Ransomware Recap: CRYPSHED Spoofs Amazon in Ransomware Campaign
CRYPSHED
A variant of the CRYPSHED ransomware has been found being spread via emails that are purportedly sent as a dispatch confirmation from Amazon. The email itself is very deceptive, with a header containing an “amazon.co.uk” domain that could trick many users into believing its legitimacy. However, hovering over the link reveals that it's a malicious attack, as it leads to a domain that differs from the one Amazon uses, using the following format:
hxxp://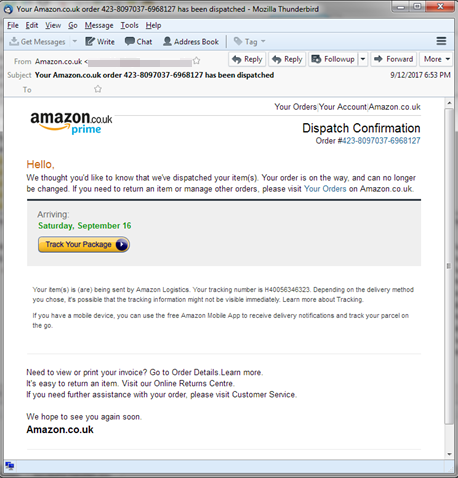
Figure 1: Fake email from “Amazon”
“AmazonSignIn.html” is injected into the vulnerable web servers, after which it will display a fake login page: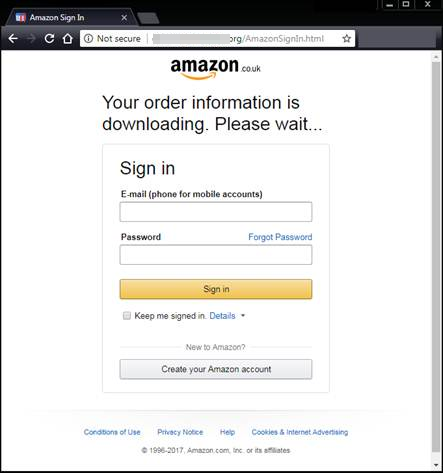
Analysis of the page’s source code reveals an iframe that redirects the user to a download URL containing a JS file. Opening this file downloads and executes CRYPSHED ransomware on the user’s system.
LOCKY/FAKEGLOBE
Dealing with one ransomware variant should be dangerous enough. But what happens when a single campaign combines two of the more notorious ransomware in FAKEGLOBE and LOCKY? In August, a new wave of attacks was seen spreading a LOCKY variant using spam emails. This was followed by a new spam campaign in September that included a link to an archive that would deliver the payload.
