Ransomware Recap: Patcher Ransomware Targets MacOS
 After discussing the rise of ransomware targeting non-Windows systems in early February, further proof of this diversification emerged with the discovery of Patcher (detected by Trend Micro as OSX_CRYPPATCHER.A), a ransomware variant that targets MacOS users.
After discussing the rise of ransomware targeting non-Windows systems in early February, further proof of this diversification emerged with the discovery of Patcher (detected by Trend Micro as OSX_CRYPPATCHER.A), a ransomware variant that targets MacOS users.
[Related: How UNIX-based ransomware is changing the game]
Patcher, which is downloaded via bittorrent, masquerades as a patcher for popular applications such as Microsoft Office and Adobe Premiere Pro. Once downloaded, the files in the folder display fake applications using the “Patcher” label.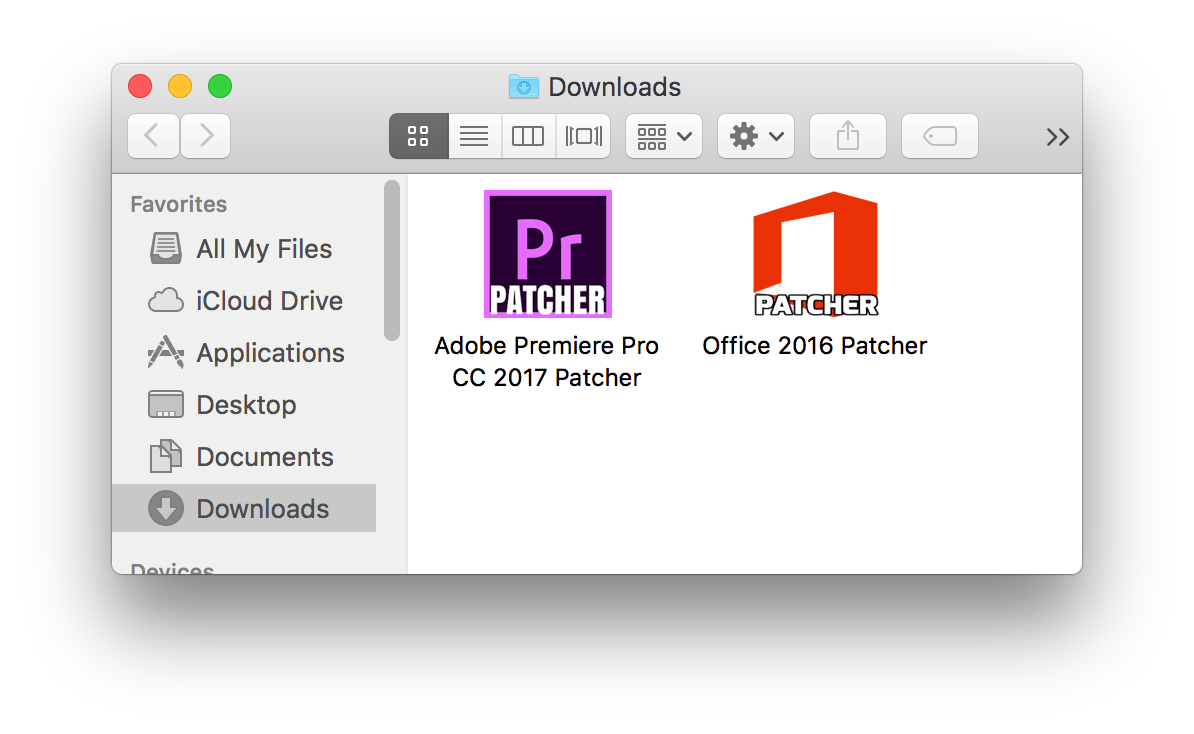
When any of these files are run, a window will pop up displaying a fake patching screen. Once initiated, the Patcher ransomware will begin to encrypt files using a random 25-character string as its encryption key. It will encrypt files found in /Users directories as well as files found in mounted and external storage using /Volumes directories. A ransom note asking for 0.25 BTC, or approximately $300, will also be dropped into the user’s system.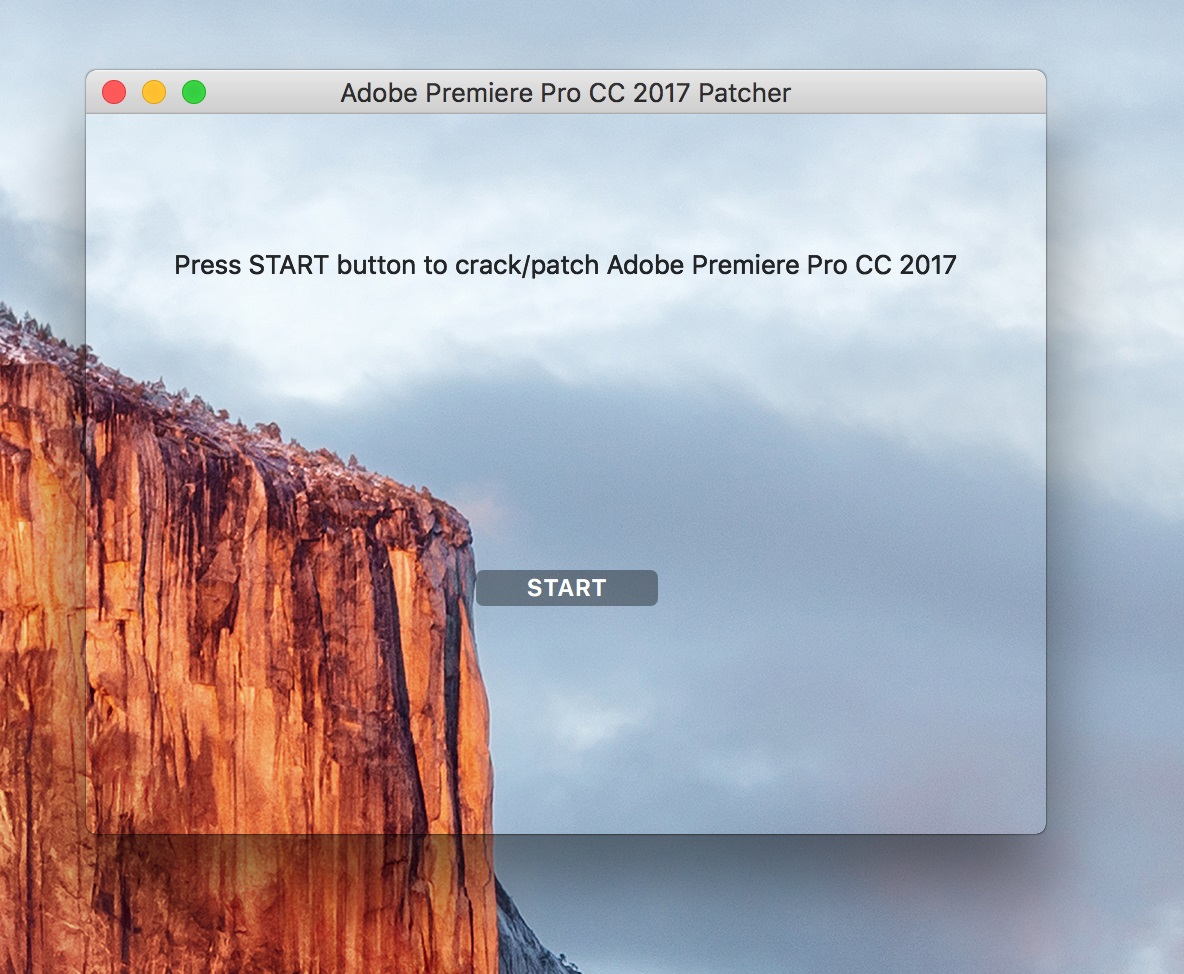
Image via bleepingcomputer.com
However, even if the malware’s victims manage to pay the ransom, their files will still suffer irreparable damage due to a serious flaw with the ransomware: the code for communicating with its command and control servers is broken. This flaw means that even the ransomware’s perpetrators will be unable to supply a method for decrypting the victim’s files.
It can be surmised that Patcher’s authors are relatively inexperienced due to the ransomware’s erroneous coding. However, it is still dangerous enough to cause extensive damage – especially due to the lack of a decryption process resulting in potentially permanent encryption.
Here are the other notable ransomware stories from the week of February 16 to 24:
Trump Locker
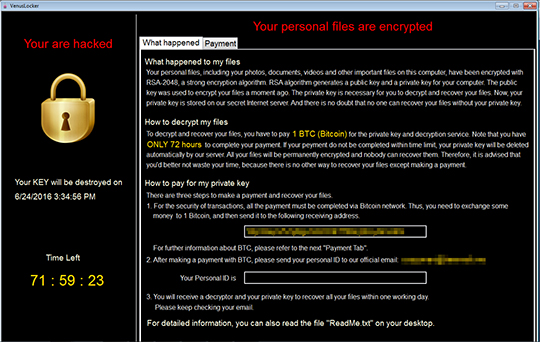
A purportedly new ransomware that is taking advantage of current US political trends might just be an older ransomware in disguise. According to researchers, the recently discovered ransomware known as Trump Locker (detected by Trend Micro as RANSOM_VENUSLOCK.F) bears heavy resemblance to the Venus Locker ransomware that was detected in August 2016.
One notable similarity between Trump Locker and the earlier Venus Locker variant (detected by Trend Micro as RANSOM_VENUSLOCK.C) is the way they encrypt files. While both malware types encrypt certain files using full encryption methods, other files that use specific file extensions only have their first 1024 kb encrypted. The fully encrypted files are appended with a .TheTrumpLockerf extension, while the partially encrypted files are given a .TheTrumpLockerp extension. Both malware will also avoid encrypting files that use certain strings in their folder path name.
Another similarity between the two ransomware variants is the ransom note, which is virtually identical except for some minor changes—primarily the email address to which the personal ID is sent to after paying the ransom.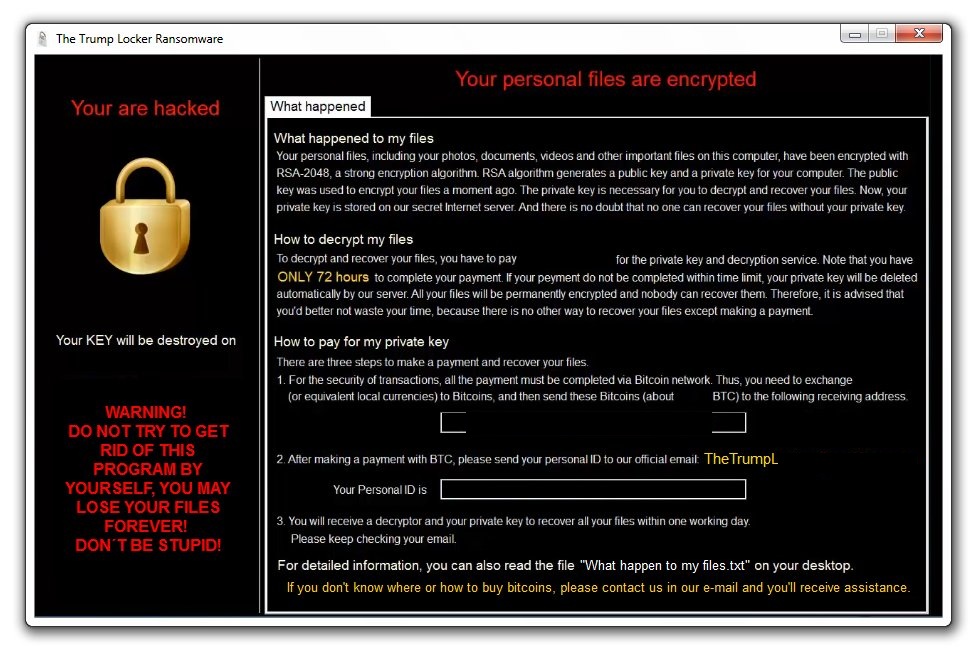 \
\
Hermes
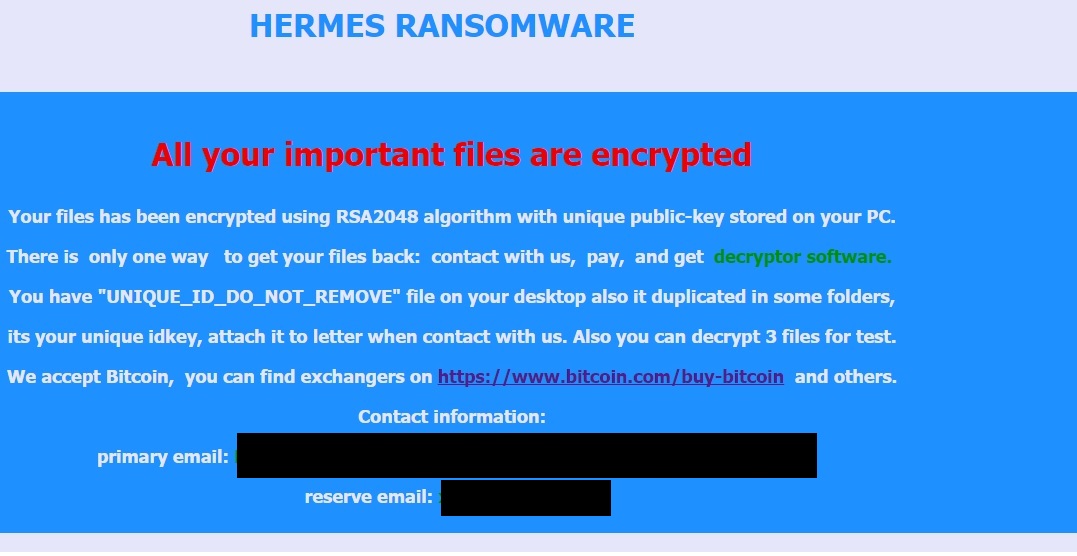
In addition to encrypting files, it also deletes System Restore points and reduces the allotted space for System Restore to a maximum shadow storage size of 401MB. In addition, it kills the task manager and deletes additional backup files.
CryptoShield
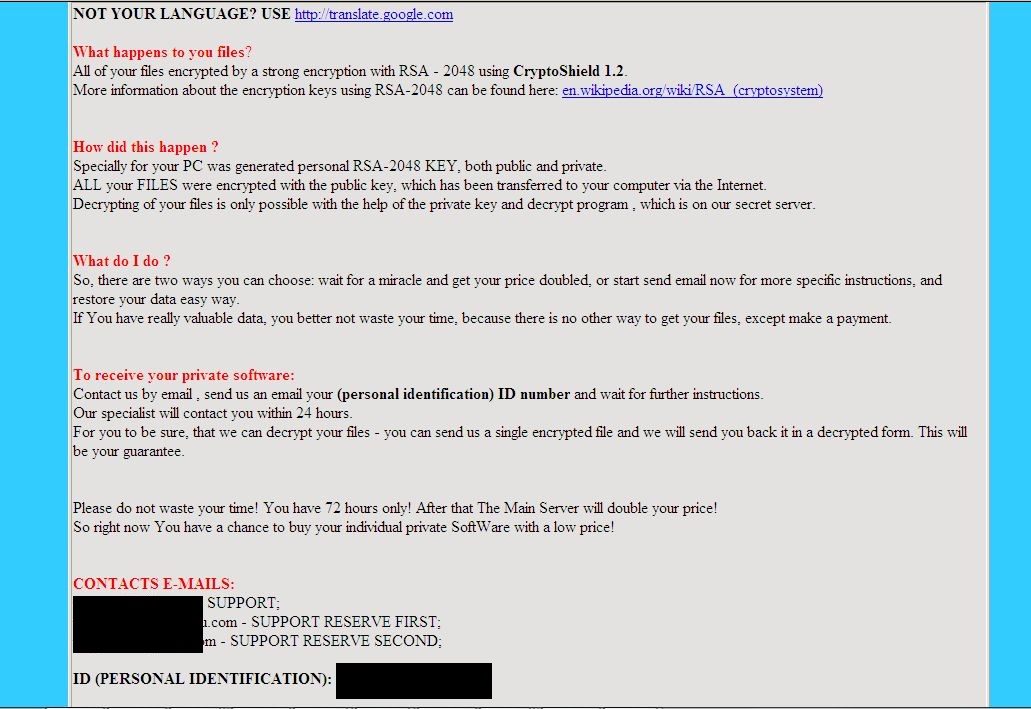
February also saw the emergence of CryptoShield (detected by Trend Micro as Ransom_CRYPAURA.SHLD), a new variant of CryptoMix that is being distributed via exploit kits.
Once it is downloaded and executed, CryptoShield will begin scanning for targeted files using specific extensions. It will then encrypt files using the AES-256 encryption and append the .CRYPTOSHIELD extension to the affected files. CryptoShield will also display a fake Explorer.exe prompt containing the following text: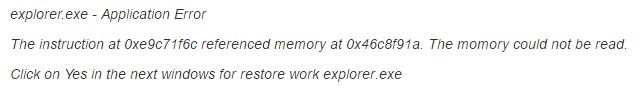
The malware will post a ransom note asking for payment within 72 hours, after which the price for decryption doubles. The ransom note also contains a personal identification number for the affected system.
Like Hermes, CryptoShield causes additional recovery problems by deleting shadow volume copies using the C:\Windows\System32\cmd.exe" /C vssadmin.exe Delete Shadows /All /Quiet command.
Ransomware Solutions:
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevents ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation