJ_PLUGX.SME
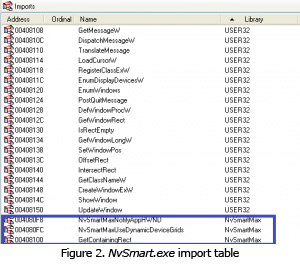
Notice that the malware drops the file NvSmart.exe, which is a known legitimate NVIDIA file.
Looking at the NvSmart.exe’s import table, we can observe that it imports three functions from NvSmartMax.dll. Normally, it would load a legitimate NvSmartMax.dll. But if a malicious version of this DLL file is located in the same directory, it would load this version instead.
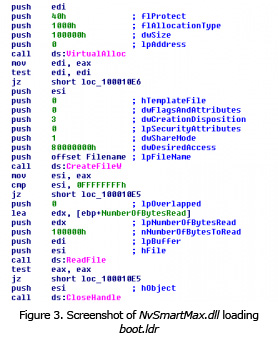
The malicious NvSmartMax.dll then loads boot.ldr found in the same directory. The said file contains the malicious code used by NvSmartMax.dll.
Digging deeper at what the loaded code does, we can see that it first decrypts itself to form what seems to be an "executable file" in its memory space. All the backdoor modules can be found in this "executable file".
However, the loaded code does not drop this decrypted "executable file". Instead, it injects the codes to the legitimate process svchost.exe, possibly to avoid detection. After it has injected its code to svchost.exe, it then terminates the initially executed NvSmart.exe.
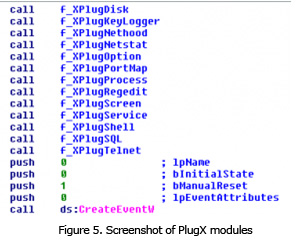
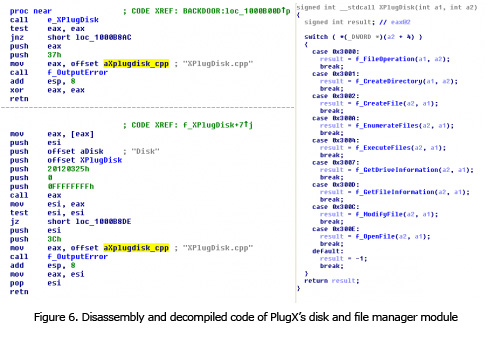
Our analysis of the decrypted executable file shows that this threat is designed and filled with several backdoor modules. These modules are organized to perform tasks unique to the module. We uncovered the following modules from the malware:
| PlugX module | Backdoor functions |
| XPlugDisk | Copy, move, rename, delete files Create directories Create files Enumerate files Execute files Get drive information Get file information Modify files Open files |
| XPlugKeyLogger | Log keystrokes and active window |
| XPlugNethood | Enumerate TCP and UDP connections Enumerate network resources Set TCP connection state |
| XPlugOption | Display a message box Lock workstation Log off user Restart/Reboot system |
| XPlugPortMap | Perform port mapping |
| XPlugProcess | Enumerate processes Get process information Terminate processes |
| XPlugRegedit | Enumerate registry keys Create registry keys Delete registry keys Copy registry keys Enumerate registry entries Modify registry entries Delete registry values |
| XPlugScreen | Screen capture Capture video |
| XPlugService | Delete services Enumerate services Get service information Modify services Start services |
| XPlugShell | Perform remote shell |
| XPlugSQL | Connect to a database server and execute a SQL statement |
| XPlugTelnet | Host Telnet server |
Similar to our initial PlugX post, we observed that it drops a debug log file in % All Users Profiel%\SxS\bug.log. This file contains error codes that the malware author can use to improve PlugX. For example, if the malware couldn’t access certain files or folders, it would create a log of this incident. Using this debug log as reference, the malware author can then modify future versions of PlugX to access these files or folders. The author could even use this log to know how it can avoid detection or being disabled. Thus, this file may be crucial in creating more effective versions of PlugX tools in the future.
Trend Micro users are protected by the Smart Protection Network™. In particular, file reputation service detects and deletes PlugX (BKDR_PLUGX and TROJ_PLUGX). Web reputation and email reputation services blocks access to the said C&C and related email respectively. Trend Micro Deep Security users are protected from this threat via rule 1004498 - Word RTF File Parsing Stack Buffer Overflow Vulnerability.
Trend Micro will continue to monitor PlugX’s development and the campaign behind it.