Unlike the August campaign that involved an indiscriminate spam email, the September campaign used social engineering tactics, tricking the users into believing that the email is a legitimate bill from one of their utility providers. The email contains both a malicious attachment and a malicious link, as seen in the email sample below: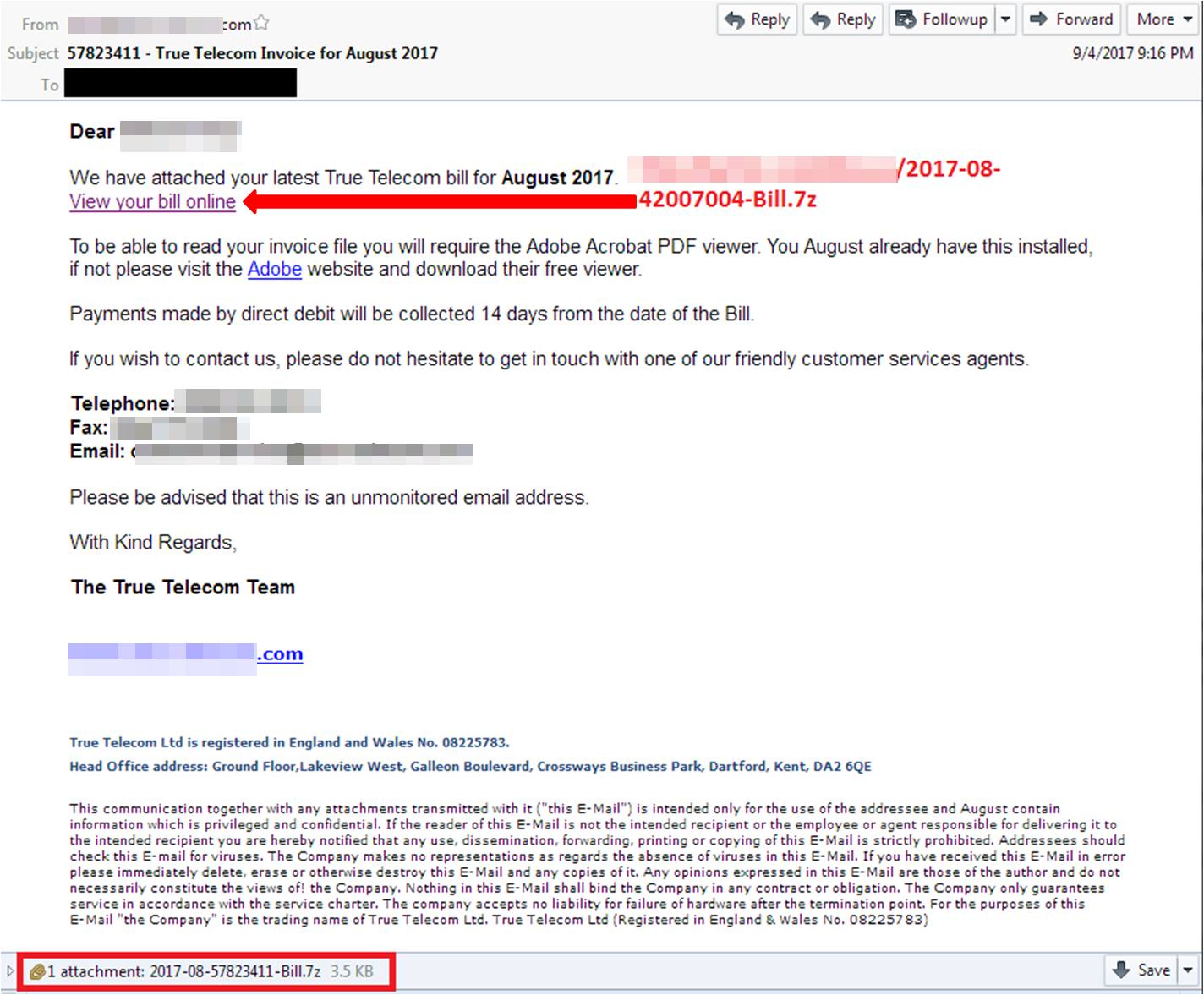
Figure 3: Spam sample containing the archived attachment
These links lead to scripts that download two different binaries. One script is responsible for downloading a variant of LOCKY (Detected by Trend Micro as RANSOM_LOCKY.TH908) with an affiliate ID of 3. The affiliate ID is then sent to LOCKY’s Command & Control (C&C) servers along with the victim ID and other information. This allows the threat actors to determine who among them will receive the payment coming from the victims, as they share the same payment infrastructure.
A second script connecting to another URL downloads an additional payload: the FAKEGLOBE or “Globe Imposter” ransomware (Detected by Trend Micro as RANSOM_FAKEGLOBE.ASUUG), which appends the .txt extension to the names of the encrypted files and drops Read_ME.html as its ransom note: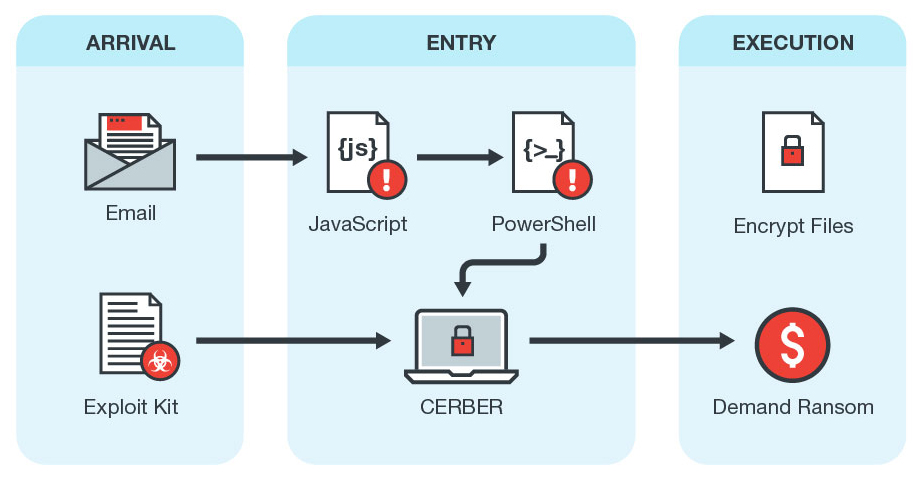
Figure 5: Cerber Version 6 Infection Chain
As of publication, it is still unclear how the attackers were able to compromise the website. However, the links to the malware have already been taken down.
AMNESIA
Months after its peak, it seems that some ransomware operators are still trying to cash in on WannaCry's success. Amnesia (Detected by Trend Micro as RANSOM_AMNESIA) is one of the ransomware that still references WannaCry.
Amnesia uses email attachments containing PDF or zip files as its main distribution method. The ransom note, in particular, mentions WannaCry as part of its text: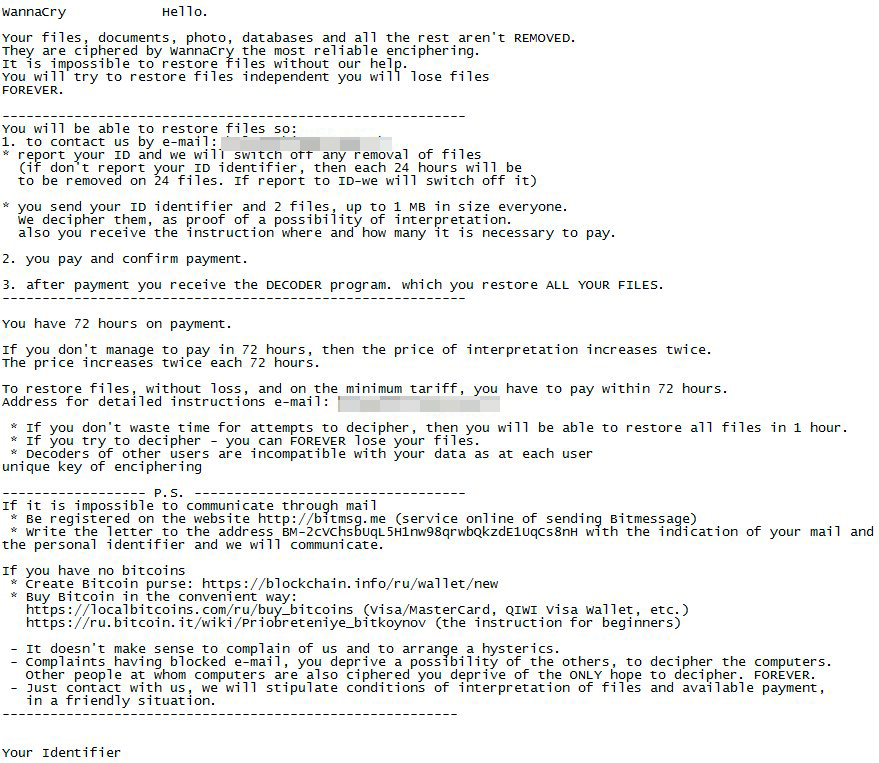
Figure 6: Amnesia ransom note (Image courtesy of Malware Hunter Team)
It also appends the .wncry extension to encrypted files, adding to the WannaCry-wannabe behavior.
PARADISE
The ironically-named Paradise ransomware (Detected by Trend Micro as RANSOM_PARADISE) is a Ransomware-as-a-Service (RaaS) that seemingly uses hacked Remote Desktop services in order to gain administrative privileges, after which it will generate a key that it will use to encrypt files.
Once done with encryption, it will drop a ransom note containing an email address and instructions on how to send payment. According to the note, the amount to be paid depends on how fast the victim replies to the attacker: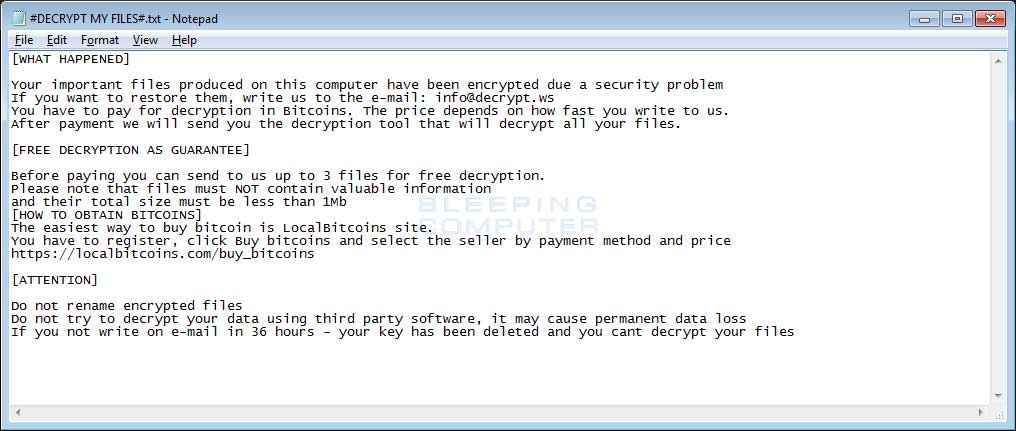
Figure 7: PARADISE ransom note (Image courtesy of Bleeping Computer)
To help mitigate the impact of the ransomware mentioned in this entry, both users and enterprises can implement these best practices.
Trend Micro Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
End users and enterprises can also benefit from multilayered mobile security solutions such as Trend Micro™ Mobile Security for Android™ (available on Google Play), and Trend Micro™ Mobile Security for Apple devices (available on the App Store). Trend Micro™ Mobile Security for Enterprise provide device, compliance and application management, data protection, and configuration provisioning, as well as protect devices from attacks that leverage vulnerabilities, preventing unauthorized access to apps, as well as detecting and blocking malware and fraudulent websites.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter
- 2025 APT Report: Staying Ahead of the Modern Threat Landscape

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation